AUF DIESER SEITE
Beispiel: Konfigurieren von IPSec-VPN in Aktiv-Aktiv-Multinode-Hochverfügbarkeit in einem Layer-3-Netzwerk
In diesem Beispiel wird gezeigt, wie das IPsec-VPN für die Einrichtung einer Aktiv-Aktiv-Multinode-Hochverfügbarkeit konfiguriert und überprüft wird.
Überblick
Bei der Hochverfügbarkeit mit mehreren Knoten arbeiten die teilnehmenden Firewalls der SRX-Serie als unabhängige Knoten in einem Layer-3-Netzwerk. Die Knoten sind mit benachbarter Infrastruktur verbunden, die zu verschiedenen Netzwerken gehört. Ein verschlüsselter logischer Interchassis-Link (ICL) verbindet die Knoten über ein geroutetes Netzwerk. Teilnehmende Knoten sichern sich gegenseitig, um im Falle eines System- oder Hardwareausfalls ein schnelles synchronisiertes Failover zu gewährleisten.
Sie können Multinode-Hochverfügbarkeit im Aktiv-Aktiv-Modus mit Unterstützung mehrerer Services Redundanz-Gruppen (SRGs) betreiben. In diesem Modus bleiben einige SRGs auf einem Knoten und einige SRGs auf einem anderen Knoten aktiv.
Multinode-Hochverfügbarkeit unterstützt IPsec-VPN im Aktiv-Aktiv-Modus mit mehreren SRGs (SRG1+). In diesem Modus können Sie mehrere aktive Tunnel von beiden Knoten aus einrichten, basierend auf der SRG-Aktivität. Multinode-Hochverfügbarkeit richtet einen IPsec-Tunnel ein und führt einen Schlüsselaustausch durch, indem die IP-Adresse der Terminierung (die auch die darauf endenden Tunnel identifiziert) der SRG zugeordnet wird. Da sich auf jedem der Geräte unterschiedliche SRG1+ im aktiven Zustand oder im Backup-Zustand befinden können, lenkt Multinode High Availability den passenden Datenverkehr effektiv zum entsprechenden aktiven SRG1. Da verschiedene SRGs auf verschiedenen Knoten aktiv sein können, werden Tunnel, die zu diesen SRGs gehören, auf beiden Knoten unabhängig voneinander aktiviert.
Wir unterstützen eine Konfiguration mit zwei Knoten in der Multinode-Lösung für hohe Verfügbarkeit.
Anforderungen
In diesem Beispiel werden die folgenden Hardware- und Softwarekomponenten verwendet:
Zwei Firewalls der SRX-Serie (unterstützte Geräte sind SRX5400, SRX5600 und SRX5800 mit SPC3, IOC3, SCB3, SCB4 und RE3)
Junos OS Version 22.4R1
In diesem Beispiel haben wir zwei Juniper Networks MX-Serie Routing-Plattform als Upstream-/Downstream-Router verwendet.
Bevor Sie beginnen
Konfigurieren Sie zustandslose Firewall-Filterung und Quality of Service (QoS) gemäß Ihren Netzwerkanforderungen und verfügen Sie über geeignete Sicherheitsrichtlinien zur Verwaltung des Datenverkehrs in Ihrem Netzwerk.
In einer typischen Hochverfügbarkeits-Bereitstellung verfügen Sie über mehrere Router und Switches auf der Nord- und Südseite des Netzwerks. In diesem Beispiel verwenden wir zwei Router auf beiden Seiten der Firewalls der SRX-Serie. Stellen Sie sicher, dass Sie vor- und nachgelagerte Router gemäß Ihren Netzwerkanforderungen konfiguriert haben.
Installieren Sie das Junos IKE-Paket mit dem folgenden Befehl
request system software add optional://junos-ike.tgzauf Ihren Firewalls der SRX-Serie. Dasjunos-ikePaket ist in Ihren Junos-Softwarepaketen (Junos OS Version 20.4R1 und höher) enthalten.
Topologie
Abbildung 1 zeigt die in diesem Beispiel verwendete Topologie.
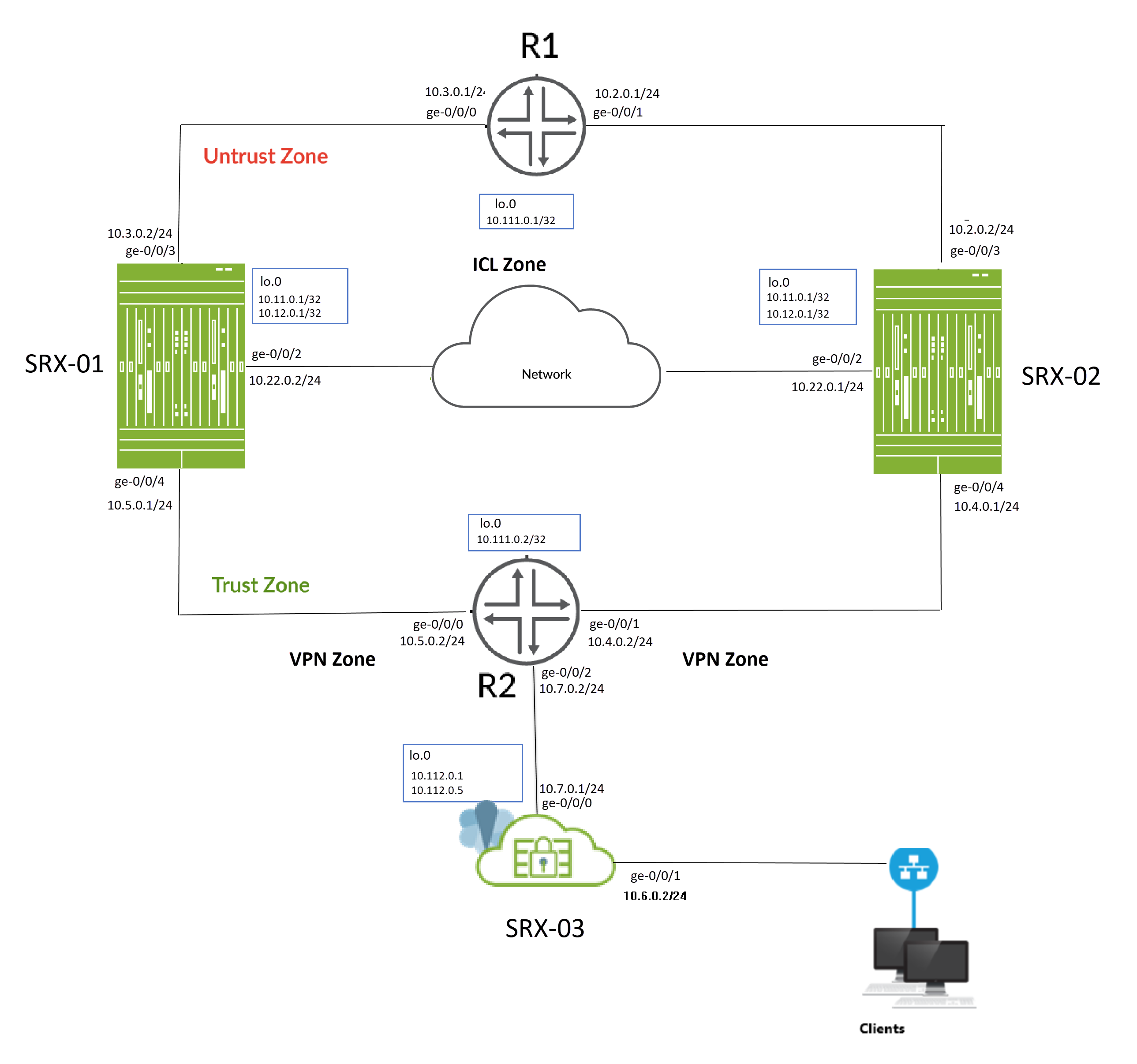
Wie in der Topologie dargestellt, sind zwei Firewalls der SRX-Serie (SRX-1 und SRX-2) mit benachbarten Routern auf der vertrauenswürdigen und nicht vertrauenswürdigen Seite verbunden und bilden eine BGP-Nachbarschaft. Ein verschlüsselter logischer Interchassis-Link (ICL) verbindet die Knoten über ein geroutetes Netzwerk. Die Knoten kommunizieren untereinander über eine routingfähige IP-Adresse (Floating-IP-Adresse) über das Netzwerk.
Das SRX-03-Gerät fungiert als Peer-Gerät für das Multinode-Setup mit hoher Verfügbarkeit und richtet IPsec-VPN-Tunnel mit SRX-01- und SRX-02-Geräten ein.
Sie führen die folgenden Aufgaben aus, um ein Multinode-Hochverfügbarkeits-Setup zu erstellen:
- Konfigurieren Sie ein Paar Firewalls der SRX-Serie als lokale und Peer-Knoten durch Zuweisen von IDs.
- Konfigurieren Sie Service-Redundanz-Gruppen (SRG1 und SRG2).
- Konfigurieren Sie eine Loopback-Schnittstelle (lo0.0), um die Floating-IP-Adresse zu hosten und das Peer-Gateway zu erreichen. Durch die Verwendung der Loopback-Schnittstelle wird sichergestellt, dass der Datenverkehr von den benachbarten Routern zu jedem beliebigen Zeitpunkt zur Floating-IP-Adresse (d. h. zum aktiven Knoten) geleitet wird.
- Konfigurieren von IP-Sonden für die Aktivitätsbestimmung und -erzwingung
- Konfigurieren Sie eine Signalroute, die für die Aktivitätserzwingung erforderlich ist, und verwenden Sie sie zusammen mit der Richtlinie "Route existiert".
- Konfigurieren Sie ein VPN-Profil für den ICL-Datenverkehr (High Availability) mit IKEv2.
- BFD-Überwachungsoptionen konfigurieren
- Konfigurieren einer Routing-Richtlinie und von Routing-Optionen
- Konfigurieren Sie Schnittstellen und Zonen entsprechend Ihren Netzwerkanforderungen. Sie müssen Dienste wie IKE für die Linkverschlüsselung und SSH für die Konfigurationssynchronisierung als Host-Eingangssystemdienste in der Sicherheitszone zulassen, die der ICL zugeordnet ist.
-
Erstellen Sie eine Gruppenkonfiguration für IPsec-VPN auf SRX-01- und SRX-02-Geräten, um einen Tunnel mit VPN-Peer-Gerät (SRX-03) einzurichten. Konfigurationsgruppen ermöglichen es Ihnen, gemeinsame Elemente anzuwenden, die in derselben Konfiguration wiederverwendet werden.
- Konfigurieren Sie IPsec-VPN-Optionen, um Tunnel mit dem SRX-03-Gerät einzurichten, und aktivieren Sie die Synchronisierung der IPsec-VPN-Konfiguration auf beiden Geräten (SRX-01 und SRX-02) mithilfe der Option [groups].
- Konfigurieren Sie VPN-Peer-Geräte mit IPsec-VPN-Optionen.
Für Interchassis Link (ICL) empfehlen wir die folgende Konfiguration:
-
Im Allgemeinen können Sie aggregiertes Ethernet (AE) oder einen Revenue-Ethernet-Port der Firewalls der SRX-Serie verwenden, um eine ICL-Verbindung einzurichten. In diesem Beispiel haben wir GE-Ports für die ICL verwendet. Wir haben auch eine Routing-Instanz für den ICL-Pfad konfiguriert, um eine maximale Segmentierung zu gewährleisten.
- Verwenden Sie nicht die dedizierten Ports für hohe Verfügbarkeit (Kontroll- und Fabric-Ports), sofern diese auf Ihrer Firewall der SRX-Serie verfügbar sind.
- Set MTU von 1514
- Lassen Sie die folgenden Services in der Sicherheitszone zu, die den für ICL verwendeten Schnittstellen zugeordnet ist
-
IKE, Hochverfügbarkeit, SSH
-
Protokolle abhängig vom Routing-Protokoll, das Sie benötigen.
-
BFD zur Überwachung der benachbarten Routen.
-
Sie können die folgenden Optionen auf SRG0 und SRG1+ konfigurieren:
Sie können die folgenden Optionen auf SRG0 und SRG1 konfigurieren:
-
SRG1: Aktive/Backup-Signalroute, Bereitstellungstyp, Aktivitätspriorität, Unterbrechung, virtuelle IP-Adresse (für Standard-Gateway-Bereitstellungen), Aktivitätssondierung und Prozesspaket bei Backup.
-
SRG1: BFD-Überwachung, IP-Überwachung und Schnittstellenüberwachungsoptionen auf SRG1.
-
SRG0: Routenoptionen für das Herunterfahren bei Fehler und Installieren bei Fehler.
Wenn Sie Überwachungsoptionen (BFD oder IP oder Schnittstelle) unter SRG1 konfigurieren, wird empfohlen, die Option zum Herunterfahren bei Fehler nicht unter SRG0 zu konfigurieren.
-
SRG1: Aktive/Backup-Signalroute, Bereitstellungstyp, Aktivitätspriorität, Unterbrechung, virtuelle IP-Adresse (für Standard-Gateway-Bereitstellungen), Aktivitätssondierung und Prozesspaket bei Backup.
-
SRG1: BFD-Überwachung, IP-Überwachung und Schnittstellenüberwachungsoptionen auf SRG1.
-
SRG0: Routenoptionen für das Herunterfahren bei Fehler und Installieren bei Fehler.
Wenn Sie Überwachungsoptionen (BFD oder IP oder Schnittstelle) unter SRG1 konfigurieren, wird empfohlen, die Option zum Herunterfahren bei Fehler nicht unter SRG0 zu konfigurieren.
Tabelle 1 zeigt die Details zur Schnittstellenkonfiguration, die in diesem Beispiel verwendet wird.
| IP-Adresse | derGeräteschnittstellenzone | , | konfiguriert für | |
|---|---|---|---|---|
| SRX-01 | lo0 | Nicht vertrauenswürdig |
10.11.0.1/32 |
Floating IP-Adresse IKE Gateway-Adresse |
| 10.12.0.1/32 |
IKE Gateway-Adresse |
|||
| GE-0/0/2 |
ICL |
10.22.0.2/24 |
ICL anschließen |
|
| GE-0/0/4 |
Vertrauen |
10.5.0.1/24 |
Verbindet sich mit dem R2-Router |
|
| GE-0/0/3 |
Nicht vertrauenswürdig |
10.3.0.2/24 |
Verbindet sich mit dem R1-Router |
|
| SRX-02 | lo0 |
Nicht vertrauenswürdig |
10.12.0.1/32 |
Floating IP-Adresse IKE Gateway-Adresse |
| 10.11.0.1/32 |
IKE Gateway-Adresse |
|||
| GE-0/0/2 |
ICL |
10.22.0.1/24 |
ICL anschließen |
|
| GE-0/0/3 |
Nicht vertrauenswürdig |
10.2.0.2/24 |
Verbindet sich mit dem R1-Router |
|
| GE-0/0/4 |
Vertrauen |
10.4.0.1/24 |
Verbindet sich mit dem R2-Router |
|
| SRX-03 | lo0 | Nicht vertrauenswürdig |
10.112.0.1/32 |
IKE Gateway-Adresse |
| 10.112.0.5/32 |
IKE Gateway-Adresse |
|||
| GE-0/0/0 |
Nicht vertrauenswürdig |
10.7.0.1/24 |
Verbindet sich mit dem R2-Router |
|
| GE-0/0/2 |
Vertrauen |
10.6.0.2/24 |
Stellt eine Verbindung zum Client-Gerät her |
| IP-Adresse | derGeräteschnittstelle | konfiguriert für | |
|---|---|---|---|
| R2 | lo0 | 10.111.0.2/32 |
Loopback-Schnittstellenadresse von R2 |
| GE-0/0/1 |
10.4.0.2/24 |
Verbindung mit SRX-02 |
|
| GE-0/0/0 |
10.5.0.2/24 |
Verbindung zu SRX-01 |
|
| GE-0/0/2 |
10.7.0.2/24 |
Verbindet sich mit SRX-03 (VPN-Peer-Gerät) |
|
| R1 | lo0 | 10.111.0.1/32 |
Loopback-Schnittstellenadresse von R1 |
| GE-0/0/0 |
10.3.0.1/24 |
Verbindung zu SRX-01 |
|
| GE-0/0/1 |
10.2.0.1/24 |
Verbindung mit SRX-02 |
Konfiguration
- Bevor Sie beginnen
- CLI-Schnellkonfiguration
- Konfiguration
- Konfiguration (SRX-03) (VPN-Peer-Gerät)
- Ergebnisse (SRX-01)
- Ergebnisse (SRX-02)
- Ergebnisse (SRX-3) (VPN-Peer-Gerät)
Bevor Sie beginnen
Das Junos IKE-Paket ist für Ihre Firewalls der SRX-Serie für die Multinode-Hochverfügbarkeitskonfiguration erforderlich. Dieses Paket ist als Standardpaket oder als optionales Paket für Firewalls der SRX-Serie erhältlich. Weitere Informationen finden Sie unter Unterstützung für das Junos IKE-Paket .
Wenn das Paket nicht standardmäßig auf Ihrer Firewall der SRX-Serie installiert ist, verwenden Sie den folgenden Befehl, um es zu installieren. Sie benötigen diesen Schritt für die ICL-Verschlüsselung.
user@host> request system software add optional://junos-ike.tgz Verified junos-ike signed by PackageProductionECP256_2022 method ECDSA256+SHA256 Rebuilding schema and Activating configuration... mgd: commit complete Restarting MGD ... WARNING: cli has been replaced by an updated version: CLI release 20220208.163814_builder.r1239105 built by builder on 2022-02-08 17:07:55 UTC Restart cli using the new version ? [yes,no] (yes)
CLI-Schnellkonfiguration
Um dieses Beispiel schnell zu konfigurieren, kopieren Sie die folgenden Befehle, fügen Sie sie in eine Textdatei ein, entfernen Sie alle Zeilenumbrüche, ändern Sie alle erforderlichen Details, damit sie mit Ihrer Netzwerkkonfiguration übereinstimmen, kopieren Sie die Befehle, fügen Sie sie [edit] in die CLI auf Hierarchieebene ein und geben Sie sie dann im Konfigurationsmodus ein commit .
