Juniper Session Smart Technology Overview

Starting wonderfully anew: Why Session Smart Router changes everything.
Most SD-WANs rely on tunnel overlay technology and are riddled by overhead, retransmissions, fragmentation, and generally poor goodput. Reid Stidolph and Adam Morris demonstrate how Session Smart breaks the badput habit of tunnels. An in-depth technical Q&A follows Reid’s presentation.
You’ll learn
Rewind the clock to 2014 for a recap of networking’s unwieldy past
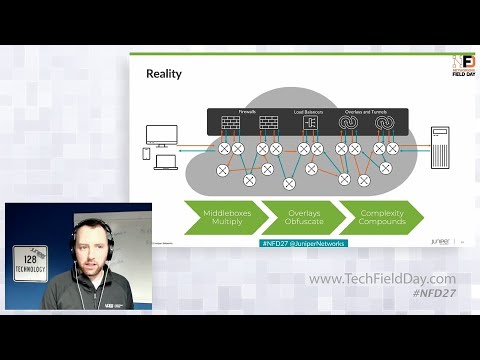
The difference between the theory and reality of networks
The four key elements of Juniper’s tunnel-less Session Smart Router
Who is this for?
Host

Transcript
0:08 and um yeah just super excited and
0:10 honored to be here with uh you know with
0:12 the the delegates and and uh
0:15 and the team to really introduce and
0:17 demonstrate session smart a bit and and
0:20 you know talk about its integration with
0:22 mist and
0:23 and uh
0:24 you know for starters here we're gonna
0:27 um i'm gonna
0:28 like was mentioned earlier some of you
0:30 may have seen you know past network
0:32 field day with 128 technology and so
0:35 some of this may be a little bit of a
0:36 refresher but you know really wanted to
0:38 set the stage here for those that may
0:40 have missed it
0:41 um and and you know talk about session
0:44 smart what it means where it came from
0:46 and and why it's here now with juniper
0:49 um i
0:50 personally enjoy talking about this
0:52 journey of session smart technology and
0:54 secure vector routing uh because i was
0:57 really lucky enough to have a front row
1:00 seat through
1:01 uh through all of it most of its
1:03 creation so
1:05 um
1:06 so to start with you know let's let's uh
1:10 let's rewind the clock a bit back to
1:12 2015 or 2014 actually when when this
1:16 tunnel-less technology that we're going
1:17 to talk about here was was first being
1:20 created now
1:21 um you guys you panelists in the
1:23 audience
1:24 will remember that uh
1:26 um
1:27 you know back in 2014 sd-wan really
1:31 wasn't that much of a
1:33 buzzword yet uh sdn and nfv were kind of
1:36 the hot topic or the hot uh buzzwords
1:39 kind of you know climbing the hype cycle
1:41 and and
1:42 and you know arguably the the tools of
1:46 software and software defined we're
1:47 still looking for a useful marketplace
1:50 landing with broad acceptance and
1:51 utility so of course in hindsight we all
1:54 know that that that place would
1:56 ultimately turn out to be the land and
1:57 and
1:58 uh but not a lot of people were talking
2:00 about it at that particular time
2:03 uh now back in 2014 the people the folks
2:07 that were working on this technology not
2:09 only had a background in ip routing but
2:11 also in ip telephony
2:14 so they kind of looked at networking
2:15 through a slightly different lens
2:18 you know for instance with an ip voice
2:20 and and video application they operate
2:23 inherently with the notion of a session
2:25 and so in like in that world you know i
2:27 pick up the phone and initiate a call to
2:30 you
2:31 and there's this signaled session that
2:33 gets established
2:34 and and there's a directionality with
2:37 that session me to you and based on that
2:40 asymmetry uh in in the conversation
2:42 progresses as we exchange information
2:45 and truthfully this is the way most
2:47 applications work um you know so this
2:49 approach to sessions where there's a
2:52 signaled exchange exten establishing in
2:55 intent and the dispossession of the
2:57 network towards the session were some of
3:00 the formational um things of the
3:02 technology but at the time
3:04 while network was networking was
3:06 certainly seeing some notable changes
3:08 that it hadn't seen in a very long time
3:10 thanks to kind of being reinvigorated
3:12 with the powers of software and software
3:14 defined you know the ip routed networks
3:17 that everyone was building upon were
3:19 were largely built and operated the same
3:22 way they had been for the past 20 or so
3:25 years as shown in the slides we see
