Seguridad avanzada y configuraciones de interconexión del centro de datos
Utilice estos ejemplos para configurar la seguridad avanzada y DCI en la arquitectura de su centro de datos colapsada.
Configurar seguridad avanzada para el tráfico entre inquilinos
La serie SRX es un firewall de última generación que puede proporcionar servicios de seguridad avanzados para el tráfico entre inquilinos. Utilice esta sección para enrutar el tráfico entre inquilinos entre JNPR_1 y JNPR_2 en DC1 a través del clúster de chasis SRX.
Requisitos
Los dispositivos que configuró en Cómo configurar una columna contraída con multiconexión EVPN.
El clúster de chasis SRX ya debe estar configurado y en ejecución. Consulte Configuración de clústeres de chasis en dispositivos de la serie SRX para obtener más información sobre cómo habilitar un clúster de chasis SRX.
Visión general
Los firewalls de la serie SRX del clúster de chasis funcionan como un único dispositivo para proporcionar redundancia de nivel de servicio, interfaz y dispositivo. Use esta sección para separar el clúster de chasis en zonas y configurar las políticas de enrutamiento para que el tráfico correcto se enrute a través de los dispositivos de seguridad.
Topología
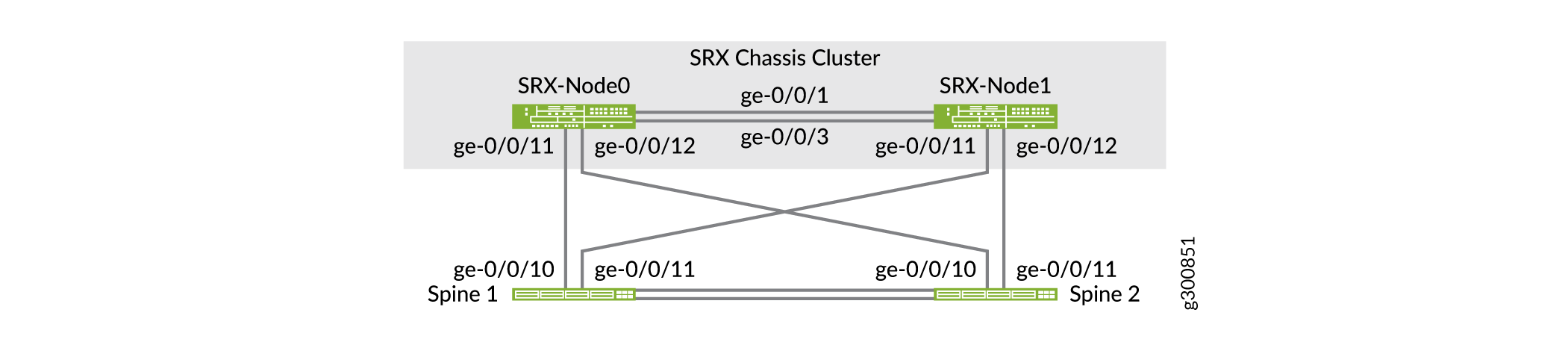
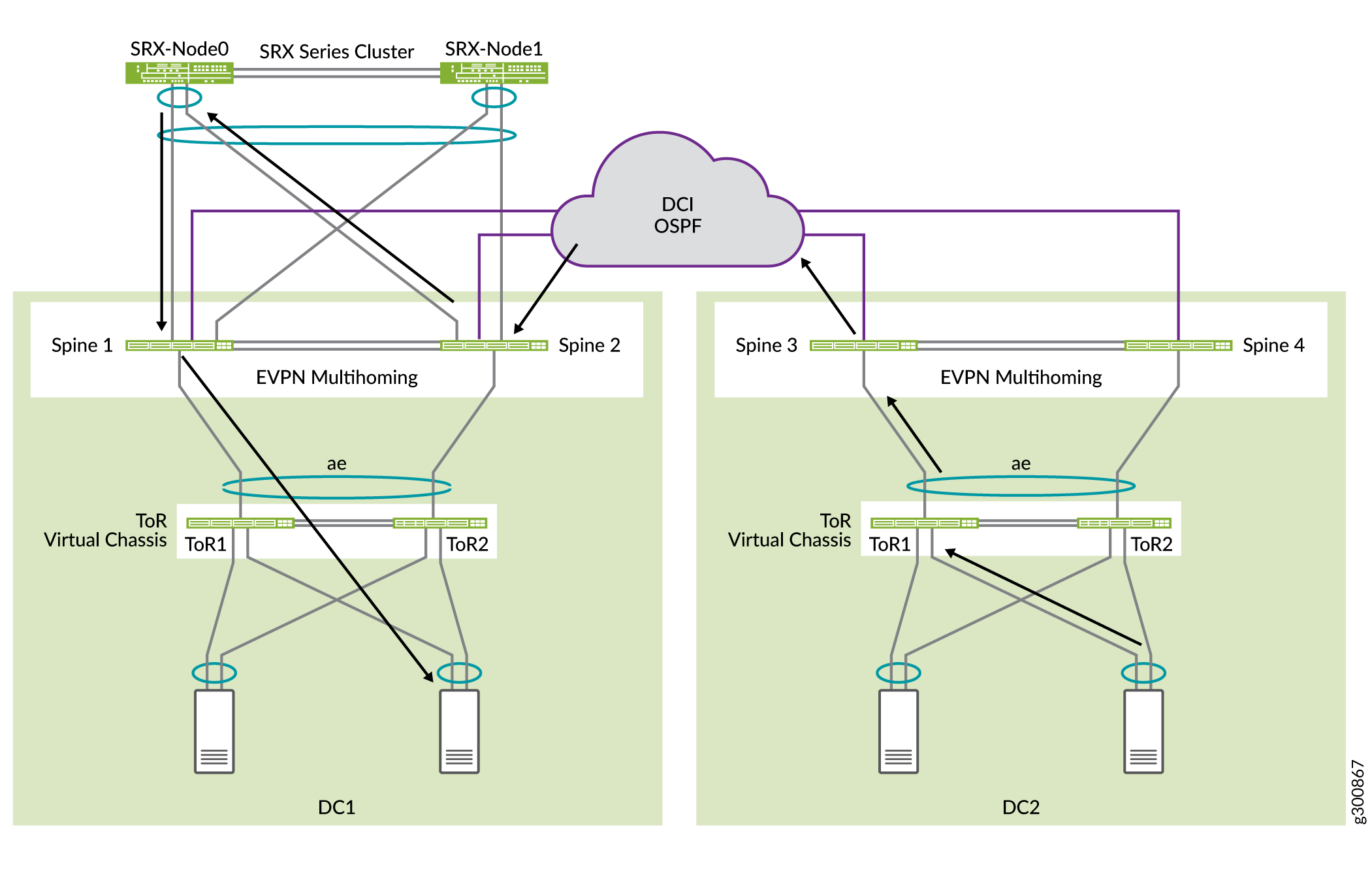
Ambos conmutadores de spine están conectados físicamente a ambos nodos SRX, como se muestra en la Figura 1.
 SRX
SRX
Este ejemplo se basa en dispositivos SRX345. Una vez colocadas en un clúster de alta disponibilidad, las interfaces del nodo 1 se asocian con la ranura 5 de FPC. Esto significa que la interfaz ge-0/0/11 que se muestra para el nodo 1 está configurada como ge-5-0/11 una vez que se forma el clúster. El número de FPC para el nodo 1 en un clúster de alta disponibilidad puede variar según el tipo de modelo SRX.