SRX-01 Gerät
set groups vpn_config when peers SRX-01 set groups vpn_config when peers SRX-02 set groups vpn_config security ike proposal SRG1_IKE_PROP authentication-method pre-shared-keys set groups vpn_config security ike proposal SRG1_IKE_PROP dh-group group14 set groups vpn_config security ike proposal SRG1_IKE_PROP authentication-algorithm sha-256 set groups vpn_config security ike proposal SRG1_IKE_PROP encryption-algorithm aes-256-cbc set groups vpn_config security ike proposal SRG1_IKE_PROP lifetime-seconds 3600 set groups vpn_config security ike proposal SRG2_IKE_PROP authentication-method pre-shared-keys set groups vpn_config security ike proposal SRG2_IKE_PROP dh-group group14 set groups vpn_config security ike proposal SRG2_IKE_PROP authentication-algorithm sha-256 set groups vpn_config security ike proposal SRG2_IKE_PROP encryption-algorithm aes-256-cbc set groups vpn_config security ike proposal SRG2_IKE_PROP lifetime-seconds 3600 set groups vpn_config security ike policy SRG1_IKE_POL1 proposals SRG1_IKE_PROP set groups vpn_config security ike policy SRG1_IKE_POL1 pre-shared-key ascii-text "$ABC123" set groups vpn_config security ike policy SRG2_IKE_POL500 proposals SRG2_IKE_PROP set groups vpn_config security ike policy SRG2_IKE_POL500 pre-shared-key ascii-text "$ABC123" set groups vpn_config security ike gateway SRG1_IKE_GW1 ike-policy SRG1_IKE_POL1 set groups vpn_config security ike gateway SRG1_IKE_GW1 address 10.112.0.1 set groups vpn_config security ike gateway SRG1_IKE_GW1 external-interface lo0 set groups vpn_config security ike gateway SRG1_IKE_GW1 local-address 10.11.0.1 set groups vpn_config security ike gateway SRG1_IKE_GW1 version v2-only set groups vpn_config security ike gateway SRG2_IKE_GW500 ike-policy SRG2_IKE_POL500 set groups vpn_config security ike gateway SRG2_IKE_GW500 address 10.112.0.5 set groups vpn_config security ike gateway SRG2_IKE_GW500 external-interface lo0 set groups vpn_config security ike gateway SRG2_IKE_GW500 local-address 10.12.0.1 set groups vpn_config security ike gateway SRG2_IKE_GW500 version v2-only set groups vpn_config security ipsec proposal SRG1_IPSEC_PROP protocol esp set groups vpn_config security ipsec proposal SRG1_IPSEC_PROP authentication-algorithm hmac-sha-256-128 set groups vpn_config security ipsec proposal SRG1_IPSEC_PROP encryption-algorithm aes-256-cbc set groups vpn_config security ipsec proposal SRG1_IPSEC_PROP lifetime-seconds 1800 set groups vpn_config security ipsec proposal SRG2_IPSEC_PROP protocol esp set groups vpn_config security ipsec proposal SRG2_IPSEC_PROP authentication-algorithm hmac-sha-256-128 set groups vpn_config security ipsec proposal SRG2_IPSEC_PROP encryption-algorithm aes-256-cbc set groups vpn_config security ipsec proposal SRG2_IPSEC_PROP lifetime-seconds 1800 set groups vpn_config security ipsec policy SRG1_IPSEC_POL1 proposals SRG1_IPSEC_PROP set groups vpn_config security ipsec policy SRG2_IPSEC_POL501 proposals SRG2_IPSEC_PROP set groups vpn_config security ipsec policy SRG2_IPSEC_POL500 proposals SRG2_IPSEC_PROP set groups vpn_config security ipsec policy SRG2_IPSEC_POL502 proposals SRG2_IPSEC_PROP set groups vpn_config security ipsec policy SRG2_IPSEC_POL503 proposals SRG2_IPSEC_PROP set groups vpn_config security ipsec vpn SRG1_IPSEC_VPN1 bind-interface st0.1 set groups vpn_config security ipsec vpn SRG1_IPSEC_VPN1 ike gateway SRG1_IKE_GW1 set groups vpn_config security ipsec vpn SRG1_IPSEC_VPN1 ike ipsec-policy SRG1_IPSEC_POL1 set groups vpn_config security ipsec vpn SRG1_IPSEC_VPN1 traffic-selector ts1 local-ip 10.1.0.2/32 set groups vpn_config security ipsec vpn SRG1_IPSEC_VPN1 traffic-selector ts1 remote-ip 10.7.0.2/32 set groups vpn_config security ipsec vpn SRG1_IPSEC_VPN1 establish-tunnels on-traffic set groups vpn_config security ipsec vpn SRG2_IPSEC_VPN500 bind-interface st0.500 set groups vpn_config security ipsec vpn SRG2_IPSEC_VPN500 ike gateway SRG2_IKE_GW500 set groups vpn_config security ipsec vpn SRG2_IPSEC_VPN500 ike ipsec-policy SRG2_IPSEC_POL500 set groups vpn_config security ipsec vpn SRG2_IPSEC_VPN500 traffic-selector ts500 local-ip 10.8.0.2/32 set groups vpn_config security ipsec vpn SRG2_IPSEC_VPN500 traffic-selector ts500 remote-ip 10.9.0.2/32 set groups vpn_config security ipsec vpn SRG2_IPSEC_VPN500 establish-tunnels on-traffic set groups vpn_config security zones security-zone vpn host-inbound-traffic system-services ike set groups vpn_config security zones security-zone vpn host-inbound-traffic protocols all set groups vpn_config security zones security-zone vpn interfaces st0.1 set groups vpn_config security zones security-zone vpn interfaces st0.500 set groups vpn_config interfaces st0 unit 1 family inet set groups vpn_config interfaces st0 unit 1 family inet6 set groups vpn_config interfaces st0 unit 500 family inet set groups vpn_config interfaces st0 unit 500 family inet6 set apply-groups vpn_config set chassis high-availability local-id 1 set chassis high-availability local-id local-ip 10.22.0.2 set chassis high-availability peer-id 2 peer-ip 10.22.0.1 set chassis high-availability peer-id 2 interface ge-0/0/2.0 set chassis high-availability peer-id 2 vpn-profile ICL_IPSEC_VPN set chassis high-availability peer-id 2 liveness-detection minimum-interval 200 set chassis high-availability peer-id 2 liveness-detection multiplier 3 set chassis high-availability services-redundancy-group 1 deployment-type routing set chassis high-availability services-redundancy-group 1 peer-id 2 set chassis high-availability services-redundancy-group 1 activeness-probe dest-ip 10.111.0.1 set chassis high-availability services-redundancy-group 1 activeness-probe dest-ip src-ip 10.11.0.1 set chassis high-availability services-redundancy-group 1 monitor bfd-liveliness 10.5.0.2 src-ip 10.5.0.1 set chassis high-availability services-redundancy-group 1 monitor bfd-liveliness 10.5.0.2 session-type singlehop set chassis high-availability services-redundancy-group 1 monitor bfd-liveliness 10.5.0.2 interface ge-0/0/3.0 set chassis high-availability services-redundancy-group 1 monitor interface ge-0/0/3 set chassis high-availability services-redundancy-group 1 monitor interface ge-0/0/4 set chassis high-availability services-redundancy-group 1 active-signal-route 10.39.1.1 set chassis high-availability services-redundancy-group 1 backup-signal-route 10.39.1.2 set chassis high-availability services-redundancy-group 1 prefix-list SRG1_PFX set chassis high-availability services-redundancy-group 1 managed-services ipsec set chassis high-availability services-redundancy-group 1 preemption set chassis high-availability services-redundancy-group 1 activeness-priority 1 set chassis high-availability services-redundancy-group 2 peer-id 2 set chassis high-availability services-redundancy-group 2 activeness-probe dest-ip 10.111.0.1 set chassis high-availability services-redundancy-group 2 activeness-probe dest-ip src-ip 10.12.0.1 set chassis high-availability services-redundancy-group 2 monitor bfd-liveliness 10.5.0.2 src-ip 10.5.0.1 set chassis high-availability services-redundancy-group 2 monitor bfd-liveliness 10.5.0.2 session-type singlehop set chassis high-availability services-redundancy-group 2 monitor bfd-liveliness 10.5.0.2 interface ge-0/0/3.0 set chassis high-availability services-redundancy-group 2 monitor interface ge-0/0/3 set chassis high-availability services-redundancy-group 2 monitor interface ge-0/0/4 set chassis high-availability services-redundancy-group 2 active-signal-route 10.49.1.1 set chassis high-availability services-redundancy-group 2 backup-signal-route 10.49.1.2 set chassis high-availability services-redundancy-group 2 prefix-list SRG2_PFX set chassis high-availability services-redundancy-group 2 managed-services ipsec set chassis high-availability services-redundancy-group 2 preemption set chassis high-availability services-redundancy-group 2 activeness-priority 200 set security ike proposal ICL_IKE_PROP description interchassis_link_encr_tunnel set security ike proposal ICL_IKE_PROP authentication-method pre-shared-keys set security ike proposal ICL_IKE_PROP dh-group group14 set security ike proposal ICL_IKE_PROP authentication-algorithm sha-256 set security ike proposal ICL_IKE_PROP encryption-algorithm aes-256-cbc set security ike proposal ICL_IKE_PROP lifetime-seconds 300 set security ike policy ICL_IKE_POL description interchassis_link_encr_tunnel set security ike policy ICL_IKE_POL proposals ICL_IKE_PROP set security ike policy ICL_IKE_POL pre-shared-key ascii-text "$ABC123" set security ike gateway ICL_IKE_GW ike-policy ICL_IKE_POL set security ike gateway ICL_IKE_GW version v2-only set security ipsec proposal ICL_IPSEC_PROP description interchassis_link_encr_tunnel set security ipsec proposal ICL_IPSEC_PROP protocol esp set security ipsec proposal ICL_IPSEC_PROP encryption-algorithm aes-256-gcm set security ipsec proposal ICL_IPSEC_PROP lifetime-seconds 300 set security ipsec policy ICL_IPSEC_POL description interchassis_link_encr_tunnel set security ipsec policy ICL_IPSEC_POL proposals ICL_IPSEC_PROP set security ipsec vpn ICL_IPSEC_VPN ha-link-encryption set security ipsec vpn ICL_IPSEC_VPN ike gateway ICL_IKE_GW set security ipsec vpn ICL_IPSEC_VPN ike ipsec-policy ICL_IPSEC_POL set security policies default-policy permit-all set security zones security-zone vpn host-inbound-traffic system-services ike set security zones security-zone vpn host-inbound-traffic protocols all set security zones security-zone vpn interfaces st0.1 set security zones security-zone untrust host-inbound-traffic system-services ike set security zones security-zone untrust host-inbound-traffic system-services ping set security zones security-zone untrust host-inbound-traffic protocols bfd set security zones security-zone untrust host-inbound-traffic protocols bgp set security zones security-zone untrust interfaces lo0.0 set security zones security-zone untrust interfaces ge-0/0/3.0 set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces ge-0/0/4.0 set security zones security-zone icl_zone host-inbound-traffic system-services ike set security zones security-zone icl_zone host-inbound-traffic system-services ping set security zones security-zone icl_zone host-inbound-traffic system-services high-availability set security zones security-zone icl_zone host-inbound-traffic system-services ssh set security zones security-zone icl_zone host-inbound-traffic protocols bfd set security zones security-zone icl_zone host-inbound-traffic protocols bgp set security zones security-zone icl_zone interfaces ge-0/0/2.0 set interfaces ge-0/0/1 unit 0 family inet set interfaces ge-0/0/2 description inter_chassis_link set interfaces ge-0/0/2 unit 0 family inet address 10.22.0.2/24 set interfaces ge-0/0/3 description untrust set interfaces ge-0/0/3 unit 0 family inet address 10.3.0.2/24 set interfaces ge-0/0/4 description trust set interfaces ge-0/0/4 unit 0 family inet address 10.5.0.1/24 set interfaces lo0 apply-groups-except global set interfaces lo0 description untrust set interfaces lo0 unit 0 family inet address 10.11.0.1/32 set interfaces lo0 unit 0 family inet address 10.12.0.1/32 set interfaces st0 unit 1 set policy-options prefix-list SRG1_PFX 10.11.0.0/24 set policy-options prefix-list SRG2_PFX 10.12.0.0/24 set policy-options route-filter-list srg1_rf_list 10.11.0.0/24 orlonger set policy-options route-filter-list srg1_rf_list 10.7.0.0/16 orlonger set policy-options route-filter-list srg1_rf_list 10.1.0.0/16 orlonger set policy-options route-filter-list srg2_rf_list 10.12.0.0/24 orlonger set policy-options route-filter-list srg2_rf_list 10.9.0.0/16 orlonger set policy-options route-filter-list srg2_rf_list 10.8.0.0/16 orlonger set policy-options policy-statement mnha-route-policy term 1 from route-filter-list srg1_rf_list set policy-options policy-statement mnha-route-policy term 1 from condition active_route_exists_srg1 set policy-options policy-statement mnha-route-policy term 1 then metric 10 set policy-options policy-statement mnha-route-policy term 1 then accept set policy-options policy-statement mnha-route-policy term 2 from route-filter-list srg1_rf_list set policy-options policy-statement mnha-route-policy term 2 from condition backup_route_exists_srg1 set policy-options policy-statement mnha-route-policy term 2 then metric 20 set policy-options policy-statement mnha-route-policy term 2 then accept set policy-options policy-statement mnha-route-policy term 3 from route-filter-list srg2_rf_list set policy-options policy-statement mnha-route-policy term 3 from condition active_route_exists_srg2 set policy-options policy-statement mnha-route-policy term 3 then metric 10 set policy-options policy-statement mnha-route-policy term 3 then accept set policy-options policy-statement mnha-route-policy term 4 from route-filter-list srg2_rf_list set policy-options policy-statement mnha-route-policy term 4 from condition backup_route_exists_srg2 set policy-options policy-statement mnha-route-policy term 4 then metric 20 set policy-options policy-statement mnha-route-policy term 4 then accept set policy-options policy-statement mnha-route-policy term default then reject set policy-options condition active_route_exists_srg1 if-route-exists address-family inet 10.39.1.1/32 set policy-options condition active_route_exists_srg1 if-route-exists address-family inet table inet.0 set policy-options condition active_route_exists_srg2 if-route-exists address-family inet 10.49.1.1/32 set policy-options condition active_route_exists_srg2 if-route-exists address-family inet table inet.0 set policy-options condition backup_route_exists_srg1 if-route-exists address-family inet 10.39.1.2/32 set policy-options condition backup_route_exists_srg1 if-route-exists address-family inet table inet.0 set policy-options condition backup_route_exists_srg2 if-route-exists address-family inet 10.49.1.2/32 set policy-options condition backup_route_exists_srg2 if-route-exists address-family inet table inet.0 set protocols bgp group trust type internal set protocols bgp group trust local-address 10.3.0.2 set protocols bgp group trust export mnha-route-policy set protocols bgp group trust local-as 100 set protocols bgp group trust bfd-liveness-detection minimum-interval 500 set protocols bgp group trust bfd-liveness-detection minimum-receive-interval 500 set protocols bgp group trust bfd-liveness-detection multiplier 3 set protocols bgp group trust neighbor 10.3.0.1 set protocols bgp group untrust type internal set protocols bgp group untrust local-address 10.5.0.1 set protocols bgp group untrust export mnha-route-policy set protocols bgp group untrust local-as 100 set protocols bgp group untrust bfd-liveness-detection minimum-interval 500 set protocols bgp group untrust bfd-liveness-detection minimum-receive-interval 500 set protocols bgp group untrust bfd-liveness-detection multiplier 3 set protocols bgp group untrust neighbor 10.5.0.2 set routing-options autonomous-system 100 set routing-options static route 10.7.0.0/16 next-hop 10.5.0.2 set routing-options static route 10.112.0.0/24 next-hop 10.5.0.2
SRX-02-Gerät