3:27 uh here you know the routed networks
3:29 were born out of a theory
3:31 that
3:32 that said hey keep the networks
3:35 stateless
3:36 leave security to the endpoints keep it
3:38 fast and simple and of course this was
3:41 obviously for really good reason in the
3:43 early days when
3:45 when rfc 1717 was being drafted by the
3:48 long bearded wizards of the itf
3:50 it was all the internet could do to
3:52 really keep up with the booming demand
3:54 for networks so
3:56 uh you know based on the technology of
3:58 the day making it go bigger and faster
4:01 were the most important things
4:04 um but you know bottom line routers
4:06 started out simple and stateless
4:09 so
4:10 you know if that was the the reality uh
4:13 or the the theory
4:14 uh in the beginning
4:17 in 2014 when
4:19 this technology was was sort of
4:21 germinating uh you know this was the
4:23 reality that we lived in you know as the
4:25 networks grew and the internet took off
4:28 uh
4:29 you know high value targets such as
4:31 financial institutions governments and
4:33 everything you know started to put
4:35 things on the network and it turns out
4:37 uh security was needed uh within the
4:40 network and so firewalls got got loaded
4:42 on top and to to keep up with the the
4:46 distribution of load and scale
4:48 applications load balancers and and
4:50 other stateful devices were piled on top
4:53 and as the networks were not the routed
4:56 networks anyways we're not smart enough
4:58 to take packets where they needed to go
5:00 tunnels and overlays proliferated to get
5:02 them where they needed to go you know so
5:04 the if the networks were envisioned to
5:07 be simple and stateless they had become
5:08 anything but that state
5:11 was everywhere and complexity really was
5:13 was the result of it so
5:16 you know for the majority of the
5:17 industry wielding the power of software
5:20 and software defined at that time
5:22 they were busily focused on taking the
5:25 same approaches and the same
5:26 architectures they had done
5:28 uh previous and just kind of recreating
5:31 them software uh recreating them in
5:33 software which really you know was only
5:35 compounding the problem of fragility and
5:38 complexity that was festering and and
5:41 you know really for just marginal gains
5:44 and end user experiences
5:46 so
5:47 the only medicine that was being applied
5:49 to this malady from our perspective was
5:51 putting packets into tunnels to get them
5:53 to go places the routed networks
5:55 wouldn't weren't smart enough to take
5:56 them and sprinkling a heavy dose of
5:59 orchestration and automation on top of
6:01 it
6:02 you know to to that team back at the
6:04 time that was the definition of
6:06 technical debt and networks everywhere
6:08 were just accumulating it so
6:10 you know the motivation was a feeling
6:12 that that what was being done just
6:14 wasn't enough if all we did was take the
6:16 same things we did in hardware and do
6:18 them in software we were just doing it
6:21 wrong so
6:22 you know the promise and vision of
6:24 software and software defined
6:26 uh of unlocking innovations and
6:29 networking to power next generations and
6:31 networks improve user experience uh they
6:34 just weren't going to be realized to
6:36 their fullest potential on the current
6:37 trajectory so
6:41 so that was the mindset um and some of
6:43 the formational thinking uh behind the
6:45 session smart router and and at the time
6:48 it was conceived of um
6:50 so they set out to build a router a
6:52 smarter router uh and and there were a
6:55 few key things that they decided a smart
6:58 router needed to have
6:59 first of all it had to make the best
7:01 possible use of software and the powers
7:04 of software defined
7:05 you know there's there's that famous
7:07 saying that says software is eating the
7:08 world and it's for good reason you know
7:11 no hardware can compare to the rapid
7:13 innovation cycles the superior economics
7:15 of software
7:17 and you know the platforms that power
