IKE for IPsec VPN
Learn about IKEv2 for IPsec VPN and its configuration in Junos OS.
Internet Key Exchange version 2 (IKEv2) is an IPsec based tunneling protocol. IKEv2 provides a secure VPN communication channel between peer VPN devices and defines negotiation and authentication for IPsec security associations (SAs) in a protected manner.
Use Feature Explorer to confirm platform and release support for specific features.
Review the Platform-Specific IKEv2 Responder Only Behavior section for notes related to your platform.
IKE and IPsec Packet Processing
IKE provides tunnel management for IPsec and authenticates end entities. IKE performs a Diffie-Hellman (DH) key exchange to generate an IPsec tunnel between network devices. The IPsec tunnels generated by IKE are used to encrypt, decrypt, and authenticate user traffic between the network devices at the IP layer.
IKE Packet Processing
When a cleartext packet arrives on a Juniper Networks device that requires tunneling, and no active Phase 2 SA exists for that tunnel, Junos OS begins IKE negotiations and drops the packet. The source and destination addresses in the IP packet header are those of the local and remote IKE gateways, respectively. In the IP packet payload, there is a UDP segment encapsulating an ISAKMP (IKE) packet. The format for IKE packets is the same for Phase 1 and Phase 2. See Figure 1.
Meanwhile, the source host has sent the dropped packet again. Typically, by the time the second packet arrives, IKE negotiations are complete, and Junos OS protects the packet and all subsequent packets in the session—with IPsec before forwarding it.
The Next Payload field contains a number indicating one of the following payload types:
-
0002—SA Negotiation Payload contains a definition for a Phase 1 or Phase 2 SA.
-
0004—Proposal Payload can be a Phase 1 or Phase 2 proposal.
-
0008—Transform Payload gets encapsulated in a proposal payload that gets encapsulated in a SA payload.
-
0010—Key Exchange (KE) Payload contains information necessary for performing a key exchange, such as a DH public value.
-
0020—Identification (IDx) Payload.
-
In Phase 1, IDii indicates the initiator ID, and IDir indicates the responder ID.
-
In Phase 2, IDui indicates the user initiator, and IDur indicates the user responder.
The IDs are IKE ID types such as FQDN, U-FQDN, IP address, and ASN.1_DN.
-
-
0040—Certificate (CERT) Payload.
-
0080—Certificate Request (CERT_REQ) Payload.
-
0100—Hash (HASH) Payload contains the digest output of a particular hash function.
-
0200—Signature (SIG) Payload contains a digital signature.
-
0400—Nonce (Nx) Payload contains some pseudorandom information necessary for the exchange).
-
0800—Notify Payload.
-
1000—ISAKMP Delete Payload.
-
2000—Vendor ID (VID) Payload can be included anywhere in Phase 1 negotiations. Junos OS uses it to mark support for NAT-T.
Each ISAKMP payload begins with the same generic header, as shown in Figure 2.
There can be multiple ISAKMP payloads chained together, with each subsequent payload type indicated by the value in the Next Header field. A value of 0000 indicates the last ISAKMP payload. See Figure 3 for an example.
IPsec Packet Processing
After IKE negotiations complete and the two IKE gateways have established Phase 1 and Phase 2 SAs, all subsequent packets are forwarded using the tunnel. If the Phase 2 SA specifies the Encapsulating Security Protocol (ESP) in tunnel mode, the packet looks like the one shown in Figure 4. The device adds two additional headers to the original packet that the initiating host sends.
As shown in Figure 4, the packet that the initiating host constructs includes the payload, the TCP header, and the inner IP header (IP1).
The router IP header (IP2), which Junos OS adds, contains the IP address of the remote gateway as the destination IP address and the IP address of the local router as the source IP address. Junos OS also adds an ESP header between the outer and inner IP headers. The ESP header contains information that allows the remote peer to properly process the packet when it receives it. See Figure 5.
The Next Header field indicates the type of data in the payload field. In tunnel mode, this value is 4, indicating an IP packet is contained within the payload. See Figure 6.
Introduction to IKE in Junos OS
IKE provides ways to exchange keys for encryption and authentication securely over an unsecured medium such as the Internet. IKE enables a pair of security gateways to: Dynamically establish a secure tunnel over which security gateways can exchange tunnel and key information. Set up user-level tunnels or SAs, including tunnel attribute negotiations and key management. These tunnels can also be refreshed and terminated on top of the same secure channel. IKE employs Diffie-Hellman methods and is optional in IPsec (the shared keys can be entered manually at the endpoints).
IKEv2 includes support for:
-
Route-based VPNs.
-
Site-to-site VPNs.
-
Dead peer detection.
-
Chassis cluster.
-
Pre-shared key authentication.
-
Certificate-based authentication.
-
Child SAs. An IKEv2 child SA is known as a Phase 2 SA in IKEv1. In IKEv2, a child SA cannot exist without the underlying IKE SA.
-
AutoVPN.
-
Dynamic endpoint VPN.
-
EAP is supported for Remote Access using IKEv2.
-
Traffic selectors.
IKEv2 does not support the following features:
-
Policy-based VPN.
-
VPN monitoring.
-
IP Payload Compression Protocol (IPComp).
- Configuring IKEv2 in Junos OS
- Understanding IKEv2 Configuration Payload
- Understanding Pico Cell Provisioning
Configuring IKEv2 in Junos OS
A VPN peer is configured as either IKEv1 or IKEv2. When a peer is configured as IKEv2, it cannot fall back to IKEv1 if its remote peer initiates IKEv1 negotiation. By default, Juniper Networks security devices are IKEv1 peers.
Use the version v2-only configuration statement at
the [edit security ike gateway gw-name
] hierarchy level to configure IKEv2.
The IKE version is displayed in the output of the show
security ike security-associations and show security ipsec
security-associations CLI operational commands.
Juniper Networks devices support up to four proposals for Phase 2 negotiations, allowing you to define how restrictive a range of tunnel parameters you will accept. Junos OS provides predefined standard, compatible, and basic Phase 2 proposal sets. You can also define custom Phase 2 proposals.
Understanding IKEv2 Configuration Payload
Configuration payload is an Internet Key Exchange version 2 (IKEv2) option offered to propagate provisioning information from a responder to an initiator. IKEv2 configuration payload is supported with route-based VPNs only.
RFC 5996, Internet Key Exchange Protocol Version 2 (IKEv2), defines 15 different configuration attributes that can be returned to the initiator by the responder. Table 1 describes the IKEv2 configuration attributes supported on the firewalls.
|
Attribute Type |
Value |
Description |
Length |
|---|---|---|---|
|
INTERNAL_IP4_ADDRESS |
1 |
Specifies an address on the internal network. Multiple internal addresses can be requested. The responder can send up to the number of addresses requested. |
0 or 4 octets |
|
INTERNAL_IP4_NETMASK |
2 |
Specifies the internal network's netmask value. Only one netmask value is allowed in the request and response messages (for example, 255.255.255.0), and it must be used only with an INTERNAL_IP4_ADDRESS attribute. |
0 or 4 octets |
|
INTERNAL_IP4_DNS |
3 |
Specifies an address of a DNS server within the network. Multiple DNS servers can be requested. The responder can respond with zero or more DNS server attributes. |
0 or 4 octets |
|
INTERNAL_IP4_NBNS |
4 |
Specifies an address of a NetBIOS name server (NBNS), for example, a WINS server, within the network. Multiple NBNS servers can be requested. The responder can respond with zero or more NBNS server attributes. |
0 or 4 octets |
|
INTERNAL_IP6_ADDRESS |
8 |
Specifies an address on the internal network. Multiple internal addresses can be requested. The responder can send up to the number of addresses requested. |
0 or 17 octets |
|
INTERNAL_IP6_DNS |
10 |
Specifies an address of a DNS server within the network. Multiple DNS servers can be requested. The responder can respond with zero or more DNS server attributes. |
0 or 16 octets |
For the IKE responder to provide the initiator with provisioning information, it must
acquire the information from a specified source such as a RADIUS server. Provisioning
information can also be returned from a DHCP server through a RADIUS server. On the RADIUS
server, the user information should not include an authentication password. The RADIUS
server profile is bound to the IKE gateway using the aaa access-profile
profile-name
configuration at the [edit security ike gateway
gateway-name
] hierarchy level.
Junos OS improved the IKEv2 configuration payload to support the following features:
-
Support for IPv4 and IPv6 local address pool. You can also assign a fixed IP address to a peer.
During IKE establishment, the initiator requests for an IPv4 address, IPv6 address, DNS address, or WINS address from the responder. After the responder has authenticated the initiator successfully, it assigns an IP address either from a local address pool or through RADIUS server. Depending on the configuration, this IP address is either assigned dynamically each time when a peer connects or assigned as a fixed IP address. If the RADIUS server responds with a framed pool, Junos OS assigns an IP address or information based on configuration from it's corresponding local pool. If you configure both local address pool and RADIUS server, the IP address allocated from RADIUS server takes precedence over the local pool. If you configure local IP address pool and the RADIUS server did not return any IP address, then local pool assigns the IP address to the request.
-
Additional option,
noneintroduced forauthentication-order. See authentication-order (Access Profile). -
RADIUS accounting start and stop messages inform the state of the tunnel or peer to the RADIUS server. These messages can be used for tracking purposes or notifications to subsystems such as a DHCP server.
Ensure that the RADIUS server support accounting start or stop messages. Also ensure that both the firewall and the RADIUS server have appropriate settings to track these messages.
-
Introduction of IPv6 support allows dual stack tunnels using configuration payload. During login process, IKE requests for both IPv4 and IPv6 addresses. AAA allow login only if all requested addresses have been allocated successfully. IKE terminates the negotiation if the requested IP is not allocated.
In a route-based VPN, secure tunnel (st0) interfaces operate in either point-to-multipoint or point-to-point mode. Address assignment through the IKEv2 configuration payload is now supported for point-to-multipoint or point-to-point mode. For point-to-multipoint interfaces, the interfaces must be numbered and the addresses in the configuration payload INTERNAL_IP4_ADDRESS attribute type must be within the subnetwork range of the associated point-to-multipoint interface.
You
can configure a common password for IKEv2 configuration payload requests for an IKE
gateway configuration. The common password in the range of 1 to 128 characters allows
the administrator to define a common password. This password is used between the
firewall
and the RADIUS server when the
firewall
requesting an IP address on behalf of a remote IPsec peer using IKEv2 configuration
payload. RADIUS server matches the credentials before it provides any IP information to
the
firewall
for the configuration payload request. You can configure the common password using
config-payload-password configured-password
configuration statement at [edit security ike gateway gateway-name aaa
access-profile access-profile-name] hierarchy level.
Both the firewall and the RADIUS server must have the same password configured and the radius server should be configured to use Password Authentication Protocol (PAP) as the authentication protocol. Without this, tunnel establishment will not be successful.
Figure 7 shows a typical workflow for a IKEv2 Configuration Payload.