set groups vpn_config when peers SRX-01 set groups vpn_config when peers SRX-02 set groups vpn_config security ike proposal SRG1_IKE_PROP authentication-method pre-shared-keys set groups vpn_config security ike proposal SRG1_IKE_PROP dh-group group14 set groups vpn_config security ike proposal SRG1_IKE_PROP authentication-algorithm sha-256 set groups vpn_config security ike proposal SRG1_IKE_PROP encryption-algorithm aes-256-cbc set groups vpn_config security ike proposal SRG1_IKE_PROP lifetime-seconds 3600 set groups vpn_config security ike proposal SRG2_IKE_PROP authentication-method pre-shared-keys set groups vpn_config security ike proposal SRG2_IKE_PROP dh-group group14 set groups vpn_config security ike proposal SRG2_IKE_PROP authentication-algorithm sha-256 set groups vpn_config security ike proposal SRG2_IKE_PROP encryption-algorithm aes-256-cbc set groups vpn_config security ike proposal SRG2_IKE_PROP lifetime-seconds 3600 set groups vpn_config security ike policy SRG1_IKE_POL1 proposals SRG1_IKE_PROP set groups vpn_config security ike policy SRG1_IKE_POL1 pre-shared-key ascii-text "$ABC123" set groups vpn_config security ike policy SRG2_IKE_POL500 proposals SRG2_IKE_PROP set groups vpn_config security ike policy SRG2_IKE_POL500 pre-shared-key ascii-text "$ABC123" set groups vpn_config security ike gateway SRG1_IKE_GW1 ike-policy SRG1_IKE_POL1 set groups vpn_config security ike gateway SRG1_IKE_GW1 address 10.112.0.1 set groups vpn_config security ike gateway SRG1_IKE_GW1 external-interface lo0 set groups vpn_config security ike gateway SRG1_IKE_GW1 local-address 10.11.0.1 set groups vpn_config security ike gateway SRG1_IKE_GW1 version v2-only set groups vpn_config security ike gateway SRG2_IKE_GW500 ike-policy SRG2_IKE_POL500 set groups vpn_config security ike gateway SRG2_IKE_GW500 address 10.112.0.5 set groups vpn_config security ike gateway SRG2_IKE_GW500 external-interface lo0 set groups vpn_config security ike gateway SRG2_IKE_GW500 local-address 10.12.0.1 set groups vpn_config security ike gateway SRG2_IKE_GW500 version v2-only set groups vpn_config security ipsec proposal SRG1_IPSEC_PROP protocol esp set groups vpn_config security ipsec proposal SRG1_IPSEC_PROP authentication-algorithm hmac-sha-256-128 set groups vpn_config security ipsec proposal SRG1_IPSEC_PROP encryption-algorithm aes-256-cbc set groups vpn_config security ipsec proposal SRG1_IPSEC_PROP lifetime-seconds 1800 set groups vpn_config security ipsec proposal SRG2_IPSEC_PROP protocol esp set groups vpn_config security ipsec proposal SRG2_IPSEC_PROP authentication-algorithm hmac-sha-256-128 set groups vpn_config security ipsec proposal SRG2_IPSEC_PROP encryption-algorithm aes-256-cbc set groups vpn_config security ipsec proposal SRG2_IPSEC_PROP lifetime-seconds 1800 set groups vpn_config security ipsec policy SRG1_IPSEC_POL1 proposals SRG1_IPSEC_PROP set groups vpn_config security ipsec policy SRG2_IPSEC_POL501 proposals SRG2_IPSEC_PROP set groups vpn_config security ipsec policy SRG2_IPSEC_POL500 proposals SRG2_IPSEC_PROP set groups vpn_config security ipsec policy SRG2_IPSEC_POL502 proposals SRG2_IPSEC_PROP set groups vpn_config security ipsec policy SRG2_IPSEC_POL503 proposals SRG2_IPSEC_PROP set groups vpn_config security ipsec vpn SRG1_IPSEC_VPN1 bind-interface st0.1 set groups vpn_config security ipsec vpn SRG1_IPSEC_VPN1 ike gateway SRG1_IKE_GW1 set groups vpn_config security ipsec vpn SRG1_IPSEC_VPN1 ike ipsec-policy SRG1_IPSEC_POL1 set groups vpn_config security ipsec vpn SRG1_IPSEC_VPN1 traffic-selector ts1 local-ip 10.1.0.2/32 set groups vpn_config security ipsec vpn SRG1_IPSEC_VPN1 traffic-selector ts1 remote-ip 10.7.0.2/32 set groups vpn_config security ipsec vpn SRG1_IPSEC_VPN1 establish-tunnels on-traffic set groups vpn_config security ipsec vpn SRG2_IPSEC_VPN500 bind-interface st0.500 set groups vpn_config security ipsec vpn SRG2_IPSEC_VPN500 ike gateway SRG2_IKE_GW500 set groups vpn_config security ipsec vpn SRG2_IPSEC_VPN500 ike ipsec-policy SRG2_IPSEC_POL500 set groups vpn_config security ipsec vpn SRG2_IPSEC_VPN500 traffic-selector ts500 local-ip 10.8.0.2/32 set groups vpn_config security ipsec vpn SRG2_IPSEC_VPN500 traffic-selector ts500 remote-ip 10.9.0.2/32 set groups vpn_config security ipsec vpn SRG2_IPSEC_VPN500 establish-tunnels on-traffic set groups vpn_config security zones security-zone vpn host-inbound-traffic system-services ike set groups vpn_config security zones security-zone vpn host-inbound-traffic protocols all set groups vpn_config security zones security-zone vpn interfaces st0.1 set groups vpn_config security zones security-zone vpn interfaces st0.500 set groups vpn_config interfaces st0 unit 1 family inet set groups vpn_config interfaces st0 unit 1 family inet6 set groups vpn_config interfaces st0 unit 500 family inet set groups vpn_config interfaces st0 unit 500 family inet6 set apply-groups vpn_config set chassis high-availability local-id 2 set chassis high-availability local-id local-ip 10.22.0.1 set chassis high-availability peer-id 1 peer-ip 10.22.0.2 set chassis high-availability peer-id 1 interface ge-0/0/2.0 set chassis high-availability peer-id 1 vpn-profile ICL_IPSEC_VPN set chassis high-availability peer-id 1 liveness-detection minimum-interval 200 set chassis high-availability peer-id 1 liveness-detection multiplier 3 set chassis high-availability services-redundancy-group 1 deployment-type routing set chassis high-availability services-redundancy-group 1 peer-id 1 set chassis high-availability services-redundancy-group 1 activeness-probe dest-ip 10.111.0.1 set chassis high-availability services-redundancy-group 1 activeness-probe dest-ip src-ip 10.11.0.1 set chassis high-availability services-redundancy-group 1 monitor bfd-liveliness 10.4.0.2 src-ip 10.4.0.1 set chassis high-availability services-redundancy-group 1 monitor bfd-liveliness 10.4.0.2 session-type singlehop set chassis high-availability services-redundancy-group 1 monitor bfd-liveliness 10.4.0.2 interface ge-0/0/3.0 set chassis high-availability services-redundancy-group 1 monitor interface ge-0/0/3 set chassis high-availability services-redundancy-group 1 monitor interface ge-0/0/4 set chassis high-availability services-redundancy-group 1 active-signal-route 10.39.1.1 set chassis high-availability services-redundancy-group 1 backup-signal-route 10.39.1.2 set chassis high-availability services-redundancy-group 1 prefix-list SRG1_PFX set chassis high-availability services-redundancy-group 1 managed-services ipsec set chassis high-availability services-redundancy-group 1 preemption set chassis high-availability services-redundancy-group 1 activeness-priority 200 set chassis high-availability services-redundancy-group 2 peer-id 1 set chassis high-availability services-redundancy-group 2 activeness-probe dest-ip 10.111.0.1 set chassis high-availability services-redundancy-group 2 activeness-probe dest-ip src-ip 10.12.0.1 set chassis high-availability services-redundancy-group 2 monitor bfd-liveliness 10.4.0.2 src-ip 10.4.0.1 set chassis high-availability services-redundancy-group 2 monitor bfd-liveliness 10.4.0.2 session-type singlehop set chassis high-availability services-redundancy-group 2 monitor bfd-liveliness 10.4.0.2 interface ge-0/0/3.0 set chassis high-availability services-redundancy-group 2 monitor interface ge-0/0/3 set chassis high-availability services-redundancy-group 2 monitor interface ge-0/0/4 set chassis high-availability services-redundancy-group 2 active-signal-route 10.49.1.1 set chassis high-availability services-redundancy-group 2 backup-signal-route 10.49.1.2 set chassis high-availability services-redundancy-group 2 prefix-list SRG2_PFX set chassis high-availability services-redundancy-group 2 managed-services ipsec set chassis high-availability services-redundancy-group 2 preemption set chassis high-availability services-redundancy-group 2 activeness-priority 1 set security ike proposal ICL_IKE_PROP description interchassisa_link_encr_tunnel set security ike proposal ICL_IKE_PROP authentication-method pre-shared-keys set security ike proposal ICL_IKE_PROP dh-group group14 set security ike proposal ICL_IKE_PROP authentication-algorithm sha-256 set security ike proposal ICL_IKE_PROP encryption-algorithm aes-256-cbc set security ike proposal ICL_IKE_PROP lifetime-seconds 300 set security ike policy ICL_IKE_POL description interchassis_link_encr_tunnel set security ike policy ICL_IKE_POL proposals ICL_IKE_PROP set security ike policy ICL_IKE_POL pre-shared-key ascii-text "$ABC123" set security ike gateway ICL_IKE_GW ike-policy ICL_IKE_POL set security ike gateway ICL_IKE_GW version v2-only set security ipsec proposal ICL_IPSEC_PROP description interchassis_link_encr_tunnel set security ipsec proposal ICL_IPSEC_PROP protocol esp set security ipsec proposal ICL_IPSEC_PROP encryption-algorithm aes-256-gcm set security ipsec proposal ICL_IPSEC_PROP lifetime-seconds 300 set security ipsec policy ICL_IPSEC_POL description interchassis_link_encr_tunnel set security ipsec policy ICL_IPSEC_POL proposals ICL_IPSEC_PROP set security ipsec vpn ICL_IPSEC_VPN ha-link-encryption set security ipsec vpn ICL_IPSEC_VPN ike gateway ICL_IKE_GW set security ipsec vpn ICL_IPSEC_VPN ike ipsec-policy ICL_IPSEC_POL set security policies default-policy permit-all set security zones security-zone untrust host-inbound-traffic system-services ike set security zones security-zone untrust host-inbound-traffic system-services ping set security zones security-zone untrust host-inbound-traffic protocols bfd set security zones security-zone untrust host-inbound-traffic protocols bgp set security zones security-zone untrust interfaces lo0.0 set security zones security-zone untrust interfaces ge-0/0/3.0 set security zones security-zone vpn host-inbound-traffic system-services ike set security zones security-zone vpn host-inbound-traffic protocols all set security zones security-zone vpn interfaces st0.1 set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces ge-0/0/4.0 set security zones security-zone icl_zone host-inbound-traffic system-services ike set security zones security-zone icl_zone host-inbound-traffic system-services ping set security zones security-zone icl_zone host-inbound-traffic system-services high-availability set security zones security-zone icl_zone host-inbound-traffic system-services ssh set security zones security-zone icl_zone host-inbound-traffic protocols bfd set security zones security-zone icl_zone host-inbound-traffic protocols bgp set security zones security-zone icl_zone interfaces ge-0/0/2.0 set interfaces ge-0/0/1 unit 0 family inet set interfaces ge-0/0/2 description inter_chassis_link set interfaces ge-0/0/2 unit 0 family inet address 10.22.0.1/24 set interfaces ge-0/0/3 description untrust set interfaces ge-0/0/3 unit 0 family inet address 10.2.0.2/24 set interfaces ge-0/0/4 description trust set interfaces ge-0/0/4 unit 0 family inet address 10.4.0.1/24 set interfaces lo0 apply-groups-except global set interfaces lo0 description untrust set interfaces lo0 unit 0 family inet address 10.11.0.1/32 set interfaces lo0 unit 0 family inet address 10.12.0.1/32 set interfaces st0 unit 1 family inet set interfaces st0 unit 1 family inet6 set policy-options prefix-list SRG1_PFX 10.11.0.0/24 set policy-options prefix-list SRG2_PFX 10.12.0.0/24 set policy-options route-filter-list srg1_rf_list 10.11.0.0/24 orlonger set policy-options route-filter-list srg1_rf_list 10.7.0.0/24 orlonger set policy-options route-filter-list srg1_rf_list 10.1.0.0/24 orlonger set policy-options route-filter-list srg2_rf_list 10.12.0.0/24 orlonger set policy-options route-filter-list srg2_rf_list 10.9.0.0/24 orlonger set policy-options route-filter-list srg2_rf_list 10.8.0.0/24 orlonger set policy-options policy-statement mnha-route-policy term 1 from route-filter-list srg1_rf_list set policy-options policy-statement mnha-route-policy term 1 from condition active_route_exists_srg1 set policy-options policy-statement mnha-route-policy term 1 then metric 10 set policy-options policy-statement mnha-route-policy term 1 then accept set policy-options policy-statement mnha-route-policy term 2 from route-filter-list srg1_rf_list set policy-options policy-statement mnha-route-policy term 2 from condition backup_route_exists_srg1 set policy-options policy-statement mnha-route-policy term 2 then metric 20 set policy-options policy-statement mnha-route-policy term 2 then accept set policy-options policy-statement mnha-route-policy term 3 from route-filter-list srg2_rf_list set policy-options policy-statement mnha-route-policy term 3 from condition active_route_exists_srg2 set policy-options policy-statement mnha-route-policy term 3 then metric 10 set policy-options policy-statement mnha-route-policy term 3 then accept set policy-options policy-statement mnha-route-policy term 4 from route-filter-list srg2_rf_list set policy-options policy-statement mnha-route-policy term 4 from condition backup_route_exists_srg2 set policy-options policy-statement mnha-route-policy term 4 then metric 20 set policy-options policy-statement mnha-route-policy term 4 then accept set policy-options policy-statement mnha-route-policy term default then reject set policy-options condition active_route_exists_srg1 if-route-exists address-family inet 10.39.1.1/32 set policy-options condition active_route_exists_srg1 if-route-exists address-family inet table inet.0 set policy-options condition active_route_exists_srg2 if-route-exists address-family inet 10.49.1.1/32 set policy-options condition active_route_exists_srg2 if-route-exists address-family inet table inet.0 set policy-options condition backup_route_exists_srg1 if-route-exists address-family inet 10.39.1.2/32 set policy-options condition backup_route_exists_srg1 if-route-exists address-family inet table inet.0 set policy-options condition backup_route_exists_srg2 if-route-exists address-family inet 10.49.1.2/32 set policy-options condition backup_route_exists_srg2 if-route-exists address-family inet table inet.0 set protocols bgp group trust type internal set protocols bgp group trust local-address 10.2.0.2 set protocols bgp group trust export mnha-route-policy set protocols bgp group trust local-as 100 set protocols bgp group trust bfd-liveness-detection minimum-interval 500 set protocols bgp group trust bfd-liveness-detection minimum-receive-interval 500 set protocols bgp group trust bfd-liveness-detection multiplier 3 set protocols bgp group trust neighbor 10.2.0.1 set protocols bgp group untrust type internal set protocols bgp group untrust local-address 10.4.0.1 set protocols bgp group untrust export mnha-route-policy set protocols bgp group untrust local-as 100 set protocols bgp group untrust bfd-liveness-detection minimum-interval 500 set protocols bgp group untrust bfd-liveness-detection minimum-receive-interval 500 set protocols bgp group untrust bfd-liveness-detection multiplier 3 set protocols bgp group untrust neighbor 10.4.0.2 set routing-options autonomous-system 100 set routing-options static route 10.7.0.0/24 next-hop 10.4.0.2 set routing-options static route 10.112.0.0/24 next-hop 10.4.0.2
SRX-3-Gerät
set security ike proposal SRG1_IKE_PROP authentication-method pre-shared-keys set security ike proposal SRG1_IKE_PROP dh-group group14 set security ike proposal SRG1_IKE_PROP authentication-algorithm sha-256 set security ike proposal SRG1_IKE_PROP encryption-algorithm aes-256-cbc set security ike proposal SRG1_IKE_PROP lifetime-seconds 3600 set security ike proposal SRG2_IKE_PROP authentication-method pre-shared-keys set security ike proposal SRG2_IKE_PROP dh-group group14 set security ike proposal SRG2_IKE_PROP authentication-algorithm sha-256 set security ike proposal SRG2_IKE_PROP encryption-algorithm aes-256-cbc set security ike proposal SRG2_IKE_PROP lifetime-seconds 3600 set security ike policy SRG1_IKE_POL1 proposals SRG1_IKE_PROP set security ike policy SRG1_IKE_POL1 pre-shared-key ascii-text "$ABC123" set security ike policy SRG2_IKE_POL500 proposals SRG2_IKE_PROP set security ike policy SRG2_IKE_POL500 pre-shared-key ascii-text "$ABC123" set security ike gateway SRG1_IKE_GW1 ike-policy SRG1_IKE_POL1 set security ike gateway SRG1_IKE_GW1 address 10.11.0.1 set security ike gateway SRG1_IKE_GW1 external-interface lo0 set security ike gateway SRG1_IKE_GW1 local-address 10.112.0.1 set security ike gateway SRG1_IKE_GW1 version v2-only set security ike gateway SRG2_IKE_GW500 ike-policy SRG2_IKE_POL500 set security ike gateway SRG2_IKE_GW500 address 10.12.0.1 set security ike gateway SRG2_IKE_GW500 external-interface lo0 set security ike gateway SRG2_IKE_GW500 local-address 10.112.0.5 set security ike gateway SRG2_IKE_GW500 version v2-only set security ipsec proposal SRG1_IPSEC_PROP protocol esp set security ipsec proposal SRG1_IPSEC_PROP authentication-algorithm hmac-sha-256-128 set security ipsec proposal SRG1_IPSEC_PROP encryption-algorithm aes-256-cbc set security ipsec proposal SRG1_IPSEC_PROP lifetime-seconds 1800 set security ipsec proposal SRG2_IPSEC_PROP protocol esp set security ipsec proposal SRG2_IPSEC_PROP authentication-algorithm hmac-sha-256-128 set security ipsec proposal SRG2_IPSEC_PROP encryption-algorithm aes-256-cbc set security ipsec proposal SRG2_IPSEC_PROP lifetime-seconds 1800 set security ipsec policy SRG1_IPSEC_POL1 proposals SRG1_IPSEC_PROP set security ipsec policy SRG2_IPSEC_POL500 proposals SRG2_IPSEC_PROP set security ipsec vpn SRG1_IPSEC_VPN1 bind-interface st0.1 set security ipsec vpn SRG1_IPSEC_VPN1 ike gateway SRG1_IKE_GW1 set security ipsec vpn SRG1_IPSEC_VPN1 ike ipsec-policy SRG1_IPSEC_POL1 set security ipsec vpn SRG1_IPSEC_VPN1 traffic-selector ts1 local-ip 10.7.0.2/32 set security ipsec vpn SRG1_IPSEC_VPN1 traffic-selector ts1 remote-ip 10.1.0.2/32 set security ipsec vpn SRG1_IPSEC_VPN1 establish-tunnels immediately set security ipsec vpn SRG2_IPSEC_VPN500 bind-interface st0.500 set security ipsec vpn SRG2_IPSEC_VPN500 ike gateway SRG2_IKE_GW500 set security ipsec vpn SRG2_IPSEC_VPN500 ike ipsec-policy SRG2_IPSEC_POL500 set security ipsec vpn SRG2_IPSEC_VPN500 traffic-selector ts1 local-ip 10.9.0.2/32 set security ipsec vpn SRG2_IPSEC_VPN500 traffic-selector ts1 remote-ip 10.8.0.2/32 set security ipsec vpn SRG2_IPSEC_VPN500 establish-tunnels immediately set security policies default-policy permit-all set security zones security-zone untrust host-inbound-traffic system-services ike set security zones security-zone untrust host-inbound-traffic protocols all set security zones security-zone untrust interfaces st0.1 set security zones security-zone untrust interfaces lo0.0 set security zones security-zone untrust interfaces st0.500 set security zones security-zone untrust interfaces ge-0/0/1.0 set security zones security-zone untrust interfaces ge-0/0/0.0 set security zones security-zone trust host-inbound-traffic system-services ike set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces ge-0/0/2.0 set interfaces ge-0/0/0 description trust set interfaces ge-0/0/0 unit 0 family inet address 10.7.0.1/24 set interfaces ge-0/0/1 description untrust set interfaces ge-0/0/1 unit 0 family inet address 10.6.0.2/24 set interfaces ge-0/0/2 description trust set interfaces ge-0/0/2 unit 0 family inet address 10.9.0.1/24 set interfaces lo0 description untrust set interfaces lo0 unit 0 family inet address 10.112.0.1/32 set interfaces lo0 unit 0 family inet address 10.112.0.5/32 set interfaces st0 unit 1 family inet set interfaces st0 unit 500 family inet set routing-options autonomous-system 100 set routing-options static route 10.4.0.0/24 next-hop 10.7.0.2 set routing-options static route 10.5.0.0/24 next-hop 10.7.0.2 set routing-options static route 10.11.0.0/24 next-hop 10.7.0.2 set routing-options static route 10.12.0.0/24 next-hop 10.7.0.2 set routing-options static route 10.111.0.1/32 next-hop 10.7.0.2 set routing-options static route 10.111.0.2/32 next-hop 10.7.0.2
In den folgenden Abschnitten werden Konfigurationsausschnitte für die Router gezeigt, die für die Einrichtung von Multinode-Hochverfügbarkeit im Netzwerk erforderlich sind.