7:20 software from small to large to cloud
7:22 and the economics of them really had to
7:24 be leveraged well
7:27 secondly it had to operate based on
7:29 sessions in the journey from client to
7:31 cloud sessions are the thread that
7:33 connect the users to the applications so
7:36 a certain amount of that network state
7:39 that was just being kind of piled on top
7:41 and all these uncoordinated middle boxes
7:44 just needed to be democratized into the
7:46 routing plane in a matter that was well
7:48 coordinated across the routing nodes
7:51 and you know
7:52 not not just for the purposes of an
7:55 evolved and better circuit synchronized
7:57 control plane but also for the purposes
7:59 of telemetry which plays an important
8:01 role in some of the stuff that we're
8:02 going to see
8:03 as we get into mist
8:05 um
8:06 so
8:07 also the way the network was designed
8:10 and operated kind of that day zero um
8:14 experience it really had to op orient
8:16 around services not ip ports prefixes uh
8:20 the network constructs themselves had to
8:22 orient around services because that's
8:24 what you know without services what's
8:26 the point of a network it's there to
8:27 deliver services and last but not least
8:30 security had to be baked in not painted
8:34 on in perimeters and
8:36 and
8:38 and
8:39 zones and things like that it really
8:40 there
8:41 an element of native zero trust had to
8:44 be um kind of baked in it at every hop
8:47 so
8:49 that's more than an adequate setup an
8:52 intro to the uh the technology let's
8:54 let's jump right into how it works and
8:57 and uh
8:59 operate so
9:01 in the diagram here we gotta we got a
9:02 simple topology of of basically two ssrs
9:07 with a cloud in the middle some network
9:09 some layer three network in the middle
9:12 um
9:13 and uh we're gonna kind of walk through
9:14 a packet as it flows through this um and
9:18 and
9:18 and talk about secure vector routing and
9:21 and and how it works um i'll point out
9:24 as we go through this that uh you know
9:27 this is a simple setup of two ssrs um
9:30 you know could be a simple hub and a
9:32 spoke at a data center or a how about a
9:34 branch or a hub at a data center spoke
9:36 at a branch um but uh you know this this
9:40 was designed and intended for multiple
9:42 hosts so there could be potentially many
9:44 ssrs kind of in this uh in this middle
9:47 bit but we'll we'll start simple here um
9:51 and you know we have a source and a
9:53 destination at the left and the right um
9:56 source ip address destination ip address
10:00 and it sends that packet into the ssr at
10:03 some point um you know ideally this ssr
10:06 is the uh is the default gateway for
10:09 this uh this source client here uh on
10:12 its lan
10:14 um and and you know the very first thing
10:17 that that ssr is going to do
10:19 is
10:20 uh
10:21 detect first of all whether or not this
10:23 is part this packet is part of an
10:25 established session you know in this
10:27 case it isn't it's the very first packet
10:29 that we've seen for this user and for
10:31 this session uh so
10:33 you know we're going to associate it
10:34 with a set of services and policies and
10:38 and tenants now the tenant is who the
10:40 user is we're going to decide
10:42 we're going to we're going to decide who
10:44 this user is and um and ultimately does
10:47 he have access to the services that he's
10:50 that this packet is destined for
10:53 and then finally we're going to
10:54 determine the policies that are
10:55 associated like how we're going to
10:57 deliver this session to the next hop and
11:00 ultimately on to its destination in this
11:02 case we determine our next top is
11:06 going to happen via
11:08 another one of our ssr brethren out
11:10 there in the network uh the one on the
11:13 right and so
11:15 we will go ahead and forward that packet
11:17 out onto the wire
11:18 and now we will we will effectively nap
11:21 the packet so now the packet is no
11:23 longer from source to destination it's
11:26 from waypoint one to waypoint two and
