DHCP Snooping for Network Security
DHCP Snooping Support
Dynamic Host Configuration Protocol (DHCP) is a network management protocol used in TCP/IP networks to dynamically assign IP addresses and other related configuration information to network devices.
How DHCP Snooping Works
Dynamic Host Configuration Protocol (DHCP) dynamically allocates IP addresses to devices, leasing addresses that can be reused when no longer needed. Hosts or end devices that require IP addresses through DHCP must communicate with a DHCP server across the LAN.
The following illustration shows the DHCP snooping process.
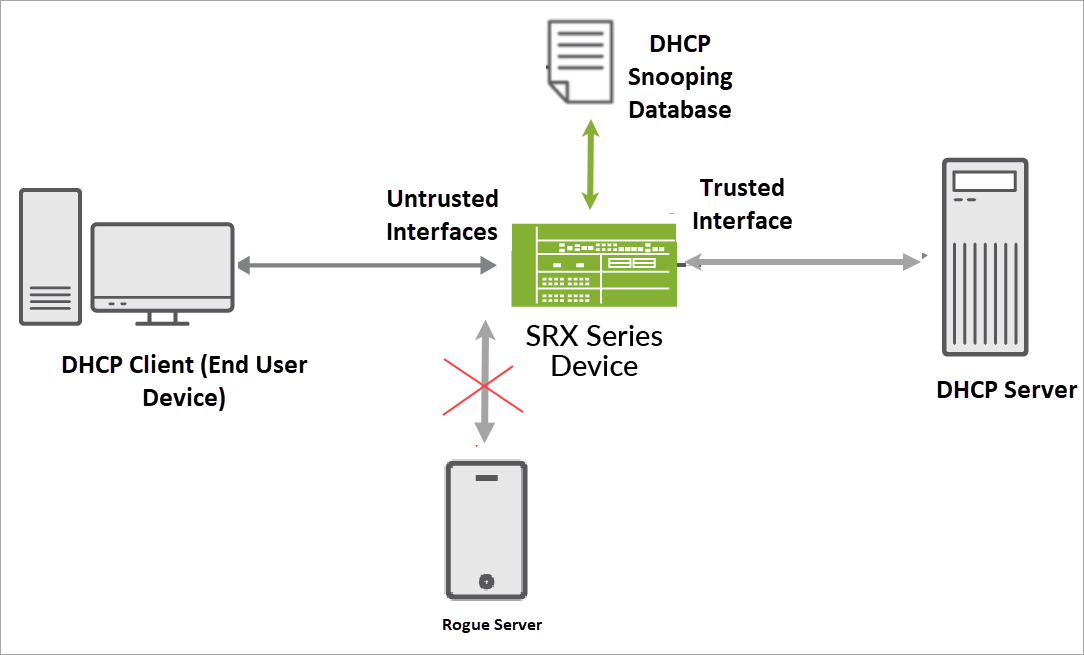
In the topology, an end user device connects to a Junos OS device (router, switch, or firewall). The Junos OS device connects to both the DHCP client and the DHCP server. The Junos OS device configured as a DHCP relay agent operates as the interface between DHCP clients and the DHCP server. This Junos OS device inspects DHCP packets. The DHCP server assigns IP addresses to clients.
The DHCP snooping feature on a Junos OS device performs the following actions:
- Validates DHCP messages received from untrusted sources and filters out invalid messages.
- Extracts the IP address leased to each client and builds a database. The DHCP snooping database (or binding table) includes information about the IP address, MAC address, and VLAN of each DHCP client.
- Uses the DHCP snooping binding table to validate subsequent requests from untrusted hosts. By verifying that DHCP requests are coming from trusted sources, the Juniper device can ensure that only valid DHCP requests are processed.
In this way, DHCP snooping acts as a guardian of network security by keeping track of valid IP addresses that a trusted DHCP server (a server connected to a trusted network port) assigns to downstream network devices.
DHCPv6 Relay Agent Snooping
The DHCPv6 relay agent enhances the DHCP relay agent by providing support in an IPv6 network. The DHCPv6 relay agent passes messages between the DHCPv6 client and the DHCPv6 server, similar to the way DHCP relay agent supports an IPv4 network. In a multi-relay topology that has multiple DHCPv6 relay agents between the client and the server, snooping enables the intervening relay agents to correctly process unicast traffic from the client and forward it to the server. Snooping in this topology involves these actions:
- The DHCPv6 relay agent snoops incoming unicast DHCPv6 packets using a filter with UDP port 547, which is the DHCPv6 UDP server port, on a per-forwarding table basis.
- The DHCPv6 relay agent then processes the packets intercepted by the filter and forwards the packets to the DHCPv6 server.
Benefits of DHCP Snooping
- DHCP snooping can provide an additional security layer by filtering IP addresses. The filtering process evaluates network traffic to allow communication from verified and valid IP addresses.
- DHCP snooping can prevent rogue DHCP activity in the network by filtering out DHCP packets that are arriving on the wrong ports, or with incorrect contents.