R1-Router
set interfaces ge-0/0/0 description srx_1 set interfaces ge-0/0/0 unit 0 family inet address 10.3.0.1/24 set interfaces ge-0/0/1 description srx_2 set interfaces ge-0/0/1 unit 0 family inet address 10.2.0.1/24 set interfaces lo0 description loopback set interfaces lo0 unit 0 family inet address 10.111.0.1/32 primary set interfaces lo0 unit 0 family inet address 10.111.0.1/32 preferred set routing-options autonomous-system 100 set protocols bgp group srx2_group type internal set protocols bgp group srx2_group local-address 10.2.0.1 set protocols bgp group srx2_group local-as 100 set protocols bgp group srx2_group bfd-liveness-detection minimum-interval 500 set protocols bgp group srx2_group bfd-liveness-detection minimum-receive-interval 500 set protocols bgp group srx2_group bfd-liveness-detection multiplier 3 set protocols bgp group srx2_group neighbor 10.2.0.2 set protocols bgp group srx1_group type internal set protocols bgp group srx1_group local-address 10.3.0.1 set protocols bgp group srx1_group local-as 100 set protocols bgp group srx1_group bfd-liveness-detection minimum-interval 500 set protocols bgp group srx1_group bfd-liveness-detection minimum-receive-interval 500 set protocols bgp group srx1_group bfd-liveness-detection multiplier 3 set protocols bgp group srx1_group neighbor 10.3.0.2
R2-Router
set interfaces ge-0/0/0 description srx_1 set interfaces ge-0/0/0 unit 0 family inet address 10.5.0.2/24 set interfaces ge-0/0/1 description srx_2 set interfaces ge-0/0/1 unit 0 family inet address 10.4.0.2/24 set interfaces ge-0/0/2 description srx-3 set interfaces ge-0/0/2 unit 0 family inet address 10.7.0.2/24 set interfaces lo0 description loopback set interfaces lo0 unit 0 family inet address 10.111.0.2/32 primary set interfaces lo0 unit 0 family inet address 10.111.0.2/32 preferred set routing-options autonomous-system 100 set routing-options static route 10.112.0.0/24 next-hop 10.7.0.1 set protocols bgp group srx2_group type internal set protocols bgp group srx2_group local-address 10.4.0.2 set protocols bgp group srx2_group local-as 100 set protocols bgp group srx2_group bfd-liveness-detection minimum-interval 500 set protocols bgp group srx2_group bfd-liveness-detection minimum-receive-interval 500 set protocols bgp group srx2_group bfd-liveness-detection multiplier 3 set protocols bgp group srx2_group neighbor 10.4.0.1 set protocols bgp group srx1_group type internal set protocols bgp group srx1_group local-address 10.5.0.2 set protocols bgp group srx1_group local-as 100 set protocols bgp group srx1_group bfd-liveness-detection minimum-interval 500 set protocols bgp group srx1_group bfd-liveness-detection minimum-receive-interval 500 set protocols bgp group srx1_group bfd-liveness-detection multiplier 3 set protocols bgp group srx1_group neighbor 10.5.0.1
Konfiguration
Schritt-für-Schritt-Anleitung
Wir zeigen die Konfiguration von SRX-01 Schritt für Schritt.
Im folgenden Beispiel müssen Sie durch verschiedene Ebenen in der Konfigurationshierarchie navigieren. Anweisungen dazu finden Sie unter Verwenden des CLI-Editors im Konfigurationsmodus im CLI-Benutzerhandbuch.
Schnittstellen konfigurieren.
[edit] user@srx-1# set interfaces ge-0/0/2 description inter_chassis_link user@srx-1# set interfaces ge-0/0/2 unit 0 family inet address 10.22.0.2/24 user@srx-1# set interfaces ge-0/0/3 description untrust user@srx-1# set interfaces ge-0/0/3 unit 0 family inet address 10.3.0.2/24 user@srx-1# set interfaces ge-0/0/4 description trust user@srx-1# set interfaces ge-0/0/4 unit 0 family inet address 10.5.0.1/24
Verwenden Sie die Schnittstellen ge-0/0/3 und ge-0/0/4, um eine Verbindung zu den vor- und nachgelagerten Routern herzustellen, und verwenden Sie die ge-0/0/2-Schnittstelle, um die ICL einzurichten.
Konfigurieren Sie die Loopback-Schnittstellen.
[edit] user@srx-1# set interfaces lo0 apply-groups-except global user@srx-1# set interfaces lo0 description untrust user@srx-1# set interfaces lo0 unit 0 family inet address 10.11.0.1/32 user@srx-1# set interfaces lo0 unit 0 family inet address 10.12.0.1/32 user@srx-1# set interfaces st0 unit 1
Weisen Sie der Loopback-Schnittstelle die IP-Adressen 10.11.0.1 und 10.12.0.1 zu. Wir verwenden 10.11.0.1 als Floating-IP-Adresse und 10.12.0.1 als IKE-Gateway-Adresse.
Konfigurieren Sie Sicherheitszonen, weisen Sie den Zonen Schnittstellen zu und geben Sie die zulässigen Systemdienste für die Sicherheitszonen an.
[edit] user@srx-1# set security zones security-zone vpn host-inbound-traffic system-services ike user@srx-1# set security zones security-zone vpn host-inbound-traffic protocols all user@srx-1# set security zones security-zone vpn interfaces st0.1 user@srx-1# set security zones security-zone untrust host-inbound-traffic system-services ike user@srx-1# set security zones security-zone untrust host-inbound-traffic system-services ping user@srx-1# set security zones security-zone untrust host-inbound-traffic protocols bfd user@srx-1# set security zones security-zone untrust host-inbound-traffic protocols bgp user@srx-1# set security zones security-zone untrust interfaces lo0.0 user@srx-1# set security zones security-zone untrust interfaces ge-0/0/3.0 user@srx-1# set security zones security-zone trust host-inbound-traffic system-services all user@srx-1# set security zones security-zone trust host-inbound-traffic protocols all user@srx-1# set security zones security-zone trust interfaces ge-0/0/4.0 user@srx-1# set security zones security-zone icl_zone host-inbound-traffic system-services ike user@srx-1# set security zones security-zone icl_zone host-inbound-traffic system-services ping user@srx-1# set security zones security-zone icl_zone host-inbound-traffic system-services high-availability user@srx-1# set security zones security-zone icl_zone host-inbound-traffic system-services ssh user@srx-1# set security zones security-zone icl_zone host-inbound-traffic protocols bfd user@srx-1# set security zones security-zone icl_zone host-inbound-traffic protocols bgp user@srx-1# set security zones security-zone icl_zone interfaces ge-0/0/2.0
Weisen Sie den Schnittstellen ge-0/0/3 und ge-0/0/4 die Zonen "vertrauenswürdig" bzw. "nicht vertrauenswürdig" zu. Weisen Sie die lo0.0-Schnittstelle der nicht vertrauenswürdigen Zone zu, um eine Verbindung über das IP-Netzwerk herzustellen. Ordnen Sie die Schnittstelle ge-0/0/2 der ICL-Zone zu. Sie verwenden diese Zone, um die ICL einzurichten. Weisen Sie die sichere Tunnelschnittstelle der VPN-Sicherheitszone zu.
- Konfigurieren Sie sowohl Details zum lokalen als auch zum Peer-Knoten, wie z. B. die Knoten-ID, die lP-Adressen des lokalen Knotens und des Peer-Knotens sowie die Schnittstelle für den Peer-Knoten.
[edit] user@srx-1# set chassis high-availability local-id 1 user@srx-1# set chassis high-availability local-id local-ip 10.22.0.2 user@srx-1# set chassis high-availability peer-id 2 peer-ip 10.22.0.1 user@srx-1# set chassis high-availability peer-id 2 interface ge-0/0/2.0
Sie verwenden die ge-0/0/2-Schnittstelle für die Kommunikation mit dem Peer-Knoten über die ICL.
Fügen Sie das IPsec-VPN-Profil IPSEC_VPN_ICL an den Peer Knoten an.
[edit] user@srx-1# set chassis high-availability peer-id 2 vpn-profile ICL_IPSEC_VPN
Sie benötigen diese Konfiguration, um eine sichere ICL-Verbindung zwischen den Knoten herzustellen.
Konfigurieren Sie BFD-Protokolloptionen (Bidirectional Forwarding Detection) für den Peer-Knoten.
[edit] user@srx-1# set chassis high-availability peer-id 2 liveness-detection minimum-interval 200 user@srx-1# set chassis high-availability peer-id 2 liveness-detection multiplier 3
-
Konfigurieren Sie die Service-Redundanz-Gruppen SRG1 und SRG2.
[edit] user@srx-1# set chassis high-availability services-redundancy-group 1 deployment-type routing user@srx-1# set chassis high-availability services-redundancy-group 1 peer-id 2 user@srx-1# set chassis high-availability services-redundancy-group 2 peer-id 2
Richten Sie die Parameter zur Bestimmung der Aktivität sowohl SRG1 als auch SRG2 ein.
SRG1
[edit] user@srx-1# set chassis high-availability services-redundancy-group 1 activeness-probe dest-ip 10.111.0.1 user@srx-1# set chassis high-availability services-redundancy-group 1 activeness-probe dest-ip src-ip 10.11.0.1
SRG2
[edit] user@srx-1# set chassis high-availability services-redundancy-group 2 activeness-probe dest-ip 10.111.0.1 user@srx-1# set chassis high-availability services-redundancy-group 2 activeness-probe dest-ip src-ip 10.11.0.1
Verwenden Sie die Floating-IP-Adresse als Quell-IP-Adresse (10.11.0.1 für SRG1 und 10.12.0.1 für SRG2) und die IP-Adressen der Upstreamrouter als Ziel-IP-Adresse (10.111.0.1) für die Aktivitätsbestimmungsprobe.
Sie können bis zu 64 IP-Adressen für die IP-Überwachung und die Aktivitätsprüfung konfigurieren. Die insgesamt 64 IP-Adressen sind die Summe der IPv4- und IPv6-Adressen)
Konfigurieren Sie BFD-Überwachungsparameter für SRG1 und SRG2, um Ausfälle im Netzwerk zu erkennen.
SRG1
[edit] user@srx-1# set chassis high-availability services-redundancy-group 1 monitor bfd-liveliness 10.5.0.2 src-ip 10.5.0.1 user@srx-1# set chassis high-availability services-redundancy-group 1 monitor bfd-liveliness 10.5.0.2 session-type singlehop user@srx-1# set chassis high-availability services-redundancy-group 1 monitor bfd-liveliness 10.5.0.2 interface ge-0/0/3.0 user@srx-1# set chassis high-availability services-redundancy-group 1 monitor interface ge-0/0/3 user@srx-1# set chassis high-availability services-redundancy-group 1 monitor interface ge-0/0/4
SRG2
[edit] user@srx-1# set chassis high-availability services-redundancy-group 2 monitor bfd-liveliness 10.5.0.2 src-ip 10.5.0.1 user@srx-1# set chassis high-availability services-redundancy-group 2 monitor bfd-liveliness 10.5.0.2 session-type singlehop user@srx-1# set chassis high-availability services-redundancy-group 2 monitor bfd-liveliness 10.5.0.2 interface ge-0/0/3.0 user@srx-1# set chassis high-availability services-redundancy-group 2 monitor interface ge-0/0/3 user@srx-1# set chassis high-availability services-redundancy-group 2 monitor interface ge-0/0/4
Konfigurieren Sie eine aktive Signalroute, die für die Durchsetzung der Aktivität erforderlich ist.
SRG1
[edit] user@srx-1# set chassis high-availability services-redundancy-group 1 active-signal-route 10.39.1.1 user@srx-1# set chassis high-availability services-redundancy-group 1 backup-signal-route 10.39.1.2 user@srx-1# set chassis high-availability services-redundancy-group 1 preemption user@srx-1# set chassis high-availability services-redundancy-group 1 activeness-priority 1
SRG2
[edit] user@srx-1# set chassis high-availability services-redundancy-group 2 active-signal-route 10.49.1.1 user@srx-1# set chassis high-availability services-redundancy-group 2 backup-signal-route 10.49.1.2 user@srx-1# set chassis high-availability services-redundancy-group 2 preemption user@srx-1# set chassis high-availability services-redundancy-group 2 activeness-priority 200
Hinweis: Sie müssen die aktive Signalroute zusammen mit der route-exists-Richtlinie in der policy-options-Anweisung angeben. Wenn Sie dieactive-signal-routeif-route-existswith-Bedingung konfigurieren, fügt der Hohe Verfügbarkeit Modul diese Route dem Routing-Tabelle hinzu.Erstellen Sie eine IP-Präfixliste, indem Sie die lokale Adresse des IKE-Gateways einschließen, und ordnen Sie die IP-Präfixliste SRG1 und SRG2 zu:
SRG1
[edit] user@srx-1# set policy-options prefix-list SRG1_PFX 10.11.0.0/24 user@srx-1# set chassis high-availability services-redundancy-group 1 prefix-list SRG1_PFX
SRG2
[edit] user@srx-1# set policy-options prefix-list SRG2_PFX 10.12.0.0/24 user@srx-1# set chassis high-availability services-redundancy-group 2 prefix-list SRG2_PFX
Diese Konfiguration verankert einen bestimmten IPsec-VPN-Tunnel an einem bestimmten Sicherheitsgerät.
Aktivieren Sie den IPsec-VPN-Dienst sowohl auf SRG1 als auch auf SRG2.
[edit] user@srx-1# set chassis high-availability services-redundancy-group 1 managed-services ipsec user@srx-1# set chassis high-availability services-redundancy-group 2 managed-services ipsec
Konfigurieren Sie IPSec-VPN-Optionen für die ICL.
Definieren Sie die Internet Key Exchange (IKE)-Konfiguration. Eine IKE-Konfiguration definiert die Algorithmen und Schlüssel, die zum Herstellen einer sicheren Verbindung verwendet werden.
[edit] user@srx-1# set security ike proposal ICL_IKE_PROP description interchassis_link_encr_tunnel user@srx-1# set security ike proposal ICL_IKE_PROP authentication-method pre-shared-keys user@srx-1# set security ike proposal ICL_IKE_PROP dh-group group14 user@srx-1# set security ike proposal ICL_IKE_PROP authentication-algorithm sha-256 user@srx-1# set security ike proposal ICL_IKE_PROP encryption-algorithm aes-256-cbc user@srx-1# set security ike proposal ICL_IKE_PROP lifetime-seconds 300 user@srx-1# set security ike policy ICL_IKE_POL description interchassis_link_encr_tunnel user@srx-1# set security ike policy ICL_IKE_POL proposals ICL_IKE_PROP user@srx-1# set security ike policy ICL_IKE_POL pre-shared-key ascii-text "$ABC123" user@srx-1# set security ike gateway ICL_IKE_GW ike-policy ICL_IKE_POL user@srx-1# set security ike gateway ICL_IKE_GW version v2-only
Für das Multinode-Hochverfügbarkeitsfeature müssen Sie die IKE-Version als
v2-only-
Geben Sie das IPsec-Vorschlagsprotokoll und den Verschlüsselungsalgorithmus an. Geben Sie IPsec-Optionen an, um einen IPsec-Tunnel zwischen zwei teilnehmenden Geräten zu erstellen, um die VPN-Kommunikation zu sichern.
[edit] user@srx-1# set security ipsec proposal ICL_IPSEC_PROP description interchassis_link_encr_tunnel user@srx-1# set security ipsec proposal ICL_IPSEC_PROP protocol esp user@srx-1# set security ipsec proposal ICL_IPSEC_PROP encryption-algorithm aes-256-gcm user@srx-1# set security ipsec proposal ICL_IPSEC_PROP lifetime-seconds 300 user@srx-1# set security ipsec policy ICL_IPSEC_POL description interchassis_link_encr_tunnel user@srx-1# set security ipsec policy ICL_IPSEC_POL proposals ICL_IPSEC_PROP user@srx-1# set security ipsec vpn ICL_IPSEC_VPN ha-link-encryption user@srx-1# set security ipsec vpn ICL_IPSEC_VPN ike gateway ICL_IKE_GW user@srx-1# set security ipsec vpn ICL_IPSEC_VPN ike ipsec-policy ICL_IPSEC_POL
ha-link-encryptionOption wird die ICL verschlüsselt, um den hochverfügbaren Datenverkehr zwischen den Knoten zu sichern.Derselbe VPN-Name ICL_IPSEC_VPN für vpn_profile den in der
set chassis high-availability peer-id <id> vpn-profile vpn_profileKonfiguration angegeben werden muss.
Konfigurieren Sie die Sicherheitsrichtlinie.
[edit] user@srx-1# set security policies default-policy permit-all
In diesem Beispiel haben wir eine Richtlinie so konfiguriert, dass der gesamte Datenverkehr zugelassen wird. Es wird dringend empfohlen, Sicherheitsrichtlinien gemäß Ihren Netzwerkanforderungen zu erstellen, um Datenverkehr zuzulassen, der durch Ihre Organisationsrichtlinie zulässig ist, und allen anderen Datenverkehr abzulehnen. Wir haben die Standardrichtlinie nur in diesem Beispiel für Demozwecke verwendet.
Konfigurieren Sie Routing-Optionen.
[edit] user@srx-1# set routing-options autonomous-system 100 user@srx-1# set routing-options static route 10.7.0.0/16 next-hop 10.5.0.2 user@srx-1# set routing-options static route 10.112.0.0/24 next-hop 10.5.0.2
Konfigurieren Sie Richtlinienoptionen.
[edit] user@srx-1# set policy-options route-filter-list srg1_rf_list 10.11.0.0/24 orlonger user@srx-1# set policy-options route-filter-list srg1_rf_list 10.7.0.0/16 orlonger user@srx-1# set policy-options route-filter-list srg1_rf_list 10.1.0.0/16 orlonger user@srx-1# set policy-options route-filter-list srg2_rf_list 10.12.0.0/24 orlonger user@srx-1# set policy-options route-filter-list srg2_rf_list 10.9.0.0/16 orlonger user@srx-1# set policy-options route-filter-list srg2_rf_list 10.8.0.0/16 orlonger user@srx-1# set policy-options policy-statement mnha-route-policy term 1 from route-filter-list srg1_rf_list user@srx-1# set policy-options policy-statement mnha-route-policy term 1 from condition active_route_exists_srg1 user@srx-1# set policy-options policy-statement mnha-route-policy term 1 then metric 10 user@srx-1# set policy-options policy-statement mnha-route-policy term 1 then accept user@srx-1# set policy-options policy-statement mnha-route-policy term 2 from route-filter-list srg1_rf_list user@srx-1# set policy-options policy-statement mnha-route-policy term 2 from condition backup_route_exists_srg1 user@srx-1# set policy-options policy-statement mnha-route-policy term 2 then metric 20 user@srx-1# set policy-options policy-statement mnha-route-policy term 2 then accept user@srx-1# set policy-options policy-statement mnha-route-policy term 3 from route-filter-list srg2_rf_list user@srx-1# set policy-options policy-statement mnha-route-policy term 3 from condition active_route_exists_srg2 user@srx-1# set policy-options policy-statement mnha-route-policy term 3 then metric 10 user@srx-1# set policy-options policy-statement mnha-route-policy term 3 then accept user@srx-1# set policy-options policy-statement mnha-route-policy term 4 from route-filter-list srg2_rf_list user@srx-1# set policy-options policy-statement mnha-route-policy term 4 from condition backup_route_exists_srg2 user@srx-1# set policy-options policy-statement mnha-route-policy term 4 then metric 20 user@srx-1# set policy-options policy-statement mnha-route-policy term 4 then accept user@srx-1# set policy-options policy-statement mnha-route-policy term default then reject user@srx-1# set policy-options condition active_route_exists_srg1 if-route-exists address-family inet 10.39.1.1/32 user@srx-1# set policy-options condition active_route_exists_srg1 if-route-exists address-family inet table inet.0 user@srx-1# set policy-options condition active_route_exists_srg2 if-route-exists address-family inet 10.49.1.1/32 user@srx-1# set policy-options condition active_route_exists_srg2 if-route-exists address-family inet table inet.0 user@srx-1# set policy-options condition backup_route_exists_srg1 if-route-exists address-family inet 10.39.1.2/32 user@srx-1# set policy-options condition backup_route_exists_srg1 if-route-exists address-family inet table inet.0 user@srx-1# set policy-options condition backup_route_exists_srg2 if-route-exists address-family inet 10.49.1.2/32 user@srx-1# set policy-options condition backup_route_exists_srg2 if-route-exists address-family inet table inet.0
Konfigurieren Sie die aktive Signalroute 10.39.1.1 (SRG1) und 10.49.1.1 (SRG2) mit der Routenübereinstimmungsbedingung (
if-route-exists). Multinode-Hochverfügbarkeit fügt diese Route der Routing-Tabelle hinzu, wenn der Knoten in die aktive Rolle wechselt. Der Knoten beginnt auch, die Route mit höherer Präferenz anzukündigen. Konfigurieren Sie die Backup-Signalroute (10.39.1.2 und 10.49.1.2), um den Backup-Knoten mit mittlerer Priorität anzukündigen. Bei Ausfällen wird die Hochverfügbarkeitsverbindung unterbrochen und der aktuell aktive Knoten gibt seine primäre Rolle wieder auf und entfernt die aktive Signalroute. Jetzt erkennt der Backup-Knoten den Zustand durch seine Sonden und wechselt in die aktive Rolle. Die Routenpräferenz wird getauscht, sodass der gesamte Datenverkehr zum neuen aktiven Knoten geleitet wirdKonfigurieren Sie BFD-Peering-Sitzungsoptionen und geben Sie Live-Erkennungs-Timer an.