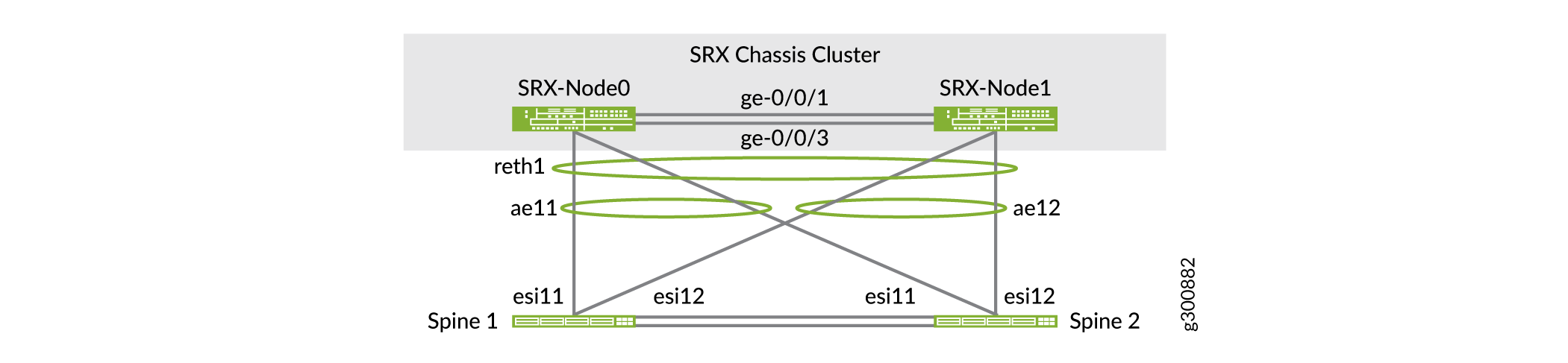
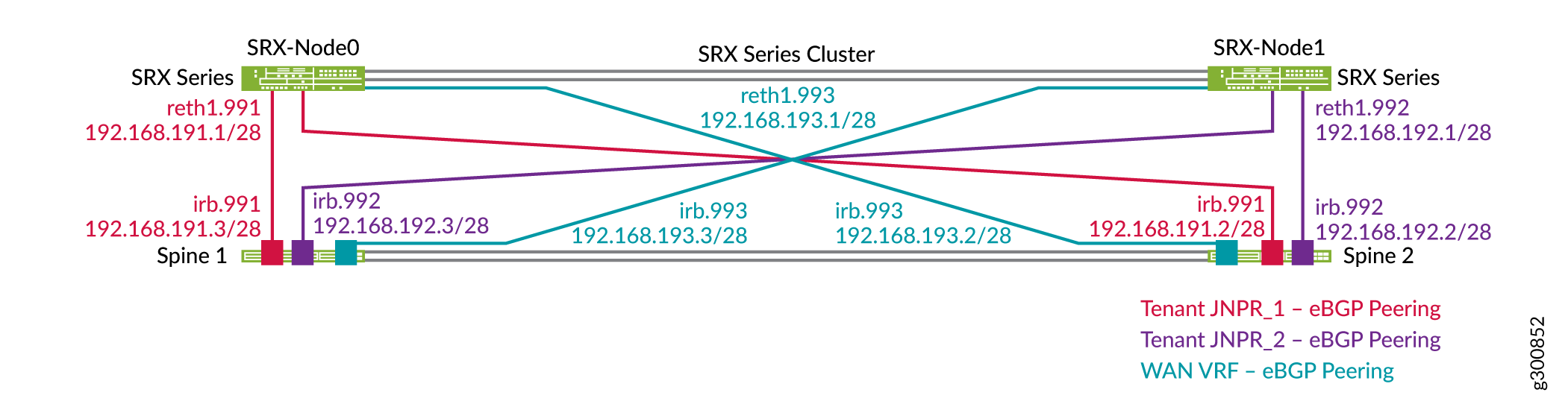
Reth1 es una interfaz lógica en el clúster SRX. Está activo en uno de los nodos del clúster SRX. Si el nodo principal o el vínculo de interconexión entre los dispositivos SRX y los conmutadores spine fallan, Reth1 conmutará por error al nodo secundario. La figura 2 muestra las interfaces lógicas entre los dispositivos SRX y los conmutadores spine.
 SRX
SRX
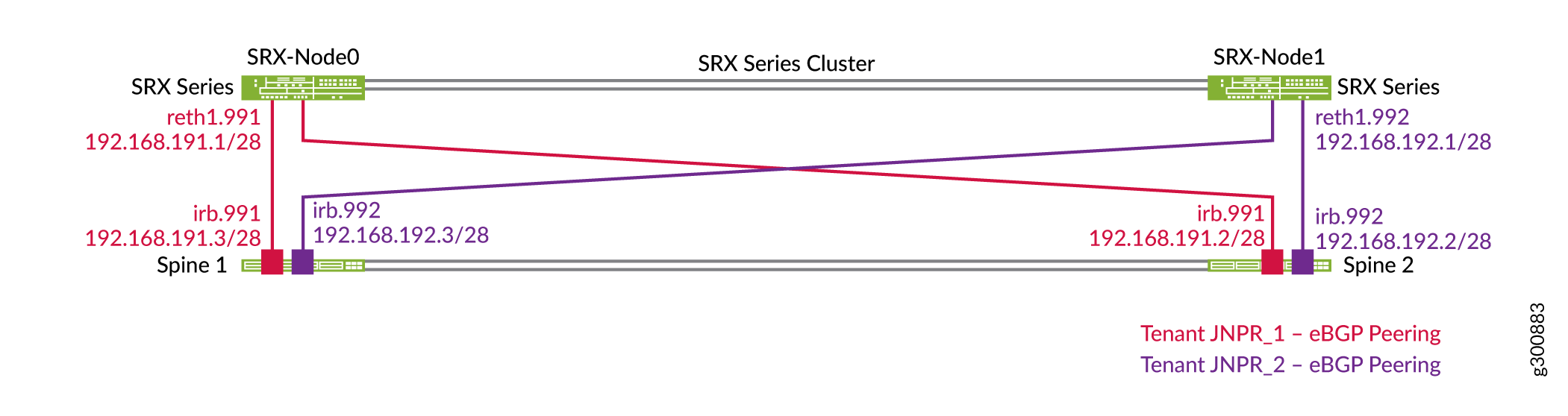
Cada conmutador spine establece emparejamientos EBGP independientes con el clúster SRX en cada instancia de enrutamiento o inquilino, como se muestra en la figura 3. Por ejemplo, Spine 1 tiene dos emparejamientos con el clúster SRX, uno en cada instancia de enrutamiento: JNPR_1 y JNPR_2. Reth1.991 se empareja con la instancia de enrutamiento JNPR_1 en los conmutadores spine y pertenece a la zona de seguridad JNPR_1. Reth1.992 se empareja con la instancia de enrutamiento JNPR_2 en los conmutadores spine y pertenece a la zona de seguridad JNPR_2.
El firewall de la serie SRX anuncia una ruta de resumen que cubre todos los prefijos (por ejemplo, 192.168.0.0/16). Los conmutadores de spine anuncian subredes específicas en cada instancia de enrutamiento.