11:29 this is effectively just a nat of the
11:31 packet uh we nap the ips and the ports
11:34 associated with it
11:36 and the original
11:37 uh
11:38 source and destination important
11:40 protocol is encapsulated in a little bit
11:43 of metadata along with the associated
11:46 policies that were that were decided
11:48 upon at this first uh router
11:50 it's cryptographically signed
11:52 and it's sent out onto the wire to
11:55 traverse this network destined for
11:56 waypoint two
11:58 ultimately it finds its way to waypoint
12:00 two
12:01 waypoint two
12:02 first of all validates that uh that is
12:05 authentic that it's secure
12:07 uh and then begins to inspect the uh the
12:10 policies that were decided and it turns
12:13 around and for or programs its
12:15 forwarding plane for the rules that were
12:17 decided on for this session and
12:19 ultimately the packet comes out the
12:20 other side source and destined to you
12:24 know to and from the the end uh um
12:27 endpoints in source and destination as
12:30 if uh as if there was nothing in the
12:32 middle
12:33 as this session progresses
12:36 uh the metadata is effectively shut off
12:38 um once the forwarding planes are all
12:41 programmed in you know one or more ssrs
12:45 in this path uh they can shut off
12:48 metadata at that point so then it's just
12:49 effectively a nat no encapsulation no
12:52 overhead and uh you know the the the
12:56 good put um of of that session is is
12:59 really maximized because it's it's just
13:01 a simple nat at that point
13:03 and because this is a network field day
13:06 let's uh let's actually look at this in
13:09 action um
13:11 so what we're going to see here is a
13:13 packet
13:14 from our endpoint at
13:17 192 168 10 10 going to 10 2 0 4 this is
13:22 the original packet that first packet
13:24 hitting the the first hop ssr
13:27 and here it is egressing the first hop
13:29 ssr
13:30 so what you see here is that little bit
13:32 of metadata that i mentioned that's kind
13:35 of stuck um you know on the end of the
13:37 transport header
13:39 and um in this particular case we've
13:41 actually decrypted the metadata here
13:44 with our dissector so we can see some of
13:45 the the elements of it but we see that
13:48 original source and dest ips and ports
13:51 and all that good stuff
13:52 and we see the tenant that was aside
13:54 this came from a user in our finance
13:57 segment uh the service is inventory new
14:00 that's the name of our service it has
14:03 you know associated policies
14:05 uh and you know we're headed for our
14:07 peer
14:08 so it
14:08 transmits across the network this is
14:10 ultimately arriving at the next top
14:13 uh pier
14:14 um and you know we see it actually goes
14:18 through multiple hops
14:20 before finally it comes out the other
14:22 end and the metadata is is removed now
14:26 yeah go ahead before this is aaron
14:27 conaway
14:28 how are the users and the tenants
14:31 detected i guess the tenant's probably
14:33 from the user right but how is the user
14:35 identified
14:37 yeah great great question ultimately
14:39 there's a variety of ways that that
14:42 user tenancy is is identified probably
14:45 the simplest way is is similar to like
14:48 you might do on a zone based firewall
14:50 where you have uh you know an interface
14:53 a vlan or something like that that is
14:55 the you know that is the gateway for um
14:58 a collection of users
15:00 and and they're matched you know based
15:02 on their their ingress point uh into the
15:05 into the network um so that's that's
15:08 kind of the
15:08 uh the the simplest way um there's some
15:12 more advanced ways like like we can do
15:15 source uh prefix matching um you know
15:18 say the
15:20 say all these packets are flowing into a
15:22 router and there's multiple different
15:25 segments for which it's not the gateway
15:27 and it's kind of further back in the
15:29 network uh we can do source prefix
15:31 matching to figure those out
15:33 um
15:34 and then we have some prototypes of of
15:36 even some more advanced things where we
