ON THIS PAGE
Example: Configuring IS-IS
This example shows how to configure IS-IS in a simple two-device network topology.
Our content testing team has validated and updated this example.
Requirements
No special configuration beyond device initialization is required before configuring this example.
Are you interested in getting hands-on experience on this feature?
Visit Juniper vLabs to reserve your pre-configured vLab Sandbox: IS-IS - Single-area and try it for free!
Overview
In this example, you configure two devices, Device R1 and Device R2, within a single IS-IS area.
To enable IS-IS routing, you must:
-
Configure a NET address (also known as the system ID or the NSAP address) on one of the device interfaces (preferably, the lo0 interface) by including the
family iso address net-addressstatement on the interface. -
Configure the ISO family on all interfaces that are supporting the IS-IS protocol by including the
family isostatement on the interface. -
Advertise the device interfaces into IS-IS by inlcuding the
interface interface-namestatement in the protocol configuration. -
(On security devices only) Enable the forwarding of IS-IS traffic by including the
family mode packet-basedstatement in the security forwarding options configuration.Note:Junos releases prior to and including 19.2R1-S2 supported ISIS PDU exchange without explicitly setting packet mode for ISIS under
[edit security forwarding-options family iso]. In newer releases this setting is required in order for ISIS to operate properly. When upgrading an SRX device to a Junos version newer than 19.2R1-S2 you must configure packet mode for ISIS or adjacencies will not form.
Figure 1 shows the topology used in this example.
In this example, we use NET addresses that incorporate the router's loopback IP addresses (49.0002.0192.0168.0001.00 and 49.0002.0192.0168.0002.00) for readability and learning purposes. In production environments, we recommend that you derive the system identifier portion of the NET address from the router's MAC address or another unique hardware identifier. For more information about configuring proper NET addresses, see Configuring an ISO System Identifier for the Router.
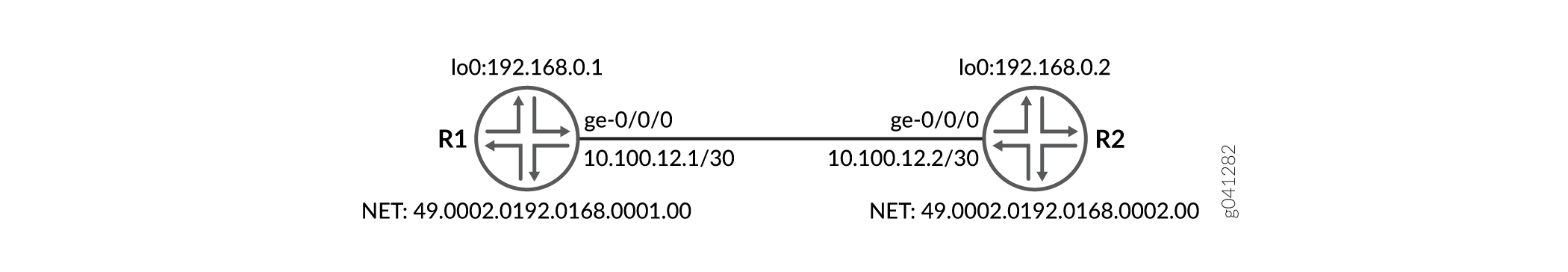
CLI Quick Configuration shows the configuration for both of the devices in Figure 1.
Configuration
Procedure
CLI Quick Configuration
To quickly configure this example, copy the following commands, paste them
into a text file, remove any line breaks, change any details necessary to
match your network configuration, and then copy and paste the commands into
the CLI at the [edit] hierarchy level.
