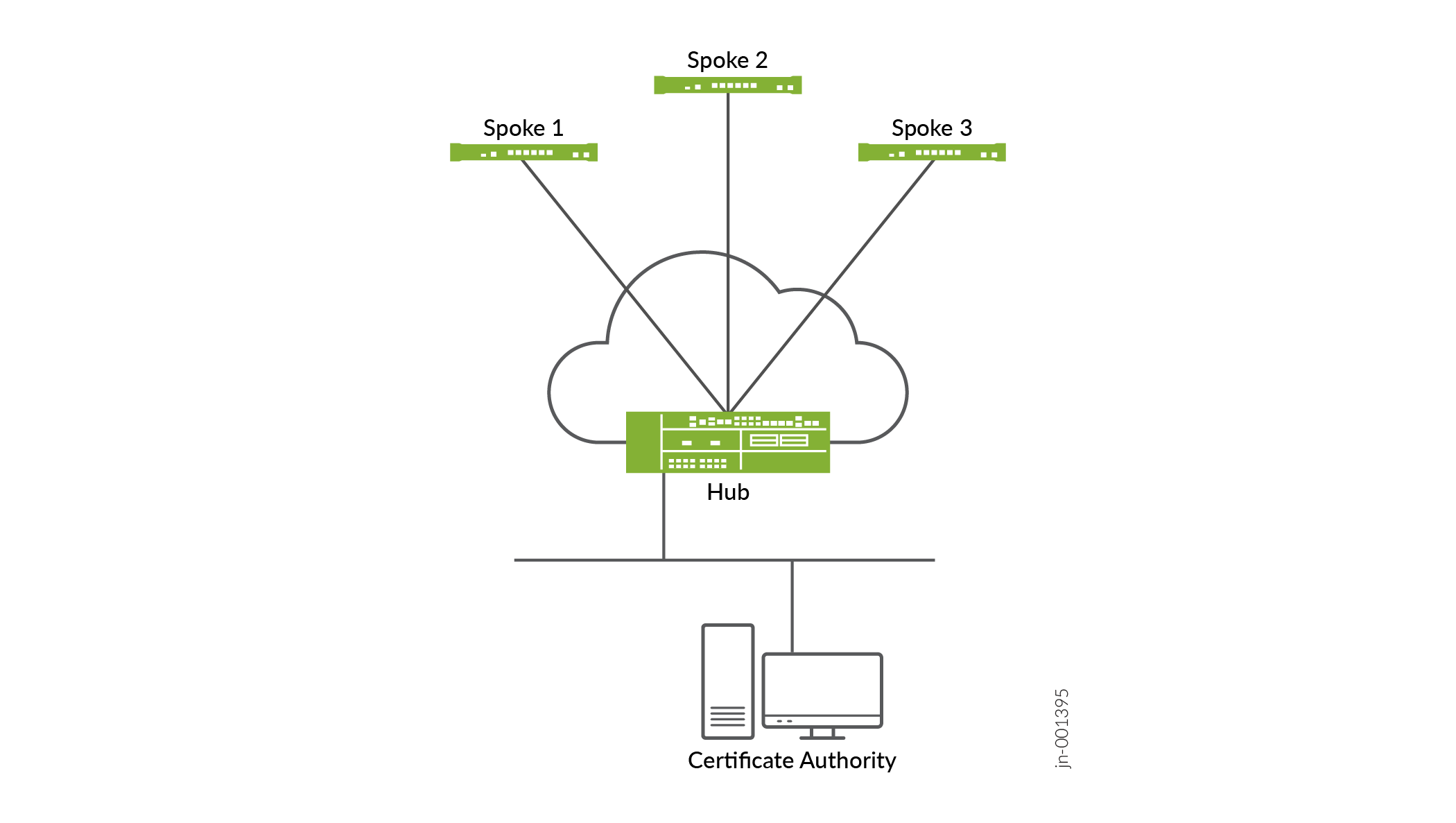
Enterprise Hub or VPN Concentrator for AutoVPN for Hub-And-Spoke IPsec Deployment Use Case
Deploy the SRX4700 Firewall as an enterprise hub or VPN concentrator for AutoVPN in hub-and-spoke IPsec deployments, enabling scalable, dynamic tunnel establishment between central hub and multiple branch spokes.
Overview
The SRX4700 Firewall is ideal as a secure VPN concentrator or hub in hub-and-spoke IPsec topologies, supporting AutoVPN for automated, scalable site-to-site VPNs with dynamic spoke connections. AutoVPN simplifies configuration using templates in Juniper Security Director or Junos OS CLI, distributing Internet Key Exchange (IKE) or IPsec load across Services Processing Units (SPUs) for high performance.
- Hub role: Central SRX4700 Firewall terminates tunnels from multiple spokes; supports load-balancing tunnels across SPUs using least-loaded algorithms.
- AutoVPN features: Automates Phase 1/2 proposals, policies, and routing (for example: BGP/OSPF over tunnels); spokes automatically discover the hub through signaling.