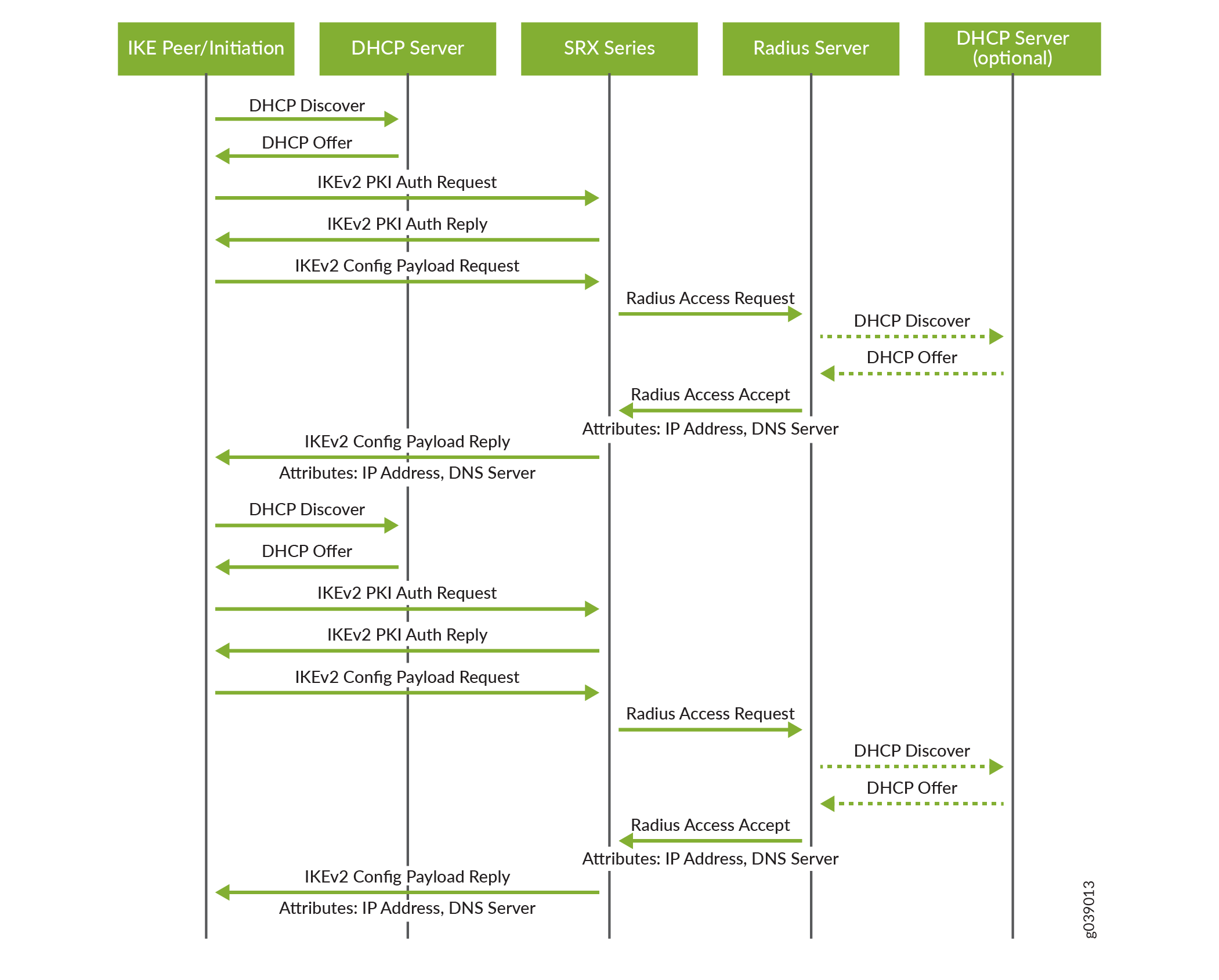
The IKEv2 configuration payload feature is supported for both point-to-multipoint secure tunnel (st0) interfaces and point-to-point interfaces. Point-to-multipoint interfaces must be numbered, and the addresses provided in the configuration payload must be within the subnetwork range of the associated point-to-multipoint interface.
Understanding Pico Cell Provisioning
IKEv2 configuration payload can be used to propagate provisioning information from an IKE responder, such as the firewall, to multiple initiators, such as LTE pico cell base stations in a cellular network. The pico cells ship from the factory with a standard configuration that allows them to connect to the firewall, but the pico cell provisioning information is stored on one or more provisioning servers within a protected network. The pico cells receive full provisioning information after establishing secure connections with the provisioning servers.
The workflow required to bootstrap and provision a pico cell and introduce it to service includes four distinct stages:
-
Initial addresses acquisition—The pico cell ships from the factory with the following information:
-
Configuration for the secure gateway tunnel to the firewall
-
Digital certificate issued by the manufacturer
-
Fully qualified domain name (FQDN) of the provisioning servers that lie within the protected network
The pico cell boots up and acquires an address to be used for IKE negotiation from a DHCP server. A tunnel is then built to the secure gateway on the firewall using this address. An address for Operation, Administration, and Management (OAM) traffic is also assigned by the DHCP server for use on the protected network.
-
-
Pico cell provisioning—Using its assigned OAM traffic address, the pico cell requests its provisioning information—typically operator certificate, license, software, and configuration information—from servers within the protected network.
-
Reboot—The pico cell reboots and uses the acquired provisioning information to make it specific to the service provider’s network and operation model.
-
Service provision—When the pico cell enters service, it uses a single certificate that contains distinguished name (DN) and subject alternative name values with a FQDN to build two tunnels to the secure gateway on the firewall: one for OAM traffic and the other for Third-Generation Partnership Project (3GPP) data traffic.
See Also
IKE Proposal
The IKE configuration defines the algorithms and keys used to establish the secure IKE connection with the peer security gateway. You can configure one or more IKE proposals. Each proposal is a list of IKE attributes to protect the IKE connection between the IKE host and its peer.
To configure an IKE proposal, include the proposal statement and specify a
name at the [edit security ike ] hierarchy level:
IKE Policy
An IKE policy defines a combination of security parameters (IKE proposals) to be used during IKE negotiation. It defines a peer address and the proposals needed for that connection. Depending on which authentication method is used, it defines the preshared key (PSK) for the given peer or the local certificate. During the IKE negotiation, IKE looks for an IKE policy that is the same on both peers. The peer that initiates the negotiation sends all its policies to the remote peer, and the remote peer tries to find a match. A match is made when both policies from the two peers have a proposal that contains the same configured attributes. If the lifetimes are not identical, the shorter lifetime between the two policies (from the host and peer) is used. The configured PSK must also match its peer.
First, you configure one or more IKE proposals; then you associate these proposals with an IKE policy.
To configure an IKE policy, include the policy statement and specify a
policy name at the [edit security ike] hierarchy level:
Rekeying and Reauthentication
Overview
With IKEv2, rekeying and reauthentication are separate processes. Rekeying establishes new keys for the IKE security association (SA) and resets message ID counters, but it does not reauthenticate the peers. Reauthentication verifies that VPN peers retain their access to authentication credentials. Reauthentication establishes new keys for the IKE SA and child SAs; rekeys of any pending IKE SA or child SA are no longer needed. After the new IKE and child SAs are created, the old IKE and child SAs are deleted.
IKEv2 reauthentication is disabled by default. You enable reauthentication by configuring a reauthentication frequency value between 1 and 100. The reauthentication frequency is the number of IKE rekeys that occurs before reauthentication occurs. For example, if the configured reauthentication frequency is 1, reauthentication occurs every time there is an IKE rekey. If the configured reauthentication frequency is 2, reauthentication occurs at every other IKE rekey. If the configured reauthentication frequency is 3, reauthentication occurs at every third IKE rekey, and so on.
You configure the reauthentication frequency with the reauth-frequency statement at the [edit security ike policy policy-name] hierarchy level. Reauthentication is disabled by setting
the reauthentication frequency to 0 (the default). Reauthentication
frequency is not negotiated by peers, and each peer can have its own
reauthentication frequency value.
Supported Features
IKEv2 reauthentication is supported with the following features:
IKEv2 initiators or responders
Dead peer detection (DPD)
Virtual routers and secure tunnel (st0) interfaces in virtual routers
Network Address Translation traversal (NAT-T)
Chassis clusters in active-active and active-passive mode
In-service software upgrade (ISSU)
Upgrade or insertion of a new Services Processing Unit (SPU) using the in-service hardware upgrade (ISHU) procedure
Limitations
Note the following caveats when using IKEv2 reauthentication:
With NAT-T, a new IKE SA can be created with different ports from the previous IKE SA. In this scenario, the old IKE SA might not be deleted.
In a NAT-T scenario, the initiator behind the NAT device can become the responder after reauthentication. If the NAT session expires, the NAT device might discard new IKE packets that might arrive on a different port. NAT-T keepalive or DPD must be enabled to keep the NAT session alive. For AutoVPN, we recommend that the reauthentication frequency configured on the spokes be smaller than the reauthentication frequency configured on the hub.
Based on the reauthentication frequency, a new IKE SA can be initiated by either the initiator or the responder of the original IKE SA. Because Extensible Authentication Protocol (EAP) authentication and configuration payload require the IKE SA to be initiated by the same party as the original IKE SA, reauthentication is not supported with EAP authentication or configuration payload.
IKE Authentication (Certificate-Based Authentication)
Multilevel Hierarchy for Certificate Authentication
Certificate-based authentication is an authentication method supported on firewalls during IKE negotiation. In large networks, multiple certificate authorities (CAs) can issue end entity (EE) certificates to their respective end devices. It is common to have separate CAs for individual locations, departments, or organizations.
When a single-level hierarchy for certificate-based authentication is employed, all EE certificates in the network must be signed by the same CA. All firewall devices must have the same CA certificate enrolled for peer certificate validation. The certificate payload sent during IKE negotiation only contains EE certificates.
Alternatively, the certificate payload sent during IKE negotiation can contain a chain of EE and CA certificates. A certificate chain is the list of certificates required to validate a peer’s EE certificate. The certificate chain includes the EE certificate and any CA certificates that are not present in the local peer.
The network administrator needs to ensure that all peers participating in an IKE negotiation have at least one common trusted CA in their respective certificate chains. The common trusted CA does not have to be the root CA. The number of certificates in the chain, including certificates for EEs and the topmost CA in the chain, cannot exceed 10.
Validation of a configured IKE peer can be done with a specified CA server or group of CA servers. With certificate chains, the root CA must match the trusted CA group or CA server configured in the IKE policy.
In the example CA hierarchy shown in Figure 8, Root-CA is the common trusted CA for all devices in the network. Root-CA issues CA certificates to the engineering and sales CAs, which are identified as Eng-CA and Sales-CA, respectively. Eng-CA issues CA certificates to the development and quality assurance CAs, which are identified as Dev-CA and Qa-CA, respectively. Host-A receives its EE certificate from Dev-CA while Host-B receives its EE certificate from Sales-CA.
Each end device needs to be loaded with the CA certificates in its hierarchy. Host-A must have Root-CA, Eng-CA, and Dev-CA certificates; Sales-CA and Qa-CA certificates are not necessary. Host-B must have Root-CA and Sales-CA certificates. Certificates can be loaded manually in a device or enrolled using the Simple Certificate Enrollment Process (SCEP).
Each end device must be configured with a CA profile for each CA in the certificate chain. The following output shows the CA profiles configured on Host-A:
admin@host-A# show security
pki {
ca-profile Root-CA {
ca-identity Root-CA;
enrollment {
url “www.example.net/scep/Root/”;
}
}
ca-profile Eng-CA {
ca-identity Eng-CA;
enrollment {
url “www.example.net/scep/Eng/”;
}
}
ca-profile Dev-CA {
ca-identity Dev-CA;
enrollment {
url “www.example.net/scep/Dev/”;
}
}
}The following output shows the CA profiles configured on Host-B:
admin@host-B# show security
pki {
ca-profile Root-CA {
ca-identity Root-CA;
enrollment {
url “www.example.net/scep/Root/”;
}
}
ca-profile Sales-CA {
ca-identity Sales-CA;
enrollment {
url “www.example.net/scep/Sales/”;
}
}
}See Also
Configure Multiple Certificate Types to Establish IKE and IPsec SA
Learn how to configure and manage multiple certificate types.
This example shows how to configure multiple certificate types to establish IKE and IPsec SA.
Starting in Junos OS Release 22.4R1, you can establish tunnels irrespective of the
certificate type used on the initiator and responder if authentication-method is configured as
certificates in IKE proposal using the set security ike proposal
ike_proposal_name authentication-method certificates
command.
You can view the certificate enrolled using show security pki local-certificate
certificate-id certificate-name detail command.
You can verify the enrolled certificate using the request security pki
local-certificate verify certificate-id certificate-name
command.
Requirements
Before you begin:
-
Ensure that you have certificates enrolled on your devices, see Certificate Enrollment.
You can verify the certificates enrolled on your devices using the
request security pki local-certificate certificate-id certificate-name detailcommand. -
Ensure that you have IKE package installed, to verify the installed IKE package use the
show version | match ikeoperational command.If you don't have the IKE package installed on the device, you can install the IKE package using the operational command
request system software add optional://junos-ike.tgz, for more information, see Enabling IPsec VPN Feature Set.
Overview
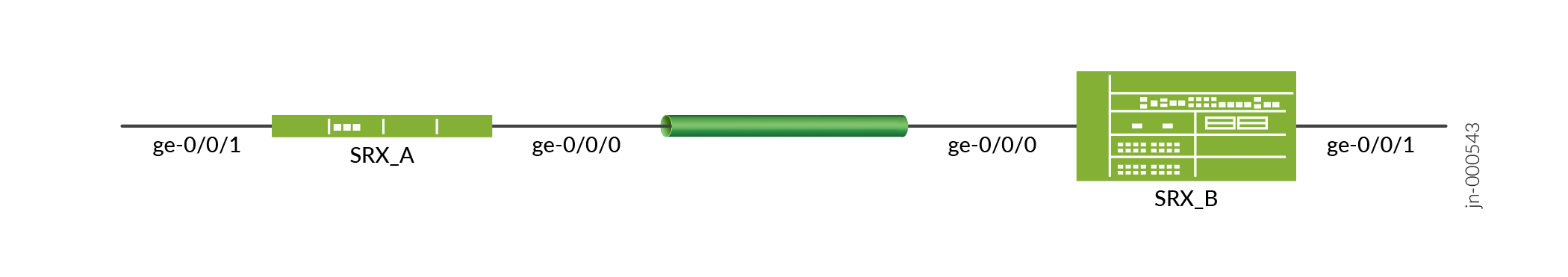
This example configures multiple certificate types to establish IKE and IPsec SA between on SRX_A and on SRX_B.
