Passwordless Public Key-based Encrypted SSH Authentication on Junos

Learning Byte: The easy, secure way to log in to SSH on Junos.
Enabling passwordless SSH key-based authentication on Junos devices can aid automation and security for your network. Juniper’s Maruf Yunus shows you step by step how to get it done.
You’ll learn
Three important facts you need to consider before you begin public key-based authentication
How to optionally encrypt the key with a passphrase for additional security
How to confirm and test the authentication
Who is this for?
Host

Transcript
0:00 [Music]
0:11 hello uh welcome to juniper network's
0:13 learning by
0:14 my name is maru i'm a lab architect
0:16 within juniper education services lab
0:18 team
0:18 in this landing byte i'm going to show
0:20 you how to enable
0:22 passwordless public key based encrypted
0:24 ssh authentication
0:26 uh on a junos device so before we
0:30 start uh with the how to uh video
0:34 i just want to talk about a few facts
0:35 about uh the
0:37 the public key best authentication to
0:39 enable uh public key based
0:40 authentication on a journal's device
0:42 you need to have ssh service must be
0:45 enabled
0:46 and the authentication with public key
0:50 helps with automation in many scenarios
0:53 like you know if you have
0:54 a automation system like ansible or
0:57 puppet or any other type of uh or even
1:00 bash scripts uh perl script
1:02 you can uh you can use the uh public key
1:05 based authentication
1:07 uh without being prompted for with
1:09 password every single time your
1:11 automation
1:12 program or script runs this makes it a
1:15 lot faster
1:16 to automate or perform automation tasks
1:19 and
1:19 obviously having public key based
1:22 authentication