 EBGP
EBGP
Configurar las interfaces
Configurar el dispositivo SRX
Procedimiento paso a paso
Configure el grupo para las interfaces lógicas en el dispositivo SRX.
set chassis cluster reth-count 3 set chassis cluster redundancy-group 0 node 0 priority 100 set chassis cluster redundancy-group 0 node 1 priority 1 set chassis cluster redundancy-group 1 node 0 priority 200 set chassis cluster redundancy-group 1 node 1 priority 100 set chassis cluster redundancy-group 1 preempt set chassis cluster redundancy-group 1 interface-monitor ge-0/0/11 weight 255 set chassis cluster redundancy-group 1 interface-monitor ge-0/0/12 weight 255 set chassis cluster redundancy-group 1 interface-monitor ge-5/0/11 weight 255 set chassis cluster redundancy-group 1 interface-monitor ge-5/0/12 weight 255
Configure las interfaces lógicas. Reth1 es una interfaz etiquetada de capa 3 en el clúster SRX. Reth1.991 se empareja con la instancia de enrutamiento JNPR_1 en los conmutadores spine. Reth1.992 se empareja con la instancia de enrutamiento JNPR_2 en los conmutadores spine.
set interfaces reth1 vlan-tagging set interfaces reth1 redundant-ether-options redundancy-group 1 set interfaces reth1 redundant-ether-options lacp active set interfaces reth1 redundant-ether-options lacp periodic fast set interfaces reth1 unit 991 description "Spine Interconnect for JNPR_1" set interfaces reth1 unit 991 vlan-id 991 set interfaces reth1 unit 991 family inet address 192.168.191.1/28 set interfaces reth1 unit 992 description "Spine Interconnect for JNPR_2" set interfaces reth1 unit 992 vlan-id 992 set interfaces reth1 unit 992 family inet address 192.168.192.1/28 set interfaces ge-0/0/11 description "To Spine1 | ge-0/0/10" set interfaces ge-0/0/11 gigether-options no-auto-negotiation set interfaces ge-0/0/11 gigether-options redundant-parent reth1 set interfaces ge-5/0/11 description "To Spine1 | ge-0/0/11" set interfaces ge-5/0/11 gigether-options no-auto-negotiation set interfaces ge-5/0/11 gigether-options redundant-parent reth1 set interfaces ge-0/0/12 description "To Spine2 | ge-0/0/10" set interfaces ge-0/0/12 gigether-options no-auto-negotiation set interfaces ge-0/0/12 gigether-options redundant-parent reth1 set interfaces ge-5/0/12 description "To Spine2 | ge-0/0/11" set interfaces ge-5/0/12 gigether-options no-auto-negotiation set interfaces ge-5/0/12 gigether-options redundant-parent reth1
Coloque las interfaces lógicas en zonas de seguridad independientes. Reth1.991 pertenece a la zona de seguridad JNPR_1 y Reth1.992 pertenece a la zona de seguridad JNPR_2.
set security zones security-zone JNPR_1-Zone host-inbound-traffic system-services ping set security zones security-zone JNPR_1-Zone host-inbound-traffic protocols bgp set security zones security-zone JNPR_1-Zone interfaces reth1.991 set security zones security-zone JNPR_2-Zone host-inbound-traffic system-services ping set security zones security-zone JNPR_2-Zone host-inbound-traffic protocols bgp set security zones security-zone JNPR_2-Zone interfaces reth1.992
Compruebe el estado del clúster de chasis.
user@srx1> show chassis cluster status Monitor Failure codes: CS Cold Sync monitoring FL Fabric Connection monitoring GR GRES monitoring HW Hardware monitoring IF Interface monitoring IP IP monitoring LB Loopback monitoring MB Mbuf monitoring NH Nexthop monitoring NP NPC monitoring SP SPU monitoring SM Schedule monitoring CF Config Sync monitoring RE Relinquish monitoring Cluster ID: 1 Node Priority Status Preempt Manual Monitor-failures Redundancy group: 0 , Failover count: 1 node0 100 primary no no None node1 1 secondary no no None Redundancy group: 1 , Failover count: 5 node0 200 primary yes no None node1 100 secondary yes no None
Configurar Spine 1
Procedimiento paso a paso
Configure las interfaces interconectadas del firewall de la serie SRX en Spine 1.
set interfaces ge-0/0/10 ether-options 802.3ad ae11 set interfaces ge-0/0/11 ether-options 802.3ad ae12 set interfaces ae11 description "to SRX Cluster | SRX-0" set interfaces ae11 mtu 9216 set interfaces ae11 esi 00:00:00:00:00:00:00:00:01:11 set interfaces ae11 esi all-active set interfaces ae11 aggregated-ether-options lacp active set interfaces ae11 aggregated-ether-options lacp periodic fast set interfaces ae11 aggregated-ether-options lacp system-id 00:00:00:00:01:11 set interfaces ae11 unit 0 family ethernet-switching interface-mode trunk set interfaces ae11 unit 0 family ethernet-switching vlan members VLAN-991 set interfaces ae12 description "to SRX Cluster | SRX-1" set interfaces ae12 mtu 9216 set interfaces ae12 esi 00:00:00:00:00:00:00:00:01:12 set interfaces ae12 esi all-active set interfaces ae12 aggregated-ether-options lacp active set interfaces ae12 aggregated-ether-options lacp periodic fast set interfaces ae11 aggregated-ether-options lacp system-id 00:00:00:00:01:12 set interfaces ae12 unit 0 family ethernet-switching interface-mode trunk set interfaces ae12 unit 0 family ethernet-switching vlan members VLAN-992
Configure las interfaces IRB.
set interfaces irb unit 991 description "Tenant1 SRX Interconnect" set interfaces irb unit 991 family inet address 192.168.191.3/28 set routing-instances JNPR_1_VRF interface irb.991 set interfaces irb unit 992 description "Tenant2 SRX Interconnect" set interfaces irb unit 992 family inet address 192.168.192.3/28 set routing-instances JNPR_2_VRF interface irb.992
Configure las VLAN.
set vlans VLAN-991 vlan-id 991 set vlans VLAN-991 l3-interface irb.991 set vlans VLAN-991 vxlan vni 5991 set vlans VLAN-992 vlan-id 992 set vlans VLAN-992 l3-interface irb.992 set vlans VLAN-992 vxlan vni 5992
Configure VNI como parte del dominio EVPN MP-BGP.
set protocols evpn extended-vni-list 5991 set protocols evpn extended-vni-list 5992
Configurar Spine 2
Procedimiento paso a paso
Configure las interfaces interconectadas del firewall de la serie SRX en Spine 2.
set interfaces ge-0/0/10 ether-options 802.3ad ae11 set interfaces ge-0/0/11 ether-options 802.3ad ae12 set interfaces ae11 description "to SRX Cluster | SRX-0" set interfaces ae11 mtu 9216 set interfaces ae11 esi 00:00:00:00:00:00:00:00:01:11 set interfaces ae11 esi all-active set interfaces ae12 aggregated-ether-options lacp active set interfaces ae12 aggregated-ether-options lacp periodic fast set interfaces ae11 aggregated-ether-options lacp system-id 00:00:00:00:01:11 set interfaces ae11 unit 0 family ethernet-switching interface-mode trunk set interfaces ae11 unit 0 family ethernet-switching vlan members VLAN-991 set interfaces ae12 description "to SRX Cluster | SRX-1" set interfaces ae12 mtu 9216 set interfaces ae12 esi 00:00:00:00:00:00:00:00:01:12 set interfaces ae12 esi all-active set interfaces ae12 aggregated-ether-options lacp active set interfaces ae12 aggregated-ether-options lacp periodic fast set interfaces ae11 aggregated-ether-options lacp system-id 00:00:00:00:01:12 set interfaces ae12 unit 0 family ethernet-switching interface-mode trunk set interfaces ae12 unit 0 family ethernet-switching vlan members VLAN-992
Configure las interfaces IRB.
set interfaces irb unit 991 description "Tenant1 SRX Interconnect" set interfaces irb unit 991 family inet address 192.168.191.2/28 set routing-instances JNPR_1_VRF interface irb.991 set interfaces irb unit 992 description "Tenant2 SRX Interconnect" set interfaces irb unit 992 family inet address 192.168.192.2/28 set routing-instances JNPR_2_VRF interface irb.992
Configure las VLAN.
set vlans VLAN-991 vlan-id 991 set vlans VLAN-991 l3-interface irb.991 set vlans VLAN-991 vxlan vni 5991 set vlans VLAN-992 vlan-id 992 set vlans VLAN-992 l3-interface irb.992 set vlans VLAN-992 vxlan vni 5992
Configure VNI como parte del dominio EVPN MP-BGP.
set protocols evpn extended-vni-list 5991 set protocols evpn extended-vni-list 5992
Configurar EBGP
- Configurar el dispositivo SRX
- Configurar Spine 1
- Configurar Spine 2
- Configurar las políticas de seguridad del firewall de la serie SRX
- Comprobar BGP en el clúster de chasis SRX
Configurar el dispositivo SRX
Procedimiento paso a paso
Configure la interconexión del EBGP.