[edit] user@srx-1# set protocols bgp group trust type internal user@srx-1# set protocols bgp group trust local-address 10.3.0.2 user@srx-1# set protocols bgp group trust export mnha-route-policy user@srx-1# set protocols bgp group trust local-as 100 user@srx-1# set protocols bgp group trust bfd-liveness-detection minimum-interval 500 user@srx-1# set protocols bgp group trust bfd-liveness-detection minimum-receive-interval 500 user@srx-1# set protocols bgp group trust bfd-liveness-detection multiplier 3 user@srx-1# set protocols bgp group trust neighbor 10.3.0.1 user@srx-1# set protocols bgp group untrust type internal user@srx-1# set protocols bgp group untrust local-address 10.5.0.1 user@srx-1# set protocols bgp group untrust export mnha-route-policy user@srx-1# set protocols bgp group untrust local-as 100 user@srx-1# set protocols bgp group untrust bfd-liveness-detection minimum-interval 500 user@srx-1# set protocols bgp group untrust bfd-liveness-detection minimum-receive-interval 500 user@srx-1# set protocols bgp group untrust bfd-liveness-detection multiplier 3 user@srx-1# set protocols bgp group untrust neighbor 10.5.0.2
IPsec VPN-Konfiguration (SRX-1 und SRX-2)
Führen Sie die folgenden Schritte aus, um eine IPsec-VPN-Verbindung mit der Peer-Firewall der SRX-Serie einzurichten. In diesem Beispiel platzieren Sie alle IPsec-VPN-Konfigurationsanweisungen in einer JUNOS-Konfigurationsgruppe mit dem Namen vpn_config.
- Erstellen Sie oben in der Konfiguration eine Konfigurationsgruppe
vpn_config, und konfigurieren Sie IPsec-VPN-spezifische Details.[edit] set groups vpn_config when peers SRX-01 set groups vpn_config when peers SRX-02 set groups vpn_config security ike proposal SRG1_IKE_PROP authentication-method pre-shared-keys set groups vpn_config security ike proposal SRG1_IKE_PROP dh-group group14 set groups vpn_config security ike proposal SRG1_IKE_PROP authentication-algorithm sha-256 set groups vpn_config security ike proposal SRG1_IKE_PROP encryption-algorithm aes-256-cbc set groups vpn_config security ike proposal SRG1_IKE_PROP lifetime-seconds 3600 set groups vpn_config security ike proposal SRG2_IKE_PROP authentication-method pre-shared-keys set groups vpn_config security ike proposal SRG2_IKE_PROP dh-group group14 set groups vpn_config security ike proposal SRG2_IKE_PROP authentication-algorithm sha-256 set groups vpn_config security ike proposal SRG2_IKE_PROP encryption-algorithm aes-256-cbc set groups vpn_config security ike proposal SRG2_IKE_PROP lifetime-seconds 3600 set groups vpn_config security ike policy SRG1_IKE_POL1 proposals SRG1_IKE_PROP set groups vpn_config security ike policy SRG1_IKE_POL1 pre-shared-key ascii-text "$ABC123" set groups vpn_config security ike policy SRG2_IKE_POL500 proposals SRG2_IKE_PROP set groups vpn_config security ike policy SRG2_IKE_POL500 pre-shared-key ascii-text "$ABC123" set groups vpn_config security ike gateway SRG1_IKE_GW1 ike-policy SRG1_IKE_POL1 set groups vpn_config security ike gateway SRG1_IKE_GW1 address 10.112.0.1 set groups vpn_config security ike gateway SRG1_IKE_GW1 external-interface lo0 set groups vpn_config security ike gateway SRG1_IKE_GW1 local-address 10.11.0.1 set groups vpn_config security ike gateway SRG1_IKE_GW1 version v2-only set groups vpn_config security ike gateway SRG2_IKE_GW500 ike-policy SRG2_IKE_POL500 set groups vpn_config security ike gateway SRG2_IKE_GW500 address 10.112.0.5 set groups vpn_config security ike gateway SRG2_IKE_GW500 external-interface lo0 set groups vpn_config security ike gateway SRG2_IKE_GW500 local-address 10.12.0.1 set groups vpn_config security ike gateway SRG2_IKE_GW500 version v2-only set groups vpn_config security ipsec proposal SRG1_IPSEC_PROP protocol esp set groups vpn_config security ipsec proposal SRG1_IPSEC_PROP authentication-algorithm hmac-sha-256-128 set groups vpn_config security ipsec proposal SRG1_IPSEC_PROP encryption-algorithm aes-256-cbc set groups vpn_config security ipsec proposal SRG1_IPSEC_PROP lifetime-seconds 1800 set groups vpn_config security ipsec proposal SRG2_IPSEC_PROP protocol esp set groups vpn_config security ipsec proposal SRG2_IPSEC_PROP authentication-algorithm hmac-sha-256-128 set groups vpn_config security ipsec proposal SRG2_IPSEC_PROP encryption-algorithm aes-256-cbc set groups vpn_config security ipsec proposal SRG2_IPSEC_PROP lifetime-seconds 1800 set groups vpn_config security ipsec policy SRG1_IPSEC_POL1 proposals SRG1_IPSEC_PROP set groups vpn_config security ipsec policy SRG2_IPSEC_POL501 proposals SRG2_IPSEC_PROP set groups vpn_config security ipsec policy SRG2_IPSEC_POL500 proposals SRG2_IPSEC_PROP set groups vpn_config security ipsec policy SRG2_IPSEC_POL502 proposals SRG2_IPSEC_PROP set groups vpn_config security ipsec policy SRG2_IPSEC_POL503 proposals SRG2_IPSEC_PROP set groups vpn_config security ipsec vpn SRG1_IPSEC_VPN1 bind-interface st0.1 set groups vpn_config security ipsec vpn SRG1_IPSEC_VPN1 ike gateway SRG1_IKE_GW1 set groups vpn_config security ipsec vpn SRG1_IPSEC_VPN1 ike ipsec-policy SRG1_IPSEC_POL1 set groups vpn_config security ipsec vpn SRG1_IPSEC_VPN1 traffic-selector ts1 local-ip 10.1.0.2/32 set groups vpn_config security ipsec vpn SRG1_IPSEC_VPN1 traffic-selector ts1 remote-ip 10.7.0.2/32 set groups vpn_config security ipsec vpn SRG1_IPSEC_VPN1 establish-tunnels on-traffic set groups vpn_config security ipsec vpn SRG2_IPSEC_VPN500 bind-interface st0.500 set groups vpn_config security ipsec vpn SRG2_IPSEC_VPN500 ike gateway SRG2_IKE_GW500 set groups vpn_config security ipsec vpn SRG2_IPSEC_VPN500 ike ipsec-policy SRG2_IPSEC_POL500 set groups vpn_config security ipsec vpn SRG2_IPSEC_VPN500 traffic-selector ts500 local-ip 10.8.0.2/32 set groups vpn_config security ipsec vpn SRG2_IPSEC_VPN500 traffic-selector ts500 remote-ip 10.9.0.2/32 set groups vpn_config security ipsec vpn SRG2_IPSEC_VPN500 establish-tunnels on-traffic set groups vpn_config security zones security-zone vpn host-inbound-traffic system-services ike set groups vpn_config security zones security-zone vpn host-inbound-traffic protocols all set groups vpn_config security zones security-zone vpn interfaces st0.1 set groups vpn_config security zones security-zone vpn interfaces st0.500 set groups vpn_config interfaces st0 unit 1 family inet set groups vpn_config interfaces st0 unit 500 family inet
Fügen Sie die application-groups-Anweisung in die Konfiguration ein, um die Anweisungen von der Konfigurationsgruppe vpn_config zu erben.
[edit] user@srx-1# set apply-groups vpn_config
Konfiguration (SRX-03) (VPN-Peer-Gerät)
Schritt-für-Schritt-Verfahren
Erstellen Sie den IKE-Vorschlag.
[edit] user@srx-3# set security ike proposal SRG1_IKE_PROP authentication-method pre-shared-keys user@srx-3# set security ike proposal SRG1_IKE_PROP dh-group group14 user@srx-3# set security ike proposal SRG1_IKE_PROP authentication-algorithm sha-256 user@srx-3# set security ike proposal SRG1_IKE_PROP encryption-algorithm aes-256-cbc user@srx-3# set security ike proposal SRG1_IKE_PROP lifetime-seconds 3600 user@srx-3# set security ike proposal SRG2_IKE_PROP authentication-method pre-shared-keys user@srx-3# set security ike proposal SRG2_IKE_PROP dh-group group14 user@srx-3# set security ike proposal SRG2_IKE_PROP authentication-algorithm sha-256 user@srx-3# set security ike proposal SRG2_IKE_PROP encryption-algorithm aes-256-cbc user@srx-3# set security ike proposal SRG2_IKE_PROP lifetime-seconds 3600
Definieren Sie IKE-Richtlinien.
[edit] user@srx-3# set security ike policy SRG1_IKE_POL1 proposals SRG1_IKE_PROP user@srx-3# set security ike policy SRG1_IKE_POL1 pre-shared-key ascii-text "$ABC123" user@srx-3# set security ike policy SRG2_IKE_POL500 proposals SRG2_IKE_PROP user@srx-3# set security ike policy SRG2_IKE_POL500 pre-shared-key ascii-text "$ABC123"
Erstellen Sie ein IKE-Gateway, definieren Sie die Adresse, geben Sie externe Schnittstellen und Version an.
[edit] user@srx-3# set security ike gateway SRG1_IKE_GW1 ike-policy SRG1_IKE_POL1 user@srx-3# set security ike gateway SRG1_IKE_GW1 address 10.11.0.1 user@srx-3# set security ike gateway SRG1_IKE_GW1 external-interface lo0 user@srx-3# set security ike gateway SRG1_IKE_GW1 local-address 10.112.0.1 user@srx-3# set security ike gateway SRG1_IKE_GW1 version v2-only user@srx-3# set security ike gateway SRG2_IKE_GW500 ike-policy SRG2_IKE_POL500 user@srx-3# set security ike gateway SRG2_IKE_GW500 address 10.12.0.1 user@srx-3# set security ike gateway SRG2_IKE_GW500 external-interface lo0 user@srx-3# set security ike gateway SRG2_IKE_GW500 local-address 10.112.0.5 user@srx-3# set security ike gateway SRG2_IKE_GW500 version v2-only
Erstellen Sie IPsec-Vorschläge.
[edit] user@srx-3# set security ipsec proposal SRG1_IPSEC_PROP protocol esp user@srx-3# set security ipsec proposal SRG1_IPSEC_PROP authentication-algorithm hmac-sha-256-128 user@srx-3# set security ipsec proposal SRG1_IPSEC_PROP encryption-algorithm aes-256-cbc user@srx-3# set security ipsec proposal SRG1_IPSEC_PROP lifetime-seconds 1800 user@srx-3# set security ipsec proposal SRG2_IPSEC_PROP protocol esp user@srx-3# set security ipsec proposal SRG2_IPSEC_PROP authentication-algorithm hmac-sha-256-128 user@srx-3# set security ipsec proposal SRG2_IPSEC_PROP encryption-algorithm aes-256-cbc user@srx-3# set security ipsec proposal SRG2_IPSEC_PROP lifetime-seconds 1800
Erstellen Sie IPsec-Richtlinien.
[edit] user@srx-3# set security ipsec policy SRG1_IPSEC_POL1 proposals SRG1_IPSEC_PROP user@srx-3# set security ipsec policy SRG2_IPSEC_POL500 proposals SRG2_IPSEC_PROP
Geben Sie die IPsec-Vorschlagsreferenzen an (IKE-Gateway, IPsec-Richtlinie, zu bindende Schnittstelle und Datenverkehrsselektoren).
[edit] user@srx-3# set security ipsec vpn SRG1_IPSEC_VPN1 bind-interface st0.1 user@srx-3# set security ipsec vpn SRG1_IPSEC_VPN1 ike gateway SRG1_IKE_GW1 user@srx-3# set security ipsec vpn SRG1_IPSEC_VPN1 ike ipsec-policy SRG1_IPSEC_POL1 user@srx-3# set security ipsec vpn SRG1_IPSEC_VPN1 traffic-selector ts1 local-ip 10.7.0.2/32 user@srx-3# set security ipsec vpn SRG1_IPSEC_VPN1 traffic-selector ts1 remote-ip 10.1.0.2/32 user@srx-3# set security ipsec vpn SRG1_IPSEC_VPN1 establish-tunnels immediately user@srx-3# set security ipsec vpn SRG2_IPSEC_VPN500 bind-interface st0.500 user@srx-3# set security ipsec vpn SRG2_IPSEC_VPN500 ike gateway SRG2_IKE_GW500 user@srx-3# set security ipsec vpn SRG2_IPSEC_VPN500 ike ipsec-policy SRG2_IPSEC_POL500 user@srx-3# set security ipsec vpn SRG2_IPSEC_VPN500 traffic-selector ts1 local-ip 10.9.0.2/32 user@srx-3# set security ipsec vpn SRG2_IPSEC_VPN500 traffic-selector ts1 remote-ip 10.8.0.2/32 user@srx-3# set security ipsec vpn SRG2_IPSEC_VPN500 establish-tunnels immediately
Erstellen Sie eine Sicherheitsrichtlinie.
[edit] user@srx-3# set security policies default-policy permit-all
In diesem Beispiel haben wir eine Richtlinie so konfiguriert, dass der gesamte Datenverkehr zugelassen wird. Es wird dringend empfohlen, Sicherheitsrichtlinien gemäß Ihren Netzwerkanforderungen zu erstellen, um Datenverkehr zuzulassen, der durch Ihre Organisationsrichtlinie zulässig ist, und allen anderen Datenverkehr abzulehnen. Wir haben die Standardrichtlinie nur in diesem Beispiel für Demozwecke verwendet.
Konfigurieren Sie die Schnittstellen.
[edit] user@srx-3# set interfaces ge-0/0/0 description trust user@srx-3# set interfaces ge-0/0/0 unit 0 family inet address 10.7.0.1/24 user@srx-3# set interfaces ge-0/0/1 description untrust user@srx-3# set interfaces ge-0/0/1 unit 0 family inet address 10.6.0.2/24 user@srx-3# set interfaces ge-0/0/2 description trust user@srx-3# set interfaces ge-0/0/2 unit 0 family inet address 10.9.0.1/24 user@srx-3# set interfaces lo0 description untrust user@srx-3# set interfaces lo0 unit 0 family inet address 10.112.0.1/32 user@srx-3# set interfaces lo0 unit 0 family inet address 10.112.0.5/32 user@srx-3# set interfaces st0 unit 1 family inet user@srx-3# set interfaces st0 unit 500 family inet
Definieren Sie Sicherheitszonen und fügen Sie Schnittstellen hinzu.
[edit] user@srx-3# set security zones security-zone untrust host-inbound-traffic system-services all user@srx-3# set security zones security-zone untrust host-inbound-traffic protocols all user@srx-3# set security zones security-zone untrust interfaces st0.1 user@srx-3# set security zones security-zone untrust interfaces lo0.0 user@srx-3# set security zones security-zone untrust interfaces st0.500 user@srx-3# set security zones security-zone untrust interfaces ge-0/0/1.0 user@srx-3# set security zones security-zone untrust interfaces ge-0/0/0.0 user@srx-3# set security zones security-zone trust host-inbound-traffic system-services all user@srx-3# set security zones security-zone trust host-inbound-traffic protocols all user@srx-3# set security zones security-zone trust interfaces ge-0/0/2.0
Konfigurieren Sie die statischen Routen.
[edit] user@srx-3# set routing-options autonomous-system 100 user@srx-3# set routing-options static route 10.4.0.0/16 next-hop 10.7.0.2 user@srx-3# set routing-options static route 10.5.0.0/16 next-hop 10.7.0.2 user@srx-3# set routing-options static route 10.11.0.0/24 next-hop 10.7.0.2 user@srx-3# set routing-options static route 10.12.0.0/24 next-hop 10.7.0.2 user@srx-3# set routing-options static route 10.111.0.1/32 next-hop 10.7.0.2 user@srx-3# set routing-options static route 10.111.0.2/32 next-hop 10.7.0.2
Ergebnisse (SRX-01)
Bestätigen Sie im Konfigurationsmodus Ihre Konfiguration durch Eingabe der folgenden Befehle.
Wenn die Ausgabe nicht die beabsichtigte Konfiguration anzeigt, wiederholen Sie die Konfigurationsanweisungen in diesem Beispiel, um sie zu korrigieren.