In this example, we have enrolled the RSA certificate on SRX_A and the ECDSA certificate on SRX_B devices. For more information about how to install the certificates, see Certificate Enrollment.
| Device Name | Interface Used | IKE Gateway Address | IKE Gateway Local IP Address |
|---|---|---|---|
| SRX_A | ge-0/0/0 | 192.168.1.2 | 192.168.1.1 |
| SRX_B | ge-0/0/0 | 192.168.1.1 | 192.168.1.2 |
Topology
The Figure 9 describes topology for multiple certificate types support configuration.
Configuration
Configuring SRX_A
CLI Quick Configuration
To quickly configure this example, copy the following commands, paste them into a text
file, remove any line breaks, change any details necessary to match your network
configuration, copy and paste the commands into the CLI at the [edit]
hierarchy level, and then enter commit from configuration mode.
set interfaces ge-0/0/0 unit 0 family inet address 192.168.1.1/24 set interfaces ge-0/0/1 unit 0 family inet address 172.16.1.1/24 set interfaces st0 unit 1 family inet set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces ge-0/0/1 set security zones security-zone untrust host-inbound-traffic system-services ike set security zones security-zone untrust interfaces ge-0/0/0 set security zones security-zone VPN interfaces st0.1 set security policies from-zone VPN to-zone trust policy 1 match source-address any set security policies from-zone VPN to-zone trust policy 1 match destination-address any set security policies from-zone VPN to-zone trust policy 1 match application any set security policies from-zone VPN to-zone trust policy 1 then permit set security policies from-zone trust to-zone VPN policy 1 match source-address any set security policies from-zone trust to-zone VPN policy 1 match destination-address any set security policies from-zone trust to-zone VPN policy 1 match application any set security policies from-zone trust to-zone VPN policy 1 then permit set security policies default-policy deny-all set security ike proposal IKE_PROP authentication-method certificates set security ike proposal IKE_PROP dh-group group5 set security ike proposal IKE_PROP authentication-algorithm sha-256 set security ike proposal IKE_PROP encryption-algorithm aes-128-cbc set security ike policy IKE_POL proposals IKE_PROP set security ike policy IKE_POL certificate local-certificate r0_rsa_crt set security ike gateway IKE_GW ike-policy IKE_POL set security ike gateway IKE_GW address 192.168.1.2 set security ike gateway IKE_GW external-interface ge-0/0/0 set security ike gateway IKE_GW local-address 192.168.1.1 set security ike gateway IKE_GW version v2-only set security ipsec proposal IPSEC_PROP protocol esp set security ipsec proposal IPSEC_PROP authentication-algorithm hmac-sha-256-128 set security ipsec proposal IPSEC_PROP encryption-algorithm aes-192-cbc set security ipsec policy IPSEC_POL proposals IPSEC_PROP set security ipsec vpn IPSEC_VPN bind-interface st0.1 set security ipsec vpn IPSEC_VPN ike gateway IKE_GW set security ipsec vpn IPSEC_VPN ike ipsec-policy IPSEC_POL set security ipsec vpn IPSEC_VPN establish-tunnels on-traffic
Step-by-step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For instructions on how to do that, see CLI Configuration Mode Overview in the CLI User Guide.
To configure multiple certificate types to establish IKE and IPsec SA:
-
View the certificates enrolled on your devices using the
show security pki local-certificate certificate-id certificate-name detailcommand.Install the certificate on your device if your device does not have the certificates enrolled. For more information, see Certificate Enrollment.
-
Configure interfaces.
user@srxa# set interfaces ge-0/0/0 unit 0 family inet address 192.168.1.1/24 user@srxa# set interfaces ge-0/0/1 unit 0 family inet address 172.16.1.1/24 user@srxa# set interfaces st0 unit 1 family inet
-
Configure security zones and the security policy.
user@srxa# set security zones security-zone trust host-inbound-traffic system-services all user@srxa# set security zones security-zone trust host-inbound-traffic protocols all user@srxa# set security zones security-zone trust interfaces ge-0/0/1 user@srxa# set security zones security-zone untrust host-inbound-traffic system-services ike user@srxa# set security zones security-zone untrust interfaces ge-0/0/0 user@srxa# set security zones security-zone VPN interfaces st0.1 user@srxa# set security policies from-zone VPN to-zone trust policy 1 match source-address any user@srxa# set security policies from-zone VPN to-zone trust policy 1 match destination-address any user@srxa# set security policies from-zone VPN to-zone trust policy 1 match application any user@srxa# set security policies from-zone VPN to-zone trust policy 1 then permit user@srxa# set security policies from-zone trust to-zone VPN policy 1 match source-address any user@srxa# set security policies from-zone trust to-zone VPN policy 1 match destination-address any user@srxa# set security policies from-zone trust to-zone VPN policy 1 match application any user@srxa# set security policies from-zone trust to-zone VPN policy 1 then permit user@srxa# set security policies default-policy deny-all
-
Configure the IKE proposal.
[edit] user@srxa# set security ike proposal IKE_PROP authentication-method certificates user@srxa# set security ike proposal IKE_PROP dh-group group5 user@srxa# set security ike proposal IKE_PROP authentication-algorithm sha-256 user@srxa# set security ike proposal IKE_PROP encryption-algorithm aes-128-cbc
-
Configure the IKE policy.
[edit] user@srxa# set security ike policy IKE_POL proposals IKE_PROP user@srxa# set security ike policy IKE_POL certificate local-certificate r0_rsa_crt
-
Configure the IKE gateway.
[edit] user@srxa# set security ike gateway IKE_GW ike-policy IKE_POL user@srxa# set security ike gateway IKE_GW address 192.168.1.2 user@srxa# set security ike gateway IKE_GW external-interface ge-0/0/0 user@srxa# set security ike gateway IKE_GW local-address 192.168.1.1 user@srxa# set security ike gateway IKE_GW version v2-only
-
Configure the IPsec proposal.
[edit] user@srxa# set security ipsec proposal IPSEC_PROP protocol esp user@srxa# set security ipsec proposal IPSEC_PROP authentication-algorithm hmac-sha-256-128 user@srxa# set security ipsec proposal IPSEC_PROP encryption-algorithm aes-192-cbc
-
Configure the IPsec policy.
[edit] user@srxa# set security ipsec policy IPSEC_POL proposals IPSEC_PROP
-
Configure the IPsec VPN.
[edit] user@srxa# set security ipsec vpn IPSEC_VPN bind-interface st0.1 user@srxa# set security ipsec vpn IPSEC_VPN ike gateway IKE_GW user@srxa# set security ipsec vpn IPSEC_VPN ike ipsec-policy IPSEC_POL user@srxa# set security ipsec vpn IPSEC_VPN establish-tunnels on-traffic
Results
From configuration mode, confirm your configuration by entering the show
interfaces, show security ike and, show security
ipsec commands. If the output does not display the intended configuration,
repeat the configuration instructions in this example to correct it.
[edit]
user@srxa# show interfaces
ge-0/0/0 {
description untrust;
unit 0 {
family inet {
address 192.168.1.1/24;
}
}
}
ge-0/0/1 {
description trust;
unit 0 {
family inet {
address 172.16.1.1/24;
}
}
}
st0 {
unit 1 {
family inet;
}
}
[edit]
user@srxa# show security ike
proposal IKE_PROP {
authentication-method certificates;
dh-group group5;
authentication-algorithm sha-256;
encryption-algorithm aes-128-cbc;
}
policy IKE_POL {
proposals IKE_PROP;
certificate {
local-certificate r0_crt_rsa;
}
}
gateway IKE_GW {
ike-policy IKE_POL;
address 192.168.1.2;
external-interface ge-0/0/0;
local-address 192.168.1.1;
version v2-only;
}
[edit]
user@srxa# show security ipsec
proposal IPSEC_PROP {
protocol esp;
authentication-algorithm hmac-sha-256-128;
encryption-algorithm aes-192-cbc;
}
policy IPSEC_POL {
proposals IPSEC_PROP;
}
vpn IPSEC_VPN {
bind-interface st0.1;
ike {
gateway IKE_GW;
ipsec-policy IPSEC_POL;
}
establish-tunnels on-traffic;
}
If you are done configuring the device, enter commit from
configuration mode.
Configuring SRX_B
CLI Quick Configuration
To quickly configure this example, copy the following commands, paste them into a text
file, remove any line breaks, change any details necessary to match your network
configuration, copy and paste the commands into the CLI at the [edit]
hierarchy level, and then enter commit from configuration mode.
set interfaces ge-0/0/0 unit 0 family inet address 192.168.1.2/24 set interfaces ge-0/0/1 unit 0 family inet address 172.18.1.2/24 set interfaces st0 unit 1 family inet set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces ge-0/0/1 set security zones security-zone untrust host-inbound-traffic system-services ike set security zones security-zone untrust interfaces ge-0/0/0 set security zones security-zone VPN interfaces st0.1 set security policies from-zone VPN to-zone trust policy 1 match source-address any set security policies from-zone VPN to-zone trust policy 1 match destination-address any set security policies from-zone VPN to-zone trust policy 1 match application any set security policies from-zone VPN to-zone trust policy 1 then permit set security policies from-zone trust to-zone VPN policy 1 match source-address any set security policies from-zone trust to-zone VPN policy 1 match destination-address any set security policies from-zone trust to-zone VPN policy 1 match application any set security policies from-zone trust to-zone VPN policy 1 then permit set security policies default-policy deny-all set security ike proposal IKE_PROP authentication-method certificates set security ike proposal IKE_PROP dh-group group5 set security ike proposal IKE_PROP authentication-algorithm sha-256 set security ike proposal IKE_PROP encryption-algorithm aes-128-cbc set security ike policy IKE_POL proposals IKE_PROP set security ike policy IKE_POL certificate local-certificate r1_crt_ecdsa384 set security ike gateway IKE_GW ike-policy IKE_POL set security ike gateway IKE_GW address 192.168.1.1 set security ike gateway IKE_GW external-interface ge-0/0/0 set security ike gateway IKE_GW local-address 192.168.1.2 set security ike gateway IKE_GW version v2-only set security ipsec proposal IPSEC_PROP protocol esp set security ipsec proposal IPSEC_PROP authentication-algorithm hmac-sha-256-128 set security ipsec proposal IPSEC_PROP encryption-algorithm aes-192-cbc set security ipsec policy IPSEC_POL proposals IPSEC_PROP set security ipsec vpn IPSEC_VPN bind-interface st0.1 set security ipsec vpn IPSEC_VPN ike gateway IKE_GW set security ipsec vpn IPSEC_VPN ike ipsec-policy IPSEC_POL set security ipsec vpn IPSEC_VPN establish-tunnels on-traffic
Step-by-step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For instructions on how to do that, see CLI Configuration Mode Overview in the CLI User Guide.
To configure multiple certificate types to establish IKE and IPsec SA:
-
View the certificates enrolled on your devices using the
request security pki local-certificate certificate-id certificate-name detailcommand.Install the certificate on your device if your device does not have the certificates enrolled. For more information, see Certificate Enrollment.
-
Configure interfaces.
user@srxb# set interfaces ge-0/0/0 unit 0 family inet address 192.168.1.2/24 user@srxb# set interfaces ge-0/0/1 unit 0 family inet address 172.18.1.2/24 user@srxb# set interfaces st0 unit 1 family inet
-
Configure security zones and the security policy.
user@srxb# set security zones security-zone trust host-inbound-traffic system-services all user@srxb# set security zones security-zone trust host-inbound-traffic protocols all user@srxb# set security zones security-zone trust interfaces ge-0/0/1 user@srxb# set security zones security-zone untrust host-inbound-traffic system-services ike user@srxb# set security zones security-zone untrust interfaces ge-0/0/0 user@srxb# set security zones security-zone VPN interfaces st0.1 user@srxb# set security policies from-zone VPN to-zone trust policy 1 match source-address any user@srxb# set security policies from-zone VPN to-zone trust policy 1 match destination-address any user@srxb# set security policies from-zone VPN to-zone trust policy 1 match application any user@srxb# set security policies from-zone VPN to-zone trust policy 1 then permit user@srxb# set security policies from-zone trust to-zone VPN policy 1 match source-address any user@srxb# set security policies from-zone trust to-zone VPN policy 1 match destination-address any user@srxb# set security policies from-zone trust to-zone VPN policy 1 match application any user@srxb# set security policies from-zone trust to-zone VPN policy 1 then permit user@srxb# set security policies default-policy deny-all
-
Configure the IKE proposal.