1:23 can help you to avoid brute force
1:26 attacks
1:26 on juno's devices by disabling uh the
1:29 password-based authentication completely
1:31 on a device
1:32 so uh these are three facts that you you
1:35 can consider
1:36 you know without further ado let's uh
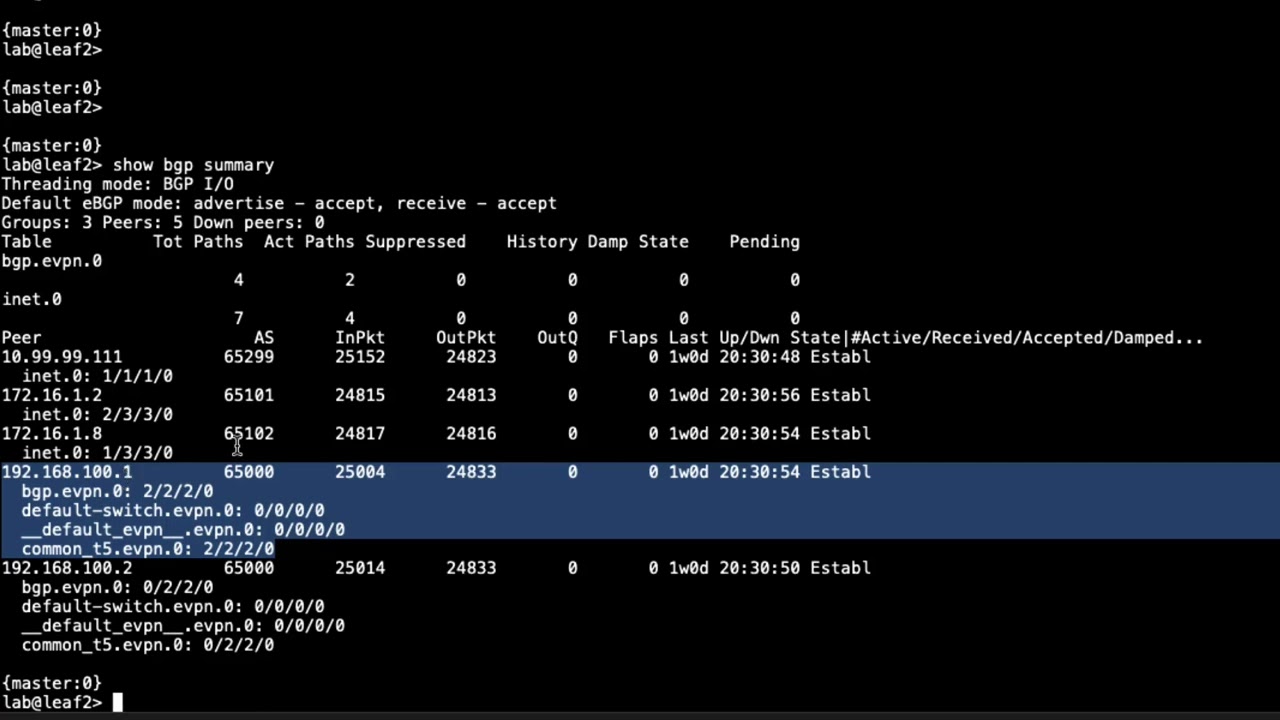
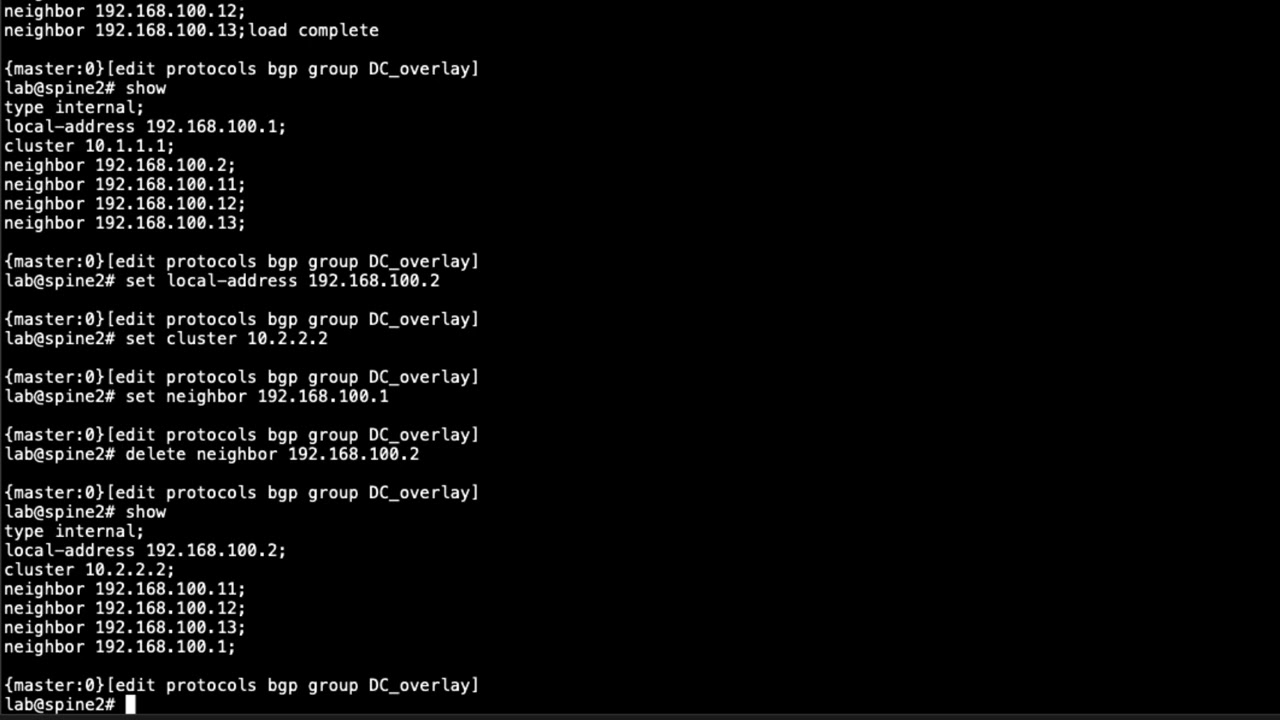
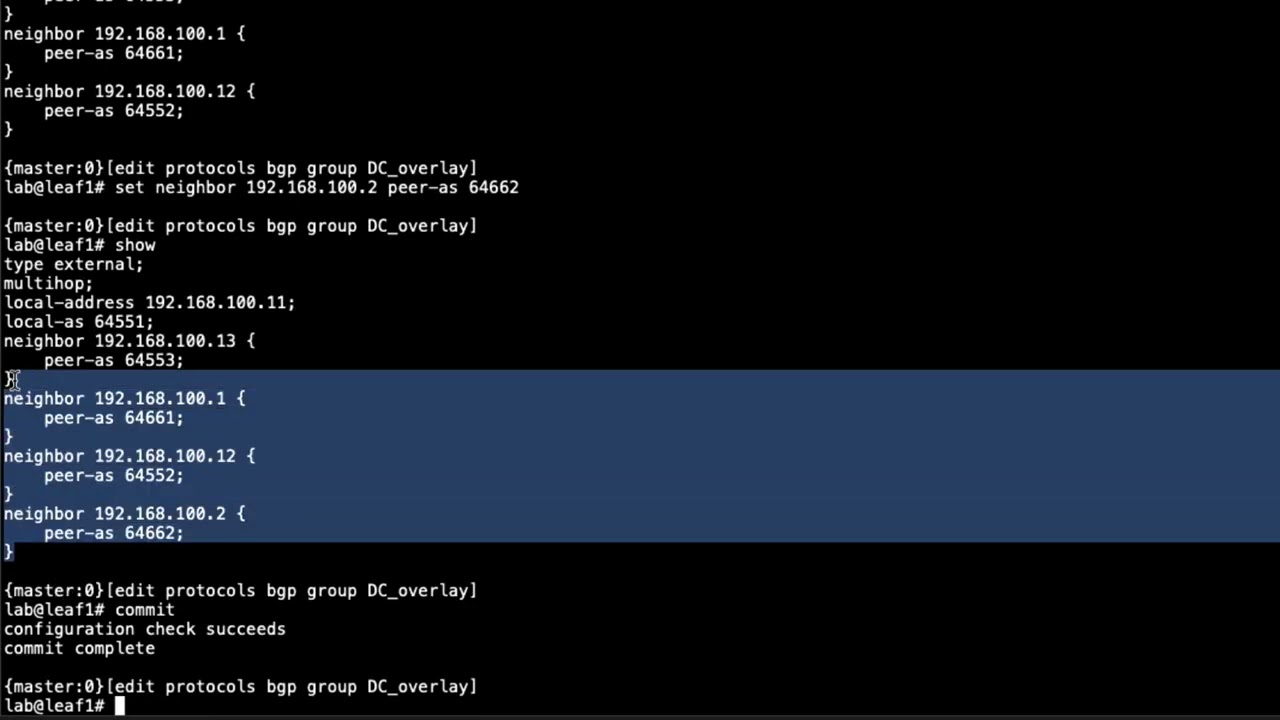
1:39 go to the demo so i have a
1:42 centos vm here running which is
1:46 basically
1:47 uh on my lab network
1:50 and i have a pmx device that i'm going
1:53 to connect
1:54 first to show you how it looks like so i
1:57 have this vmx device
1:59 i'm going to log into my password and
2:02 lab is the user i'm going to demonstrate
2:04 with this user can log in to this device
2:06 and it's a super user
2:08 you know you can do things uh whatever
2:10 you want to do
2:11 you can do various things okay
2:16 so say i want to automate run automation
2:18 scripts or
2:19 uh from my sent to us server
2:22 right i may have scripts on the server
2:24 that i want to use
2:26 so that it can ssh to the bmx device
2:29 without any password
2:30 first of all i need to generate ssh key
2:34 so i do ssh keygen
2:39 t rsa okay
2:43 and then it's gonna say okay we're gonna
2:44 save the file in this case i'm gonna
2:46 keep the default
2:47 under my home directory enter
2:50 actually i already had a key so i'm
2:52 going to override that
2:55 and then it asks for passphrase now to
2:57 add additional security you can add
2:59 passphrase for my automation script i'm
3:01 not going to add any password so that i
3:02 don't get prompted for the password but
3:04 you can add that extra layer of security
3:06 every time you use the key
3:07 uh with the passphrase i'm gonna press