[edit]
user@srx-1# show groups vpn_config
when {
peers [ SRX-01 SRX-02 ];
}
security {
ike {
proposal SRG1_IKE_PROP {
authentication-method pre-shared-keys;
dh-group group14;
authentication-algorithm sha-256;
encryption-algorithm aes-256-cbc;
lifetime-seconds 3600;
}
proposal SRG2_IKE_PROP {
authentication-method pre-shared-keys;
dh-group group14;
authentication-algorithm sha-256;
encryption-algorithm aes-256-cbc;
lifetime-seconds 3600;
}
policy SRG1_IKE_POL1 {
proposals SRG1_IKE_PROP;
pre-shared-key ascii-text "$ABC123"; ## SECRET-DATA
}
policy SRG2_IKE_POL500 {
proposals SRG2_IKE_PROP;
pre-shared-key ascii-text "$ABC123"; ## SECRET-DATA
}
gateway SRG1_IKE_GW1 {
ike-policy SRG1_IKE_POL1;
address 10.112.0.1;
external-interface lo0;
local-address 10.11.0.1;
version v2-only;
}
gateway SRG2_IKE_GW500 {
ike-policy SRG2_IKE_POL500;
address 10.112.0.5;
external-interface lo0;
local-address 10.12.0.1;
version v2-only;
}
}
ipsec {
proposal SRG1_IPSEC_PROP {
protocol esp;
authentication-algorithm hmac-sha-256-128;
encryption-algorithm aes-256-cbc;
lifetime-seconds 1800;
}
proposal SRG2_IPSEC_PROP {
protocol esp;
authentication-algorithm hmac-sha-256-128;
encryption-algorithm aes-256-cbc;
lifetime-seconds 1800;
}
policy SRG1_IPSEC_POL1 {
proposals SRG1_IPSEC_PROP;
}
policy SRG2_IPSEC_POL501 {
proposals SRG2_IPSEC_PROP;
}
policy SRG2_IPSEC_POL500 {
proposals SRG2_IPSEC_PROP;
}
policy SRG2_IPSEC_POL502 {
proposals SRG2_IPSEC_PROP;
}
policy SRG2_IPSEC_POL503 {
proposals SRG2_IPSEC_PROP;
}
vpn SRG1_IPSEC_VPN1 {
bind-interface st0.1;
ike {
gateway SRG1_IKE_GW1;
ipsec-policy SRG1_IPSEC_POL1;
}
traffic-selector ts1 {
local-ip 10.1.0.2/32;
remote-ip 10.7.0.2/32;
}
establish-tunnels on-traffic;
}
vpn SRG2_IPSEC_VPN500 {
bind-interface st0.500;
ike {
gateway SRG2_IKE_GW500;
ipsec-policy SRG2_IPSEC_POL500;
}
traffic-selector ts500 {
local-ip 10.8.0.2/32;
remote-ip 10.9.0.2/32;
}
establish-tunnels on-traffic;
}
}
zones {
security-zone vpn {
host-inbound-traffic {
system-services {
ike;
}
protocols {
all;
}
}
interfaces {
st0.1;
st0.500;
}
}
}
}
interfaces {
st0 {
unit 1 {
family inet;
family inet6;
}
unit 500 {
family inet;
family inet6;
}
}
}
[edit]
user@srx-1# show chassis high-availability
local-id 1 local-ip 10.22.0.2;
peer-id 2 {
peer-ip 10.22.0.1;
interface ge-0/0/2.0;
vpn-profile ICL_IPSEC_VPN;
liveness-detection {
minimum-interval 200;
multiplier 3;
}
}
services-redundancy-group 1 {
deployment-type routing;
peer-id {
2;
}
activeness-probe {
dest-ip {
10.111.0.1;
src-ip 10.11.0.1;
}
}
monitor {
bfd-liveliness 10.5.0.2 {
src-ip 10.5.0.1;
session-type singlehop;
interface ge-0/0/3.0;
}
interface {
ge-0/0/3;
ge-0/0/4;
}
}
active-signal-route {
10.39.1.1;
}
backup-signal-route {
10.39.1.2;
}
prefix-list SRG1_PFX;
managed-services ipsec;
preemption;
activeness-priority 1;
}
services-redundancy-group 2 {
peer-id {
2;
}
activeness-probe {
dest-ip {
10.111.0.1;
src-ip 10.12.0.1;
}
}
monitor {
bfd-liveliness 10.5.0.2 {
src-ip 10.5.0.1;
session-type singlehop;
interface ge-0/0/3.0;
}
interface {
ge-0/0/3;
ge-0/0/4;
}
}
active-signal-route {
10.49.1.1;
}
backup-signal-route {
10.49.1.2;
}
prefix-list SRG2_PFX;
managed-services ipsec;
preemption;
activeness-priority 200;
}
[edit]
user@srx-1# show security ike
proposal ICL_IKE_PROP {
description interchassis_link_encr_tunnel;
authentication-method pre-shared-keys;
dh-group group14;
authentication-algorithm sha-256;
encryption-algorithm aes-256-cbc;
lifetime-seconds 300;
}
policy ICL_IKE_POL {
description interchassis_link_encr_tunnel;
proposals ICL_IKE_PROP;
pre-shared-key ascii-text "$ABC123"; ## SECRET-DATA
}
gateway ICL_IKE_GW {
ike-policy ICL_IKE_POL;
version v2-only;
}
[edit]
user@srx-1# show security ipsec
proposal ICL_IPSEC_PROP {
description interchassis_link_encr_tunnel;
protocol esp;
encryption-algorithm aes-256-gcm;
lifetime-seconds 300;
}
policy ICL_IPSEC_POL {
description interchassis_link_encr_tunnel;
proposals ICL_IPSEC_PROP;
}
vpn ICL_IPSEC_VPN {
ha-link-encryption;
ike {
gateway ICL_IKE_GW;
ipsec-policy ICL_IPSEC_POL;
}
}
[edit]
user@srx-1# show policy-options
prefix-list SRG1_PFX {
10.11.0.0/24;
}
prefix-list SRG2_PFX {
10.12.0.0/24;
}
route-filter-list srg1_rf_list {
10.11.0.0/24 orlonger;
10.7.0.0/16 orlonger;
10.1.0.0/16 orlonger;
}
route-filter-list srg2_rf_list {
10.12.0.0/24 orlonger;
10.9.0.0/16 orlonger;
10.8.0.0/16 orlonger;
}
policy-statement mnha-route-policy {
term 1 {
from {
route-filter-list srg1_rf_list;
condition active_route_exists_srg1;
}
then {
metric 10;
accept;
}
}
term 2 {
from {
route-filter-list srg1_rf_list;
condition backup_route_exists_srg1;
}
then {
metric 20;
accept;
}
}
term 3 {
from {
route-filter-list srg2_rf_list;
condition active_route_exists_srg2;
}
then {
metric 10;
accept;
}
}
term 4 {
from {
route-filter-list srg2_rf_list;
condition backup_route_exists_srg2;
}
then {
metric 20;
accept;
}
}
term default {
then reject;
}
}
condition active_route_exists_srg1 {
if-route-exists {
address-family {
inet {
10.39.1.1/32;
table inet.0;
}
}
}
}
condition active_route_exists_srg2 {
if-route-exists {
address-family {
inet {
10.49.1.1/32;
table inet.0;
}
}
}
}
condition backup_route_exists_srg1 {
if-route-exists {
address-family {
inet {
10.39.1.2/32;
table inet.0;
}
}
}
}
condition backup_route_exists_srg2 {
if-route-exists {
address-family {
inet {
10.49.1.2/32;
table inet.0;
}
}
}
}
[edit]
user@srx-1# show routing-options
autonomous-system 100;
static {
route 10.7.0.0/16 next-hop 10.5.0.2;
route 10.112.0.0/24 next-hop 10.5.0.2;
}
[edit]
user@srx-1# show security zones
security-zone vpn {
host-inbound-traffic {
system-services {
ike;
}
protocols {
all;
}
}
interfaces {
st0.1;
}
}
security-zone untrust {
host-inbound-traffic {
system-services {
ike;
ping;
}
protocols {
bfd;
bgp;
}
}
interfaces {
lo0.0;
ge-0/0/3.0;
}
}
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
ge-0/0/4.0;
}
}
security-zone icl_zone {
host-inbound-traffic {
system-services {
ike;
ping;
high-availability;
ssh;
}
protocols {
bfd;
bgp;
}
}
interfaces {
ge-0/0/2.0;
}
}
[edit]
user@srx-1# show interfaces
ge-0/0/1 {
unit 0 {
family inet;
}
}
ge-0/0/2 {
description inter_chassis_link;
unit 0 {
family inet {
address 10.22.0.2/24;
}
}
}
ge-0/0/3 {
description untrust;
unit 0 {
family inet {
address 10.3.0.2/24;
}
}
}
ge-0/0/4 {
description trust;
unit 0 {
family inet {
address 10.5.0.1/24;
}
}
}
lo0 {
apply-groups-except global;
description untrust;
unit 0 {
family inet {
address 10.11.0.1/32;
address 10.12.0.1/32;
}
}
}
st0 {
unit 1;
}
Wenn Sie mit der Konfiguration des Geräts fertig sind, rufen Sie den Konfigurationsmodus auf commit .
Ergebnisse (SRX-02)
Bestätigen Sie im Konfigurationsmodus Ihre Konfiguration durch Eingabe der folgenden Befehle. Wenn die Ausgabe nicht die beabsichtigte Konfiguration anzeigt, wiederholen Sie die Konfigurationsanweisungen in diesem Beispiel, um sie zu korrigieren.
[edit]
user@srx-2# show groups vpn_config
when {
peers [ SRX-01 SRX-02 ];
}
security {
ike {
proposal SRG1_IKE_PROP {
authentication-method pre-shared-keys;
dh-group group14;
authentication-algorithm sha-256;
encryption-algorithm aes-256-cbc;
lifetime-seconds 3600;
}
proposal SRG2_IKE_PROP {
authentication-method pre-shared-keys;
dh-group group14;
authentication-algorithm sha-256;
encryption-algorithm aes-256-cbc;
lifetime-seconds 3600;
}
policy SRG1_IKE_POL1 {
proposals SRG1_IKE_PROP;
pre-shared-key ascii-text "$ABC123"; ## SECRET-DATA
}
policy SRG2_IKE_POL500 {
proposals SRG2_IKE_PROP;
pre-shared-key ascii-text "$ABC123"; ## SECRET-DATA
}
gateway SRG1_IKE_GW1 {
ike-policy SRG1_IKE_POL1;
address 10.112.0.1;
external-interface lo0;
local-address 10.11.0.1;
version v2-only;
}
gateway SRG2_IKE_GW500 {
ike-policy SRG2_IKE_POL500;
address 10.112.0.5;
external-interface lo0;
local-address 10.12.0.1;
version v2-only;
}
}
ipsec {
proposal SRG1_IPSEC_PROP {
protocol esp;
authentication-algorithm hmac-sha-256-128;
encryption-algorithm aes-256-cbc;
lifetime-seconds 1800;
}
proposal SRG2_IPSEC_PROP {
protocol esp;
authentication-algorithm hmac-sha-256-128;
encryption-algorithm aes-256-cbc;
lifetime-seconds 1800;
}
policy SRG1_IPSEC_POL1 {
proposals SRG1_IPSEC_PROP;
}
policy SRG2_IPSEC_POL501 {
proposals SRG2_IPSEC_PROP;
}
policy SRG2_IPSEC_POL500 {
proposals SRG2_IPSEC_PROP;
}
policy SRG2_IPSEC_POL502 {
proposals SRG2_IPSEC_PROP;
}
policy SRG2_IPSEC_POL503 {
proposals SRG2_IPSEC_PROP;
}
vpn SRG1_IPSEC_VPN1 {
bind-interface st0.1;
ike {
gateway SRG1_IKE_GW1;
ipsec-policy SRG1_IPSEC_POL1;
}
traffic-selector ts1 {
local-ip 10.1.0.2/32;
remote-ip 10.7.0.2/32;
}
establish-tunnels on-traffic;
}
vpn SRG2_IPSEC_VPN500 {
bind-interface st0.500;
ike {
gateway SRG2_IKE_GW500;
ipsec-policy SRG2_IPSEC_POL500;
}
traffic-selector ts500 {
local-ip 10.8.0.2/32;
remote-ip 10.9.0.2/32;
}
establish-tunnels on-traffic;
}
}
zones {
security-zone vpn {
host-inbound-traffic {
system-services {
ike;
}
protocols {
all;
}
}
interfaces {
st0.1;
st0.500;
}
}
}
}
interfaces {
st0 {
unit 1 {
family inet;
family inet6;
}
unit 500 {
family inet;
family inet6;
}
}
}
[edit]
user@srx-2# show chassis high-availability
local-id 2 local-ip 10.22.0.1;
peer-id 1 {
peer-ip 10.22.0.2;
interface ge-0/0/2.0;
vpn-profile ICL_IPSEC_VPN;
liveness-detection {
minimum-interval 200;
multiplier 3;
}
}
services-redundancy-group 1 {
deployment-type routing;
peer-id {
1;
}
activeness-probe {
dest-ip {
10.111.0.1;
src-ip 10.11.0.1;
}
}
monitor {
bfd-liveliness 10.4.0.2 {
src-ip 10.4.0.1;
session-type singlehop;
interface ge-0/0/3.0;
}
interface {
ge-0/0/3;
ge-0/0/4;
}
}
active-signal-route {
10.39.1.1;
}
backup-signal-route {
10.39.1.2;
}
prefix-list SRG1_PFX;
managed-services ipsec;
preemption;
activeness-priority 200;
}
services-redundancy-group 2 {
peer-id {
1;
}
activeness-probe {
dest-ip {
10.111.0.1;
src-ip 10.12.0.1;
}
}
monitor {
bfd-liveliness 10.4.0.2 {
src-ip 10.4.0.1;
session-type singlehop;
interface ge-0/0/3.0;
}
interface {
ge-0/0/3;
ge-0/0/4;
}
}
active-signal-route {
10.49.1.1;
}
backup-signal-route {
10.49.1.2;
}
prefix-list SRG2_PFX;
managed-services ipsec;
preemption;
activeness-priority 1;
}
[edit]
user@srx-2# show security ike
proposal ICL_IKE_PROP {
description interchassisa_link_encr_tunnel;
authentication-method pre-shared-keys;
dh-group group14;
authentication-algorithm sha-256;
encryption-algorithm aes-256-cbc;
lifetime-seconds 300;
}
policy ICL_IKE_POL {
description interchassis_link_encr_tunnel;
proposals ICL_IKE_PROP;
pre-shared-key ascii-text "$ABC123"; ## SECRET-DATA
}
gateway ICL_IKE_GW {
ike-policy ICL_IKE_POL;
version v2-only;
}
[edit]
user@srx-2# show security ipsec
proposal ICL_IPSEC_PROP {
description interchassis_link_encr_tunnel;
protocol esp;
encryption-algorithm aes-256-gcm;
lifetime-seconds 300;
}
policy ICL_IPSEC_POL {
description interchassis_link_encr_tunnel;
proposals ICL_IPSEC_PROP;
}
vpn ICL_IPSEC_VPN {
ha-link-encryption;
ike {
gateway ICL_IKE_GW;
ipsec-policy ICL_IPSEC_POL;
}
}
[edit]
user@srx-2# show policy-options
prefix-list SRG1_PFX {
10.11.0.0/24;
}
prefix-list SRG2_PFX {
10.12.0.0/24;
}
route-filter-list srg1_rf_list {
10.11.0.0/24 orlonger;
10.7.0.0/24 orlonger;
10.1.0.0/24 orlonger;
}
route-filter-list srg2_rf_list {
10.12.0.0/24 orlonger;
10.9.0.0/24 orlonger;
10.8.0.0/24 orlonger;
}
policy-statement mnha-route-policy {
term 1 {
from {
route-filter-list srg1_rf_list;
condition active_route_exists_srg1;
}
then {
metric 10;
accept;
}
}
term 2 {
from {
route-filter-list srg1_rf_list;
condition backup_route_exists_srg1;
}
then {
metric 20;
accept;
}
}
term 3 {
from {
route-filter-list srg2_rf_list;
condition active_route_exists_srg2;
}
then {
metric 10;
accept;
}
}
term 4 {
from {
route-filter-list srg2_rf_list;
condition backup_route_exists_srg2;
}
then {
metric 20;
accept;
}
}
term default {
then reject;
}
}
condition active_route_exists_srg1 {
if-route-exists {
address-family {
inet {
10.39.1.1/32;
table inet.0;
}
}
}
}
condition active_route_exists_srg2 {
if-route-exists {
address-family {
inet {
10.49.1.1/32;
table inet.0;
}
}
}
}
condition backup_route_exists_srg1 {
if-route-exists {
address-family {
inet {
10.39.1.2/32;
table inet.0;
}
}
}
}
condition backup_route_exists_srg2 {
if-route-exists {
address-family {
inet {
10.49.1.2/32;
table inet.0;
}
}
}
}
[edit]
user@srx-2# show routing-options
autonomous-system 100;
static {
route 10.7.0.0/24 next-hop 10.4.0.2;
route 10.112.0.0/24 next-hop 10.4.0.2;
}
[edit]
user@srx-2# show security zones
security-zone untrust {
host-inbound-traffic {
system-services {
ike;
ping;
}
protocols {
bfd;
bgp;
}
}
interfaces {
lo0.0;
ge-0/0/3.0;
}
}
security-zone vpn {
host-inbound-traffic {
system-services {
ike;
}
protocols {
all;
}
}
interfaces {
st0.1;
}
}
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
ge-0/0/4.0;
}
}
security-zone icl_zone {
host-inbound-traffic {
system-services {
ike;
ping;
high-availability;
ssh;
}
protocols {
bfd;
bgp;
}
}
interfaces {
ge-0/0/2.0;
}
}
[edit]
user@srx-2# show interfaces
ge-0/0/1 {
unit 0 {
family inet;
}
}
ge-0/0/2 {
description inter_chassis_link;
unit 0 {
family inet {
address 10.22.0.1/24;
}
}
}
ge-0/0/3 {
description untrust;
unit 0 {
family inet {
address 10.2.0.2/24;
}
}
}
ge-0/0/4 {
description trust;
unit 0 {
family inet {
address 10.4.0.1/24;
}
}
}
lo0 {
apply-groups-except global;
description untrust;
unit 0 {
family inet {
address 10.11.0.1/32;
address 10.12.0.1/32;
}
}
}
st0 {
unit 1 {
family inet;
}
}
Wenn Sie mit der Konfiguration des Geräts fertig sind, rufen Sie den Konfigurationsmodus auf commit .
user@host# commit warning: High Availability Mode changed, please reboot the device to avoid undesirable behavior commit complete
Ergebnisse (SRX-3) (VPN-Peer-Gerät)
Bestätigen Sie im Konfigurationsmodus Ihre Konfiguration durch Eingabe der folgenden Befehle. Wenn die Ausgabe nicht die beabsichtigte Konfiguration anzeigt, wiederholen Sie die Konfigurationsanweisungen in diesem Beispiel, um sie zu korrigieren.