[edit] user@srxb# set security ike proposal IKE_PROP authentication-method certificates user@srxb# set security ike proposal IKE_PROP dh-group group5 user@srxb# set security ike proposal IKE_PROP authentication-algorithm sha-256 user@srxb# set security ike proposal IKE_PROP encryption-algorithm aes-128-cbc
-
Configure the IKE policy.
[edit] user@srxb# set security ike policy IKE_POL proposals IKE_PROP user@srxb# set security ike policy IKE_POL certificate local-certificate r1_crt_ecdsa384
-
Configure the IKE gateway.
[edit] user@srxb# set security ike gateway IKE_GW ike-policy IKE_POL user@srxb# set security ike gateway IKE_GW address 192.168.1.1 user@srxb# set security ike gateway IKE_GW external-interface ge-0/0/0 user@srxb# set security ike gateway IKE_GW local-address 192.168.1.2 user@srxb# set security ike gateway IKE_GW version v2-only
-
Configure the IPsec proposal.
[edit] user@srxb# set security ipsec proposal IPSEC_PROP protocol esp user@srxb# set security ipsec proposal IPSEC_PROP authentication-algorithm hmac-sha-256-128 user@srxb# set security ipsec proposal IPSEC_PROP encryption-algorithm aes-192-cbc
-
Configure the IPsec policy.
[edit] user@srxb# set security ipsec policy IPSEC_POL proposals IPSEC_PROP
-
Configure the IPsec VPN.
[edit] user@srxb# set security ipsec vpn IPSEC_VPN bind-interface st0.1 user@srxb# set security ipsec vpn IPSEC_VPN ike gateway IKE_GW user@srxb# set security ipsec vpn IPSEC_VPN ike ipsec-policy IPSEC_POL user@srxb# set security ipsec vpn IPSEC_VPN establish-tunnels immediately
Results
From configuration mode, confirm your configuration by entering the show
interfaces, show security ike and, show security
ipsec commands. If the output does not display the intended configuration,
repeat the configuration instructions in this example to correct it.
[edit]
user@srxb# show interfaces
ge-0/0/0 {
description untrust;
unit 0 {
family inet {
address 192.168.1.2/24;
}
}
}
ge-0/0/1 {
description trust;
unit 0 {
family inet {
address 172.18.1.2/24;
}
}
}
st0 {
unit 1 {
family inet;
}
}
[edit]
user@srxb# show security ike
proposal IKE_PROP {
authentication-method certificates;
dh-group group5;
authentication-algorithm sha-256;
encryption-algorithm aes-128-cbc;
}
policy IKE_POL {
proposals IKE_PROP;
certificate {
local-certificate r1_crt_ecdsa384;
}
}
gateway IKE_GW {
ike-policy IKE_POL;
address 192.168.1.1;
external-interface ge-0/0/0;
local-address 192.168.1.2;
version v2-only;
}
[edit]
user@srxb# show security ipsec
proposal IPSEC_PROP {
protocol esp;
authentication-algorithm hmac-sha-256-128;
encryption-algorithm aes-192-cbc;
}
policy IPSEC_POL {
proposals IPSEC_PROP;
}
vpn IPSEC_VPN {
bind-interface st0.1;
ike {
gateway IKE_GW;
ipsec-policy IPSEC_POL;
}
establish-tunnels immediately;
}
If you are done configuring the device, enter commit from
configuration mode.
Verification
Confirm that the configuration is working properly.
Verify SRX_A
The sample outputs shown are on SRX-A.
Purpose
Verify the IPsec Phase 2 status.
Action
From operational mode, enter the show security ike
security-associations command.
user@srxa> show security ike security-associations Index State Initiator cookie Responder cookie Mode Remote Address 32 UP 6723643250f0f357 f6295f11b0d7c8ab IKEv2 192.168.1.2
From operational mode, enter the show security ipsec
security-associations command.
user@srxa> show security ipsec security-associations Total active tunnels: 1 Total IPsec sas: 1 ID Algorithm SPI Life:sec/kb Mon lsys Port Gateway <500033 ESP:aes-cbc-192/sha256 0x5f156c1b 2750/ unlim - root 500 192.168.1.2 >500033 ESP:aes-cbc-192/sha256 0x7ea065e7 2750/ unlim - root 500 192.168.1.2
From operational mode, enter the show security ike security-associations
detail command.
user@srxa> show security ike security-associations detail
IKE peer 192.168.1.2, Index 32, Gateway Name: IKE_GW
Role: Responder, State: UP
Initiator cookie: 6723643250f0f357, Responder cookie: f6295f11b0d7c8ab
Exchange type: IKEv2, Authentication method: RSA-signatures
Local gateway interface: ge-0/0/0.0
Routing instance: default
Local: 192.168.1.1:500, Remote: 192.168.1.2:500
Lifetime: Expires in 28165 seconds
Reauth Lifetime: Disabled
IKE Fragmentation: Enabled, Size: 576
Remote Access Client Info: Unknown Client
Peer ike-id: 192.168.1.2
AAA assigned IP: 0.0.0.0
Algorithms:
Authentication : hmac-sha256-128
Encryption : aes128-cbc
Pseudo random function: hmac-sha256
Diffie-Hellman group : DH-group-5
Traffic statistics:
Input bytes : 1346
Output bytes : 1887
Input packets: 3
Output packets: 4
Input fragmented packets: 2
Output fragmented packets: 3
IPSec security associations: 2 created, 0 deleted
Phase 2 negotiations in progress: 1
IPSec Tunnel IDs: 500033
Negotiation type: Quick mode, Role: Responder, Message ID: 0
Local: 192.168.1.1:500, Remote: 192.168.1.2:500
Local identity: 192.168.1.1
Remote identity: 192.168.1.2
Flags: IKE SA is created
IPsec SA Rekey CREATE_CHILD_SA exchange stats:
Initiator stats: Responder stats:
Request Out : 0 Request In : 0
Response In : 0 Response Out : 0
No Proposal Chosen In : 0 No Proposal Chosen Out : 0
Invalid KE In : 0 Invalid KE Out : 0
TS Unacceptable In : 0 TS Unacceptable Out : 0
Res DH Compute Key Fail : 0 Res DH Compute Key Fail: 0
Res Verify SA Fail : 0
Res Verify DH Group Fail: 0
Res Verify TS Fail : 0
From operational mode, enter the show security ipsec security-associations
detail command.
user@srxa> show security ipsec security-associations detail
ID: 500033 Virtual-system: root, VPN Name: IPSEC_VPN
Local Gateway: 192.168.1.1, Remote Gateway: 192.168.1.2
Local Identity: ipv4(0.0.0.0-255.255.255.255)
Remote Identity: ipv4(0.0.0.0-255.255.255.255)
TS Type: proxy-id
Version: IKEv2
PFS group: N/A
DF-bit: clear, Copy-Outer-DSCP Disabled, Bind-interface: st0.1, Tunnel MTU: 0, Policy-name: IPSEC_POL
Port: 500, Nego#: 0, Fail#: 0, Def-Del#: 0 Flag: 0
Multi-sa, Configured SAs# 0, Negotiated SAs#: 0
Tunnel events:
Thu Mar 09 2023 22:41:36: IPsec SA negotiation succeeds (1 times)
Location: FPC 0, PIC 0, KMD-Instance 0
Anchorship: Thread 1
Distribution-Profile: default-profile
Direction: inbound, SPI: 0x5f156c1b, AUX-SPI: 0
, VPN Monitoring: -
Hard lifetime: Expires in 2895 seconds
Lifesize Remaining: Unlimited
Soft lifetime: Expires in 2286 seconds
Mode: Tunnel(0 0), Type: dynamic, State: installed
Protocol: ESP, Authentication: hmac-sha256-128, Encryption: aes-cbc (192 bits)
Anti-replay service: counter-based enabled, Replay window size: 64
Extended-Sequence-Number: Disabled
tunnel-establishment: establish-tunnels-on-traffic
IKE SA Index: 32
Direction: outbound, SPI: 0x7ea065e7, AUX-SPI: 0
, VPN Monitoring: -
Hard lifetime: Expires in 2895 seconds
Lifesize Remaining: Unlimited
Soft lifetime: Expires in 2286 seconds
Mode: Tunnel(0 0), Type: dynamic, State: installed
Protocol: ESP, Authentication: hmac-sha256-128, Encryption: aes-cbc (192 bits)
Anti-replay service: counter-based enabled, Replay window size: 64
Extended-Sequence-Number: Disabled
tunnel-establishment: establish-tunnels-on-traffic
IKE SA Index: 32
From operational mode, enter the show security pki local-certificate
certificate-id r0_rsa_cr detail command.
user@srxa> show security pki local-certificate certificate-id r0_rsa_crt detail
LSYS: root-logical-system
Certificate identifier: r0_rsa_crt
Certificate version: 3
Serial number:
hexadecimal: 0x0186a62478ae8f0cdd766eb38dbd53
decimal: 7923302907757301847007106226306387
Issuer:
Organization: juniper, Country: India, Common name: Root-CA
Subject:
Organization: juniper, Organizational unit: marketing, State: california, Locality: sunnyvale, Common name: r0, Domain component: juniper
Subject string:
DC=juniper, CN=r0, OU=marketing, O=juniper, L=sunnyvale, ST=california, C=us
Alternate subject: "r0@juniper.net", r0.juniper.net, 192.168.1.1
Cert-Chain: Root-CA
Validity:
Not before: 03- 3-2023 05:54 UTC
Not after: 06- 6-2027 12:36 UTC
Public key algorithm: rsaEncryption(2048 bits)
30:82:01:0a:02:82:01:01:00:b0:e5:53:8d:7e:20:fa:6b:21:c2:d1
2b:48:8f:af:c3:eb:8b:23:4a:f7:c5:1f:cf:2c:6a:b3:2e:8a:ef:1b
f7:97:aa:fd:1d:ab:1c:76:9b:40:a3:ac:bb:49:f6:93:f9:e1:4e:62
df:3d:ca:e5:d2:95:9c:a0:f4:2b:d7:7e:1d:20:94:69:a8:e4:cf:dc
15:90:4c:be:1d:d8:1c:52:08:3a:d1:05:a3:bb:2f:8f:31:0c:6b:21
ef:76:c3:c7:fb:be:4a:cb:da:cc:8d:04:3a:75:0c:eb:5d:e2:f6:13
50:fe:39:67:c0:77:2f:32:b0:5e:38:6f:9c:79:b3:5d:f3:57:f4:f8
42:f5:22:5b:6c:58:67:90:4e:1e:ec:6a:03:e2:c0:87:65:02:ca:da
6f:95:0a:8c:2a:fd:45:4f:3a:b5:ef:18:05:1c:54:e6:fe:45:bb:73
53:81:b2:c6:b7:36:36:57:6d:9c:d3:d9:80:e7:d6:85:92:74:32:88
16:01:03:27:57:76:8e:5e:d6:73:ac:bf:68:fd:6d:a1:2a:8f:f5:3a
29:b0:c9:44:9b:c8:46:c1:bf:c0:52:2a:f0:51:be:b5:f6:e1:f5:3e
96:1d:3a:42:29:28:d3:cf:60:b9:eb:24:04:47:d3:f1:3f:5e:38:fc
7f:33:f6:94:9d:02:03:01:00:01
Signature algorithm: sha256WithRSAEncryption
Fingerprint:
4d:f6:89:c5:d6:3c:74:73:db:3e:f6:4b:1e:26:6c:c1:1c:1d:a7:4d (sha1)
6b:1c:a8:1f:de:5a:9b:3e:d5:c4:85:29:af:3f:82:f2 (md5)
6b:7a:b5:d1:57:cf:75:9d:1f:63:b9:f6:49:e4:4e:b3:13:2c:83:f1:f7:25:44:6f:45:2f:0d:2f:ae:a8:80:85 (sha256)
Auto-re-enrollment:
Status: Disabled
Next trigger time: Timer not startedFrom operational mode, enter the show security pki ca-certificate ca-profile
Root-CA detail command.