set protocols bgp group INTERCONNECT type external set protocols bgp group INTERCONNECT import INTERCONNECT-IMPORT set protocols bgp group INTERCONNECT family inet unicast set protocols bgp group INTERCONNECT authentication-key "$ABC123" set protocols bgp group INTERCONNECT export INTERCONNECT-EXPORT set protocols bgp group INTERCONNECT local-as 65200 set protocols bgp group INTERCONNECT multipath multiple-as set protocols bgp group INTERCONNECT bfd-liveness-detection minimum-interval 1000 set protocols bgp group INTERCONNECT bfd-liveness-detection multiplier 3 set protocols bgp group INTERCONNECT neighbor 192.168.191.2 peer-as 65112 set protocols bgp group INTERCONNECT neighbor 192.168.191.3 peer-as 65113 set protocols bgp group INTERCONNECT neighbor 192.168.192.2 peer-as 65212 set protocols bgp group INTERCONNECT neighbor 192.168.192.3 peer-as 65213
Configure las opciones de enrutamiento.
set routing-options static route 192.168.0.0/16 discard
Configure las opciones de directiva.
set policy-options policy-statement INTERCONNECT-EXPORT term Tenant_Aggregate from protocol static set policy-options policy-statement INTERCONNECT-EXPORT term Tenant_Aggregate from route-filter 192.168.0.0/16 exact set policy-options policy-statement INTERCONNECT-EXPORT term Tenant_Aggregate then accept set policy-options policy-statement INTERCONNECT-EXPORT term Advertise_Loopback from protocol direct set policy-options policy-statement INTERCONNECT-EXPORT term Advertise_Loopback from route-filter 192.168.255.1/32 exact set policy-options policy-statement INTERCONNECT-EXPORT term Advertise_Loopback then accept set policy-options policy-statement INTERCONNECT-EXPORT term Reject_All then reject set policy-options policy-statement INTERCONNECT-IMPORT term Tenant_Routes from route-filter 192.168.0.0/16 longer set policy-options policy-statement INTERCONNECT-IMPORT term Tenant_Routes then accept set policy-options policy-statement INTERCONNECT-IMPORT term DEFAULT then reject
Configurar Spine 1
Procedimiento paso a paso
Configure los emparejamientos de EBGP en la instancia de enrutamiento JNPR_1.
set routing-instances JNPR_1_VRF protocols bgp group INTERCONNECT type external set routing-instances JNPR_1_VRF protocols bgp group INTERCONNECT import Interconnect_JNPR_1-IMPORT set routing-instances JNPR_1_VRF protocols bgp group INTERCONNECT family inet unicast set routing-instances JNPR_1_VRF protocols bgp group INTERCONNECT authentication-key "$ABC123" set routing-instances JNPR_1_VRF protocols bgp group INTERCONNECT export Interconnect_JNPR_1-EXPORT set routing-instances JNPR_1_VRF protocols bgp group INTERCONNECT local-as 65113 set routing-instances JNPR_1_VRF protocols bgp group INTERCONNECT multipath multiple-as set routing-instances JNPR_1_VRF protocols bgp group INTERCONNECT bfd-liveness-detection minimum-interval 1000 set routing-instances JNPR_1_VRF protocols bgp group INTERCONNECT bfd-liveness-detection multiplier 3 set routing-instances JNPR_1_VRF protocols bgp group INTERCONNECT neighbor 192.168.191.1 peer-as 65200
Configure los emparejamientos de EBGP en la instancia de enrutamiento JNPR_2.
set routing-instances JNPR_2_VRF protocols bgp group INTERCONNECT type external set routing-instances JNPR_2_VRF protocols bgp group INTERCONNECT import Interconnect_JNPR_2-IMPORT set routing-instances JNPR_2_VRF protocols bgp group INTERCONNECT family inet unicast set routing-instances JNPR_2_VRF protocols bgp group INTERCONNECT authentication-key "$ABC123" set routing-instances JNPR_2_VRF protocols bgp group INTERCONNECT export Interconnect_JNPR_2-EXPORT set routing-instances JNPR_2_VRF protocols bgp group INTERCONNECT local-as 65213 set routing-instances JNPR_2_VRF protocols bgp group INTERCONNECT multipath multiple-as set routing-instances JNPR_2_VRF protocols bgp group INTERCONNECT bfd-liveness-detection minimum-interval 1000 set routing-instances JNPR_2_VRF protocols bgp group INTERCONNECT bfd-liveness-detection multiplier 3 set routing-instances JNPR_2_VRF protocols bgp group INTERCONNECT neighbor 192.168.192.1 peer-as 65200
Configure las políticas de importación y exportación para la interconexión con el dispositivo SRX.
set policy-options policy-statement Interconnect_JNPR_1-EXPORT term Tenant_Routes from route-filter 192.168.0.0/16 orlonger set policy-options policy-statement Interconnect_JNPR_1-EXPORT term Tenant_Routes then accept set policy-options policy-statement Interconnect_JNPR_1-EXPORT term DEFAULT then reject set policy-options policy-statement Interconnect_JNPR_1-IMPORT term Tenant_Routes from route-filter 192.168.0.0/16 orlonger set policy-options policy-statement Interconnect_JNPR_1-IMPORT term Tenant_Routes then accept set policy-options policy-statement Interconnect_JNPR_1-IMPORT term DEFAULT then reject set policy-options policy-statement Interconnect_JNPR_2-EXPORT term Tenant_Routes from route-filter 192.168.0.0/16 orlonger set policy-options policy-statement Interconnect_JNPR_2-EXPORT term Tenant_Routes then accept set policy-options policy-statement Interconnect_JNPR_2-EXPORT term DEFAULT then reject set policy-options policy-statement Interconnect_JNPR_2-IMPORT term Tenant_Routes from route-filter 192.168.0.0/16 orlonger set policy-options policy-statement Interconnect_JNPR_2-IMPORT term Tenant_Routes then accept set policy-options policy-statement Interconnect_JNPR_2-IMPORT term DEFAULT then reject
Configurar Spine 2
Procedimiento paso a paso
-
Configure los emparejamientos de EBGP en la instancia de enrutamiento JNPR_1.
set routing-instances JNPR_1_VRF protocols bgp group INTERCONNECT type external set routing-instances JNPR_1_VRF protocols bgp group INTERCONNECT import Interconnect_JNPR_1-IMPORT set routing-instances JNPR_1_VRF protocols bgp group INTERCONNECT family inet unicast set routing-instances JNPR_1_VRF protocols bgp group INTERCONNECT authentication-key "$ABC123" set routing-instances JNPR_1_VRF protocols bgp group INTERCONNECT export Interconnect_JNPR_1-EXPORT set routing-instances JNPR_1_VRF protocols bgp group INTERCONNECT local-as 65112 set routing-instances JNPR_1_VRF protocols bgp group INTERCONNECT multipath multiple-as set routing-instances JNPR_1_VRF protocols bgp group INTERCONNECT bfd-liveness-detection minimum-interval 1000 set routing-instances JNPR_1_VRF protocols bgp group INTERCONNECT bfd-liveness-detection multiplier 3 set routing-instances JNPR_1_VRF protocols bgp group INTERCONNECT neighbor 192.168.191.1 peer-as 65200
-
Configure los emparejamientos de EBGP en la instancia de enrutamiento JNPR_2.
set routing-instances JNPR_2_VRF protocols bgp group INTERCONNECT type external set routing-instances JNPR_2_VRF protocols bgp group INTERCONNECT import Interconnect_JNPR_2-IMPORT set routing-instances JNPR_2_VRF protocols bgp group INTERCONNECT family inet unicast set routing-instances JNPR_2_VRF protocols bgp group INTERCONNECT authentication-key "$ABC123" set routing-instances JNPR_2_VRF protocols bgp group INTERCONNECT export Interconnect_JNPR_2-EXPORT set routing-instances JNPR_2_VRF protocols bgp group INTERCONNECT local-as 65212 set routing-instances JNPR_2_VRF protocols bgp group INTERCONNECT multipath multiple-as set routing-instances JNPR_2_VRF protocols bgp group INTERCONNECT bfd-liveness-detection minimum-interval 1000 set routing-instances JNPR_2_VRF protocols bgp group INTERCONNECT bfd-liveness-detection multiplier 3 set routing-instances JNPR_2_VRF protocols bgp group INTERCONNECT neighbor 192.168.192.1 peer-as 65200
-
Configure las políticas de importación y exportación para la interconexión con el dispositivo SRX.