15:38 actually have drivers on an endpoint
15:41 like on a windows device
15:44 that will
15:45 that will actually associate the user to
15:47 a tenant and actually put metadata right
15:50 in the packet so that packet could
15:52 almost enter from anywhere uh and and
15:55 that tendency would be established by by
15:58 a driver right on the on the endpoint
15:59 that that is is a is a prototype i i
16:03 can't go into a whole lot of detail on
16:04 that one but uh um you know the the the
16:08 implementation they're sort of the way
16:10 that we identify tenancy today in the
16:12 implementation uh but certainly the
16:14 protocol and the technology was always
16:16 designed where uh this tendency could be
16:19 established in a variety of ways um you
16:21 know and ultimately once it hits the
16:23 router um and you know then that that
16:27 tenancy feeds into the services and and
16:29 the associated policy great question
16:32 thanks
16:33 hey reid i've got a question for you as
16:34 well while your flow is broken so yeah
16:36 looking at the packet capture here and
16:38 looking you know down the stack here am
16:40 i am i reading this right is the 128 t
16:42 is that payload or is that somewhere
16:43 else that you guys are putting that in
16:45 header data where does that sit exactly
16:48 yeah to ultimately to the you know to a
16:51 router in the middle that didn't
16:52 understand metadata it would look like
16:54 payload it's it's right after you know
16:56 it's put right on the end of the of the
16:58 transport um um
17:01 protocol uh you'll note here that our
17:04 source and desk ports are
17:07 are
17:07 different they're changed as well so you
17:09 know here here's waypoint one and
17:11 waypoint two of of the routers that you
17:14 know in the fabric that this is uh um
17:17 you know heading to and from
17:19 um every you know one unique thing about
17:22 this technology is every session in
17:25 equals a session out
17:27 meaning
17:28 um
17:29 every you know if when you think about a
17:31 traditional tunnel it's going to kind of
17:33 stack up all of all sessions in
17:36 and to devices in the middle that may be
17:38 doing ecmp based on flow hashing or
17:40 something like that
17:42 often they will have problems with that
17:43 because it will all look like you know
17:45 port 4500 port 4500 or something like
17:48 that um this
17:51 the
17:52 the
17:52 i the five tuple basically the outer
17:55 five tuple that we see here ultimately
17:57 becomes a flow key
17:59 uh not just for
18:01 you know the end ssr as it enters the
18:03 next the the the ssr that it's destined
18:05 to uh but you know other devices in the
18:08 middle will see these as unique flows as
18:11 well they'll they'll you know distribute
18:13 load and everything um and you you kind
18:16 of prevent some of those elephant pro
18:19 flow problems that you can get in other
18:20 places so just a couple clarifications
18:22 so this packet is this packet is sent
18:24 like at intervals to identify the flow
18:26 and then you've got you know whatever
18:27 your user payload data is or is this are
18:29 you borrowing from the payload in each
18:30 packet to make sure this metadata is
18:32 encoded how does that work yeah so this
18:35 this what we'll see here i'm going to
18:36 kind of go down through a few of these
18:38 here um
18:39 you know there's there's that forward
18:42 metadata in the first packet of a flow
18:44 that would that would um
18:46 again program the forwarding planes for
18:48 one or more ssrs in in the path
18:51 um
18:52 and as this flow progresses you're going
18:55 to see in the reverse direction there's
18:57 a little bit of metadata re sent in the
18:59 reverse direction and that metadata will
19:02 include sometimes it'll include things
19:04 like state of of
19:06 um like load state of the next hops you
19:08 know they're kind of talking to one
19:09 another here
19:11 so like it's an as needed this this is
19:12 sent as needed as you're needing to to
19:14 take action in the forwarding plane