user@srxa> show security pki ca-certificate ca-profile Root-CA detail
LSYS: root-logical-system
CA profile: Root-CA
Certificate identifier: Root-CA
Certificate version: 3
Serial number:
hexadecimal: 0x00000440
decimal: 1088
Issuer:
Organization: juniper, Country: India, Common name: Root-CA
Subject:
Organization: juniper, Country: India, Common name: Root-CA
Subject string:
C=India, O=juniper, CN=Root-CA
Validity:
Not before: 06- 7-2022 12:36 UTC
Not after: 06- 6-2027 12:36 UTC
Public key algorithm: rsaEncryption(2048 bits)
30:82:01:0a:02:82:01:01:00:cd:9c:e6:9f:62:6c:49:15:c2:da:eb
8e:e6:e5:a1:88:40:d8:b5:2e:5b:1a:0e:de:96:d7:0b:19:f9:03:44
98:49:d5:cc:a8:90:2b:7f:1b:58:7b:1f:26:92:18:4c:2d:37:65:5c
9f:0f:6e:10:b5:34:6f:2d:b5:9c:27:3b:a6:b1:b5:a0:e2:a6:92:3d
e4:68:fe:5d:71:06:6f:ce:e6:0f:0f:e3:94:2a:23:57:98:a0:6a:9c
e0:52:a2:47:ff:ce:b0:47:bd:36:95:80:a7:af:d2:49:b1:5d:2a:3d
28:e4:95:06:b8:b3:d9:07:11:3c:13:af:c6:e2:51:08:22:82:2d:ec
4f:26:40:b0:b0:55:2d:6e:c0:c8:19:34:a7:99:5a:bc:58:98:69:ae
04:d6:6d:ec:4a:c9:55:a5:ff:00:cb:3b:02:85:fa:02:a1:5c:c1:9d
6d:44:b8:95:8f:77:c0:53:fc:7f:a4:09:a3:25:1c:4a:e2:9d:0c:81
08:b4:c8:b8:0d:bc:94:75:54:75:57:4f:d3:a4:17:0d:5d:1a:f3:c1
1d:5d:73:2f:fe:8b:cb:fc:1f:93:87:72:d6:be:df:86:d7:e6:d1:c7
0d:00:1a:6e:58:db:6a:1c:2f:1d:17:46:9a:f2:69:b4:21:db:08:5d
8d:ab:30:7d:7f:02:03:01:00:01
Signature algorithm: sha256WithRSAEncryption
Distribution CRL:
http://10.102.40.55:8080/crl-as-der/currentcrl-11.crl?id=11
Use for key: CRL signing, Certificate signing, Key encipherment, Digital signature
Fingerprint:
8b:84:60:2a:58:5b:80:f0:b9:ae:25:9f:67:3d:d6:81:ee:43:6c:d4 (sha1)
ab:ec:4d:fe:d4:04:9c:c9:79:1d:9a:33:4e:6d:78:f6 (md5)
9d:f0:c0:a0:93:74:11:53:d3:4d:2d:75:d3:60:37:5f:fb:b7:a9:67:42:cd:7c:3c:0e:0f:9b:58:36:3c:14:f5 (sha256)Verify SRX_B
The sample outputs shown are on SRX-B.
Purpose
Verify the IPsec Phase 2 status.
Action
From operational mode, enter the show security ike
security-associations command.
user@srxb> show security ike security-associations Index State Initiator cookie Responder cookie Mode Remote Address 56042 UP 6723643250f0f357 f6295f11b0d7c8ab IKEv2 192.168.1.1
From operational mode, enter the show security ipsec
security-associations command.
user@srxb> show security ipsec security-associations Total active tunnels: 1 Total IPsec sas: 1 ID Algorithm SPI Life:sec/kb Mon lsys Port Gateway <500230 ESP:aes-cbc-192/sha256 0x7ea065e7 2638/ unlim - root 500 192.168.1.1 >500230 ESP:aes-cbc-192/sha256 0x5f156c1b 2638/ unlim - root 500 192.168.1.1
From operational mode, enter the show security ike security-associations
detail command.
user@srxb> show security ike security-associations detail
IKE peer 192.168.1.1, Index 56042, Gateway Name: IKE_GW
Role: Responder, State: UP
Initiator cookie: 6723643250f0f357, Responder cookie: f6295f11b0d7c8ab
Exchange type: IKEv2, Authentication method: ECDSA-384-signatures
Local gateway interface: ge-0/0/0.0
Routing instance: default
Local: 192.168.1.2:500, Remote: 192.168.1.1:500
Lifetime: Expires in 18995 seconds
Reauth Lifetime: Disabled
IKE Fragmentation: Enabled, Size: 576
Remote Access Client Info: Unknown Client
Peer ike-id: 192.168.1.1
AAA assigned IP: 0.0.0.0
Algorithms:
Authentication : hmac-sha256-128
Encryption : aes128-cbc
Pseudo random function: hmac-sha256
Diffie-Hellman group : DH-group-5
Traffic statistics:
Input bytes : 2934
Output bytes : 2379
Input packets: 10
Output packets: 9
Input fragmented packets: 3
Output fragmented packets: 2
IPSec security associations: 8 created, 3 deleted
Phase 2 negotiations in progress: 1
IPSec Tunnel IDs: 500230
Negotiation type: Quick mode, Role: Responder, Message ID: 0
Local: 192.168.1.2:500, Remote: 192.168.1.1:500
Local identity: 192.168.1.2
Remote identity: 192.168.1.1
Flags: IKE SA is created
IPsec SA Rekey CREATE_CHILD_SA exchange stats:
Initiator stats: Responder stats:
Request Out : 1 Request In : 2
Response In : 1 Response Out : 2
No Proposal Chosen In : 0 No Proposal Chosen Out : 0
Invalid KE In : 0 Invalid KE Out : 0
TS Unacceptable In : 0 TS Unacceptable Out : 0
Res DH Compute Key Fail : 0 Res DH Compute Key Fail: 0
Res Verify SA Fail : 0
Res Verify DH Group Fail: 0
Res Verify TS Fail : 0
From operational mode, enter the show security ipsec security-associations
detail command.
user@srxb> show security ipsec security-associations detail
ID: 500230 Virtual-system: root, VPN Name: IPSEC_VPN
Local Gateway: 192.168.1.2, Remote Gateway: 192.168.1.1
Local Identity: ipv4(0.0.0.0-255.255.255.255)
Remote Identity: ipv4(0.0.0.0-255.255.255.255)
TS Type: proxy-id
Version: IKEv2
PFS group: N/A
DF-bit: clear, Copy-Outer-DSCP Disabled, Bind-interface: st0.1, Tunnel MTU: 0, Policy-name: IPSEC_POL
Port: 500, Nego#: 0, Fail#: 0, Def-Del#: 0 Flag: 0
Multi-sa, Configured SAs# 0, Negotiated SAs#: 0
Tunnel events:
Thu Mar 02 2023 22:26:16: IPsec SA negotiation succeeds (1 times)
Location: FPC 0, PIC 0, KMD-Instance 0
Anchorship: Thread 1
Distribution-Profile: default-profile
Direction: inbound, SPI: 0x7ea065e7, AUX-SPI: 0
, VPN Monitoring: -
Hard lifetime: Expires in 2633 seconds
Lifesize Remaining: Unlimited
Soft lifetime: Expires in 2002 seconds
Mode: Tunnel(0 0), Type: dynamic, State: installed
Protocol: ESP, Authentication: hmac-sha256-128, Encryption: aes-cbc (192 bits)
Anti-replay service: counter-based enabled, Replay window size: 64
Extended-Sequence-Number: Disabled
tunnel-establishment: establish-tunnels-on-traffic
IKE SA Index: 56042
Direction: outbound, SPI: 0x5f156c1b, AUX-SPI: 0
, VPN Monitoring: -
Hard lifetime: Expires in 2633 seconds
Lifesize Remaining: Unlimited
Soft lifetime: Expires in 2002 seconds
Mode: Tunnel(0 0), Type: dynamic, State: installed
Protocol: ESP, Authentication: hmac-sha256-128, Encryption: aes-cbc (192 bits)
Anti-replay service: counter-based enabled, Replay window size: 64
Extended-Sequence-Number: Disabled
tunnel-establishment: establish-tunnels-on-traffic
IKE SA Index: 56042From operational mode, enter the show security pki local-certificate
certificate-id r1_crt_ecdsa384 detail command.
user@srxb> show security pki local-certificate certificate-id r1_crt_ecdsa384 detail
LSYS: root-logical-system
Certificate identifier: r1_crt_ecdsa384
Certificate version: 3
Serial number:
hexadecimal: 0x0186a6254347a38063946d08595a55
decimal: 7923303152683216740296668848151125
Issuer:
Organization: juniper, Country: India, Common name: root-ecdsa-384
Subject:
Organization: juniper, Organizational unit: marketing, State: california, Locality: sunnyvale, Common name: r1_spk1, Domain component: juniper
Subject string:
DC=juniper, CN=r1_spk1, OU=marketing, O=juniper, L=sunnyvale, ST=california, C=us
Alternate subject: "r1_spk1@juniper.net", r1_spk1.juniper.net, 192.168.2
Cert-Chain: root-ecdsa-384
Validity:
Not before: 03- 3-2023 05:55 UTC
Not after: 06- 6-2027 13:21 UTC
Public key algorithm: ecdsaEncryption(384 bits)
04:c2:ba:19:dc:0d:62:a7:94:7b:9b:1d:4d:ff:a1:e1:44:b5:57:a7
cb:7d:33:6b:35:87:b8:e4:ca:44:b1:6c:6d:63:ae:6f:3c:31:7c:7e
65:99:b3:2d:a3:76:30:23:e5:0e:34:e1:28:54:d6:3e:d3:8b:de:b6
b9:45:05:82:6f:1d:20:b7:6f:3c:ce:a2:13:a2:b4:37:0b:db:35:1e
20:54:b5:06:9d:f8:7f:19:7b:c5:d7:7b:57:8b:28:31:d3
Signature algorithm: ecdsa-with-SHA384
Fingerprint:
9b:cb:5a:57:a8:60:a0:ee:5c:be:59:4c:db:35:39:d3:b7:29:ef:b1 (sha1)
ef:b5:e3:be:35:1b:6e:02:0b:61:11:a5:53:07:b4:89 (md5)
8f:86:d0:12:ea:bc:a8:81:a8:17:3a:f9:03:e4:91:57:20:9c:11:bc:a4:dd:d1:7f:d1:48:3f:5b:d9:fb:93:32 (sha256)
Auto-re-enrollment:
Status: Disabled
Next trigger time: Timer not started
s
From operational mode, enter the show security pki ca-certificate ca-profile
Root-CA detail command.
user@srxb> show security pki ca-certificate ca-profile Root-CA detail
LSYS: root-logical-system
CA profile: Root-CA
Certificate identifier: Root-CA
Certificate version: 3
Serial number:
hexadecimal: 0x00000440
decimal: 1088
Issuer:
Organization: juniper, Country: India, Common name: Root-CA
Subject:
Organization: juniper, Country: India, Common name: Root-CA
Subject string:
C=India, O=juniper, CN=Root-CA
Validity:
Not before: 06- 7-2022 12:36 UTC
Not after: 06- 6-2027 12:36 UTC
Public key algorithm: rsaEncryption(2048 bits)
30:82:01:0a:02:82:01:01:00:cd:9c:e6:9f:62:6c:49:15:c2:da:eb
8e:e6:e5:a1:88:40:d8:b5:2e:5b:1a:0e:de:96:d7:0b:19:f9:03:44
98:49:d5:cc:a8:90:2b:7f:1b:58:7b:1f:26:92:18:4c:2d:37:65:5c
9f:0f:6e:10:b5:34:6f:2d:b5:9c:27:3b:a6:b1:b5:a0:e2:a6:92:3d
e4:68:fe:5d:71:06:6f:ce:e6:0f:0f:e3:94:2a:23:57:98:a0:6a:9c
e0:52:a2:47:ff:ce:b0:47:bd:36:95:80:a7:af:d2:49:b1:5d:2a:3d
28:e4:95:06:b8:b3:d9:07:11:3c:13:af:c6:e2:51:08:22:82:2d:ec
4f:26:40:b0:b0:55:2d:6e:c0:c8:19:34:a7:99:5a:bc:58:98:69:ae
04:d6:6d:ec:4a:c9:55:a5:ff:00:cb:3b:02:85:fa:02:a1:5c:c1:9d
6d:44:b8:95:8f:77:c0:53:fc:7f:a4:09:a3:25:1c:4a:e2:9d:0c:81
08:b4:c8:b8:0d:bc:94:75:54:75:57:4f:d3:a4:17:0d:5d:1a:f3:c1
1d:5d:73:2f:fe:8b:cb:fc:1f:93:87:72:d6:be:df:86:d7:e6:d1:c7
0d:00:1a:6e:58:db:6a:1c:2f:1d:17:46:9a:f2:69:b4:21:db:08:5d
8d:ab:30:7d:7f:02:03:01:00:01
Signature algorithm: sha256WithRSAEncryption
Distribution CRL:
http://10.102.40.55:8080/crl-as-der/currentcrl-11.crl?id=11
Use for key: CRL signing, Certificate signing, Key encipherment, Digital signature
Fingerprint:
8b:84:60:2a:58:5b:80:f0:b9:ae:25:9f:67:3d:d6:81:ee:43:6c:d4 (sha1)
ab:ec:4d:fe:d4:04:9c:c9:79:1d:9a:33:4e:6d:78:f6 (md5)
9d:f0:c0:a0:93:74:11:53:d3:4d:2d:75:d3:60:37:5f:fb:b7:a9:67:42:cd:7c:3c:0e:0f:9b:58:36:3c:14:f5 (sha256)Signature Authentication in IKEv2
Read this topic to learn about the signature authentication method in IKEv2 and how it works in Junos OS.
