Components of Juniper Connected Security
Juniper Connected Security uniquely protects your business, unifying all your network elements into a threat-aware network. It dynamically enforces security policy with software-defined containment designed to reduce the overall attack surface.
Because Juniper Networks security solutions are open and extensible, our partnerships with network and security vendors extend the Juniper Connected Security vision by providing customers with a choice of products to deploy a best of breed solution.
Centralized Policy
At the core of the Juniper Connected Security, Junos Space Security Director provides centralized policy and management. Security Director is a management application designed to quickly create, maintain, and apply accurate and consistent network security policies. It also manages the firewalls.
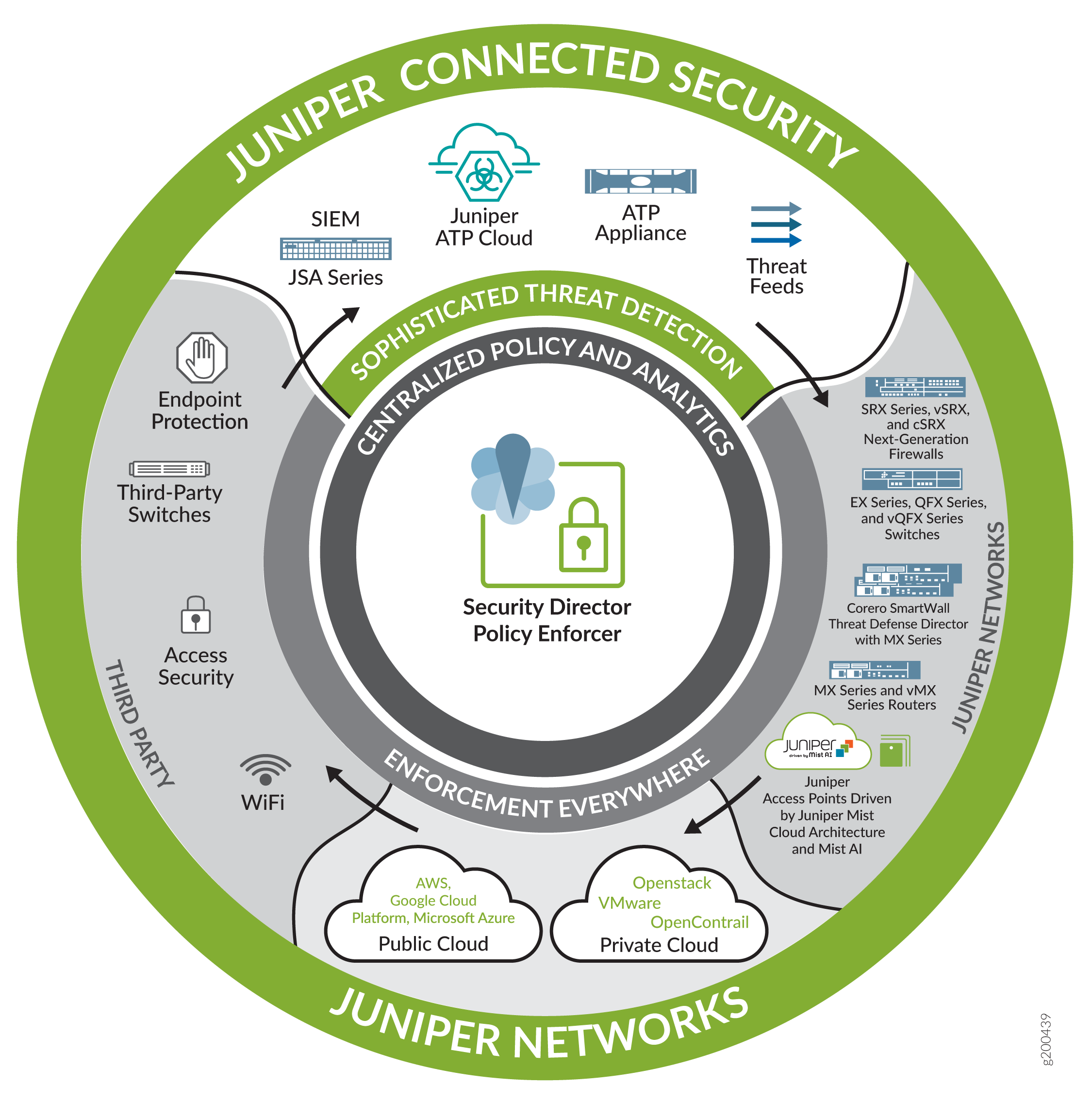
Policy Enforcer provides the management interface that communicates with Juniper devices and third-party devices (through Juniper’s ecosystem partners) across the network, globally enforcing threat prevention policies and consolidating threat intelligence from different sources. It enables you to act on that intelligence from a single management interface where you can view, analyze, and apply your threat prevention policies.
