Data Center Filter-Based Forwarding — Firewall

Juniper Learning Byte: Start here to expand your knowledge of firewalls inside data center devices.
In this Learning Byte, Juniper’s Zach Gibbs walks you through the process of configuring firewalls with filter-based forwarding on data center devices. This video is most appropriate for users who have a high degree of knowledge and skill with data center technologies.
You’ll learn
What will happen to network traffic if there is no specific host route
How to show security zones and security policies and how to edit them
How to verify your firewall configuration
Who is this for?
Host

Transcript
0:11 hello my name is zach gibbs and i'm a content developer within education services inside juniper
0:18 networks and today we will be going through the data center filter-based forwarding firewall
0:24 learning bike all right so here is the topology and in here we have a few different devices we
0:32 have router l1 router l2 which are normal router leaves and then service leaf service l1 which is
0:39 a service leaf and then we have the dc firewall or dcfw which is our firewall for our data center
0:47 and with this learning by we're going to be focusing on the firewall configuration so it's
0:52 dcfw and keep in mind that i have done other learning bytes that go over the router l1 and
0:59 router l2 configuration as well as the service l1 configuration and there will be another learning
1:04 byte that goes over the verification of this whole filter-based forwarding in a data center scenario
1:10 so with that being said let's go ahead and jump to the cli and get this going all right so here
1:17 is the firewall device we won't be doing too much configuration or really any configuration here
1:21 i've pre-done that configuration because this is a lot to go through with all this configuration but
1:27 there is some things we do need to look at and so with that being said uh let's go ahead and
1:32 jump back to the topology to have a look and see where we're at all right so here's the topology
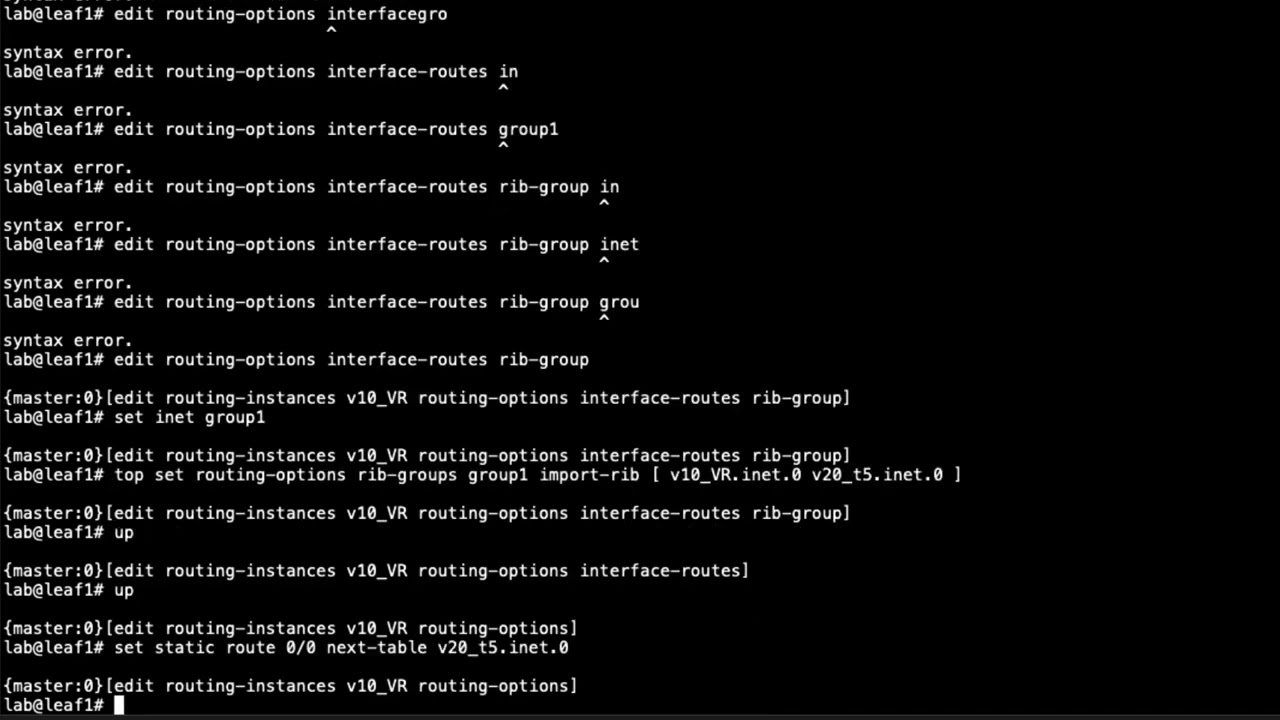
1:38 we have previously configured router l1 and router l2 and surface leaf l1 we configured the inspect
1:44 vrf on both of those or all three of those or i guess it's both just two and the secure vrfs on
1:50 the surface leaf l1 and router leaf l2 connected those together with the correct route targets