The Internet Key Exchange version 2 (IKEv2) protocol supports signature-based authentication that uses public key cryptography. In IKEv2, signature-based authentication supports one authentication method per signature algorithm. For example, the IKE peers use a separate authentication method for each of these digital signatures—RSA, Digital Signature Algorithm (DSA), and Elliptic Curve DSA (ECDSA). Each hash algorithm is tied to one signature for authentication. In IKEv2 proposal configuration, when you specify the authentication method, the device uses that method to authenticate the source of IKEv2 messages. It is difficult for the IKE peer to know which hash algorithm is associated with the signature. This process becomes even more cumbersome with the introduction of every new algorithm. See Internet Key Exchange for more information about IKEv2.
You can address these challenges with the digital signature authentication method that is based on RFC 7427. This method is more generic compared to the signature-based authentication method, as the IKE peers can use any of the supported signature algorithms and also negotiate the signature hash algorithm. Read further to understand about the signature authentication in IKEv2.
Implementation of Signature Authentication in IKEv2
In addition to supporting signature-based authentication on a per algorithm basis, Junos OS also supports the digital signature authentication method described in RFC 7427. In this method, the IKEv2 authentication payload indicates not only the type of public key, but also the hash algorithm that the device uses to generate the signature. The device uses the SIGNATURE_HASH_ALGORITHM notification to notify its peer about the RFC 7427 support and provide the list of supported hash algorithms.
To use the feature, you must configure the digital signature authentication method on your
device. For more information about the digital signature authentication method,
see proposal (Security IKE).
You can use the configuration option signature-hash-algorithm to define the
specific signature hash algorithms that must match in the hierarchical order with each of
the received signature hash algorithms. If you do not specify the signature hash algorithm,
the device matches the received signature hash algorithm from the default list of all the
supported hash algorithms.
See Signature Hash Algorithm (Security IKE).
In Junos OS, the authentication method involves the following steps that are defined in the IKEv2 message flow. See RFC 7296, Internet Key Exchange Protocol Version 2 (IKEv2) for more details.
-
Both the IKE peers initially notify the list of supported hash algorithms to each other. Your device sends the SIGNATURE_HASH_ALGORITHM payload in the IKE_SA_INIT message to the peer device and receives a response. The peers then negotiate a signature hash algorithm.
-
In the IKE_AUTH message, the peers exchange the digital signature authentication method.
The device uses the default certificate authentication method in either of these scenarios:
-
Responder doesn’t support RFC 7427.
-
Initiator doesn't support the received hash algorithm.
Benefits
-
Flexible—Includes traditional and new digital signatures.
-
Ease of use—Integrates into the existing public key infrastructure (PKI).
-
Robust solution—Performs better identity verification compared to the signature-based authentication method, improving overall security and reliability of the IKE peers.
See Also
IKE Protection from DDoS Attacks
Denial of service (DoS) is one of the most common yet serious attacks in an insecure IPsec VPN network. A DoS attack provides a quick and easy way to grab the network as it doesn’t require much toehold in the network infrastructure. Cyberattackers choose this method to take control of the network.
What happens in a DoS attack?
The attacker tries to flood and gradually crash the network with too much traffic, depleting the network resources, and further taking control of the device resources such as memory and CPU. If the attacker tries to control using multiple orchestrated systems, synchronously attacking a single target, it is called Distributed DoS (DDoS) attacks.
- DDoS Vulnerabilities on IKE Implementations
- Protection Against DDoS Attacks
- Ways to Monitor DDoS Attacks
DDoS Vulnerabilities on IKE Implementations
When the remote peer (initiator) sends an SA_INIT message, the local peer (responder) replies and allocates memory for the message structure. We call the session a half-open IKE session until authentication happens with the help of the IKE_AUTH message. After the peers establish an IKE security association (SA), the session becomes a full-open IKE session.
To understand the IKEv2 DDoS vulnerabilities, let's look at some of the ways an attacker can create an easy attack vector against the IKE SAs:
-
Send a large number of SA_INIT messages (without IKE_AUTH messages) for which the attacker can create half-open IKE security association structures. The attack causes the device to utilize the resources and run out of memory.
-
Send a large number of junk IKE_AUTH packets with the correct SPI_i and SPI_r on the initiator and the responder, respectively. The device runs out of memory while trying to decrypt the packets.
-
Send SA_INIT packets continuously. The device runs out of memory while trying to generate keys for the encrypted packets.
-
Send a large number of rekey requests per second during full open IKE sessions.
-
Send a large number of messages with distinct message identifiers (IDs). The device queues all incoming IKE messages and runs out of memory.
How to safeguard the IKE implementations
We provide a robust infrastructure to mitigate and to monitor DDoS attacks for both IKEv1 and IKEv2 protocols. You can protect against the attacks on IKE implementations when your firewall runs the iked process (in the junos-ike package) for the IPsec VPN service.
For details about DDoS protection for IKEv2, see RFC 8019, Protecting Internet Key Exchange Protocol Version 2 (IKEv2) Implementations from Distributed Denial-of-Service Attacks. We provide similar protection for IKEv1 when your firewall runs the IPsec VPN service using the iked process. We do not support the client puzzle mechanism that the RFC presents.
Protection Against DDoS Attacks
You can enable multiple defense mechanisms against the DDoS attacks during the IKE security association creation process. These mechanisms include configuration of rate limiting and a retention period for the half-open IKE SAs, and further managing the incoming exchange rates for the rekey requests. We provide the following measures to ensure protection against DDoS attacks on IKE SAs:
- Protection
measures
for
half-open
IKE SAs:
-
The responder does not allow configuration of half-open IKE SAs for a certain duration. You can set this limit so that the responder does not configure the SAs until it reaches the timeout duration. For more details, see session (Security IKE) for the option
timeout. -
You can set a limit on the maximum allowed half-open IKE SAs on the responder. When the total number of half-open IKE SAs reaches the maximum count, the responder rejects new connections for both IKEv1 and IKEv2 SAs. For more details, see the
max-countoption insession (Security IKE). -
The responder enforces threshold values on the session count for half-open IKE SAs. When the total number of half-open IKE SAs reaches the threshold values:
-
In case of IKEv2 SAs, the responder invokes cookie mechanism for any new connections.
-
In case of IKEv1 SAs, the responder rejects new connections.
For more details, see the
thresholds,send-cookieandreduce-timeoutoptions in session (Security IKE). -
-
The responder can discard duplicate sessions. For more details, see the
discard-duplicateoption in session (Security IKE). -
You can set backoff timeouts for authentication failure and initiation failure phases. For more details, see session (Security IKE) for the options
backoff-timeouts,init-phase-failureandauth-phase-failure.
-
-
For full open IKE SAs:
-
You can configure maximum incoming rekey request rates to throttle the requests in a scaled scenario. For more details, see the
incoming-exchange-max-ratesoption in session (Security IKE).
-
-
The responder can block an incoming IKE session from peers based on the peer IKE ID. For more details, see blocklists (Security IKE).
-
For dynamic gateways, you can set a limit for the number of connections at the IKE gateway configuration level using the option
connections-limit. For more details, see gateway (Security IKE).
For further details on how to configure these options, see Configure Protection Against IKE DDoS Attacks.
We do not support:
-
DDoS protection with IPsec VPN service based on the kmd process.
-
Protection against Hash and URL certificate encoding attacks as we do not support these encoding types.
Ways to Monitor DDoS Attacks
We provide the following mechanisms to monitor the DDoS attacks:
-
Use the
show security ike security-associationscommand to list down all the matured and non-matured IKE security associations. For more details, see show security ike security-associations. -
Use the
show security ike statscommand to display global IKE statistics of the IPsec VPN tunnel, such as in-progress, established, expired statistics. For more details, see show security ike stats. -
Use the
show security ike active-peercommand to display details of the successful IKE negotiations with the remote peers. For more details, see show security ike active-peer. -
Use the
show security ike peers in-progresscommand to display the details of in progress IKE SAs, including the half open IKE SAs. For more details, see show security ike peers. You can also see the details of the blocked, failed, and backoff peers using this command. -
Use the
clear security ike peerscommand to clear the IKE peers that are backed off, blocked, failed or in progress. For more details, see clear security ike peers. -
To delete an existing IKE security association with peers that needs to be blocked from further communications, use the
clear security ike security-associationscommand. For more details, see clear security ike security-associations. -
The iked system log (syslog) messages IKE_GATEWAY_PEER_BLOCKED, IKE_GATEWAY_PEER_BACKOFF and IKE_GATEWAY_PEER_FAILED provide details about the blocked, backed-off, and failed IKE negotiations with the remote peers, respectively.
-
For additional security, Junos OS provides services to users for protection against packet-based system attacks such as filtering, session count, and rate limiting. For more details, see the show firewall command and the ids-option statement at the [
edit security screen ids-option screen-name] hierarchy level.
Configure Protection Against IKE DDoS Attacks
See this section to understand how to configure protection against DDoS attacks on IKE protocol.
Preprequisites
Before configuring protection against the IKE DDoS attacks, ensure that you meet the following prerequisites:
-
Firewall that supports
junos-ikepackage to run the IPsec VPN service using the iked process. -
Firewall that serves as the local endpoint (the responder) is reachable to the remote IKE peer (the initiator).
-
An IKE policy that can associate an IKE blocklist.
Following actions are involved in configuring protection against the IKE DDoS attacks:
-
Manage the incoming half open IKE SAs.
-
Manage the incoming full open IKE SAs.
-
Configure multiple blocking methods in order to block the incoming IKE sessions from various peers and associate one of the blocklists with an IKE peer.
See the following tasks to configure these actions.
- Configure the IKE Session for Half Open IKE SAs
- Configure the IKE Session for Full Open IKE SAs
- Configure the IKE Session Blocklists
Configure the IKE Session for Half Open IKE SAs
Overview
Ensure you meet all the prerequisites discussed above.
In this section, you'll see how to configure the timeouts, maximum count and
thresholds for the half open IKE SAs. The configuration changes are applicable
to the new sessions, while the existing sessions continue to use the default
values when not configured explicitly earlier. The scope of these configurations
at the [edit security ike session half-open] hierarchy level is
applicable at global level and not per peer level.
Configuration
-
To set the responder lifetime parameter using the option
timeout seconds:[edit] user@host# set security ike session half-open timeout 150
During this period, the responder does not allow the configuration of half open IKE SAs till it reaches the timeout duration. The initiator can continue to have 60 seconds timeout duration irrespective of the responder's configuration.
-
To set the responder maximum count parameter using the option
max-count value:[edit] user@host# set security ike session half-open max-count 1000
The option sets the maximum numbers of half open IKE sessions on the responder. The default value is 300, if you do not specify. The
max-countconfiguration disables all thresholds. In such cases, you need to expliclty configure thresholds to enforce them. -
Specify the different types of actions using the option
thresholdwhen the responder's session count reaches the limit.-
To set the minimum number of half open IKE sessions to enforce cookie action using the option
send-cookie count:[edit] user@host# set security ike session half-open threshold send-cookie 500
This specifies the threshold limit from which the responder requests the remote peers to retry the session initiation with a cookie sent back to the peer in the initial response. Here, when the half open IKE session count limit reaches 500, the iked process employs a cookie mechanism for the new IKE sessions.
-
To set the minimum number of half open IKE sessions to enforce reduced timeout action using the option
reduced-timeout count timeout seconds:[edit] user@host# set security ike session half-open threshold reduce-timeout 600 timeout 100
This specifies the limit from which the iked process reduces the lifetime of the new half open IKE SAs. Once the half open responder IKE session count reduces below the threshold, the half open responder IKE sessions use the default timeout value again.
-
-
To set the option
discard-duplicatein order to discard the duplicate half open IKE sessions without sending response back to the initiator:[edit] user@host# set security ike session half-open discard-duplicate
For a duplicate session initiation request (SA_INIT) that comes from the same peer, with a different initiator cookie for which there is no IKE SA while the negotiation is in progress, the responder discards the packet.
-
You can set the backoff timeouts using the option
backoff-timeouts.This gives some time for the remote peer to back off in the event of a session initiation failure, ensuring that the same peer cannot initiate a new session during that period. After the backoff timeout, the peer can initiate a new session. The session initiation can fail at two phases—the initialization phase and the authentication phase.