19:16 exactly once this is established you
19:18 know there's no metadata it's it's just
19:20 there's nothing there there
19:23 as you alluded there's instances where a
19:25 little bit of metadata will be turned on
19:27 say we need to move a flow to a
19:28 different path
19:29 just turn on metadata move to a
19:31 different path um you know maybe there's
19:33 other kind of flow maintenance tasks
19:35 that will uh that will happen from time
19:37 to time but uh you know ultimately
19:40 unlike a
19:42 you know a tunnel with full
19:44 encapsulation uh this
19:46 metadata represents a
19:48 pretty much insignificant amount of
19:50 bandwidth in the overall life of of of
19:52 most flows gotcha one more question and
19:54 then i'll let you go what so what are
19:56 the implications for ipv6 uh you know
19:58 specifically since you don't have
20:00 fragmentation and you know mobile
20:02 networks are on the rise i think we went
20:04 over 51 of mobile usage in you know the
20:06 us in december for internet so we're
20:08 more mobile than we are you know
20:09 anything else and you've got some
20:10 slightly reduced mtus when you're
20:12 dealing with ipv6 payloads there what
20:14 are the amplification implications of
20:16 that when you're you know obviously
20:18 you're trying to build an sd-wan
20:19 connected ecosystem which includes
20:20 mobility devices a lot yeah um how does
20:23 that play into ipv6
20:24 yeah i mean ultimately our first
20:27 you know the the
20:29 step one is we try to prevent
20:31 fragmentation at all possible when it's
20:34 when it's required obviously the
20:36 the transit networks in the underlay can
20:39 be
20:39 uh can be ipv6 uh you can have ipv6 in
20:43 the in the outer you know you can kind
20:45 of weave in and out of ipv6 and ibv4 um
20:49 but one of the things that that
20:52 the
20:52 the routers do as they as they detect
20:55 paths
20:56 um between one another they will
20:59 actually monitor
21:00 you know there's kind of a process where
21:01 they discover the path say it's an ipv6
21:04 network um they discover the path
21:06 between themselves and they will
21:08 actually probe and discover things like
21:11 mtu size and and um you know kind of
21:15 understand if there's stateful devices
21:17 in the in the middle that could be
21:18 impacting or or
21:20 uh causing issues and then it'll deploy
21:23 prevention
21:24 you know and and and uh traversal
21:27 mechanisms uh as needed so um you know
21:30 in the case where you have a network in
21:33 the middle that that does require some
21:35 fragmentation um we we don't
21:38 in that fabric we don't do a traditional
21:41 ip fragment it would it would look on
21:44 the wire like a udp packet
21:46 um
21:47 but it it it transmits ultimately um um
21:51 sort of invisibly across that uh even
21:54 even if we'll take say that one
21:56 oversized ipv
21:58 or um
22:00 tcp packet and then transit it across
22:03 the fabric at broken up into two udp
22:05 packets
22:07 thank you guys do you guys spoof like
22:09 path mt discovery so that doesn't
22:11 actually have to happen on a discovery
22:13 basis because you know the mtu sizing
22:14 that you could do
22:16 sort of end to end so that way and hosts
22:18 when they're negotiating sort of
22:21 you know sort of kevin's point right you
22:22 can you can just answer back quickly and
22:25 tell them what size and set you want and
22:26 then because you guys are fragmenting
22:28 internally it doesn't matter
22:29 yeah yeah exactly can you do can you can
22:32 you actually do that do you actually
22:34 spoof pat mtu for v6 or is it not
22:36 something you do yeah we don't we don't
22:39 spoof it currently but but um you know
22:42 again
22:43 most times because we sort of
22:45 make that invisible to the end devices
22:48 um for the most part we do do some
22:50 things like mtu um or sorry mss clamping
22:53 where we will intelligently affect mss
22:56 again just to make it more efficient and
22:58 avoid fragmentation if at all possible
23:01 but we don't do that with the path mtu
