Stop Paying Double for Encryption

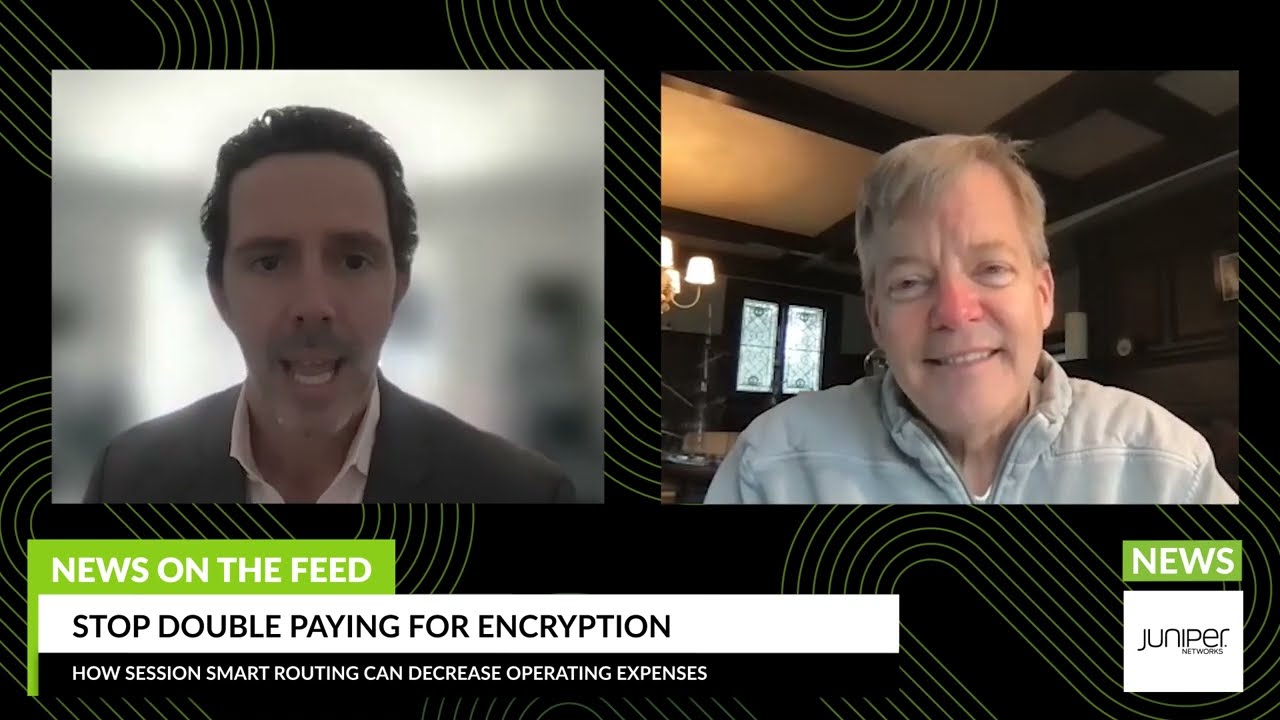
Are you paying double for encryption? Here’s how to stop.
In this edition of News on The Feed, Juniper’s Patrick MeLampy talks about how Session Smart Routing can decrease your operating expenses by avoiding double encryption.
You’ll learn
Why you might be paying double for encryption and the problems re-encryption can cause
What you can do to avoid double encryption
How Juniper’s Session Smart Routing (SSR) products encrypt only the traffic that needs to be, saving you both money and network headaches
Who is this for?
Host