set policy-options policy-statement Interconnect_JNPR_1-EXPORT term Tenant_Routes from route-filter 192.168.0.0/16 orlonger set policy-options policy-statement Interconnect_JNPR_1-EXPORT term Tenant_Routes then accept set policy-options policy-statement Interconnect_JNPR_1-EXPORT term DEFAULT then reject set policy-options policy-statement Interconnect_JNPR_1-IMPORT term Tenant_Routes from route-filter 192.168.0.0/16 orlonger set policy-options policy-statement Interconnect_JNPR_1-IMPORT term Tenant_Routes then accept set policy-options policy-statement Interconnect_JNPR_1-IMPORT term DEFAULT then reject set policy-options policy-statement Interconnect_JNPR_2-EXPORT term Tenant_Routes from route-filter 192.168.0.0/16 orlonger set policy-options policy-statement Interconnect_JNPR_2-EXPORT term Tenant_Routes then accept set policy-options policy-statement Interconnect_JNPR_2-EXPORT term DEFAULT then reject set policy-options policy-statement Interconnect_JNPR_2-IMPORT term Tenant_Routes from route-filter 192.168.0.0/16 orlonger set policy-options policy-statement Interconnect_JNPR_2-IMPORT term Tenant_Routes then accept set policy-options policy-statement Interconnect_JNPR_2-IMPORT term DEFAULT then reject
Configurar las políticas de seguridad del firewall de la serie SRX
Procedimiento paso a paso
Configure las directivas de seguridad en la zona 1 para JNPR_1.
set security policies from-zone JNPR_1-Zone to-zone JNPR_2-Zone policy Allow_All match source-address any set security policies from-zone JNPR_1-Zone to-zone JNPR_2-Zone policy Allow_All match destination-address any set security policies from-zone JNPR_1-Zone to-zone JNPR_2-Zone policy Allow_All match application any set security policies from-zone JNPR_1-Zone to-zone JNPR_2-Zone policy Allow_All then permit
Configure las políticas de seguridad en la zona 1 para JNPR_2.
set security policies from-zone JNPR_2-Zone to-zone JNPR_1-Zone policy Allow_All match source-address any set security policies from-zone JNPR_2-Zone to-zone JNPR_1-Zone policy Allow_All match destination-address any set security policies from-zone JNPR_2-Zone to-zone JNPR_1-Zone policy Allow_All match application any set security policies from-zone JNPR_2-Zone to-zone JNPR_1-Zone policy Allow_All then permit
Comprobar BGP en el clúster de chasis SRX
Procedimiento paso a paso
Asegúrese de que se hayan establecido todas las sesiones de emparejamiento BGP con los conmutadores spine.
user@srx> show bgp summary Groups: 1 Peers: 4 Down peers: 0 Table Tot Paths Act Paths Suppressed History Damp State Pending inet.0 26 14 0 0 0 0 Peer AS InPkt OutPkt OutQ Flaps Last Up/Dwn State|#Active/Received/Accepted/Damped... 192.168.191.2 65112 113 106 0 73 47:34 Establ inet.0: 4/7/7/0 192.168.191.3 65113 110 107 0 41 47:35 Establ inet.0: 4/7/7/0 192.168.192.2 65212 111 106 0 71 47:35 Establ inet.0: 3/6/6/0 192.168.192.3 65213 109 106 0 34 47:35 Establ inet.0: 3/6/6/0Compruebe que el firewall de la serie SRX recibió las rutas BGP del inquilino JNPR_1.
user@srx> show route receive-protocol bgp 192.168.191.2 inet.0: 18 destinations, 35 routes (18 active, 0 holddown, 0 hidden) Prefix Nexthop MED Lclpref AS path 192.168.191.0/28 192.168.191.2 65112 I 192.168.191.1/32 192.168.191.2 65112 I 192.168.201.0/24 192.168.191.2 65112 I * 192.168.202.42/32 192.168.191.2 65112 I 192.168.202.0/24 192.168.191.2 65112 I * 192.168.251.12/32 192.168.191.2 65112 I 192.168.251.13/32 192.168.191.2 65112 65100 I
user@srx> show route receive-protocol bgp 192.168.191.3 inet.0: 18 destinations, 35 routes (18 active, 0 holddown, 0 hidden) Prefix Nexthop MED Lclpref AS path 192.168.191.0/28 192.168.191.3 65113 I 192.168.191.1/32 192.168.191.3 65113 I * 192.168.201.0/24 192.168.191.3 65113 I 192.168.202.42/32 192.168.191.3 65113 I * 192.168.202.0/24 192.168.191.3 65113 I 192.168.251.12/32 192.168.191.3 65113 65100 I * 192.168.251.13/32 192.168.191.3 65113 I
Compruebe que el firewall de la serie SRX recibió las rutas BGP del inquilino JNPR_2.
user@srx> show route receive-protocol bgp 192.168.192.2 inet.0: 18 destinations, 35 routes (18 active, 0 holddown, 0 hidden) Prefix Nexthop MED Lclpref AS path 192.168.192.0/28 192.168.192.2 65212 I 192.168.192.1/32 192.168.192.2 65212 I 192.168.211.0/24 192.168.192.2 65212 I 192.168.212.0/24 192.168.192.2 65212 I * 192.168.252.12/32 192.168.192.2 65212 I 192.168.252.13/32 192.168.192.2 65212 65100 I
user@srx> show route receive-protocol bgp 192.168.192.3 inet.0: 18 destinations, 35 routes (18 active, 0 holddown, 0 hidden) Prefix Nexthop MED Lclpref AS path 192.168.192.0/28 192.168.192.3 65213 I 192.168.192.1/32 192.168.192.3 65213 I * 192.168.211.0/24 192.168.192.3 65213 I * 192.168.212.0/24 192.168.192.3 65213 I 192.168.252.12/32 192.168.192.3 65213 65100 I * 192.168.252.13/32 192.168.192.3 65213 I
Compruebe que el clúster de chasis SRX anuncia una ruta de resumen a los dispositivos spine.
user@srx> show route advertising-protocol bgp 192.168.191.2 inet.0: 18 destinations, 35 routes (18 active, 0 holddown, 0 hidden) Prefix Nexthop MED Lclpref AS path * 192.168.0.0/16 Self I * 192.168.255.1/32 Self I
user@srx> show route advertising-protocol bgp 192.168.191.3 inet.0: 18 destinations, 35 routes (18 active, 0 holddown, 0 hidden) Prefix Nexthop MED Lclpref AS path * 192.168.0.0/16 Self I * 192.168.255.1/32 Self I
user@srx> show route advertising-protocol bgp 192.168.192.2 inet.0: 18 destinations, 35 routes (18 active, 0 holddown, 0 hidden) Prefix Nexthop MED Lclpref AS path * 192.168.0.0/16 Self I * 192.168.255.1/32 Self I
user@srx> show route advertising-protocol bgp 192.168.192.3 inet.0: 18 destinations, 35 routes (18 active, 0 holddown, 0 hidden) Prefix Nexthop MED Lclpref AS path * 192.168.0.0/16 Self I * 192.168.255.1/32 Self I
Compruebe el tráfico entre inquilinos mediante el clúster de chasis de SRX.