-
To set the backoff timeout when there's a failure during the IKE_AUTH phase using the option
backoff-timeouts auth-phase-failure value:[edit] user@host# set security ike session half-open backoff-timeouts auth-phase-failure 150
When you configure
auth-phase-failure, any remote peer that is blocklisted, backsoff even when you do not configure backoff as an action for the target blocklist rule. The timeout for the backoff is the one configured forauth-phase-failure. In this example, the device initiates a new session after 150 seconds. To overwrite this backoff timeout for a particular rule, you can explicitly configure thebackoffaction for the blocklistrulementioning the timeout at the [edit security ike blocklists blocklist1 rule rule-name then backoff timeout-value] hierarchy level. -
To set the backoff timeout when there's a failure during the SA_INIT phase using the option
backoff-timeouts init-phase-failure value:[edit] user@host# set security ike session half-open backoff-timeouts init-phase-failure 160
In this example, the device initiates a new session after 160 seconds.
-
Configure the IKE Session for Full Open IKE SAs
Overview
Ensure you meet all the prerequisites discussed above.
In this section, you'll see how to configure various incoming request rates for
the full open IKE SAs using the option
incoming-exchange-max-rates at the [edit security
ike session full-open] hierarchy level.
Configuration
Configure the incoming-exchange-max-rates option to set the
maximum rates for various exchanges initiated by the remote peer after
establishing an IKE SA. You can configure three types of exchange rates—IKE
rekey, IPsec rekey and keepalive (also known as Dead Peer Detection).
-
To set the incoming peer initiated IKE rekey maximum rate using the option
incoming-exchange-max-rates ike-rekey value:[edit] user@host# set security ike session full-open incoming-exchange-max-rates ike-rekey 200/60
The option is applicable to IKEv2 rekey on a per peer basis with an existing peer where an IKE SA is already present.
-
To set the incoming peer initiated IPsec SA rekey maximum rate using the option
incoming-exchange-max-rates ipsec-rekey value:[edit] user@host# set security ike session full-open incoming-exchange-max-rates ipsec-rekey 100/60
The limit is applicable on a per tunnel basis.
-
To set the incoming peer initiated keepalive maximum rate using the option
incoming-exchange-max-rates keepalive value:[edit] user@host# set security ike session full-open incoming-exchange-max-rates keepalive 60/60
The limit is applicable on a per peer basis.
Configure the IKE Session Blocklists
Overview
Ensure you meet all the prerequisites discussed above.
To block an incoming IKE session from peers based on the peer IKE ID, you need to configure one or more blocklists. Each blocklist contains one or more rules. Each rule has a match criteria and an action.
Consider the following criteria when configuring the blocklists:
-
Blocklist rules are applicable on the new IKE SAs that are being negotiated and doesn't affect the existing IKE SAs. At the peer authentication stage, the device applies the blocklist rules.
-
The order of application of the rules is dependent on the sequence in which these rules are listed.
-
Configure the match criteria based on the role (initiator or responder), an ID type (IPv4 or IPv6 address, hostname, distinguished name, email ID, or a key ID) and an ID pattern which is a regular expression to match the IKE ID.
-
You can configure each rule with an ID type. This allows you to configure different IKE IDs for different rules within the same blocklist.
-
Configure an action to either discard or reject the peer connection. Based on the match, the device applies an action. Optionally, you can set the backoff timer with these actions.
-
Refer the blocklist in the IKE policy which is associated to the IKE gateway.
-
Each IKE gateway supports only one type of remote IKE ID type. If you attach a blocklist to a gateway and configure it with rules containing different IKE IDs, the gateway will apply and match only the rules whose IKE ID type is the same as the one configured for the IKE gateway.
-
The tunnel setup rate metrices with blocklists that are attached to the IKE gateways is based on the number of rules configured in the blocklists.
In this section, you'll see how to configure blocklists and associate the blocklist to an IKE policy.
Configuration
-
To create a blocklist with multiple rules:
-
Create a blocklist.
[edit] user@host# set security ike blocklists blocklist1 description block_from_remote
-
Create one or more rules.
[edit] user@host# set security ike blocklists blocklist1 rule rule1 description rule_1 user@host# set security ike blocklists blocklist1 rule rule2 description rule_2
You can create multiple such blocklists and its rules.
-
-
To configure the match criteria and specify the action:
-
Configure the match criteria for the rule1 in the blocklist blocklist1.
[edit] user@host# set security ike blocklists blocklist1 rule rule1 match role initiator user@host# set security ike blocklists blocklist1 rule rule1 match id-type hostname user@host# set security ike blocklists blocklist1 rule rule1 match id-pattern "peer.*\.example\.net" user@host# set security ike blocklists blocklist1 rule rule2 match role initiator user@host# set security ike blocklists blocklist1 rule rule2 match id-type user-at-hostname user@host# set security ike blocklists blocklist1 rule rule2 match id-pattern "hr.example.com"
To configure blocklists using a group of IKE IDs or partial IKE IDs, use the
id-pattern valuewith a suffix or prefix. For example, you can use the value *.example.com, when you need to match hr.example.com, finance.example.com, admin.example.com. In the rule rule1, the device looks for the hostname that matches the pattern peer.*\.example\.net. Here peer.example.net, peer.1.example.net, and peer.uplink.example.net are a few potential matches. In the rule rule2, the device looks for the email address that matches the pattern hr.example.com. Similarly, you can configure another match criteria for the other rules based on differentid-typeorid-pattern. These patterns use the standard regular expression. -
Specify the action for a match:
[edit] user@host# set security ike blocklists blocklist1 rule rule1 then reject user@host# set security ike blocklists blocklist1 rule rule1 then backoff 60 user@host# set security ike blocklists blocklist1 rule rule2 then discard user@host# set security ike blocklists blocklist1 rule rule2 then backoff 100
-
-
To associate a blocklist with an IKE peer:
-
Configure the blocklist blocklist1 in the IKE policy ike_policy1.
[edit] user@host# set security ike policy ike_policy1 blocklist blocklist1
-
Example: Configuring a Device for Peer Certificate Chain Validation
This example shows how to configure a device for certificate chains used to validate peer devices during IKE negotiation.
Requirements
Before you begin, obtain the address of the certificate authority (CA) and the information they require (such as the challenge password) when you submit requests for local certificates.
Overview
This example shows how to configure a local device for certificate chains, enroll CA and local certificates, check the validity of enrolled certificates, and check the revocation status of the peer device.
Topology
This example shows the configuration and operational commands on Host-A, as shown in Figure 10. A dynamic CA profile is automatically created on Host-A to allow Host-A to download the CRL from Sales-CA and check the revocation status of Host-B’s certificate.
The IPsec VPN configuration for Phase 1 and Phase 2 negotiation is shown for Host-A in this example. The peer device (Host-B) must be properly configured so that Phase 1 and Phase 2 options are successfully negotiated and security associations (SAs) are established. See Configuring Remote IKE IDs for Site-to-Site VPNs for examples of configuring peer devices for VPNs.
Configuration
To configure a device for certificate chains:
Configure CA Profiles
CLI Quick Configuration
To quickly configure this example, copy the
following commands, paste them into a text file, remove any line breaks,
change any details necessary to match your network configuration,
copy and paste the commands into the CLI at the [edit] hierarchy
level, and then enter commit from configuration mode.
set security pki ca-profile Root-CA ca-identity CA-Root set security pki ca-profile Root-CA enrollment url http://198.51.100.230:8080/scep/Root/ set security pki ca-profile Root-CA revocation-check crl set security pki ca-profile Eng-CA ca-identity Eng-CA set security pki ca-profile Eng-CA enrollment url http://198.51.100.230:8080/scep/Eng/ set security pki ca-profile Eng-CA revocation-check crl set security pki ca-profile Dev-CA ca-identity Dev-CA set security pki ca-profile Dev-CA enrollment url http://198.51.100.230:8080/scep/Dev/ set security pki ca-profile Dev-CA revocation-check crl
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For instructions on how to do that, see Using the CLI Editor in Configuration Mode in the CLI User Guide.
To configure CA profiles:
Create the CA profile for Root-CA.
[edit security pki] user@host# set ca-profile Root-CA ca-identity CA-Root user@host# set ca-profile Root-CA enrollment url http://198.51.100.230:8080/scep/Root/ user@host# set ca-profile Root-CA revocation-check crl
Create the CA profile for Eng-CA.
[edit security pki] user@host# set ca-profile Eng-CA ca-identity Eng-CA user@host# set ca-profile Eng-CA enrollment url http://198.51.100.230:8080/scep/Eng/ user@host# set ca-profile Eng-CA revocation-check crl
Create the CA profile for Dev-CA.
[edit security pki] user@host# set ca-profile Dev-CA ca-identity Dev-CA user@host# set ca-profile Dev-CA enrollment url http://198.51.100.230:8080/scep/Dev/ user@host# set ca-profile Dev-CA revocation-check crl
Results
From configuration mode, confirm your configuration
by entering the show security pki command. If the output
does not display the intended configuration, repeat the configuration
instructions in this example to correct it.
[edit]
user@host# show security pki
ca-profile Root-CA {
ca-identity Root-CA;
enrollment {
url "http:/;/198.51.100.230:8080/scep/Root/";
}
revocation-check {
crl ;
}
}
ca-profile Eng-CA {
ca-identity Eng-CA;
enrollment {
url "http:/;/198.51.100.230:8080/scep/Eng/";
}
revocation-check {
crl ;
}
}
ca-profile Dev-CA {
ca-identity Dev-CA;
enrollment {
url "http:/;/198.51.100.230:8080/scep/Dev/";
}
revocation-check {
crl ;
}
}
If you are done configuring the device, enter commit from configuration mode.
Enroll Certificates
Step-by-Step Procedure
To enroll certificates:
Enroll the CA certificates.
user@host> request security pki ca-certificate enroll ca-profile Root-CA
user@host> request security pki ca-certificate enroll ca-profile Eng-CA
user@host> request security pki ca-certificate enroll ca-profile Dev-CA
Type yes at the prompts to load the CA certificate.
Verify that the CA certificates are enrolled in the device.
user@host> show security pki ca-certificate ca-profile Root-CA Certificate identifier: Root-CA Issued to: Root-CA, Issued by: C = us, O = example, CN = Root-CA Validity: Not before: 08-14-2012 22:19 Not after: 08-13-2017 22:19 Public key algorithm: rsaEncryption(2048 bits)user@host> show security pki ca-certificate ca-profile Eng-CA Certificate identifier: Eng-CA Issued to: Eng-CA, Issued by: C = us, O = example, CN = Root-CA Validity: Not before: 08-15-2012 01:02 Not after: 08-13-2017 22:19 Public key algorithm: rsaEncryption(2048 bits)user@host> show security pki ca-certificate ca-profile Dev-CA Certificate identifier: Dev-CA Issued to: Dev-CA, Issued by: C = us, O = example, CN = Eng-CA Validity: Not before: 08-15-2012 17:41 Not after: 08-13-2017 22:19 Public key algorithm: rsaEncryption(2048 bits)Verify the validity of the enrolled CA certificates.
user@host> request security pki ca-certificate verify ca-profile Root-CA CA certificate Root-CA verified successfully
user@host> request security pki ca-certificate verify ca-profile Eng-CA CA certificate Eng-CA verified successfully
user@host> request security pki ca-certificate verify ca-profile Dev-CA CA certificate Dev-CA verified successfully
Generate a key pair.
user@host> request security pki generate-key-pair certificate-id Host-A type rsa size 1024
Enroll the local certificate.
user@host> request security pki local-certificate enroll certificate-id Host-A ca-profile Dev-CA challenge-password example domain-name host-a.example.net email host-a@example.net subject DC=example,CN=Host-A, OU=DEV,O=PKI,L=Sunnyvale,ST=CA,C=US
Verify that the local certificate is enrolled in the device.
user@host> show security pki local-certificate Issued to: Host-A, Issued by: C = us, O = example, CN = Dev-CA Validity: Not before: 09-17-2012 22:22 Not after: 08-13-2017 22:19 Public key algorithm: rsaEncryption(1024 bits)Verify the validity of the enrolled local certificate.
user@host> request security pki local-certificate verify certificate-id Host-A Local certificate Host-A verification success
Check the CRL download for configured CA profiles.