1:55 configure the correct vnis configured the evpn protocol to export routes as type 5 routes and
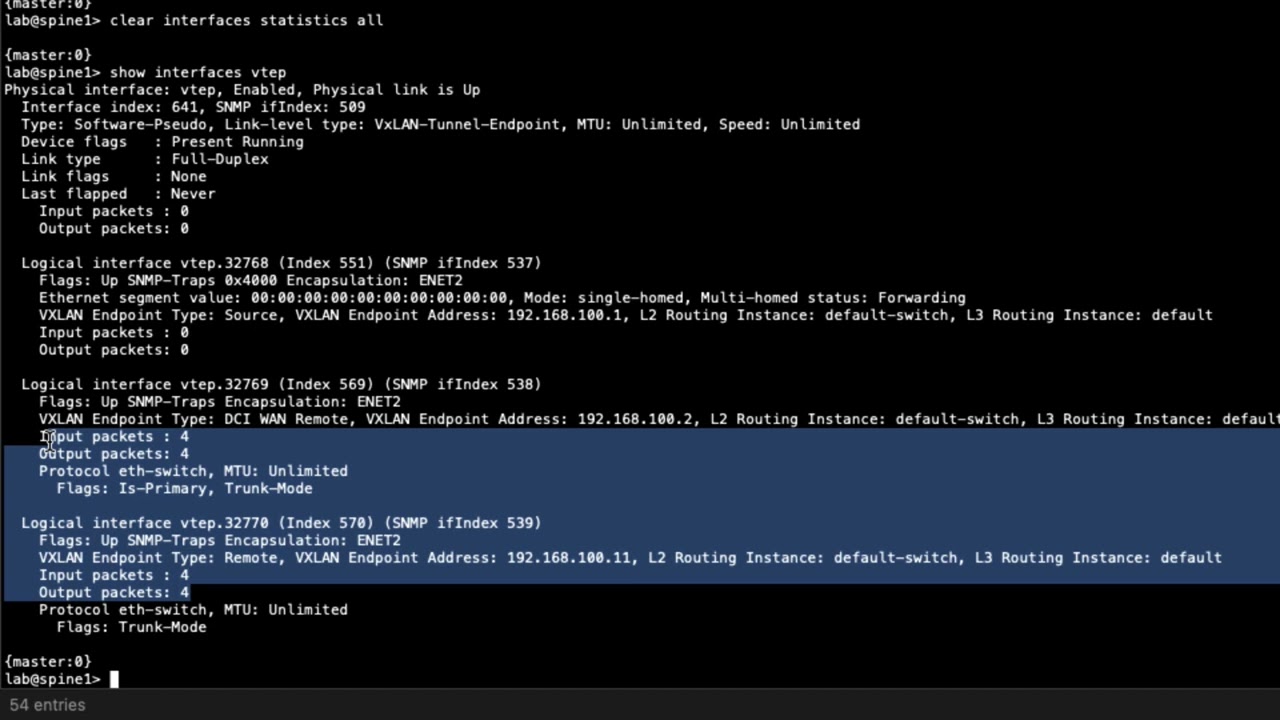
2:02 so the routing is being shared and we'll show the verification of that later but right now
2:06 we want to focus on the dc fw which is the data center firewall and here you can see
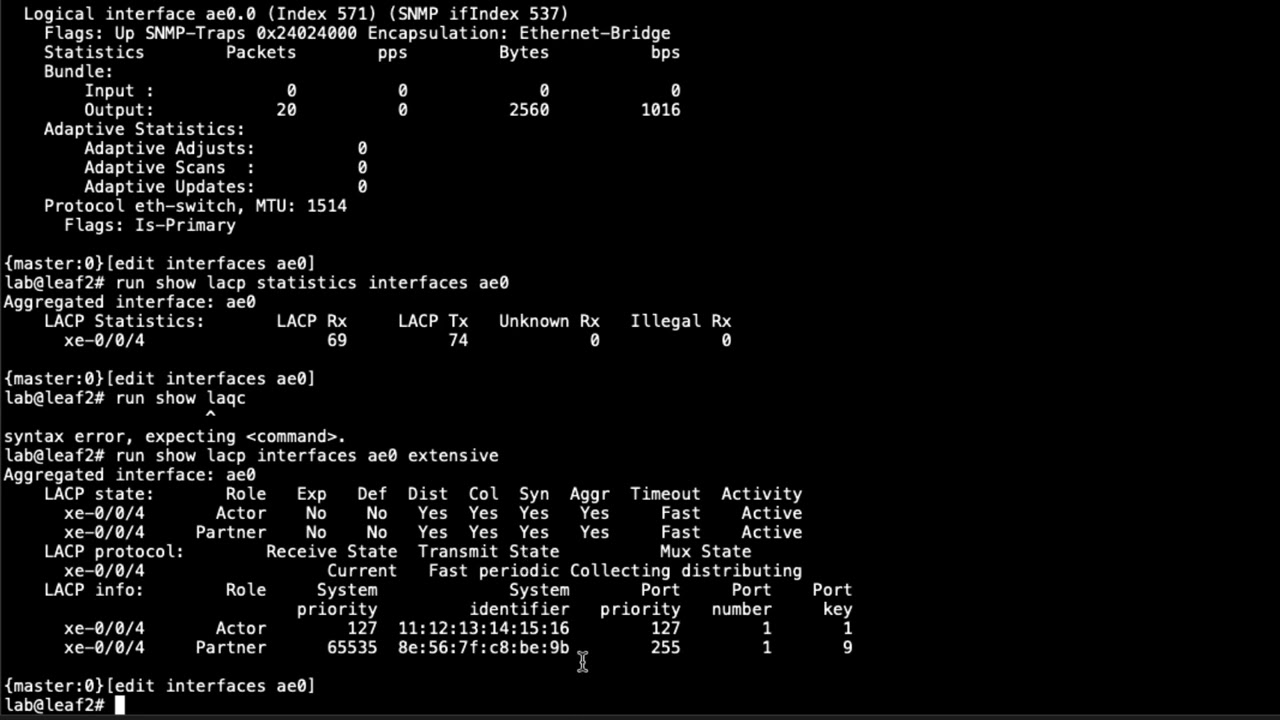
2:12 it connects into service leaf one we have two different interfaces gigi002.91 and gigi002.992
2:19 those interfaces connect into uh well the 991 connects into the inspect vrf and the 992 connects
2:26 into the secure brf on the service leaf and so we'll look at that configuration and see what's
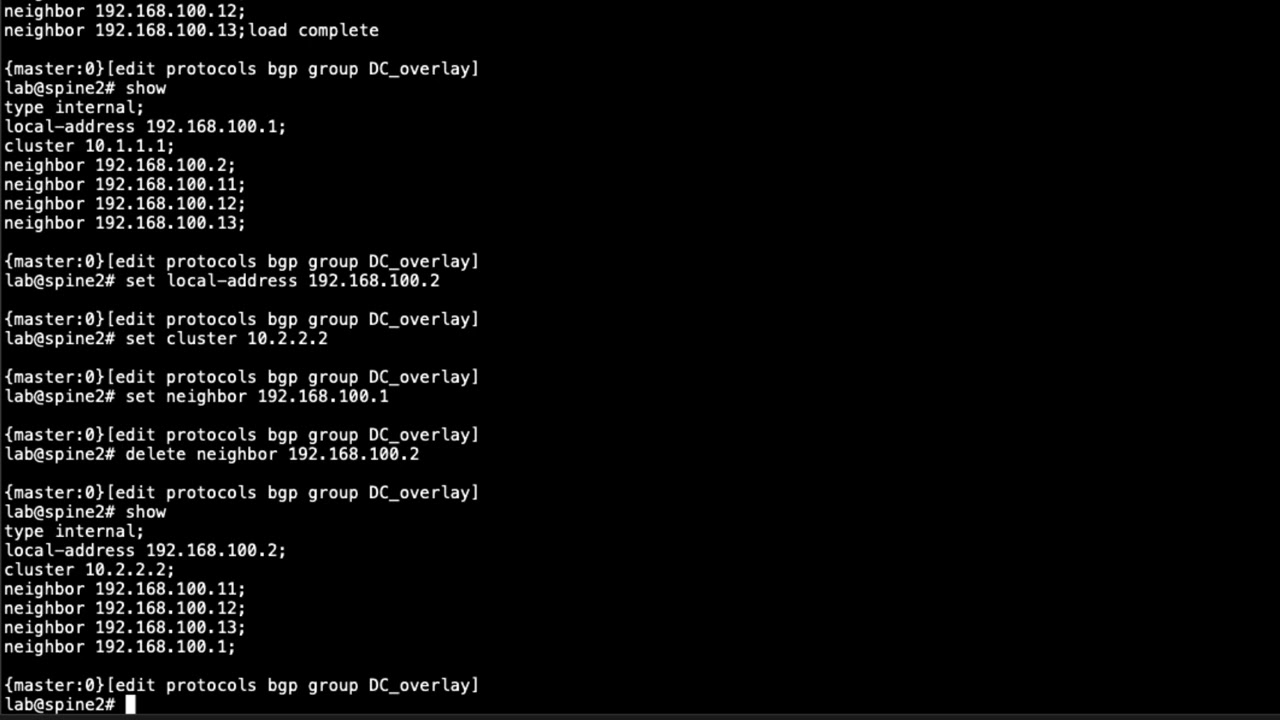
2:30 going on and we'll look at the bgp groups the pairings we configure that with service leaf one
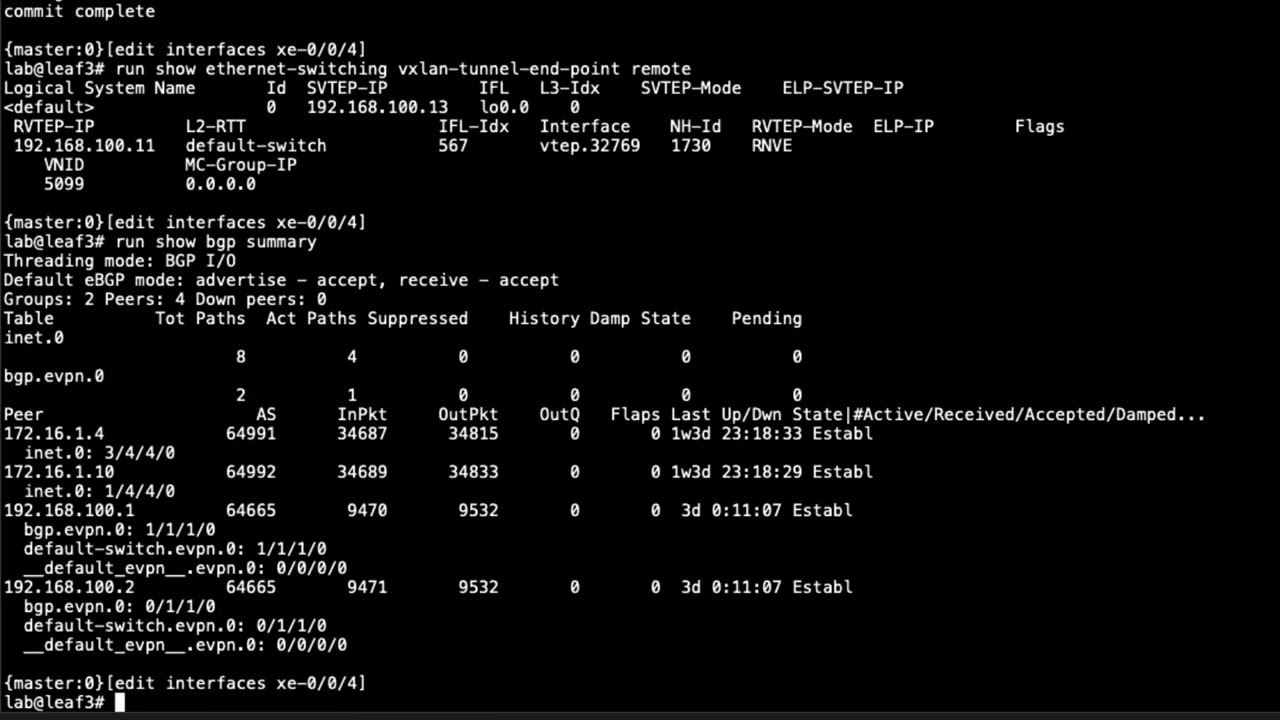
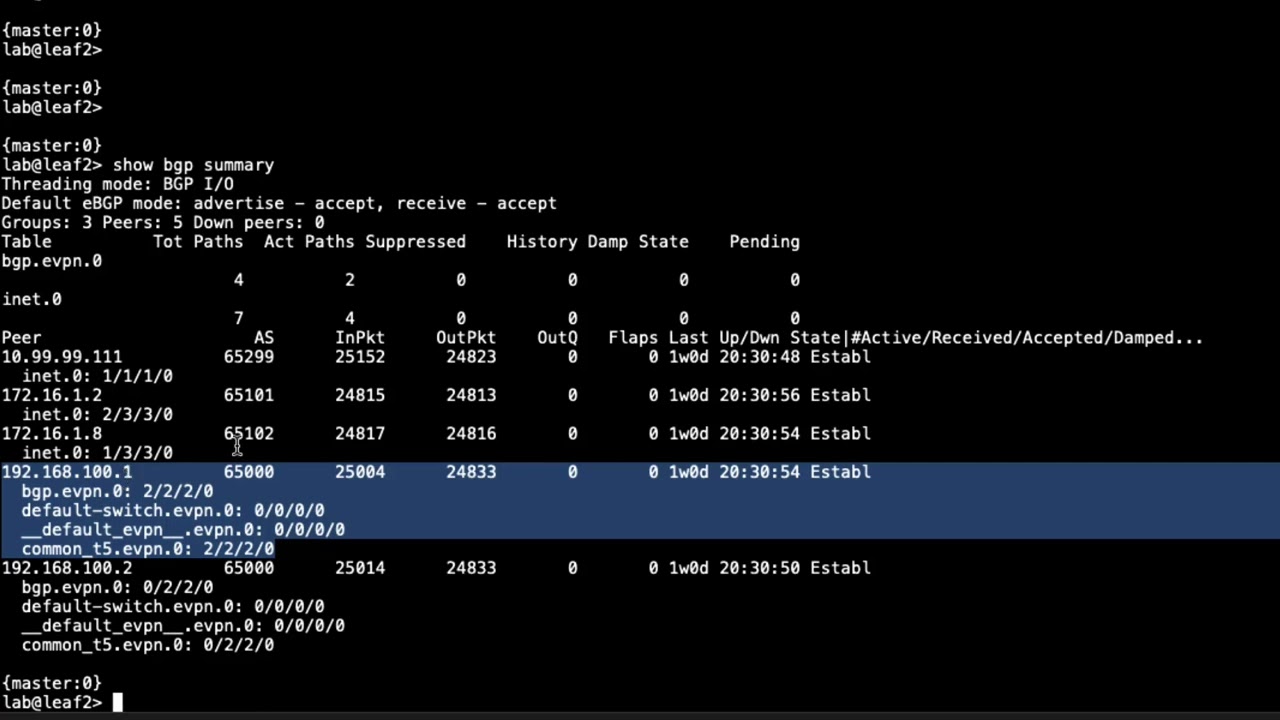
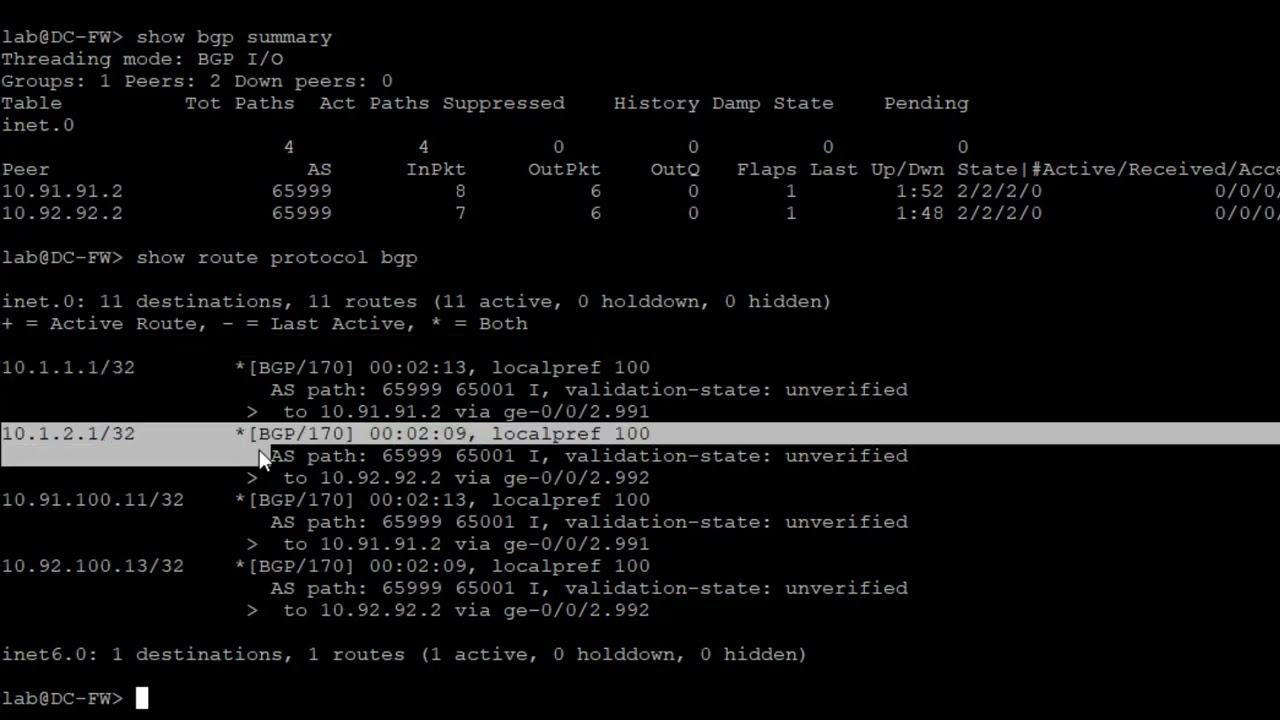
2:36 so let's go ahead and jump back to the firewall and so here let's first look at the bgp groups
2:43 and you can see that we do have two groups recall that 10991 or rather the 10 91 91.2 is the inspect