En este ejemplo, Endpoint12 forma parte de VLAN 212 y de JNPR_2 de inquilinos. Endpoint12 está haciendo ping a Endpoint2, que forma parte de VLAN 201 y JNPR_1 de inquilino, como se muestra en la figura 4. Dado que se trata de tráfico entre inquilinos, este tráfico pasa por el miembro activo del clúster de chasis SRX. SRX-Node0 es el miembro activo del clúster de chasis SRX y SRX-Node1 es el miembro pasivo.
Figura 4: Tráfico entre inquilinos a través del clúster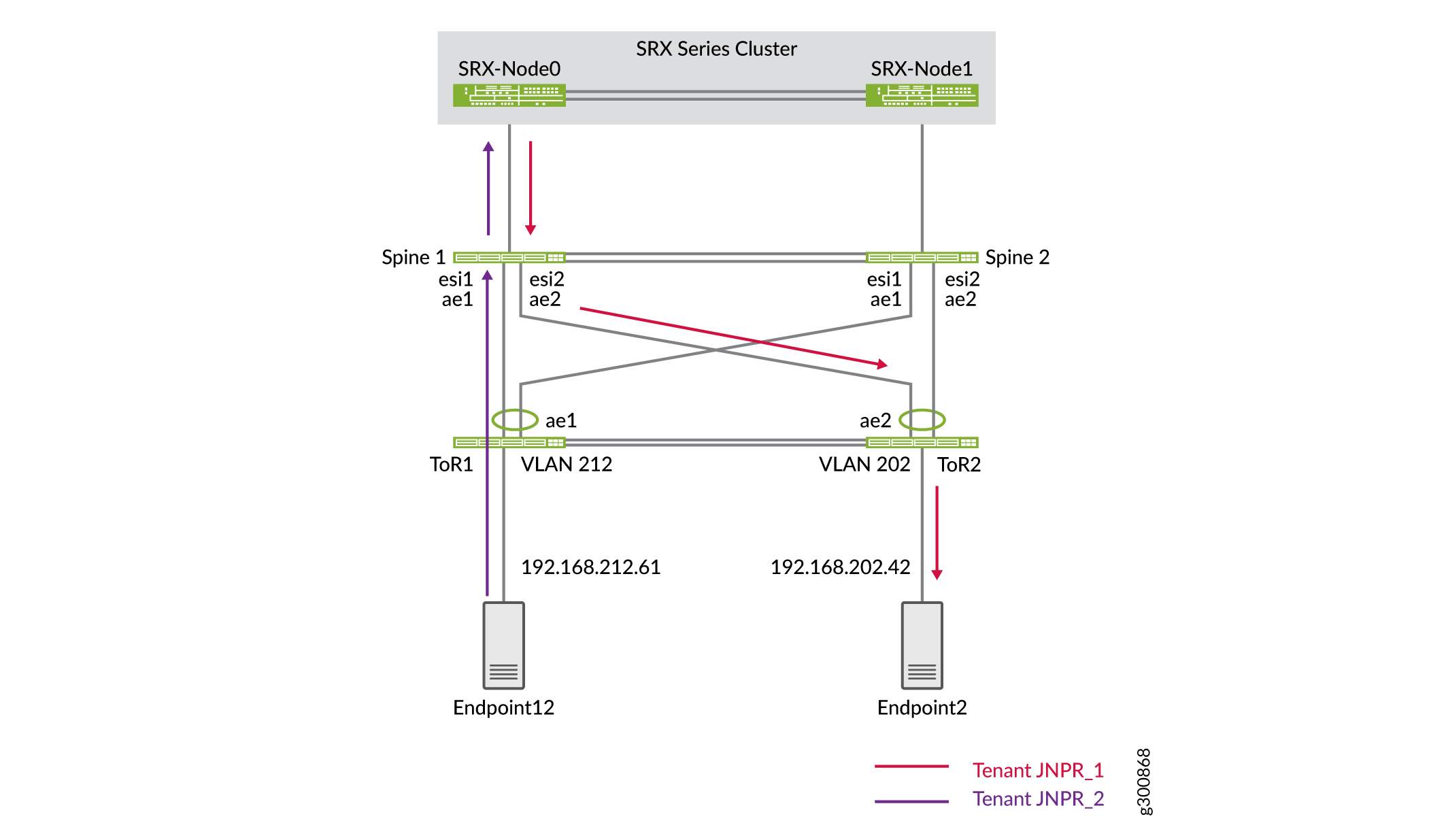 SRX
SRX
Confirme que la tabla de flujo del firewall de la serie SRX muestra este tráfico que atraviesa el clúster de chasis de SRX.
user@srx> show security flow session destination-prefix 192.168.202.42 node0: -------------------------------------------------------------------------- Session ID: 15548, Policy name: Allow_All/7, State: Active, Timeout: 2, Valid In: 192.168.212.61/623 --> 192.168.202.42/8204;icmp, Conn Tag: 0x0, If: reth1.992, Pkts: 1, Bytes: 84, Out: 192.168.202.42/8204 --> 192.168.212.61/623;icmp, Conn Tag: 0x0, If: reth1.991, Pkts: 1, Bytes: 84, Session ID: 15551, Policy name: Allow_All/7, State: Active, Timeout: 2, Valid In: 192.168.212.61/624 --> 192.168.202.42/8204;icmp, Conn Tag: 0x0, If: reth1.992, Pkts: 1, Bytes: 84, Out: 192.168.202.42/8204 --> 192.168.212.61/624;icmp, Conn Tag: 0x0, If: reth1.991, Pkts: 1, Bytes: 84, Session ID: 15555, Policy name: Allow_All/7, State: Active, Timeout: 4, Valid In: 192.168.212.61/625 --> 192.168.202.42/8204;icmp, Conn Tag: 0x0, If: reth1.992, Pkts: 1, Bytes: 84, Out: 192.168.202.42/8204 --> 192.168.212.61/625;icmp, Conn Tag: 0x0, If: reth1.991, Pkts: 1, Bytes: 84, Total sessions: 3
Ha configurado la seguridad avanzada para su centro de datos y ha confirmado que el tráfico entre inquilinos se enruta a través del clúster de chasis de SRX.
Configurar la interconexión del centro de datos (DCI)
Requisitos
Los dispositivos que configuró en Cómo configurar una columna vertebral colapsada con multiconexión EVPN y configurar la seguridad avanzada para el tráfico entre inquilinos.
Visión general
Ahora que ha configurado una arquitectura de columna colapsada para ambos centros de datos y ha agregado seguridad avanzada a DC1, es hora de conectar DC1 y DC2 mediante la interconexión del centro de datos (DCI).
Topología
En este ejemplo, no es necesario extender la capa 2 entre centros de datos. La comunicación entre centros de datos se enruta a través del clúster de chasis SRX en DC1, como se muestra en la figura 5. Cada uno de los conmutadores spine tiene una instancia de enrutamiento WAN y están conectados a la WAN entre centros de datos. Los conmutadores de la columna vertebral transfieren las rutas de capa 3 al enrutador WAN (no se muestra en esta figura).
El clúster de chasis SRX anuncia una subred 192.168.0.0/16. Los conmutadores de spine DC2 Spine 3 y Spine 4 anuncian las dos subredes 192.168.221.0/24 y 192.168.222.0/24.
 datos
datos
Cada firewall de la serie SRX está configurado con tres zonas que corresponden a las instancias de enrutamiento JNPR_1, JNPR_2 y WAN. Todo el tráfico entre JNPR_1 y JNPR_2 se enruta a través del clúster de chasis SRX. Todo el tráfico entre DC1 y DC2 se enruta a través del clúster de chasis SRX mediante la instancia de enrutamiento WAN. Cada firewall de la serie SRX tiene un emparejamiento EBGP individual con Spine 1 y Spine 2 en cada una de las instancias de enrutamiento. La figura 6 muestra el emparejamiento de EBGP entre los conmutadores spine y el clúster de chasis SRX en DC1.
Configuración
Configurar el dispositivo SRX
Procedimiento paso a paso
Cada firewall de la serie SRX debe dividirse en tres zonas que corresponden a las tres instancias de enrutamiento: JNPR_1, JNPR_2 y WAN. Ya creó la zona JNPR_1 y la zona JNPR_2 en Configurar seguridad avanzada para el tráfico entre inquilinos.