user@host> show security pki crl CA profile: Root-CA CRL version: V00000001 CRL issuer: C = us, O = example, CN = Root-CA Effective date: 09- 9-2012 13:08 Next update: 09-21-2012 02:55 CA profile: Eng-CA CRL version: V00000001 CRL issuer: C = us, O = example, CN = Eng-CA Effective date: 08-22-2012 17:46 Next update: 10-24-2015 03:33 CA profile: Dev-CA CRL version: V00000001 CRL issuer: C = us, O = example, CN = Dev-CA Effective date: 09-14-2012 21:15 Next update: 09-26-2012 11:02
Configure IPsec VPN Options
CLI Quick Configuration
To quickly configure this example, copy the
following commands, paste them into a text file, remove any line breaks,
change any details necessary to match your network configuration,
copy and paste the commands into the CLI at the [edit] hierarchy
level, and then enter commit from configuration mode.
set security ike proposal ike_cert_prop_01 authentication-method rsa-signatures set security ike proposal ike_cert_prop_01 dh-group group5 set security ike proposal ike_cert_prop_01 authentication-algorithm sha1 set security ike proposal ike_cert_prop_01 encryption-algorithm aes-256-cbc set security ike policy ike_cert_pol_01 mode main set security ike policy ike_cert_pol_01 proposals ike_cert_prop_01 set security ike policy ike_cert_pol_01 certificate local-certificate Host-A set security ike gateway ike_cert_gw_01 ike-policy ike_cert_pol_01 set security ike gateway ike_cert_gw_01 address 192.0.2.51 set security ike gateway ike_cert_gw_01 external-interface ge-0/0/1.0 set security ike gateway ike_cert_gw_01 local-identity 192.0.2.31 set security ipsec proposal ipsec_prop_01 protocol esp set security ipsec proposal ipsec_prop_01 authentication-algorithm hmac-sha1-96 set security ipsec proposal ipsec_prop_01 encryption-algorithm 3des-cbc set security ipsec proposal ipsec_prop_01 lifetime-seconds 300 set security ipsec policy ipsec_pol_01 proposals ipsec_prop_01 set security ipsec vpn ipsec_cert_vpn_01 bind-interface st0.1 set security ipsec vpn ipsec_cert_vpn_01 ike gateway ike_cert_gw_01 set security ipsec vpn ipsec_cert_vpn_01 ike ipsec-policy ipsec_pol_01
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For instructions on how to do that, see Using the CLI Editor in Configuration Mode in the CLI User Guide.
To configure IPsec VPN options:
Configure Phase 1 options.
[edit security ike proposal ike_cert_prop_01] user@host# set authentication-method rsa-signatures user@host# set dh-group group5 user@host# set authentication-algorithm sha1 user@host# set encryption-algorithm aes-256-cbc [edit security ike policy ike_cert_pol_01] user@host# set mode main user@host# set proposals ike_cert_prop_01 user@host# set certificate local-certificate Host-A [edit security ike gateway ike_cert_gw_01] user@host# set ike-policy ike_cert_pol_01 user@host# set address 192.0.2.51 user@host# set external-interface ge-0/0/1.0 user@host# set local-identity 192.0.2.31
Configure Phase 2 options.
[edit security ipsec proposal ipsec_prop_01] user@host# set protocol esp user@host# set authentication-algorithm hmac-sha1-96 user@host# set encryption-algorithm 3des-cbc user@host# set lifetime-seconds 300 [edit security ipsec policy ipsec_pol_01] user@host# set proposals ipsec_prop_01 [edit security ipsec vpn ipsec_cert_vpn_01] user@host# set bind-interface st0.1 user@host# set ike gateway ike_cert_gw_01 user@host# set ike ipsec-policy ipsec_pol_01
Results
From configuration mode, confirm your configuration
by entering the show security ike and show security
ipsec commands. If the output does not display the intended
configuration, repeat the configuration instructions in this example
to correct it.
[edit]
user@host# show security ike
proposal ike_cert_prop_01 {
authentication-method rsa-signatures;
dh-group group5;
authentication-algorithm sha1;
encryption-algorithm aes-256-cbc;
}
policy ike_cert_pol_01 {
mode main;
proposals ike_cert_prop_01;
certificate {
local-certificate Host-A;
}
}
gateway ike_cert_gw_01 {
ike-policy ike_cert_pol_01;
address 192.0.2.51;
external-interface ge-0/0/1.0;
}
[edit]
user@host# show security ipsec
proposal ipsec_prop_01 {
protocol esp;
authentication-algorithm hmac-sha1-96;
encryption-algorithm 3des-cbc;
lifetime-seconds 300;
}
policy ipsec_pol_01 {
proposals ipsec_prop_01;
}
vpn ipsec_cert_vpn_01 {
bind-interface st0.1;
ike {
gateway ike_cert_gw_01;
ipsec-policy ipsec_pol_01;
}
}
If you are done configuring the device, enter commit from configuration mode.
Verification
If certificate validation is successful during IKE negotiation between peer devices, both IKE and IPsec security associations (SAs) are established.
The IKE SA is UP if the certificate is valid. The IKE SA is DOWN and IPSEC SA is formed if the certificate is revoked, only if revocation check is configured on the peer device
Verifying IKE Phase 1 Status
Purpose
Verify the IKE Phase 1 status.
Action
Enter the show security ike security-associations command from operational mode.
user@host> show security ike security-associations
Index State Initiator cookie Responder cookie Mode Remote Address
2090205 DOWN 285feacb50824495 59fca3f72b64da10 Main 192.0.2.51
Verifying IPsec Phase 2 Status
Purpose
Verify the IPsec Phase 2 status.
Action
Enter the show security ipsec security-associations command from operational mode.
user@host> show security ipsec security-associations
Total active tunnels: 1
ID Algorithm SPI Life:sec/kb Mon vsys Port Gateway
<131073 ESP:3des/sha1 a4756de9 207/ unlim - root 500 192.0.2.51
>131073 ESP:3des/sha1 353bacd3 207/ unlim - root 500 192.0.2.51
IKE and IPsec SA Failure for a Revoked Certificate
Checking for Revoked Certificates
Problem
If certificate validation fails during IKE negotiation
between peer devices, check to make sure that the peer’s certificate
has not been revoked. A dynamic CA profile allows the local device
to download the CRL from the peer’s CA and check the revocation
status of the peer’s certificate. To enable dynamic CA profiles,
the revocation-check crl option must be configured on a
parent CA profile.
Solution
To check the revocation status of a peer’s certificate:
Identify the dynamic CA profile that will show the CRL for the peer device by entering the show security pki crl command from operational mode.
user@host> show security pki crl CA profile: Root-CA CRL version: V00000001 CRL issuer: C = us, O = example, CN = Root-CA Effective date: 09- 9-2012 13:08 Next update: 09-21-2012 02:55 CA profile: Eng-CA CRL version: V00000001 CRL issuer: C = us, O = example, CN = Eng-CA Effective date: 08-22-2012 17:46 Next update: 10-24-2015 03:33 CA profile: Dev-CA CRL version: V00000001 CRL issuer: C = us, O = example, CN = Dev-CA Effective date: 09-14-2012 21:15 Next update: 09-26-2012 11:02 CA profile: dynamic-001 CRL version: V00000001 CRL issuer: C = us, O = example, CN = Sales-CA Effective date: 09-14-2012 21:15 Next update: 09-26-2012 11:02The CA profile
dynamic-001is automatically created on Host-A so that Host-A can download the CRL from Host-B’s CA (Sales-CA) and check the revocation status of the peer’s certificate.Display CRL information for the dynamic CA profile by entering the show security pki crl ca-profile dynamic-001 detail command from operational mode.
Enter
user@host> show security pki crl ca-profile dynamic-001 detail CA profile: dynamic-001 CRL version: V00000001 CRL issuer: C = us, O = example, CN = Sub11 Effective date: 09-19-2012 17:29 Next update: 09-20-2012 01:49 Revocation List: Serial number Revocation date 10647C84 09-19-2012 17:29 UTCHost-B’s certificate (serial number 10647084) has been revoked.
IKEv2 Fragmentation
Message Fragmentation
IKEv2 message fragmentation, as described in RFC 7383, Internet Key Exchange Protocol Version 2 (IKEv2) Message Fragmentation, allows IKEv2 to operate in environments where IP fragments might be blocked and peers would not be able to establish an IPsec security association (SA). IKEv2 fragmentation splits a large IKEv2 message into a set of smaller ones so that there is no fragmentation at the IP level. Fragmentation takes place before the original message is encrypted and authenticated, so that each fragment is separately encrypted and authenticated. On the receiver, the fragments are collected, verified, decrypted, and merged into the original message.
For IKEv2 fragmentation to occur, both VPN peers must indicate fragmentation support by including the IKEV2_FRAGMENTATION_SUPPORTED notification payload in the IKE_SA_INIT exchange. If both peers indicate fragmentation support, it is up to the initiator of the message exchange to determine whether or not IKEv2 fragmentation is used.
On firewalls, a maximum of 32 fragments are allowed per IKEv2 message. If the number of IKEv2 message fragments to be sent or received exceeds 32, the fragments are dropped and the tunnel is not established. Retransmission of individual message fragments is not supported
Configuration
On firewalls, IKEv2 fragmentation is enabled by default for IPv4 and
IPv6 messages. To disable IKEv2 fragmentation, use the disable
statement at the [edit security ike gateway gateway-name
fragmentation] hierarchy level. You can also use the
size statement to configure the size of the packet at which
messages are fragmented; the packet size ranges from 500 to 1300 bytes. If
size is not configured, the default packet size is 576 bytes
for IPv4 traffic and 1280 bytes for IPv6 traffic. An IKEv2 packet that is larger
than the configured packet size is fragmented.
After IKEv2 fragmentation is disabled or enabled or the packet fragment size is changed, the VPN tunnels that are hosted on the IKE gateway are brought down and IKE and IPsec SAs are renegotiated.
Caveats
The following features are not supported with IKEv2 fragmentation:
Path MTU Discovery.
SNMP.
See Also
IKE Policy with a Trusted CA
This example shows how to bind a trusted CA server to an IKE policy of the peer.
Before you begin, you must have a list of all the trusted CAs you want to associate with the IKE policy of the peer.
You can associate an IKE policy to a single trusted CA profile or a trusted CA group. For establishing a secure connection, the IKE gateway uses the IKE policy to limit itself to the configured group of CAs (ca-profiles) while validating the certificate. A certificate issued by any source other than the trusted CA or trusted CA group is not validated. If there is a certificate validation request coming from an IKE policy then the associated CA profile of the IKE policy will validate the certificate. If an IKE policy is not associated with any CA then by default the certificate is validated by any one of the configured CA profiles.
In this example, a CA profile named root-ca is created
and a root-ca-identity is associated to the profile.
You can configure a maximum of 20 CA profiles that you want to add to a trusted CA group. You cannot commit your configuration if you configure more than 20 CA profiles in a trusted CA group.
To view the CA profiles and the trusted CA groups configured
on your device, run show security pki command.
user@host# show security ike
proposal ike_prop {
authentication-method rsa-signatures;
dh-group group2;
authentication-algorithm sha-256;
encryption-algorithm aes-256-cbc;
}
policy ike_policy {
proposals ike_prop;
certificate {
local-certificate SPOKE;
trusted-ca ca-profile root-ca;
}
}
The show security ike command displays the CA profile
group under the IKE policy named ike_policy and the certificate
associated with the IKE policy.
See Also
Configuring Establish-Tunnel Responder-only in IKE
This topic shows how to configure establish-tunnels responder-only in Internet Key Exchange (IKE). Initiate the tunnels from the remote peer and send the traffic through all the tunnels. Specifies when IKE is activated.
On
firewalls, the
establish-tunnels
option supports the responder-only and
responder-only-no-rekey values under the [edit security
ipsec vpn vpn-name] hierarchy-level.
These options are supported only on a site-to-site VPN. These option are not supported on Auto VPN.
The responder-only and responder-only-no-rekey options
does not establish any VPN tunnel from the device, so the VPN tunnel is initiated from
the remote peer. When you configure responder-only, an established
tunnel rekeys both IKE and IPsec based on the configured IKE and IPsec lifetime values.
When you configure responder-only-no-rekey, an established tunnel does
not rekey from the device and relies on the remote peer to initiate rekey. If the remote
peer does not initiate rekey, then the tunnel teardown occurs after hard-lifetime
expires.
Before you begin:
Understand how to establish an AutoKey IKE IPsec tunnel. Read IPsec Overview.
To configure establish-tunnel responder-only in IKE:
Platform-Specific IKEv2 Responder Only Behavior
Use Feature Explorer to confirm platform and release support for specific features.
Use the following table to review platform-specific behaviors for your platforms.
| Platform | Difference |
|---|---|
| SRX Series |
|
Change History Table
Feature support is determined by the platform and release you are using. Use Feature Explorer to determine if a feature is supported on your platform.
responder-only and
responder-only-no-rekey values in the
establish-tunnels option at the [edit security
ipsec vpn vpn-name] hierarchy-level is
introduced on SRX5000 line in Junos OS Release 19.1R1.