2:53 vrf on the service relief and 10.92.92.2 is the secure vrf on the service leaf so we can look
3:01 at the routes see what we're receiving and you can see here we have the host one route the host
3:08 two route and then the loopback interfaces or the vrfs those are being sent and that's good
3:16 that's what we want to do and so with that let's see what we're sending the service leaf vrfs
3:27 let's see just specify the neighbor and you can see we're sending them a default
3:33 route and that's exactly what we want to do because that'll help attract the traffic
3:37 in the vrfs towards the firewall and so we can look at
3:44 what we're sending the secure vrf and again the default route now that default route is just
3:51 something that's configured here locally as a static route with a next top of discard so
3:57 if there's no specific host route then and traffic comes in and matches something else
4:01 it's just going to discard it and that's what we want to do we only want to be passing around
4:05 traffic for specific routes and here recall that if we look at bgp routes we can see here we have
4:15 routes for host one and host two so we won't be discarding that traffic if any other traffic
4:19 shows up here it's going to discard it because that's what the next hop for the default route is
4:25 and so okay so what else do we want to show we want to show
4:29 security zones there we go the security zones okay we can see here that gigi
4:34 uh zero zero two nine nine one is part of the inspect zone and gigi002.992 is part of the
4:41 secure zone and for host inbound traffic we're only permitting bgp traffic and that's because we
4:46 need to have bgp pairings with the service leaf from the firewall so that makes perfect sense
4:52 and then uh what else do we would be good to show okay so the security policies let's
4:57 jump in there we're going to need to edit some of those security policies because we'll see
5:02 we'll see how they look currently they're currently set up but they're not set up correctly
5:05 okay so from zone secure to zone no we don't want to do that we want to inspect to secure now recall
5:13 it's going to be coming in the inspect interface or the inspect zone coming from the inspect brf
5:19 and then to the secure zone to the secure vrf on the service lead and so we have some security
