What is Spyware?
What is Spyware?
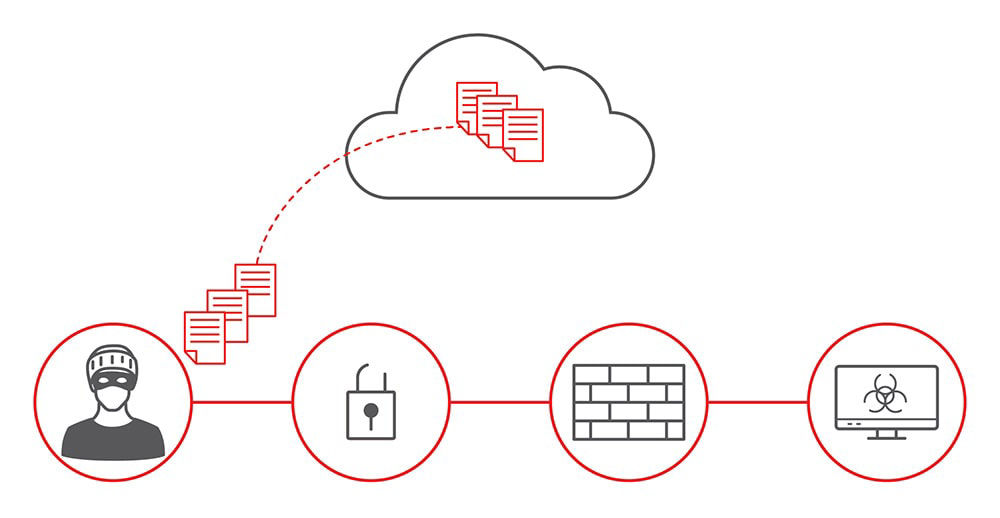
Spyware is software that can secretly record your activity on your computer. Most commonly, it is delivered through a free download or from an infected email attachment; this is known as a Trojan horse. A simple click is enough to install spyware on your computer without your knowledge. Once installed, spyware hides in the operating system and becomes transparent to you. This makes it difficult to detect and even harder to uninstall. With spyware running in the background, you are at risk of exposing confidential information, such as Web surfing habits, passwords, email addresses, and so on.
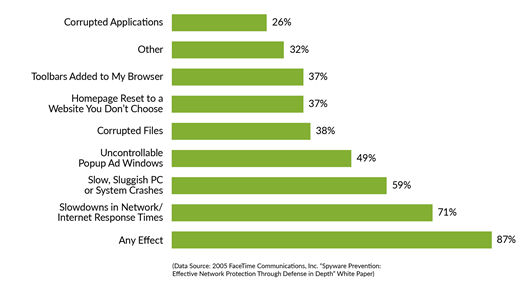
The bar chart shows the methods used by spyware and viruses to attack end users. (Source: FaceTime Study).
A Brief History of Spyware
The first use of the term “spyware” appeared was in 1995 in a Usenet article that targeted Microsoft's business model. In early 2000, it reappeared in a press release for a personal firewall product. This marked the beginning and acceptance of the “spyware” term.
What are the Common Signs of Spyware?
- You feel uncertain when you click a link, or start a Web search and it takes you to an unexpected location.
- A pop-up displays when you are not browsing.
- Your browser homepage settings have changed to an untrustworthy website or perhaps it has new toolbars.
- An antivirus scan runs although you have not purchased it.
- Your computer slows down when accessing websites on the Internet.
If you experience any of these symptoms, then you are under a spyware attack!
How Can I Get Rid of Spyware?
Uninstalling spyware can be a challenge. Spyware typically prevents you from uninstalling an application using the Control Panel, and may even reinstall automatically. With the evolution of such programs, it is increasingly more difficult to detect, identify, and prevent hackers from developing and implementing spyware.
If you determine that you are infected with spyware:
- Disconnect your computer from the network.
- Run a full scan or uninstall the infected programs or applications.
- If you still need assistance, contact your IT department for help.
How Can I Prevent Spyware?
The best way to prevent spyware from infecting the network is to develop a sound security policy for your organization and educate your employees. Simple training should include: what software to download and from which site, how to block pop-ups, reading any End User License Agreement before accepting it, refrain from clicking any suspicious attachments and links, never installing unknown software, and so on.
Always make a habit of backing up your data, keeping the software and security settings up to date, and using a reliable firewall and accurate antispyware. To keep your data safe and your users less vulnerable to attacks, gain more control over the applications, and protect your business assets against attacks with end-to-end, automated, and intelligent defense.
Juniper Networks offers a range of purpose-built, high-performance platforms that provide best-in-class security (SRX Series Next-Generation Firewalls) and routing for branch and regional offices, enterprises, and service providers of all sizes to combat the evolving cyber threat landscape.