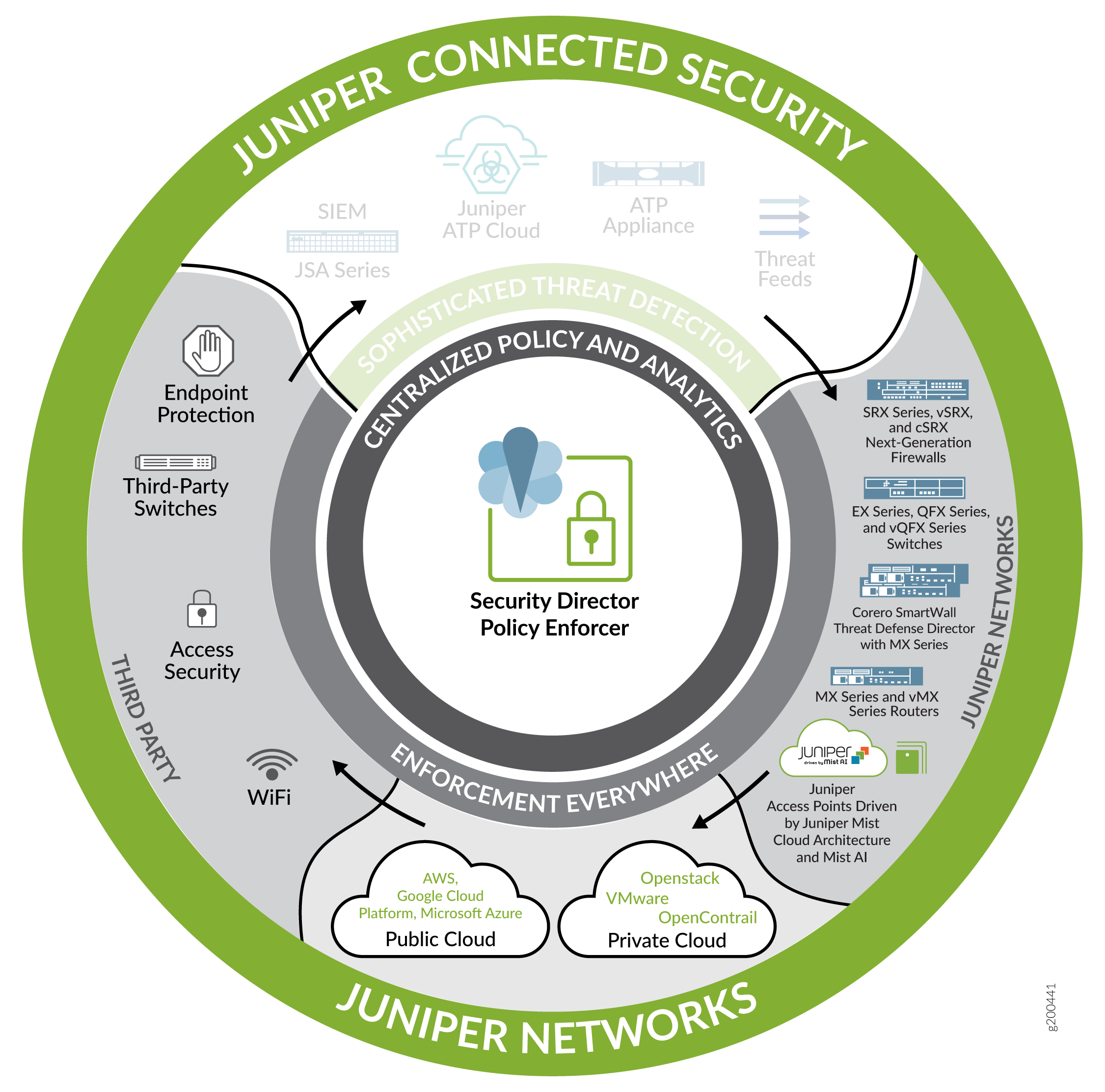
Sophisticated Threat Detection and Analytics
Sophisticated threats to your network can come from both known sources (in-house logging, cloud feeds) and unknown sources (cybercrime, Internet-of-Things (IoT) botnets, machine learning, hacktivism). Additionally, each threat can pose various degrees of network disruption ranging from low/moderate impact (where damage from these attacks have the potential to disrupt core business functions and access some sensitive data) to severe/catastrophic impact (where business functions are severely impacted, outages of critical services occur, sensitive data is compromised, and systems and infrastructure are destroyed).