Challenges in large hub-and-spoke VPNs and AutoVPN solutions:
- Configuration Complexity: Traditional setups require hub changes for each new spoke, risking errors; AutoVPN enables dynamic spoke connect or disconnect without hub modifications using certificates and CRL for revocation.
- Spoke-Spoke Traffic Load: Full mesh is impractical; AutoVPN with ADVPN shortcuts offloads direct spoke-spoke tunnels, using hub-suggested paths and multipoint st0 interfaces.
- Route Distribution: Dynamic protocols (OSPF, BGP, IS-IS) propagate routes over tunnels for efficient scaling.
In a retail office environment, payment card transactions are securely transferred to HQ/DC over IPsec VPN tunnels, where per-tunnel bandwidth is low (< 1 Mbps) but tunnel count scales high for 1000+ branches. The SRX4700 Firewall serves as an ideal headquarters or data center hub for medium-to-large enterprises, supporting up to 7500 IPsec tunnels with AutoVPN to simplify management.
Deploy the SRX4700 Firewall in distributed enterprise segments as an IPsec VPN hub using static routing and BGP to secure traffic, terminate connections across sites, and enable scalable, high-availability routing with reduced complexity.
Benefits
-
Simplifies VPN management by dynamically creating and terminating IPsec tunnels, reducing the need for manual configuration and updates.
-
Enhances network performance and availability by integrating routing protocols, ensuring efficient route sharing and secure data transmission.
-
Supports additional services such as VoIP and SD-WAN, providing a versatile and scalable solution for diverse enterprise needs.
-
Reduces device load and optimizes resource utilization by enabling dynamic spoke connections, leading to improved overall system efficiency.
-
Ensures secure and efficient traffic flow across distributed enterprise segments using IPsec VPN hubs, static paths, and BGP, maintaining high availability and reliability.
Topology
Baseline Configurations
- Interfaces and Zones
- IKE (Phase 1) for AutoVPN
- IPsec
- AutoVPN Hub Gateway and VPN (Enables Dynamic Spoke Tunnels)
- Security Policies
- Routing
Interfaces and Zones
set interfaces st0 unit 0 family inet set security zones security-zone hub-vpn interfaces st0.0 set security zones security-zone trust interfaces <lan-if> set security zones security-zone untrust interfaces <wan-if>
IKE (Phase 1) for AutoVPN
set security ike proposal IKE-PROP authentication-method pre-shared-keys set security ike proposal IKE-PROP encryption-algorithm aes-256-cbc set security ike proposal IKE-PROP authentication-algorithm sha-384 set security ike proposal IKE-PROP dh-group group19 set security ike proposal IKE-PROP lifetime-seconds 8640
IPsec
set security ipsec proposal autovpn-ipsec-prop protocol esp set security ipsec proposal autovpn-ipsec-prop authentication-algorithm hmac-sha2-256 set security ipsec proposal autovpn-ipsec-prop encryption-algorithm aes-256-gcm # Or aes-256-cbc set security ipsec proposal autovpn-ipsec-prop lifetime-seconds 3600
AutoVPN Hub Gateway and VPN (Enables Dynamic Spoke Tunnels)
set security ike gateway autovpn-hub ike-policy autovpn-pol set security ike gateway autovpn-hub address 0.0.0.0/0 # Accepts any spoke set security ike gateway autovpn-hub local-identity inet <hub-public-IP> set security ike gateway autovpn-hub external-interface <wan-if> set security ipsec vpn autovpn-hub-vpn ike gateway autovpn-hub set security ipsec vpn autovpn-hub-vpn ipsec-proposal autovpn-ipsec-prop set security ipsec vpn autovpn-hub-vpn bind-interface st0.0 set security ipsec vpn autovpn-hub-vpn establish-tunnels on-traffic
For complete configuration see CLI Quick Configuration at Example: Configuring Basic AutoVPN with iBGP
Security Policies
Configure security policies (Trust to VPN, Bidirectional):
set security policies from-zone trust to-zone hub-vpn policy hub-allow match source-address any set security policies from-zone trust to-zone hub-vpn policy hub-allow match destination-address any set security policies from-zone trust to-zone hub-vpn policy hub-allow then permit tunnel ipsec-vpn autovpn-hub-vpn set security policies from-zone hub-vpn to-zone trust policy spoke-allow match source-address any set security policies from-zone hub-vpn to-zone trust policy spoke-allow match destination-address any set security policies from-zone hub-vpn to-zone trust policy spoke-allow then permit
Routing
set protocols bgp group autovpn type internal set protocols bgp group autovpn local-address <hub-loopback> set protocols bgp group autovpn family inet unicast set protocols bgp group autovpn neighbor <spoke-range> # Or dynamic via AutoVPN
Verification and Monitoring
Verify your configurations using the following commands:
show security ipsec tunnel-distribution summary(SPU load balancing)show security ike security-associationsshow security ipsec security-associationsshow security ipsec tunnel-distribution srg-id id(For multinode HA)