3:10 enter
3:10 enter again and my key is generated
3:14 so uh now i'm gonna i can see the key
3:17 here
3:18 you know if i do a right click
3:22 okay so this is my key that got
3:24 generated
3:25 right now so now what i'm going to do
3:27 i'm going to copy this key to my junos
3:30 device
3:32 okay i'm going to scp that to my device
3:34 first
3:43 i'm going to do under var temp i'm going
3:45 to delete that
3:46 later okay let's copy
3:49 i'm going to go back to my device
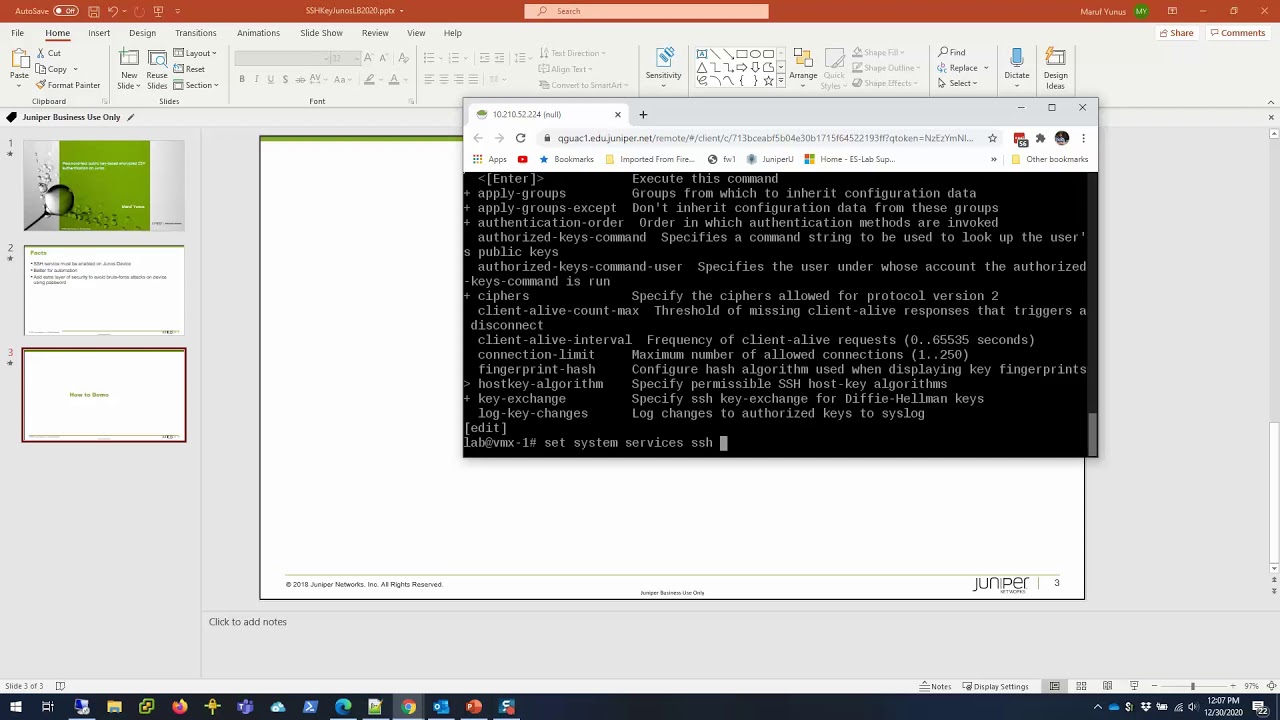
3:59 okay so i'm going to configure mode
4:03 i'm going to first set
4:07 system login user
4:11 authentication is the user i'm going to
4:14 make change and then authentication
4:19 and i'm going to do a load key file
4:23 that i can load you can press the you
4:26 know
4:26 key content configuration file as well
4:28 but that i find this one easier
4:30 server temp id
4:34 and there you go okay and i'm gonna also
4:38 disable the ssh so i think my
4:42 system services as it's already enabled
4:45 so if i do a show
4:48 you'll see that i have ssh already
4:51 enabled
4:52 right i'm gonna change that to only key
4:56 base so no password-based authentication
4:57 so to do that
4:59 i can do like this
5:03 set system services ssh
5:07 i'm gonna do a question mark it's called
5:09 uh
5:14 sage
5:18 sage is called uh
5:22 sorry no password authentication so i'm
5:26 gonna
5:26 i'm gonna use that so uh i'm gonna say
5:30 no password authentication
5:35 okay so i'm gonna show compare see what
5:38 i got going here
5:40 so i'm adding a key to the lab users and
5:43 i'm going to say no password
5:44 authentication
5:45 commit and confirm first okay
5:49 it's always good to use confirmed