Configuring DHCP Snooped Packets Forwarding Support for DHCP Local Server
You can configure how DHCP local server handles DHCP snooped packets. Depending on the configuration, DHCP local server either forwards or drops the snooped packets it receives.
Table 1 indicates the action the router takes for DHCP local server snooped packets.
Configured interfaces are those interfaces that have been
configured with the group statement
in the [edit system services dhcp-local-server] hierarchy.
Non-configured interfaces are those that are in the logical system/routing
instance but have not been configured by the group statement.
forward-snooped-clients Configuration |
Action on Configured Interfaces |
Action on Non-Configured Interfaces |
|---|---|---|
|
dropped |
dropped |
|
forwarded |
forwarded |
|
forwarded |
dropped |
|
dropped |
forwarded |
To configure DHCP snooped packet forwarding for DHCP local server:
For example, to configure DHCP local server to forward DHCP snooped packets on only configured interfaces:
[edit]
system {
services {
dhcp-local-server {
forward-snooped-clients configured-interfaces;
}
}
}
See Also
Enabling and Disabling DHCP Snooped Packets Support for DHCP Relay Agent
DHCP relay agent uses a two-part configuration to determine how to handle DHCP snooped packets. This topic describes the first procedure, in which you enable or disable snooping support for DHCP relay agent and, optionally, override the default snooping configuration.
The second procedure, which applies only to DHCPv4 relay agent, is described in Configuring DHCP Snooped Packets Forwarding Support for DHCP Relay Agent, and configures the forwarding action for snooped clients, which specifies whether DHCP relay agent forwards or drops snooped traffic.
You can enable or disable DHCP globally for DHCP relay, for a group of interfaces, or for a specific interface in a group.
By default, DHCP snooping is enabled for DHCP relay. To enable or disable DHCP snooping support globally:
For example, to enable global DHCP snooping support :
forwarding-options {
dhcp-relay {
overrides {
allow-snooped-clients;
}
}
}
To enable or disable DHCP snooping support for a group of interfaces:
Specify that you want to configure DHCP relay agent.
For DHCP relay agent:
[edit] user@host# edit forwarding-options dhcp-relay
For DHCPv6 relay agent:
[edit] user@host# edit forwarding-options dhcp-relay dhcpv6
Specify the named group.
For DHCP relay agent:
[edit forwarding-options dhcp-relay] user@host# edit group group-name
For DHCPv6 relay agent:
[edit forwarding-options dhcp-relay dhcpv6] user@host# edit group group-name
Specify that you want to override the default configuration.
For DHCP relay agent:
[edit forwarding-options dhcp-relay group group-name] user@host# edit overrides
For DHCPv6 relay agent:
[edit forwarding-options dhcp-relay dhcpv6 group group-name] user@host# edit overrides
Enable or disable DHCP snooping support.
To enable DHCP snooping:
For DHCP relay agent:
[edit forwarding-options dhcp-relay group group-name overrides] user@host# set allow-snooped-clients
For DHCPv6 relay agent:
[edit forwarding-options dhcp-relay dhcpv6 group group-name overrides] user@host# set allow-snooped-clients
To disable DHCP snooping:
For DHCP relay agent:
[edit forwarding-options dhcp-relay group group-name overrides] user@host# set no-allow-snooped-clients
For DHCPv6 relay agent:
[edit forwarding-options dhcp-relay dhcpv6 group group-name overrides] user@host# set no-allow-snooped-clients
For example, to enable DHCP snooping support on all interfaces
in group boston:
forwarding-options {
dhcp-relay {
group boston {
overrides {
allow-snooped-clients;
}
}
}
}
To enable or disable DHCP snooping support on a specific interface:
Specify that you want to configure DHCP relay agent.
For DHCP relay agent:
[edit] user@host# edit forwarding-options dhcp-relay
For DHCPv6 relay agent:
[edit] user@host# edit forwarding-options dhcp-relay dhcpv6
Specify the named group containing the interface.
For DHCP relay agent:
[edit forwarding-options dhcp-relay] user@host# edit group group-name
For DHCPv6 relay agent:
[edit forwarding-options dhcp-relay dhcpv6] user@host# edit group group-name
Specify the interface for which you want to configure DHCP snooping.
For DHCP relay agent:
[edit forwarding-options dhcp-relay group group-name] user@host# edit interface interface-name
For DHCPv6 relay agent:
[edit forwarding-options dhcp-relay dhcpv6 group group-name] user@host# edit interface interface-name
Specify that you want to override the default configuration on the interface.
For DHCP relay agent:
[edit forwarding-options dhcp-relay group group-name interface interface-name] user@host# edit overrides
For DHCPv6 relay agent:
[edit forwarding-options dhcp-relay dhcpv6 group group-name interface interface-name] user@host# edit overrides
Enable or disable DHCP snooping support.