Agregue una nueva subinterfaz en Reth1 para la interconexión WAN.
set interfaces reth1 unit 993 description "DC1 Spine Interconnect for WAN VRF" set interfaces reth1 unit 993 vlan-id 993 set interfaces reth1 unit 993 family inet address 192.168.193.1/28
Configure la zona de seguridad WAN.
set security zones security-zone WAN-Zone host-inbound-traffic system-services ping set security zones security-zone WAN-Zone host-inbound-traffic protocols bgp set security zones security-zone WAN-Zone interfaces reth1.993
Configure EBGP para la zona de seguridad WAN.
set protocols bgp group INTERCONNECT neighbor 192.168.193.2 peer-as 65312 set protocols bgp group INTERCONNECT neighbor 192.168.193.3 peer-as 65313
Configure las políticas de seguridad. Para simplificar, las directivas de seguridad de este ejemplo son abiertas. En su configuración, modifique las políticas de seguridad según sea necesario.
set security address-book global address 192.168.221.0/24 192.168.221.0/24 set security address-book global address 192.168.222.0/24 192.168.222.0/24
set security policies from-zone WAN-Zone to-zone JNPR_1-Zone policy ALLOW_ALL match source-address 192.168.221.0/24 set security policies from-zone WAN-Zone to-zone JNPR_1-Zone policy ALLOW_ALL match source-address 192.168.222.0/24 set security policies from-zone WAN-Zone to-zone JNPR_1-Zone policy ALLOW_ALL match destination-address any set security policies from-zone WAN-Zone to-zone JNPR_1-Zone policy ALLOW_ALL match application any set security policies from-zone WAN-Zone to-zone JNPR_1-Zone policy ALLOW_ALL then permit
set security policies from-zone WAN-Zone to-zone JNPR_2-Zone policy ALLOW_ALL match source-address 192.168.221.0/24 set security policies from-zone WAN-Zone to-zone JNPR_2-Zone policy ALLOW_ALL match source-address 192.168.222.0/24 set security policies from-zone WAN-Zone to-zone JNPR_2-Zone policy ALLOW_ALL match destination-address any set security policies from-zone WAN-Zone to-zone JNPR_2-Zone policy ALLOW_ALL match application any set security policies from-zone WAN-Zone to-zone JNPR_2-Zone policy ALLOW_ALL then permit
set security policies from-zone JNPR_1-Zone to-zone WAN-Zone policy ALLOW_ALL match source-address any set security policies from-zone JNPR_1-Zone to-zone WAN-Zone policy ALLOW_ALL match destination-address 192.168.222.0/24 set security policies from-zone JNPR_1-Zone to-zone WAN-Zone policy ALLOW_ALL match destination-address 192.168.221.0/24 set security policies from-zone JNPR_1-Zone to-zone WAN-Zone policy ALLOW_ALL match application any set security policies from-zone JNPR_1-Zone to-zone WAN-Zone policy ALLOW_ALL then permit
set security policies from-zone JNPR_2-Zone to-zone WAN-Zone policy ALLOW_ALL match source-address any set security policies from-zone JNPR_2-Zone to-zone WAN-Zone policy ALLOW_ALL match destination-address 192.168.222.0/24 set security policies from-zone JNPR_2-Zone to-zone WAN-Zone policy ALLOW_ALL match destination-address 192.168.221.0/24 set security policies from-zone JNPR_2-Zone to-zone WAN-Zone policy ALLOW_ALL match application any set security policies from-zone JNPR_2-Zone to-zone WAN-Zone policy ALLOW_ALL then permit
Configurar conmutadores Spine
Procedimiento paso a paso
-
Configure las instancias de enrutamiento y la interfaz IRB en Spine 1.
set interfaces irb unit 993 family inet address 192.168.193.3/28 set routing-instances WAN_VRF description "VRF for tenant WAN" set routing-instances WAN_VRF instance-type vrf set routing-instances WAN_VRF interface et-0/0/48.0 set routing-instances WAN_VRF interface irb.993 set routing-instances WAN_VRF interface lo0.103 set routing-instances WAN_VRF route-distinguisher 192.168.253.13:103 set routing-instances WAN_VRF vrf-target target:3:65001 set routing-instances WAN_VRF vrf-table-label set routing-instances WAN_VRF routing-options auto-export set routing-instances WAN_VRF routing-options multipath set routing-instances WAN_VRF protocols bgp group INTERCONNECT type external set routing-instances WAN_VRF protocols bgp group INTERCONNECT import Interconnect_WAN-IMPORT set routing-instances WAN_VRF protocols bgp group INTERCONNECT family inet unicast set routing-instances WAN_VRF protocols bgp group INTERCONNECT authentication-key "$ABC123" set routing-instances WAN_VRF protocols bgp group INTERCONNECT export Interconnect_WAN-EXPORT set routing-instances WAN_VRF protocols bgp group INTERCONNECT local-as 65313 set routing-instances WAN_VRF protocols bgp group INTERCONNECT multipath multiple-as set routing-instances WAN_VRF protocols bgp group INTERCONNECT bfd-liveness-detection minimum-interval 1000 set routing-instances WAN_VRF protocols bgp group INTERCONNECT bfd-liveness-detection multiplier 3 set routing-instances WAN_VRF protocols bgp group INTERCONNECT neighbor 192.168.193.1 peer-as 65200 set routing-instances WAN_VRF protocols bgp group WAN_UNDERLAY type external set routing-instances WAN_VRF protocols bgp group WAN_UNDERLAY description "Connection to EBGP WAN_UNDERLAY" set routing-instances WAN_VRF protocols bgp group WAN_UNDERLAY family inet unicast set routing-instances WAN_VRF protocols bgp group WAN_UNDERLAY authentication-key "$ABC123" set routing-instances WAN_VRF protocols bgp group WAN_UNDERLAY local-as 65313 set routing-instances WAN_VRF protocols bgp group WAN_UNDERLAY multipath multiple-as set routing-instances WAN_VRF protocols bgp group WAN_UNDERLAY bfd-liveness-detection minimum-interval 350 set routing-instances WAN_VRF protocols bgp group WAN_UNDERLAY bfd-liveness-detection multiplier 3 set routing-instances WAN_VRF protocols bgp group WAN_UNDERLAY neighbor 192.168.100.2 peer-as 65300
Configure las instancias de enrutamiento en Spine 2.
set interfaces irb unit 993 family inet address 192.168.193.2/28 set routing-instances WAN_VRF description "VRF for tenant WAN" set routing-instances WAN_VRF instance-type vrf set routing-instances WAN_VRF interface et-0/0/48.0 set routing-instances WAN_VRF interface irb.993 set routing-instances WAN_VRF interface lo0.103 set routing-instances WAN_VRF route-distinguisher 192.168.253.12:103 set routing-instances WAN_VRF vrf-target target:3:65001 set routing-instances WAN_VRF vrf-table-label set routing-instances WAN_VRF routing-options auto-export set routing-instances WAN_VRF routing-options multipath set routing-instances WAN_VRF protocols bgp group INTERCONNECT type external set routing-instances WAN_VRF protocols bgp group INTERCONNECT import Interconnect_WAN-IMPORT set routing-instances WAN_VRF protocols bgp group INTERCONNECT family inet unicast set routing-instances WAN_VRF protocols bgp group INTERCONNECT authentication-key "$ABC123" set routing-instances WAN_VRF protocols bgp group INTERCONNECT export Interconnect_WAN-EXPORT set routing-instances WAN_VRF protocols bgp group INTERCONNECT local-as 65312 set routing-instances WAN_VRF protocols bgp group INTERCONNECT multipath multiple-as set routing-instances WAN_VRF protocols bgp group INTERCONNECT bfd-liveness-detection minimum-interval 1000 set routing-instances WAN_VRF protocols bgp group INTERCONNECT bfd-liveness-detection multiplier 3 set routing-instances WAN_VRF protocols bgp group INTERCONNECT neighbor 192.168.193.1 peer-as 65200 set routing-instances WAN_VRF protocols bgp group WAN_UNDERLAY type external set routing-instances WAN_VRF protocols bgp group WAN_UNDERLAY description "Connection to EBGP WAN_UNDERLAY" set routing-instances WAN_VRF protocols bgp group WAN_UNDERLAY family inet unicast set routing-instances WAN_VRF protocols bgp group WAN_UNDERLAY authentication-key "$ABC123" set routing-instances WAN_VRF protocols bgp group WAN_UNDERLAY local-as 65312 set routing-instances WAN_VRF protocols bgp group WAN_UNDERLAY multipath multiple-as set routing-instances WAN_VRF protocols bgp group WAN_UNDERLAY bfd-liveness-detection minimum-interval 350 set routing-instances WAN_VRF protocols bgp group WAN_UNDERLAY bfd-liveness-detection multiplier 3 set routing-instances WAN_VRF protocols bgp group WAN_UNDERLAY neighbor 192.168.100.0 peer-as 65300
Configure EBGP en Spine 3.