5:51 because you know what if my key doesn't
5:53 work or what something goes wrong so
5:54 that i can go back
5:55 in 10 minutes it'll roll back again so
5:57 this is a good way to test it
5:59 if it looks good then we can commit it
6:00 right so i'm going to commit confirmed
6:03 okay so now it will be rolled back in 10
6:05 minutes so that gives me some time to
6:07 test
6:07 my uh whatever i did okay
6:11 oh and i have to file delete
6:15 bar temp
6:22 id okay so file deleted so i
6:25 don't have the key anymore laying there
6:27 okay now if i do ssh
6:28 172 25 11 and 1
6:32 there you go boom i'm in without any
6:34 password
6:35 so i can do like this you know cli
6:41 show version
6:45 show this time up time
6:50 i can involve these commands the same
6:52 time
6:54 through my cli and that's how i can
6:57 script it
6:58 so i'm going to do a separate video on
6:59 that how to script
7:01 from a bash script uh using uh using
7:03 this method
7:04 so hopefully this helps so now if i try
7:07 uh you know try login with the password
7:09 let's see
7:12 let's go back to a different device that
7:14 i have on the network
7:16 and then from there i do ssh
7:19 172.105.11.1
7:21 and i cannot okay
7:25 it's not gonna let me log in without a
7:27 password so
7:28 uh you know i hope this video helps
7:32 thank you for watching
7:35 visit the juniper education services
7:37 website
7:38 to learn more about courses view our
7:41 full range of classroom
7:42 online and e-learning courses
7:45 learning paths industry segment and
7:48 technology specific
7:49 training paths juniper networks
7:52 certification program
7:54 the ultimate demonstration of your
7:56 competence and
7:57 the training community from forums to
8:00 social media
8:01 join the discussion