Device R1
set security forwarding-options family iso mode packet-based set interfaces ge-0/0/0 unit 0 description "To R2" set interfaces ge-0/0/0 unit 0 family inet address 10.100.12.1/30 set interfaces ge-0/0/0 unit 0 family iso set interfaces lo0 unit 0 family inet address 192.168.0.1/32 set interfaces lo0 unit 0 family iso address 49.0002.0192.0168.0001.00 set protocols isis interface ge-0/0/0.0 set protocols isis interface lo0.0
Device R2
set security forwarding-options family iso mode packet-based set interfaces ge-0/0/0 unit 0 description "To R1" set interfaces ge-0/0/0 unit 0 family inet address 10.100.12.2/30 set interfaces ge-0/0/0 unit 0 family iso set interfaces lo0 unit 0 family inet address 192.168.0.2/32 set interfaces lo0 unit 0 family iso address 49.0002.0192.0168.0002.00 set protocols isis interface ge-0/0/0.0 set protocols isis interface lo0.0
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode in the CLI User Guide.
To configure IS-IS:
-
(On security devices only) Enable the forwarding of IS-IS traffic to overcome the default behavior of dropping IS-IS traffic.
[edit security] user@R1# set forwarding-options family iso mode packet-based
-
Configure the device interface, and enable the ISO family on the interface.
[edit interfaces] user@R1# set ge-0/0/0 unit 0 description "To R2" user@R1# set ge-0/0/0 unit 0 family inet address 10.100.12.1/30 user@R1# set ge-0/0/0 unit 0 family iso
-
Configure the loopback interface and set the NET address.
[edit interfaces] user@R1# set lo0 unit 0 family inet address 192.168.0.1/32 user@R1# set lo0 unit 0 family iso address 49.0002.0192.0168.0001.00
-
Enable IS-IS for the device interfaces.
[edit protocols] user@R1# set isis interface ge-0/0/0.0 user@R1# set isis interface lo0.0
Results
From configuration mode, confirm your configuration by entering the
show command. If the output does not display the
intended configuration, repeat the instructions in this example to correct
the configuration.
user@R1# show
security {
forwarding-options {
family iso {
mode packet-based;
}
}
}
interfaces {
ge-0/0/0 {
unit 0 {
description "To R2";
family inet {
address 10.100.12.1/30;
}
family iso;
}
}
lo0 {
unit 0 {
family inet {
address 192.168.0.1/32;
}
family iso {
address 49.0002.0192.0168.0001.00;
}
}
}
}
protocols {
isis {
interface ge-0/0/0.0;
interface lo0.0;
}
}If you are done configuring the device, enter commit from
configuration mode.
Verification
Confirm that the configuration is working properly.
Verifying IS-IS Adjacencies and Interfaces
Purpose
Verify that IS-IS adjacencies are up and that the IS-IS interfaces are included in the protocol configuration.
Action
From operational mode, enter the show isis adjacency and show isis interface commands.
user@R1> show isis adjacency Interface System L State Hold (secs) SNPA ge-0/0/0.0 R2 1 Up 7 56:4:1e:0:5f:58 ge-0/0/0.0 R2 2 Up 7 56:4:1e:0:5f:58
user@R1> show isis interface IS-IS interface database: Interface L CirID Level 1 DR Level 2 DR L1/L2 Metric ge-0/0/0.0 3 0x1 R2.02 R2.02 10/10 lo0.0 3 0x1 Passive Passive 0/0
Meaning
Device R1 has established adjacency with Device R2 as indicated by the
State output field which is Up.
Device R1 interfaces are advertised into IS-IS with Device R2 as the
designated router responsible for sending link-state advertisements. Both
the devices are enabled with Level 1 and Level 2 IS-IS as indicated by the
L 3 output field.
Verifying End-to-End Connectivity
Purpose
Verify that the devices are reachable by pinging their loopback addresses.
Action
From operational mode, enter the ping 192.168.0.1 source 192.168.0.2
count 100 rapid command.
user@R1> ping 192.168.0.1 source 192.168.0.2 count 100 rapid PING 192.168.0.2 (192.168.0.2): 56 data bytes !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! --- 192.168.0.2 ping statistics --- 100 packets transmitted, 100 packets received, 0% packet loss round-trip min/avg/max/stddev = 1.807/2.425/6.447/0.553 ms
Meaning
The devices can succcessfully ping each other's loopback address.