Starting at the top of the diagram, the Juniper Connected Security includes products that can detect and combat these threats by leveraging the entire network and ecosystem.
JSA Series Secure Analytics Appliance (physical and virtual) is an industry-leading security information and event management (SIEM) system optimized for virtualized environments, and suited for cloud-based deployments.
ATP Cloud (Advanced Threat Prevention Cloud) is a cloud-based solution that integrates with Policy Enforcer to secure sensitive data and detect malware in a cloud shared environment. The SRX device sends the threat information to the ATP Cloud. ATP Cloud then gathers information about the threats (inside and outside the network perimeter) and reports it to Policy Enforcer. Policy Enforcer learns about these threats, and based on the configured policy, the enforcement points then respond to and take action to block and quarantine those threats.
Advanced Threat Prevention (ATP) Appliance (physical and virtual) leverages advanced machine learning and behavioral analysis technologies to identify existing and unknown advanced threats in near real time through continuous, multistage detection and analysis of Web, email, and lateral spread traffic.
Threat intelligence (TI) and Command & Control (C&C) feeds are ongoing internal and external streams of data related to potential or current threats to your company’s security. Possible sources of threat intelligence data include free and paid feeds, bulletins, internal intelligence gathering and strategic partnerships. Policy Enforcer can also gather third-party feeds, and based on the configured policy, the enforcement points can then respond to and take action to block and quarantine those threats.
Enforcement Everywhere
Continuing clock-wise from the top of the Juniper Connected Security diagram, any physical or virtual point of the network can be used as enforcement point including: switches, firewalls, and routers, public cloud and private cloud platforms, and third-party devices.
Juniper Networks’ Devices
Policy Enforcer integrates with Juniper’s physical and virtual devices: switches, firewalls, and routers. With information learned from threat detection, Policy Enforcer automatically updates security policies with dynamic address entries and deploys new enforcement to firewalls and switches, blocking, quarantining and tracking infected hosts in the network.
EX Series and QFX Series switches. EX Series switches deliver switching services in branch, campus, and data center networks, while QFX Series switches are high-performance, high-density edge devices optimized for data center environments. These switches provide access security, control, and connection to servers and clients. EX Series and QFX Series devices act as access and aggregation switches, and connect clients/endpoints with endpoint protection software.
SRX Series next-generation physical, virtual (vSRX), and container (cSRX) firewalls provide high-performance network security with advanced integrated threat intelligence delivered on a scalable and resilient platform. You can modernize and upgrade your perimeter to make it adaptable, while simplifying your network and removing niche appliances. SRX Series firewalls connect EX Series and QFX Series switches securely. You can use Security Director to manage the SRX Series firewalls to provide security enforcement and deep inspection across all network layers and applications. Juniper Secure Connect on SRX Series devices allows you to securely connect and access protected resources on your network from devices anywhere across the globe.
MX Series and vMX (virtual MX) Series routers support a universal set of edge applications, enabling you to rapidly respond to evolving business and technical requirements, simplify operations, and gain flexibility. With the Juniper Trio chipset, you can scale MX Series routers for bandwidth, subscribers, and services, and support new features without upgrading hardware. MX Series routers with Corero SmartWall Threat Defense Director deliver real-time DDoS protection on networks.
Juniper Wireless Access Points work in conjunction with the Juniper Mist Cloud Architecture and Mist AI to collect and analyze metadata in near real-time from all wireless clients.
Private and Public Cloud Hosting Platforms
Juniper Connected Security taps into the power of cloud computing by adopting an open, multivendor ecosystem to detect and enforce security across Juniper solutions, private and public clouds, and third-party ecosystems.
Private cloud (also known as internal, corporate, or enterprise cloud) –A cloud type implemented in a proprietary network or data center that uses cloud computing technologies to create a virtualized infrastructure dedicated to the needs and goals of a single organization, whether managed internally or externally. Private cloud examples are: VMware NSX, Juniper Contrail.
Public cloud–A cloud type in which a hosting service provider makes resources such as applications, storage, and CPU usage available to the public. Public clouds must be based on a standard cloud computing model. Public cloud examples are Amazon AWS, Google Cloud Platform (GCP), and Microsoft Azure.
Third-Party Devices
The Juniper Connected Security enforces threat prevention policies for the following third-party devices:
Access security points. Supports any network element (physical devices, virtual machines, software applications, third-party switches, wi-fi devices, and mobile devices) that is part of a network access controller (NAC) solution, such as: Cisco Identity Services Engine (ISE), Aruba ClearPass, ForeScout CounterACT, or Cisco’s Wireless LAN Controller (WLC).