[edit]
user@srx-3# show security ike
proposal SRG1_IKE_PROP {
authentication-method pre-shared-keys;
dh-group group14;
authentication-algorithm sha-256;
encryption-algorithm aes-256-cbc;
lifetime-seconds 3600;
}
proposal SRG2_IKE_PROP {
authentication-method pre-shared-keys;
dh-group group14;
authentication-algorithm sha-256;
encryption-algorithm aes-256-cbc;
lifetime-seconds 3600;
}
policy SRG1_IKE_POL1 {
proposals SRG1_IKE_PROP;
pre-shared-key ascii-text "$ABC123"; ## SECRET-DATA
}
policy SRG2_IKE_POL500 {
proposals SRG2_IKE_PROP;
pre-shared-key ascii-text "$ABC123"; ## SECRET-DATA
}
gateway SRG1_IKE_GW1 {
ike-policy SRG1_IKE_POL1;
address 10.11.0.1;
external-interface lo0;
local-address 10.112.0.1;
version v2-only;
}
gateway SRG2_IKE_GW500 {
ike-policy SRG2_IKE_POL500;
address 10.12.0.1;
external-interface lo0;
local-address 10.112.0.5;
version v2-only;
}
[edit]
user@srx-3# show security ipsec
proposal SRG1_IPSEC_PROP {
protocol esp;
authentication-algorithm hmac-sha-256-128;
encryption-algorithm aes-256-cbc;
lifetime-seconds 1800;
}
proposal SRG2_IPSEC_PROP {
protocol esp;
authentication-algorithm hmac-sha-256-128;
encryption-algorithm aes-256-cbc;
lifetime-seconds 1800;
}
policy SRG1_IPSEC_POL1 {
proposals SRG1_IPSEC_PROP;
}
policy SRG2_IPSEC_POL500 {
proposals SRG2_IPSEC_PROP;
}
vpn SRG1_IPSEC_VPN1 {
bind-interface st0.1;
ike {
gateway SRG1_IKE_GW1;
ipsec-policy SRG1_IPSEC_POL1;
}
traffic-selector ts1 {
local-ip 10.7.0.2/32;
remote-ip 10.1.0.2/32;
}
establish-tunnels immediately;
}
vpn SRG2_IPSEC_VPN500 {
bind-interface st0.500;
ike {
gateway SRG2_IKE_GW500;
ipsec-policy SRG2_IPSEC_POL500;
}
traffic-selector ts1 {
local-ip 10.9.0.2/32;
remote-ip 10.8.0.2/32;
}
establish-tunnels immediately;
}
[edit]
user@srx-3# show routing-options
autonomous-system 100;
static {
route 10.4.0.0/24 next-hop 10.7.0.2;
route 10.5.0.0/24 next-hop 10.7.0.2;
route 10.11.0.0/24 next-hop 10.7.0.2;
route 10.12.0.0/24 next-hop 10.7.0.2;
route 10.111.0.1/32 next-hop 10.7.0.2;
route 10.111.0.2/32 next-hop 10.7.0.2;
}
[edit]
user@srx-3# show security zones
security-zone untrust {
host-inbound-traffic {
system-services {
ike;
}
protocols {
all;
}
}
interfaces {
st0.1;
lo0.0;
st0.500;
ge-0/0/1.0;
ge-0/0/0.0;
}
}
security-zone trust {
host-inbound-traffic {
system-services {
ike;
}
protocols {
all;
}
}
interfaces {
ge-0/0/2.0;
}
}
[edit]
user@srx-3# show interfaces
ge-0/0/0 {
description trust;
unit 0 {
family inet {
address 10.7.0.1/24;
}
}
}
ge-0/0/1 {
description untrust;
unit 0 {
family inet {
address 10.6.0.2/24;
}
}
}
ge-0/0/2 {
description trust;
unit 0 {
family inet {
address 10.9.0.1/24;
}
}
}
lo0 {
description untrust;
unit 0 {
family inet {
address 10.112.0.1/32;
address 10.112.0.5/32;
}
}
}
st0 {
unit 1 {
family inet;
}
unit 500 {
family inet;
}
}
Wenn Sie mit der Konfiguration des Geräts fertig sind, rufen Sie den Konfigurationsmodus auf commit .
Verifizierung
Bestätigen Sie, dass die Konfiguration ordnungsgemäß funktioniert.
- Überprüfen Sie die Details zur Multinode-Hochverfügbarkeit
- Überprüfen Sie die Details zur Multinode-Hochverfügbarkeit
- Überprüfen Sie den Status des Peer-Knotens mit hoher Verfügbarkeit von Multinodes.
- Überprüfen Sie die Redundanzgruppen für Multinode-Services mit hoher Verfügbarkeit
- Überprüfen Sie den Interchassis Link (ICL)-Verschlüsselungsstatus
- Überprüfen Sie die Tunnelstatistiken für die Linkverschlüsselung
- Überprüfen Sie die aktiven Peers der Interchassis-Verbindung
- VPN-Status bestätigen
- Details zur IPsec-Sicherheit-Zuordnung anzeigen
- Anzeige aktiver Peers pro SRG
- Zuordnung von IP-Präfix zu SRG anzeigen
- Zeigen Sie BGP-Sitzungsinformationen an.
Überprüfen Sie die Details zur Multinode-Hochverfügbarkeit
Zweck
Zeigen Sie die Details der auf Ihrem Sicherheitsgerät konfigurierten Multinode-Hochverfügbarkeitseinrichtung an und überprüfen Sie sie.
Aktion
Führen Sie im Betriebsmodus den folgenden Befehl aus:
Auf SRX-1
user@srx-01> show chassis high-availability information
Node failure codes:
HW Hardware monitoring LB Loopback monitoring
MB Mbuf monitoring SP SPU monitoring
CS Cold Sync monitoring SU Software Upgrade
Node Status: ONLINE
Local-id: 1
Local-IP: 10.22.0.2
HA Peer Information:
Peer Id: 2 IP address: 10.22.0.1 Interface: ge-0/0/2.0
Routing Instance: default
Encrypted: YES Conn State: UP
Cold Sync Status: COMPLETE
SRG failure event codes:
BF BFD monitoring
IP IP monitoring
IF Interface monitoring
CP Control Plane monitoring
Services Redundancy Group: 1
Deployment Type: ROUTING
Status: BACKUP
Activeness Priority: 1
Preemption: ENABLED
Process Packet In Backup State: NO
Control Plane State: READY
System Integrity Check: COMPLETE
Failure Events: NONE
Peer Information:
Peer Id: 2
Status : ACTIVE
Health Status: HEALTHY
Failover Readiness: N/A
Services Redundancy Group: 2
Deployment Type: ROUTING
Status: ACTIVE
Activeness Priority: 200
Preemption: ENABLED
Process Packet In Backup State: NO
Control Plane State: READY
System Integrity Check: N/A
Failure Events: NONE
Peer Information:
Peer Id: 2
Status : BACKUP
Health Status: HEALTHY
Failover Readiness: NOT READY
Auf SRX-2
user@srx-02> show chassis high-availability information
Node failure codes:
HW Hardware monitoring LB Loopback monitoring
MB Mbuf monitoring SP SPU monitoring
CS Cold Sync monitoring SU Software Upgrade
Node Status: ONLINE
Local-id: 2
Local-IP: 10.22.0.1
HA Peer Information:
Peer Id: 1 IP address: 10.22.0.2 Interface: ge-0/0/2.0
Routing Instance: default
Encrypted: YES Conn State: UP
Cold Sync Status: COMPLETE
SRG failure event codes:
BF BFD monitoring
IP IP monitoring
IF Interface monitoring
CP Control Plane monitoring
Services Redundancy Group: 1
Deployment Type: ROUTING
Status: ACTIVE
Activeness Priority: 200
Preemption: ENABLED
Process Packet In Backup State: NO
Control Plane State: READY
System Integrity Check: N/A
Failure Events: NONE
Peer Information:
Peer Id: 1
Status : BACKUP
Health Status: HEALTHY
Failover Readiness: NOT READY
Services Redundancy Group: 2
Deployment Type: ROUTING
Status: BACKUP
Activeness Priority: 1
Preemption: ENABLED
Process Packet In Backup State: NO
Control Plane State: READY
System Integrity Check: COMPLETE
Failure Events: NONE
Peer Information:
Peer Id: 1
Status : ACTIVE
Health Status: HEALTHY
Failover Readiness: N/A
Bedeutung
Überprüfen Sie diese Details in der Befehlsausgabe:
Details zum lokalen Knoten und Peer-Knoten wie IP-Adresse und ID.
Das Feld
Encrypted: YESgibt an, dass der Datenverkehr geschützt ist.Das Feld
Deployment Type: ROUTINGgibt eine Layer-3-Moduskonfiguration an, d. h. das Netzwerk verfügt über Router auf beiden Seiten.Das Feld
Services Redundancy Group: 1undServices Redundancy Group: 2geben den Status von SRG1 und SRG2 (aktiv oder Backup) auf diesem Knoten an.
Überprüfen Sie die Details zur Multinode-Hochverfügbarkeit
Zweck
Zeigen Sie die Details der auf Ihrem Sicherheitsgerät konfigurierten Multinode-Hochverfügbarkeitseinrichtung an und überprüfen Sie sie.
Aktion
Führen Sie im Betriebsmodus den folgenden Befehl aus:
Auf SRX-01
user@srx-01> show chassis high-availability information detail
Node level Information:
Node Status: ONLINE
Local-id: 1
Local-IP: 10.22.0.2
HA Peer Information:
Peer-ID: 2 IP address: 10.22.0.1 Interface: ge-0/0/2.0
Routing Instance: default
Encrypted: YES Conn State: UP
Cold Sync Status: COMPLETE
Internal Interface: st0.16000
Internal Local-IP: 180.100.1.2
Internal Peer-IP: 180.100.1.1
Internal Routing-instance: __juniper_private1__
Packet Statistics:
Receive Error : 0 Send Error : 0
Packet-type Sent Received
SRG Status Msg 4 6
SRG Status Ack 4 4
Attribute Msg 1 1
Attribute Ack 1 1
HA Peer Conn events:
Jan 31 00:55:19.249 : HA Peer 180.100.1.1 BFD conn came up
Cold Synchronization:
Status:
Cold synchronization completed for: N/A
Cold synchronization failed for: N/A
Cold synchronization not known for: N/A
Current Monitoring Weight: 0
Progress:
CS Prereq 1 of 1 SPUs completed
1. if_state sync 1 SPUs completed
2. ha peer conn 1 SPUs completed
3. policy data sync 1 SPUs completed
4. cp ready 1 SPUs completed
5. VPN data sync 1 SPUs completed
6. IPID data sync 1 SPUs completed
7. All SPU ready 1 SPUs completed
8. AppID ready 1 SPUs completed
9. Tunnel Sess ready 1 SPUs completed
CS RTO sync 1 of 1 SPUs completed
CS Postreq 1 of 1 SPUs completed
Statistics:
Number of cold synchronization completed: 0
Number of cold synchronization failed: 0
Events:
Jan 31 00:55:24.616 : Cold sync for PFE is Post-req check in process
Jan 31 00:55:25.615 : Cold sync for PFE is Completed
SPU monitoring:
Status: Enabled
Current monitoring weight: 0
Statistics:
SPU up count: 1
NPC up count: 0
SPU down count: 0
NPC down count: 0
Chassis info processing error count: 0
Loopback Information:
PIC Name Loopback Nexthop Mbuf
-------------------------------------------------
Success Success Success
Hardware monitoring:
Status:
Activation status: Enabled
Ctrl Plane Hardware errors: 0
Data Plane Hardware errors: 0
SRGS Information:
Services Redundancy Group: 1
Deployment Type: ROUTING
Status: BACKUP
Activeness Priority: 1
Hold Timer: 1
Services: [ IPSEC ]
Process Packet In Backup State: NO
Control Plane State: READY
System Integrity Check: COMPLETE
Peer Information:
Failure Events: NONE
Peer Id: 2
Last Advertised HA Status: ACTIVE
Last Advertised Health Status: HEALTHY
Failover Readiness: N/A
Signal Route Info:
Active Signal Route:
IP: 10.39.1.1
Routing Instance: default
Status: NOT INSTALLED
Backup Signal Route:
IP: 10.39.1.2
Routing Instance: default
Status: INSTALLED
Split-brain Prevention Probe Info:
DST-IP: 10.111.0.1
SRC-IP: 10.11.0.1
Routing Instance: default
Status: NOT RUNNING
Result: N/A Reason: N/A
SRG State Change Events:
Jan 31 00:52:14.347 : SRG[1] state UNKNOWN -> HOLD, Reason: State machine start
Jan 31 00:56:33.046 : SRG[1] state HOLD -> BACKUP, Reason: Peer state Active received
BFD Monitoring:
Status: UNKNOWN
SRC-IP: 10.5.0.1 DST-IP: 10.5.0.2
Routing Instance: default
Type: SINGLE-HOP
IFL Name: ge-0/0/3.0
State: INSTALLED
Interface Monitoring:
Status: UP
IF Name: ge-0/0/4 State: Up
IF Name: ge-0/0/3 State: Up
Probe status events:
Jan 31 00:54:12.695 : SRG[1] HA probe dst 10.111.0.1 became unreachable, Reason: UNKNOWN
SRGS Information:
Services Redundancy Group: 2
Deployment Type: ROUTING
Status: ACTIVE
Activeness Priority: 200
Hold Timer: 1
Services: [ IPSEC ]
Process Packet In Backup State: NO
Control Plane State: READY
System Integrity Check: N/A
Peer Information:
Failure Events: NONE
Peer Id: 2
Last Advertised HA Status: BACKUP
Last Advertised Health Status: HEALTHY
Failover Readiness: NOT READY
Signal Route Info:
Active Signal Route:
IP: 10.49.1.1
Routing Instance: default
Status: INSTALLED
Backup Signal Route:
IP: 10.49.1.2
Routing Instance: default
Status: NOT INSTALLED
Split-brain Prevention Probe Info:
DST-IP: 10.111.0.1
SRC-IP: 10.12.0.1
Routing Instance: default
Status: NOT RUNNING
Result: N/A Reason: N/A
SRG State Change Events:
Jan 31 00:52:14.439 : SRG[2] state UNKNOWN -> HOLD, Reason: State machine start
Jan 31 00:55:24.263 : SRG[2] state HOLD -> ACTIVE, Reason: Local Priority Higher
BFD Monitoring:
Status: UNKNOWN
SRC-IP: 10.5.0.1 DST-IP: 10.5.0.2
Routing Instance: default
Type: SINGLE-HOP
IFL Name: ge-0/0/3.0
State: INSTALLED
Interface Monitoring:
Status: UP
IF Name: ge-0/0/4 State: Up
IF Name: ge-0/0/3 State: Up
Probe status events:
Jan 31 00:54:13.698 : SRG[2] HA probe dst 10.111.0.1 became unreachable, Reason: UNKNOWN
Bedeutung
Überprüfen Sie diese Details in der Befehlsausgabe:
Das Feld
Services: [ IPSEC ]gibt das zugeordnete IPSec-VPN für jede SRG an.Die Felder
BFD Monitoring,Interface MonitoringzeigenSplit-brain Prevention Probe InfoMonitoring-Details an.Die Felder
Cold SynchronizationSRG State Change Eventsenthalten Details zum aktuellen Status und zu den letzten Änderungen.Das Feld
Services Redundancy Group: 1undServices Redundancy Group: 2geben den Status von SRG1 und SRG2 (aktiv oder Backup) auf diesem Knoten an.
In der Befehlsausgabe werden die IP-Adressen wie IP 180.100.1.2 intern von Junos OS generiert und diese Adressen beeinträchtigen Routing-Tabellen nicht.
Überprüfen Sie den Status des Peer-Knotens mit hoher Verfügbarkeit von Multinodes.
Zweck
Zeigen Sie die Details des Peer-Knotens an und überprüfen Sie sie.
Aktion
Führen Sie im Betriebsmodus den folgenden Befehl auf SRX-01 und SRX-02 aus:
SRX-01
user@srx-01> show chassis high-availability peer-info
HA Peer Information:
Peer-ID: 2 IP address: 10.22.0.1 Interface: ge-0/0/2.0
Routing Instance: default
Encrypted: YES Conn State: UP
Cold Sync Status: COMPLETE
Internal Interface: st0.16000
Internal Local-IP: 180.100.1.2
Internal Peer-IP: 180.100.1.1
Internal Routing-instance: __juniper_private1__
Packet Statistics:
Receive Error : 0 Send Error : 0
Packet-type Sent Received
SRG Status Msg 4 6
SRG Status Ack 4 4
Attribute Msg 1 1
Attribute Ack 1 1
SRX-02
user@srx-02> show chassis high-availability peer-info
HA Peer Information:
Peer-ID: 1 IP address: 10.22.0.2 Interface: ge-0/0/2.0
Routing Instance: default
Encrypted: YES Conn State: UP
Cold Sync Status: COMPLETE
Internal Interface: st0.16000
Internal Local-IP: 180.100.1.1
Internal Peer-IP: 180.100.1.2
Internal Routing-instance: __juniper_private1__
Packet Statistics:
Receive Error : 0 Send Error : 0
Packet-type Sent Received
SRG Status Msg 6 4
SRG Status Ack 4 4
Attribute Msg 2 1
Attribute Ack 1 1
Bedeutung
Überprüfen Sie diese Details in der Befehlsausgabe:
Details zum Peer-Knoten wie verwendete Schnittstelle, IP-Adresse und ID
Verschlüsselungsstatus, Verbindungsstatus und Kaltsynchronisierungsstatus
Paketstatistiken über den gesamten Knoten.
Überprüfen Sie die Redundanzgruppen für Multinode-Services mit hoher Verfügbarkeit
Zweck
Stellen Sie sicher, dass die SRGs konfiguriert sind und ordnungsgemäß funktionieren.