set protocols bgp group WAN_UNDERLAY type external set protocols bgp group WAN_UNDERLAY description "Connection to EBGP WAN_UNDERLAY" set protocols bgp group WAN_UNDERLAY family inet unicast set protocols bgp group WAN_UNDERLAY authentication-key "$ABC123" set protocols bgp group WAN_UNDERLAY export WAN_EXPORT set protocols bgp group WAN_UNDERLAY local-as 65322 set protocols bgp group WAN_UNDERLAY multipath multiple-as set protocols bgp group WAN_UNDERLAY bfd-liveness-detection minimum-interval 350 set protocols bgp group WAN_UNDERLAY bfd-liveness-detection multiplier 3 set protocols bgp group WAN_UNDERLAY neighbor 192.168.100.10 peer-as 65300 set policy-options policy-statement WAN_EXPORT term DIRECT_ROUTES from protocol direct set policy-options policy-statement WAN_EXPORT term DIRECT_ROUTES from route-filter 192.168.221.0/24 exact set policy-options policy-statement WAN_EXPORT term DIRECT_ROUTES from route-filter 192.168.222.0/24 exact set policy-options policy-statement WAN_EXPORT term DIRECT_ROUTES then accept
Configure EBGP en Spine 4.
set protocols bgp group WAN_UNDERLAY type external set protocols bgp group WAN_UNDERLAY description "Connection to EBGP WAN_UNDERLAY" set protocols bgp group WAN_UNDERLAY family inet unicast set protocols bgp group WAN_UNDERLAY authentication-key "$ABC123" set protocols bgp group WAN_UNDERLAY export WAN_EXPORT set protocols bgp group WAN_UNDERLAY local-as 65323 set protocols bgp group WAN_UNDERLAY multipath multiple-as set protocols bgp group WAN_UNDERLAY bfd-liveness-detection minimum-interval 350 set protocols bgp group WAN_UNDERLAY bfd-liveness-detection multiplier 3 set protocols bgp group WAN_UNDERLAY neighbor 192.168.100.16 peer-as 65300 set policy-options policy-statement WAN_EXPORT term DIRECT_ROUTES from protocol direct set policy-options policy-statement WAN_EXPORT term DIRECT_ROUTES from route-filter 192.168.221.0/24 exact set policy-options policy-statement WAN_EXPORT term DIRECT_ROUTES from route-filter 192.168.222.0/24 exact set policy-options policy-statement WAN_EXPORT term DIRECT_ROUTES then accept
Verificar rutas DCI
Procedimiento paso a paso
Compruebe las rutas en el clúster de chasis SRX. El SRX debe aprender todas las rutas específicas para las diferentes subredes.
user@srx> show route inet.0: 31 destinations, 37 routes (31 active, 0 holddown, 0 hidden) + = Active Route, - = Last Active, * = Both 192.168.201.0/24 *[BGP/170] 00:59:11, localpref 100 AS path: 65113 I, validation-state: unverified > to 192.168.191.3 via reth1.991 192.168.201.10/32 *[BGP/170] 00:00:07, localpref 100 AS path: 65113 I, validation-state: unverified > to 192.168.191.3 via reth1.991 192.168.201.81/32 *[BGP/170] 00:00:07, localpref 100 AS path: 65113 I, validation-state: unverified > to 192.168.191.3 via reth1.991 192.168.202.0/24 *[BGP/170] 00:59:11, localpref 100 AS path: 65113 I, validation-state: unverified > to 192.168.191.3 via reth1.991 192.168.202.61/32 *[BGP/170] 00:59:11, localpref 100 AS path: 65113 I, validation-state: unverified > to 192.168.191.3 via reth1.991 192.168.202.62/32 *[BGP/170] 00:59:11, localpref 100 AS path: 65113 I, validation-state: unverified > to 192.168.191.3 via reth1.991 192.168.203.0/24 *[BGP/170] 00:59:11, localpref 100 AS path: 65113 I, validation-state: unverified > to 192.168.191.3 via reth1.991 192.168.203.61/32 *[BGP/170] 00:15:09, localpref 100 AS path: 65113 I, validation-state: unverified > to 192.168.191.3 via reth1.991 192.168.211.0/24 *[BGP/170] 00:34:09, localpref 100 AS path: 65213 I, validation-state: unverified > to 192.168.192.3 via reth1.992 192.168.212.0/24 *[BGP/170] 00:34:09, localpref 100 AS path: 65213 I, validation-state: unverified > to 192.168.192.3 via reth1.992 192.168.221.0/24 *[BGP/170] 00:25:07, localpref 100 AS path: 65313 65300 65322 I, validation-state: unverified > to 192.168.193.3 via reth1.993 192.168.222.0/24 *[BGP/170] 00:25:07, localpref 100 AS path: 65313 65300 65322 I, validation-state: unverified > to 192.168.193.3 via reth1.993Verifique las rutas en Spine 1 y Spine 2. El clúster SRX anuncia la ruta de resumen 192.168.0.0/16 a los dispositivos spine en todos los VRF. Todo el tráfico entre VRF y DCI pasa por el clúster de chasis SRX.
user@spine1> show route 192.168.0.0 JNPR_1_VRF.inet.0: 19 destinations, 23 routes (19 active, 0 holddown, 0 hidden) + = Active Route, - = Last Active, * = Both 192.168.0.0/16 *[BGP/170] 01:05:15, localpref 100 AS path: 65200 I, validation-state: unverified > to 192.168.191.1 via irb.991 JNPR_2_VRF.inet.0: 13 destinations, 16 routes (13 active, 0 holddown, 0 hidden) + = Active Route, - = Last Active, * = Both 192.168.0.0/16 *[BGP/170] 00:40:12, localpref 100 AS path: 65200 I, validation-state: unverified > to 192.168.192.1 via irb.992 WAN_VRF.inet.0: 12 destinations, 12 routes (12 active, 0 holddown, 0 hidden) + = Active Route, - = Last Active, * = Both 192.168.0.0/16 *[BGP/170] 01:04:59, localpref 100 AS path: 65200 I, validation-state: unverified > to 192.168.193.1 via irb.993Verifique las rutas en Spine 3 y Spine 4. Los dispositivos spine DC2 reciben la ruta agregada de los VRF WAN en los dispositivos spine DC1. Todo el tráfico entre los dos centros de datos se enruta a través del clúster de chasis SRX.
user@spine3> show route 192.168.0.0 inet.0: 24 destinations, 26 routes (21 active, 0 holddown, 0 hidden) + = Active Route, - = Last Active, * = Both 192.168.0.0/16 [BGP ] 00:11:47 AS path: 65300 65313 65200 I, validation-state: unverified > to 192.168.100.10 via et-0/0/30.0Ha conectado sus redes de centro de datos colapsadas con DCI.