5:25 policy set up but we've set up to permit icmp and block and log or deny and log ssh and we want to
5:32 flip that around remember we're not going to allow icmp but we're going to allow ssh so let's just go
5:38 ahead and delete those policies and we'll say paul's edit policy allow ssh source set match
5:47 source address post one now this it's already host one is already configured in the address book
5:53 uh destination address host to application junos ssh and we're gonna set then permit we're just
6:02 gonna permit that traffic so that looks good and we're gonna specify a new policy called uh
6:09 block icmp we're gonna say match source address post one destination address hosts
6:18 post two application i'm going to say junos icmp all and then we're going to say deny or set then
6:28 let's say reject log i'm going to say set then log session to net so the session initialization
6:37 now one thing to look at with this is this is only coming from the inspect zone to the secure zone so
6:42 if host two attempts to initiate traffic to host one it won't even attempt to set up the session
6:48 we don't even have it set up to log those attempts or whatever but at least with this
6:54 regards we do have it set up to permit the ssh traffic from host one host two and block
6:59 icmp traffic and log that now if something else say it's some sort of mail protocol or ftp
7:06 or something else comes through it'll just get silently rejected or discarded because
7:11 the default policy on an srx is to silently discard without logging so keep that in mind
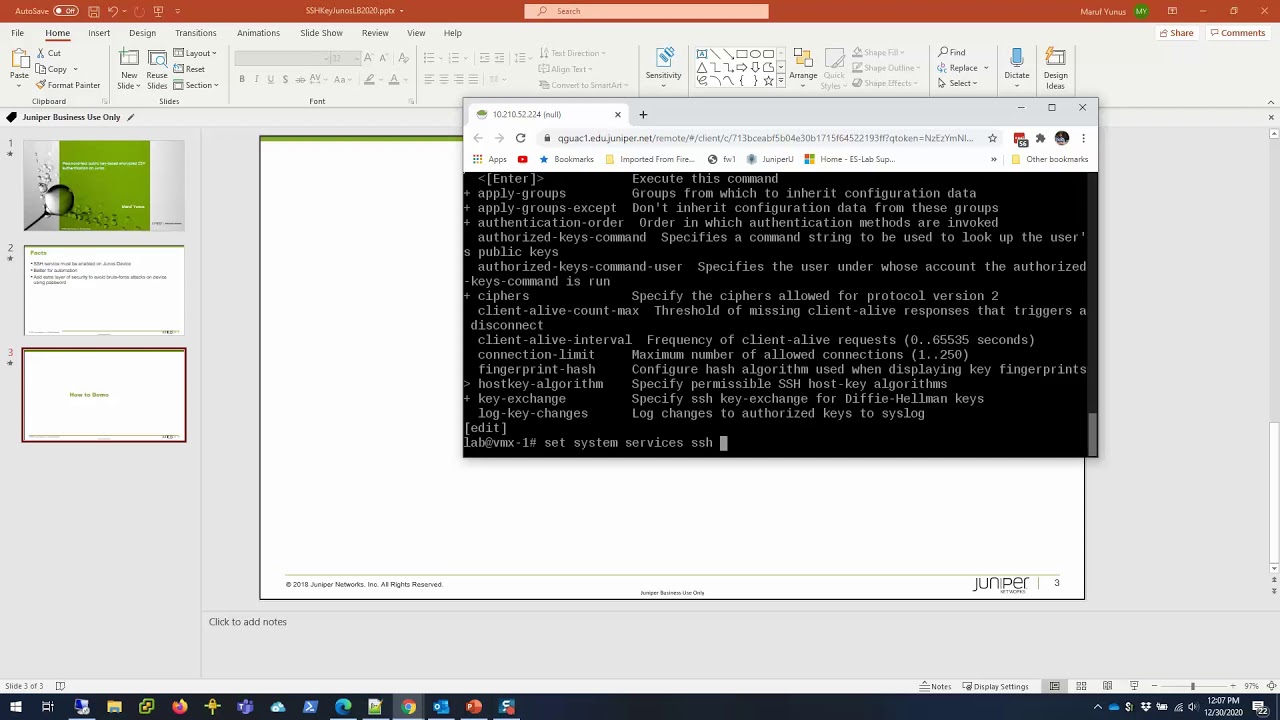
7:18 and so i think we're good there let's go ahead and commit that and exit to operational mode and then
7:23 we can verify this and so we have the firewall configured and so next we'll jump to verification
7:29 right this brings us to the end of this learning byte here we demonstrate how to configure the
7:34 firewall with regards to data center filter based forwarding so as always thanks for watching
7:41 visit the juniper education services website to learn more about courses view our full range of
7:48 classroom online and e-learning courses learning paths industry segment and technology specific
7:56 training paths juniper networks certification program the ultimate demonstration of your
8:02 competence and the training community from forums to social media join the discussion
8:14 you