Aktion
Führen Sie im Betriebsmodus den folgenden Befehl auf beiden Sicherheitsgeräten aus:
SRG1 auf SRX-02
user@srx-02> show chassis high-availability services-redundancy-group 1
SRG failure event codes:
BF BFD monitoring
IP IP monitoring
IF Interface monitoring
CP Control Plane monitoring
Services Redundancy Group: 1
Deployment Type: ROUTING
Status: ACTIVE
Activeness Priority: 200
Preemption: ENABLED
Process Packet In Backup State: NO
Control Plane State: READY
System Integrity Check: N/A
Failure Events: NONE
Peer Information:
Peer Id: 1
Status : BACKUP
Health Status: HEALTHY
Failover Readiness: NOT READY
Signal Route Info:
Active Signal Route:
IP: 10.39.1.1
Routing Instance: default
Status: INSTALLED
Backup Signal Route:
IP: 10.39.1.2
Routing Instance: default
Status: NOT INSTALLED
Split-brain Prevention Probe Info:
DST-IP: 10.111.0.1
SRC-IP: 10.11.0.1
Routing Instance: default
Status: NOT RUNNING
Result: N/A Reason: N/A
BFD Monitoring:
Status: UNKNOWN
SRC-IP: 10.4.0.1 DST-IP: 10.4.0.2
Routing Instance: default
Type: SINGLE-HOP
IFL Name: ge-0/0/3.0
State: INSTALLED
Interface Monitoring:
Status: UP
IF Name: ge-0/0/4 State: Up
IF Name: ge-0/0/3 State: Up
IP SRGID Table:
SRGID IP Prefix Routing Table
1 10.11.0.0/24 default
SRG2 auf SRX-02
user@srx-02> show chassis high-availability services-redundancy-group 2
SRG failure event codes:
BF BFD monitoring
IP IP monitoring
IF Interface monitoring
CP Control Plane monitoring
Services Redundancy Group: 2
Deployment Type: ROUTING
Status: BACKUP
Activeness Priority: 1
Preemption: ENABLED
Process Packet In Backup State: NO
Control Plane State: READY
System Integrity Check: COMPLETE
Failure Events: NONE
Peer Information:
Peer Id: 1
Status : ACTIVE
Health Status: HEALTHY
Failover Readiness: N/A
Signal Route Info:
Active Signal Route:
IP: 10.49.1.1
Routing Instance: default
Status: NOT INSTALLED
Backup Signal Route:
IP: 10.49.1.2
Routing Instance: default
Status: INSTALLED
Split-brain Prevention Probe Info:
DST-IP: 10.111.0.1
SRC-IP: 10.12.0.1
Routing Instance: default
Status: NOT RUNNING
Result: N/A Reason: N/A
BFD Monitoring:
Status: UNKNOWN
SRC-IP: 10.4.0.1 DST-IP: 10.4.0.2
Routing Instance: default
Type: SINGLE-HOP
IFL Name: ge-0/0/3.0
State: INSTALLED
Interface Monitoring:
Status: UP
IF Name: ge-0/0/4 State: Up
IF Name: ge-0/0/3 State: Up
IP SRGID Table:
SRGID IP Prefix Routing Table
2 10.12.0.0/24 default
SRG1 auf SRX-01
user@srx-01> show chassis high-availability services-redundancy-group 1
SRG failure event codes:
BF BFD monitoring
IP IP monitoring
IF Interface monitoring
CP Control Plane monitoring
Services Redundancy Group: 1
Deployment Type: ROUTING
Status: BACKUP
Activeness Priority: 1
Preemption: ENABLED
Process Packet In Backup State: NO
Control Plane State: READY
System Integrity Check: COMPLETE
Failure Events: NONE
Peer Information:
Peer Id: 2
Status : ACTIVE
Health Status: HEALTHY
Failover Readiness: N/A
Signal Route Info:
Active Signal Route:
IP: 10.39.1.1
Routing Instance: default
Status: NOT INSTALLED
Backup Signal Route:
IP: 10.39.1.2
Routing Instance: default
Status: INSTALLED
Split-brain Prevention Probe Info:
DST-IP: 10.111.0.1
SRC-IP: 10.11.0.1
Routing Instance: default
Status: NOT RUNNING
Result: N/A Reason: N/A
BFD Monitoring:
Status: UNKNOWN
SRC-IP: 10.5.0.1 DST-IP: 10.5.0.2
Routing Instance: default
Type: SINGLE-HOP
IFL Name: ge-0/0/3.0
State: INSTALLED
Interface Monitoring:
Status: UP
IF Name: ge-0/0/4 State: Up
IF Name: ge-0/0/3 State: Up
IP SRGID Table:
SRGID IP Prefix Routing Table
1 10.11.0.0/24 default
SRG2 auf SRX-01
user@srx-01> show chassis high-availability services-redundancy-group 2
SRG failure event codes:
BF BFD monitoring
IP IP monitoring
IF Interface monitoring
CP Control Plane monitoring
Services Redundancy Group: 2
Deployment Type: ROUTING
Status: ACTIVE
Activeness Priority: 200
Preemption: ENABLED
Process Packet In Backup State: NO
Control Plane State: READY
System Integrity Check: N/A
Failure Events: NONE
Peer Information:
Peer Id: 2
Status : BACKUP
Health Status: HEALTHY
Failover Readiness: NOT READY
Signal Route Info:
Active Signal Route:
IP: 10.49.1.1
Routing Instance: default
Status: INSTALLED
Backup Signal Route:
IP: 10.49.1.2
Routing Instance: default
Status: NOT INSTALLED
Split-brain Prevention Probe Info:
DST-IP: 10.111.0.1
SRC-IP: 10.12.0.1
Routing Instance: default
Status: NOT RUNNING
Result: N/A Reason: N/A
BFD Monitoring:
Status: UNKNOWN
SRC-IP: 10.5.0.1 DST-IP: 10.5.0.2
Routing Instance: default
Type: SINGLE-HOP
IFL Name: ge-0/0/3.0
State: INSTALLED
Interface Monitoring:
Status: UP
IF Name: ge-0/0/4 State: Up
IF Name: ge-0/0/3 State: Up
IP SRGID Table:
SRGID IP Prefix Routing Table
2 10.12.0.0/24 default
Bedeutung
Überprüfen Sie diese Details in der Befehlsausgabe:
Details zum Peer-Knoten wie Bereitstellung, Status, aktive und Backup-Signalrouten.
Sonde zur Split-Brain-Prävention, IP-Überwachung und BFD-Überwachungsstatus.
Zugeordnete IP-Präfixtabelle.
Überprüfen Sie den Interchassis Link (ICL)-Verschlüsselungsstatus
Zweck
Überprüfen Sie den ICL-Status (Interchassis Link).
Aktion
Führen Sie den folgenden Befehl auf SRX-01 aus:
user@srx-01> show security ipsec security-associations ha-link-encryption Total active tunnels: 1 Total IPsec sas: 1 ID Algorithm SPI Life:sec/kb Mon lsys Port Gateway <495002 ESP:aes-gcm-256/aes256-gcm 0x0008d9c7 236/ unlim - root 500 10.22.0.1 >495002 ESP:aes-gcm-256/aes256-gcm 0x0001a573 236/ unlim - root 500 10.22.0.1
user@srx-01> show security ike security-associations ha-link-encryption Index State Initiator cookie Responder cookie Mode Remote Address 16776938 UP 9f8fe46ce3be92f8 44e6b3fd74cc9294 IKEv2 10.22.0.1
user@srx-01> show security ipsec security-associations ha-link-encryption detail
ID: 495002 Virtual-system: root, VPN Name: ICL_IPSEC_VPN
Local Gateway: 10.22.0.2, Remote Gateway: 10.22.0.1
Traffic Selector Name: __ICL_IPSEC_VPN__multi_node__
Local Identity: ipv4(180.100.1.2-180.100.1.2)
Remote Identity: ipv4(180.100.1.1-180.100.1.1)
TS Type: traffic-selector
Version: IKEv2
Quantum Secured: No
PFS group: N/A
SRG ID: 0
DF-bit: clear, Copy-Outer-DSCP Disabled, Bind-interface: st0.16000, Policy-name: ICL_IPSEC_POL
Port: 500, Nego#: 0, Fail#: 0, Def-Del#: 0 Flag: 0
Multi-sa, Configured SAs# 0, Negotiated SAs#: 0
HA Link Encryption Mode: Multi-Node
Location: FPC -, PIC -, KMD-Instance -
Anchorship: Thread -
Distribution-Profile: default-profile
Direction: inbound, SPI: 0x0008d9c7, AUX-SPI: 0
, VPN Monitoring: -
Hard lifetime: Expires in 200 seconds
Lifesize Remaining: Unlimited
Soft lifetime: Expires in 115 seconds
Mode: Tunnel(0 0), Type: dynamic, State: installed
Protocol: ESP, Authentication: aes256-gcm, Encryption: aes-gcm (256 bits)
Anti-replay service: counter-based enabled, Replay window size: 64
Extended-Sequence-Number: Disabled
tunnel-establishment: establish-tunnels-immediately
Location: FPC 0, PIC 0, KMD-Instance 0
Anchorship: Thread 0
IKE SA Index: 16776938
Direction: outbound, SPI: 0x0001a573, AUX-SPI: 0
, VPN Monitoring: -
Hard lifetime: Expires in 200 seconds
Lifesize Remaining: Unlimited
Soft lifetime: Expires in 115 seconds
Mode: Tunnel(0 0), Type: dynamic, State: installed
Protocol: ESP, Authentication: aes256-gcm, Encryption: aes-gcm (256 bits)
Anti-replay service: counter-based enabled, Replay window size: 64
Extended-Sequence-Number: Disabled
tunnel-establishment: establish-tunnels-immediately
Location: FPC 0, PIC 0, KMD-Instance 0
Anchorship: Thread 0
IKE SA Index: 16776938
Bedeutung
Die Befehlsausgabe enthält die folgenden Informationen:
Details zum lokalen Gateway und Remote-Gateway.
Das IPsec-SA-Paar für jeden Thread in PIC.
Link-Verschlüsselungsmodus für Hohe Verfügbarkeit (wie in der folgenden Zeile gezeigt):
HA Link Encryption Mode: Multi-NodeVerwendete Authentifizierungs- und Verschlüsselungsalgorithmen
Der in der Befehlsausgabe angezeigte IP-Bereich (180.100.1.x) dient als ICL-IPsec-Datenverkehrsselektor. Das System weist diesen IP-Bereich dynamisch zu, und es ist wichtig, ihn nicht zu ändern oder zu modifizieren. Darüber hinaus wird BFD (Bidirectional Forwarding Detection) automatisch für den breiteren IP-Bereich 180.x.x.x aktiviert.
Überprüfen Sie die Tunnelstatistiken für die Linkverschlüsselung
Zweck
Überprüfen Sie die Link-Verschlüsselungs-Tunnel-Statistiken sowohl auf aktiven als auch auf Backup-Knoten.
Aktion
Führen Sie den folgenden Befehl auf SRX-01 aus:
user@srx-01> show security ipsec statistics ha-link-encryption ESP Statistics: Encrypted bytes: 106294156 Decrypted bytes: 51961287 Encrypted packets: 979531 Decrypted packets: 989651 AH Statistics: Input bytes: 0 Output bytes: 0 Input packets: 0 Output packets: 0 Errors: AH authentication failures: 0, Replay errors: 0 ESP authentication failures: 0, ESP decryption failures: 0 Bad headers: 0, Bad trailers: 0 Invalid SPI: 0, TS check fail: 0 Exceeds tunnel MTU: 0 Discarded: 0
Bedeutung
Wenn Sie Probleme mit Paketverlusten in einem VPN feststellen, können Sie den show security ipsec statistics ha-link-encryption Befehl mehrmals ausführen, um zu überprüfen, ob die Zähler für verschlüsselte und entschlüsselte Pakete inkrementiert werden. Sie sollten auch überprüfen, ob die anderen Fehlerzähler inkrementiert werden.
Verwenden Sie den clear security ipsec security-associations ha-link-encryption Befehl, um alle IPsec-Statistiken zu löschen.
Überprüfen Sie die aktiven Peers der Interchassis-Verbindung
Zweck
Zeigen Sie nur aktive ICL-Peers an, aber keine regulären aktiven IKE-Peers.
Aktion
Führen Sie die folgenden Befehle auf SRX-01- und SRX-02-Geräten aus:
SRX-1
user@srx-01> show security ike active-peer ha-link-encryption Remote Address Port Peer IKE-ID AAA username Assigned IP 10.22.0.1 500 10.22.0.1 not available 0.0.0.0
SRX-2
user@srx-02> show security ike active-peer ha-link-encryption Remote Address Port Peer IKE-ID AAA username Assigned IP 10.22.0.2 500 10.22.0.2 not available 0.0.0.0
Bedeutung
Die Befehlsausgabe zeigt nur den aktiven Peer des ICL mit Details wie den Peer-Adressen und Ports an, die der aktive Peer verwendet.
VPN-Status bestätigen
Zweck
Bestätigen Sie den VPN-Status, indem Sie den Status aller IKE-Sicherheitsverbände auf SRG-Ebene überprüfen.
Aktion
Führen Sie die folgenden Befehle auf SRX-1, SRX-2 und SRX-3 (VPN-Peer-Gerät) aus:
SRX-01
user@srx-01> show security ike security-associations srg-id 1
Index State Initiator cookie Responder cookie Mode Remote Address
16777319 UP 19e7cd4e503eeb2e 0800a7ceaafda740 IKEv2 10.112.0.1
user@srx-01> show security ike security-associations srg-id 2
Index State Initiator cookie Responder cookie Mode Remote Address
33554536 UP 9944aaf1ab914b42 15cef0da496bdd92 IKEv2 10.112.0.5
SRX-02
user@srx-02> show security ike security-associations srg-id 1 Index State Initiator cookie Responder cookie Mode Remote Address 16777319 UP 19e7cd4e503eeb2e 0800a7ceaafda740 IKEv2 10.112.0.1
user@srx-02> show security ike security-associations srg-id 2 Index State Initiator cookie Responder cookie Mode Remote Address 33554534 UP 366d174d847f8c71 2f654c6f1c463d80 IKEv2 10.112.0.5
SRX-3 (VPN-Peer-Gerät)
user@srx-03> show security ike security-associations Index State Initiator cookie Responder cookie Mode Remote Address 5929032 UP 366d174d847f8c71 2f654c6f1c463d80 IKEv2 10.12.0.1 5929033 UP 19e7cd4e503eeb2e 0800a7ceaafda740 IKEv2 10.11.0.1
Bedeutung
Die Ausgabe zeigt an, dass:
- IP-Adressen der Remote-Peers.
- Der Zustand, der für beide Remotepeers UP anzeigt, zeigt die erfolgreiche Zuordnung der Phase-1-Einrichtung an.
- Die Remote-Peer-IP-Adresse, die IKE-Richtlinie und die externen Schnittstellen sind alle korrekt.
Details zur IPsec-Sicherheit-Zuordnung anzeigen
Zweck
Zeigen Sie die einzelnen IPsec-SA-Details an, die durch SRG-IDs identifiziert werden.
Aktion
Führen Sie den folgenden Befehl auf den Firewalls der SRX-Serie aus:
SRX-1
user@srx-01> show security ipsec security-associations srg-id 1 Total active tunnels: 1 Total IPsec sas: 1 ID Algorithm SPI Life:sec/kb Mon lsys Port Gateway <17277223 ESP:aes-cbc-256/sha256 0xc50520d4 1210/ unlim - root 500 10.112.0.1 >17277223 ESP:aes-cbc-256/sha256 0x6d1e9c89 1210/ unlim - root 500 10.112.0.1
user@srx-01> show security ipsec security-associations srg-id 2 Total active tunnels: 1 Total IPsec sas: 1 ID Algorithm SPI Life:sec/kb Mon lsys Port Gateway <34054437 ESP:aes-cbc-256/sha256 0x9feb290c 1382/ unlim - root 500 10.112.0.5 >34054437 ESP:aes-cbc-256/sha256 0xf41d091c 1382/ unlim - root 500 10.112.0.5
SRX-02
user@srx-02> show security ipsec security-associations srg-id 1
Total active tunnels: 1 Total IPsec sas: 1
ID Algorithm SPI Life:sec/kb Mon lsys Port Gateway
<17277223 ESP:aes-cbc-256/sha256 0xc50520d4 1286/ unlim - root 500 10.112.0.1
>17277223 ESP:aes-cbc-256/sha256 0x6d1e9c89 1286/ unlim - root 500 10.112.0.1
user@srx-02> show security ipsec security-associations srg-id 2 Total active tunnels: 1 Total IPsec sas: 1 ID Algorithm SPI Life:sec/kb Mon lsys Port Gateway <34054437 ESP:aes-cbc-256/sha256 0x9feb290c 1461/ unlim - root 500 10.112.0.5 >34054437 ESP:aes-cbc-256/sha256 0xf41d091c 1461/ unlim - root 500 10.112.0.5
SRX-03
user@srx-03> show security ipsec security-associations
Total active tunnels: 2 Total Ipsec sas: 2
ID Algorithm SPI Life:sec/kb Mon lsys Port Gateway
<67108865 ESP:aes-cbc-256/sha256 6d1e9c89 1392/ unlim - root 500 10.11.0.1
>67108865 ESP:aes-cbc-256/sha256 c50520d4 1392/ unlim - root 500 10.11.0.1
<67108866 ESP:aes-cbc-256/sha256 f41d091c 1570/ unlim - root 500 10.12.0.1
>67108866 ESP:aes-cbc-256/sha256 9feb290c 1570/ unlim - root 500 10.12.0.1
Bedeutung
Die Ausgabe zeigt den Status des VPN an.
Anzeige aktiver Peers pro SRG
Zweck
Zeigen Sie die Liste der verbundenen aktiven Peers mit den von ihnen verwendeten Peer-Adressen und -Ports an.
Aktion
Führen Sie die folgenden Befehle auf den Firewalls der SRX-Serie aus:
SRX-01
user@srx-01> show security ike active-peer srg-id 1 Remote Address Port Peer IKE-ID AAA username Assigned IP 10.112.0.1 500 10.112.0.1 not available 0.0.0.0
user@srx-01> show security ike active-peer srg-id 2 Remote Address Port Peer IKE-ID AAA username Assigned IP 10.112.0.5 500 10.112.0.5 not available 0.0.0.0
SRX-02
user@srx-02> show security ike active-peer srg-id 1 Remote Address Port Peer IKE-ID AAA username Assigned IP 10.112.0.1 500 10.112.0.1 not available 0.0.0.0
user@srx-02> show security ike active-peer srg-id 2 Remote Address Port Peer IKE-ID AAA username Assigned IP 10.112.0.5 500 10.112.0.5 not available 0.0.0.0
Bedeutung
Die Ausgabe zeigt die Liste der angeschlossenen Geräte mit Details zu den verwendeten Peer-Adressen und Ports an.
Zuordnung von IP-Präfix zu SRG anzeigen
Zweck
Anzeige des IP-Präfixes für SRG-Zuordnungsinformationen.
Aktion
Führen Sie den folgenden Befehl auf dem SRX-01-Gerät aus.
user@srx-01> show chassis high-availability prefix-srgid-table
IP SRGID Table:
SRGID IP Prefix Routing Table
1 10.11.0.0/24 default
2 10.12.0.0/24 default
Bedeutung
Die Ausgabe zeigt IP-Adresspräfixe an, die SRGs im Setup zugeordnet sind.
Zeigen Sie BGP-Sitzungsinformationen an.
Zweck
Zeigen Sie zusammenfassende Informationen zu BGP und seinen Nachbarn an, um festzustellen, ob Routen von Peers empfangen werden.
Aktion
Führen Sie die folgenden Befehle auf den Firewalls der SRX-Serie aus:
SRX-1 Gerät
user@srx-01> show bgp summary
Threading mode: BGP I/O
Default eBGP mode: advertise - accept, receive - accept
Groups: 2 Peers: 2 Down peers: 0
Table Tot Paths Act Paths Suppressed History Damp State Pending
inet.0
0 0 0 0 0 0
Peer AS InPkt OutPkt OutQ Flaps Last Up/Dwn State|#Active/Received/Accepted/Damped...
10.3.0.1 100 37 40 0 0 15:43 Establ
inet.0: 0/0/0/0
10.5.0.2 100 37 40 0 0 15:42 Establ
inet.0: 0/0/0/0
SRX-2 Gerät
user@srx-02> show bgp summary
Threading mode: BGP I/O
Default eBGP mode: advertise - accept, receive - accept
Groups: 2 Peers: 2 Down peers: 0
Table Tot Paths Act Paths Suppressed History Damp State Pending
inet.0
0 0 0 0 0 0
Peer AS InPkt OutPkt OutQ Flaps Last Up/Dwn St ate|#Active/Received/Accepted/Damped...
10.2.0.1 100 842 846 0 0 6:18:40 Es tabl
inet.0: 0/0/0/0
10.4.0.2 100 842 846 0 0 6:18:42 Es tabl
inet.0: 0/0/0/0
Bedeutung
Die Ausgabe zeigt, dass die BGP-Sitzung eingerichtet wurde und die Peers Aktualisierungsnachrichten austauschen.