Guest speakers

Transcript
0:00 well welcome to news on the feed network
0:02 security is a top concern for many
0:04 businesses but i was shocked to learn
0:05 that many companies are double paying
0:07 for encryption and slowing down their
0:09 networks at the same time our guest
0:11 today patrick molampi raised the issue
0:13 on a recent blog post patrick why is
0:15 this happening
0:18 well it's fascinating you know as much
0:20 as eighty percent of everything that
0:22 that you do on on the on the internet
0:24 today is already encrypted even things
0:27 like netflix are encrypted facebook
0:29 google email a gmail
0:31 uh all the webmail stuff is encrypted
0:34 almost every website you go to for
0:36 shopping is encrypted and inside your
0:38 business when you're working on your
0:40 business applications most of those are
0:42 already encrypted as well and so what
0:45 people do today is they use
0:47 wan solutions that use ipsec tunnels and
0:51 the ipsec tunnels
0:53 actually re-encrypt information that's
0:55 already encrypted and when they do that
0:56 re-encryption they add uh a substantial
1:00 number of bytes frequently uh somewhere
1:02 around 30 bytes per packet maybe more
1:05 uh there's also tunnel overhead added on
1:07 top of the the encryption overhead and
1:11 encryption actually takes a lot of cpu
1:13 time it's one of the uh most intensive
1:15 uh things that a edge router does if it
1:17 if it's doing encryption is uh
1:19 encrypting traffic and so
1:22 80 of this traffic's already encrypted
1:24 and you're re-encrypting it again
1:27 and it has all these subsequent
1:29 inefficiencies that it causes including
1:31 sometimes
1:33 it causes packet fragmentation uh which
1:37 it's basically a packet gets too big it
1:38 has to be cut in half and sent his two
1:40 packets and then on the other side it
1:42 has to those two packets had to be put
1:43 back together again and and and taped
1:46 back up and sent on their way so it's a
1:48 it it's a massive amount of inefficiency
1:51 invariably adding latency as well uh we
1:54 we've seen that
1:55 it it can add between 40 and 50
1:57 milliseconds of latency to go through a
1:59 software-based encryption and decryption
2:02 uh
2:02 tunneling encapsulation and
2:04 de-encapsulation solutions so
2:06 so in general why do it if you don't
2:08 have to and if 80 of the time you don't
2:11 have to
2:12 why would you not want a solution where
2:14 you didn't have to to re-encrypt the
2:16 stuff that's already encrypted yeah no i
2:18 mean that is fascinating i completely
2:20 agree so i guess one of the biggest
2:22 questions is like what do people do so
2:24 that they aren't double encrypting
2:27 well for for you to avoid double
2:29 encrypting you have to get away from
2:30 using ipsec tunnels because ibsec
2:32 tunnels can't send traffic that isn't
2:35 re-encrypted they're not it's not
2:36 possible for them they have to
2:38 re-encrypt everything and so for that 20
2:40 of the traffic that's unencrypted uh
2:42 what you really need to do is try to
2:44 find a way to only encrypt that traffic
2:47 what we do at juniper networks with the
2:49 ssr product is we actually route
2:52 sessions we we actually don't use
2:55 tunnels we we use the session smart
2:56 router and that's the juniper ssr that
2:59 actually routes sessions one by one
3:01 instead of putting them all into a big
3:03 tunnel and that way we can re-encrypt or
3:06 encrypt
3:07 only the 20 of traffic that needs
3:09 encryption and avoid the re-encryption
3:11 penalty
3:12 that's amazing so if someone is facing
3:15 double encryption now or wants to learn
3:17 more what do you recommend that they do
3:19 they really should give us a call
3:21 because there are so many benefits
3:23 beyond double encryption associated with
3:25 a session smart router uh starting with
3:28 security and and being more efficient
3:31 and on bandwidth across the board
3:32 there's so many other benefits they
3:34 should definitely give us a call and we
3:36 can show you how you can avoid
3:37 re-encryption and and
3:39 get a lot of other benefits as well
3:41 that's awesome well patrick thank you so
3:43 much for your time thanks for joining
3:44 the show so for any of our viewers if
3:46 you're interested in learning more
3:47 simply click the link below to see
3:49 adaptive encryption in action uh with
3:51 our session smart routing demo
3:53 and there's also a link to the blog so
3:55 thanks again patrick and i hope
3:56 everybody has a wonderful rest of their
3:58 day