23:03 at this time what are the control
23:06 mechanisms that kind of would prevent
23:08 um users from
23:10 being able to kind of uh
23:13 spoof their own source routing
23:16 yeah um you know
23:19 ultimately we
23:21 you know this is where we get into the
23:23 full stack um and some of you know using
23:26 some of our our uh um aps and switches
23:29 as well uh with the full stack and
23:31 juniper
23:33 you know we we are able to delegate a
23:35 little bit of that to the you know to
23:37 the wireless and wired access
23:39 um so by you know in a lot of these
23:42 environments by the time it hits the the
23:44 ssr
23:45 um you know there's already been some
23:48 element of of
23:50 you know access control relevant to
23:53 whatever their their access mechanism is
23:58 thanks
24:00 all right so
24:04 let's uh
24:06 let's just keep it moving here so um
24:09 yeah so that's kind of an overview of of
24:12 svr secure vector routing the protocol
24:14 how it works um you know but how does
24:16 this actually get deployed
24:18 uh in in you know in in real life and
24:22 and where do you put it how does it drop
24:24 into existing networks
24:25 uh
24:26 really you know as the routers um are
24:28 deployed at branches and data centers
24:30 and cloud edges these these those
24:32 waypoints that you saw
24:35 you know they kind of appear and and
24:38 become strategic points in the topology
24:40 to kind of to form an overlay fabric
24:43 and
24:44 you know the session smart routers
24:46 themselves are software based like we
24:47 mentioned running on x86 platforms and
24:50 they leverage uh kernel bypass
24:52 technology namely dpdk to streamline uh
24:56 the components
24:58 of of off-the-shelf hardware for
25:00 performance and latency
25:02 um and you know while the software
25:05 itself runs on commodity whitebox
25:07 platforms we have a versatile set of
25:09 certified platforms that we rigorously
25:12 and continuously test in our automated
25:14 test environments
25:15 to give the highest levels of uh you
25:18 know assurances for functionality
25:19 performance and support so the the
25:21 software scales up and down for small
25:24 branches small offices to large hubs uh
25:28 and and interconnect points alike and so
25:31 you know at the end of the day it forms
25:33 this uh um
25:36 this service-centric fabric uh that
25:38 becomes the sd-wan
25:40 now um you know at the end of the day um
25:44 software does need hardware to run on
25:46 and uh um as we alluded to uh at the
25:49 beginning of the presentation we're
25:51 excited to be introducing uh a branch
25:54 appliance for the ssr this is the ssr
25:58 100 line
26:00 and
26:03 you know these are ssr 120 and 130 these
26:05 are great small to medium branch
26:08 appliances and and you know really our
26:10 our aim with this is to simplify how we
26:13 get session smart routing into customers
26:15 hands
26:16 um
26:18 now
26:19 first party platforms aside the openness
26:22 and flexibility of the software remains
26:24 a really huge part of session smart
26:26 routing i mean you know
26:28 at the end of the day it's
26:30 platforms are simply a vehicle to get
26:32 session smart routing into more places
26:34 so networks and users can start enjoying
26:37 the benefits
26:38 and
26:39 you know here you see some of the
26:41 portfolio of third-party options um and
26:47 you know the some of the benefits here
26:49 in this era
26:51 current time as you guys know with
26:52 crippling supply train uh supply chain
26:55 shortages
26:56 um all over the industry we've we've
26:59 really seen that that you know thanks to
27:01 this uh ability of software and the
27:04 ability to run on more platforms
27:06 we've really been able to weather the
27:07 storm uh much better than most
27:12 so that's kind of hardware and a and a
27:16 you know a blast through uh or through
27:19 session smart routing and where it came
27:20 from and what's it all about and of
27:22 course we're we're
27:24 using that at the end of the day to
27:26 deploy
27:27 an sd-wan
27:36 you