To enable DHCP snooping:
For DHCP relay agent:
[edit forwarding-options dhcp-relay group group-name interface interface-name overrides] user@host# set allow-snooped-clients
For DHCPv6 relay agent:
[edit forwarding-options dhcp-relay dhcpv6 group group-name interface interface-name overrides] user@host# set allow-snooped-clients
To disable DHCP snooping:
For DHCP relay agent:
[edit forwarding-options dhcp-relay group group-name interface interface-name overrides] user@host# set no-allow-snooped-clients
For DHCPv6 relay agent:
[edit forwarding-options dhcp-relay dhcpv6 group group-name interface interface-name overrides] user@host# set no-allow-snooped-clients
For example, to disable DHCP snooping support on interface ge-2/1/8.0 in group boston:
forwarding-options {
dhcp-relay {
group boston {
interface ge-2/1/8.0 {
overrides {
no-allow-snooped-clients;
}
}
}
}
}
To enable DHCPv6 snooping support on interface ge-3/2/1.1 in group sunnyvale:
forwarding-options {
dhcp-relay {
dhcpv6 {
group sunnyvale {
interface ge-3/2/1.1 {
overrides {
allow-snooped-clients;
}
}
}
}
}
}
See Also
DHCP Snooping Configuration
Disabling DHCP Snooping Filters
DHCP snooping provides DHCP security by identifying
incoming DHCP packets. In the default DHCP snooping configuration,
all traffic is snooped. You can optionally use the forward-snooped-clients statement to evaluate the snooped traffic and to determine whether
the traffic is forwarded or dropped, based on whether or not the interface
is configured as part of a group.
In both the default configuration and in configurations using
the forward-snooped-clients statement, all DHCP traffic
is forwarded from the hardware control plane to the routing plane
of the routing instance to ensure that all DHCP packets are intercepted.
In certain topologies, such as a Metropolitan Routing Ring topology,
forwarding all DHCP traffic to the control plane can result in excessive
traffic. The no-snoop configuration statement disables
the snooping filter for DHCP traffic that can be directly forwarded
on the hardware control plane, such as Layer 3 unicast packets with
a valid route, causing those DHCP packets to bypass the slower routing
plane. You can disable DHCP
snooping filters starting in Junos OS Release 15.1R2.
To disable DHCP snooping filters on the DHCP local server:
To disable DHCP snooping filters on the DHCP relay server:
Specify that you want to configure DHCP relay server.
[edit] user@host# edit forwarding-options dhcp-relay
Disable DHCP snooping filters for DHCP local server.
[edit forwarding-options dhcp-relay] user@host# set no-snoop
Specify that you want to configure DHCPv6 relay server.
[edit forwarding-options dhcp-relay] user@host# edit dhcpv6
Disable DHCP snooping filters for DHCPv6 local server.
[edit forwarding-options dhcp-relay dhcpv6] user@host# set no-snoop
See Also
Example: Configuring DHCP Snooping Support for DHCP Relay Agent
This example shows how to configure DHCP snooping support for DHCP relay agent.
Requirements
Configure DHCP relay agent. See Extended DHCP Relay Agent Overview.
Overview
In this example, you configure DHCP snooping support for DHCP relay agent by completing the following operations:
Override the default DHCP snooping configuration and enable DHCP snooping support for the interfaces in group frankfurt.
Configure DHCP relay agent to forward snooped packets to only configured interfaces.
Configuration
Procedure
Step-by-Step Procedure
To configure DHCP relay support for DHCP snooping:
Specify that you want to configure DHCP relay agent.
[edit] user@host# edit forwarding-options dhcp-relay
Specify the named group of interfaces on which DHCP snooping is supported.
[edit forwarding-options dhcp-relay] user@host# edit group frankfurt
Specify the interfaces that you want to include in the group. DHCP relay agent considers these as the configured interfaces when determining whether to forward or drop traffic.
[edit forwarding-options dhcp-relay group frankfurt] user@host# set interface fe-1/0/1.3 upto fe-1/0/1.9
Specify that you want to override the default configuration for the group.
[edit forwarding-options dhcp-relay group frankfurt] user@host# edit overrides
Enable DHCP snooping support for the group.
[edit forwarding-options dhcp-relay group frankfurt overrides] user@host# set allow-snooped-clients
Return to the
[edit forwarding-options dhcp-relay]hierarchy level to configure the forwarding action and specify that DHCP relay agent forward snooped packets on only configured interfaces:[edit forwarding-options dhcp-relay group frankfurt overrides] user@host# up 2
Enable DHCP snooped packet forwarding for DHCP relay agent.
[edit forwarding-options dhcp-relay] user@host# edit forward-snooped-clients
Specify that snooped packets are forwarded on only configured interfaces (the interfaces in group
frankfurt).[edit forwarding-options dhcp-relay forward-snooped-clients] user@host# set configured-interfaces
Results
From configuration mode, confirm your configuration
by entering the show forwarding-options command. If the
output does not display the intended configuration, repeat the instructions
in this example to correct it. The following output also shows a range
of configured interfaces in group frankfurt.
[edit]
user@host# show forwarding-options
dhcp-relay {
forward-snooped-clients configured-interfaces;
group frankfurt {
overrides {
allow-snooped-clients;
}
interface fe-1/0/1.3 {
upto fe-1/0/1.9;
}
}
}
If you are done configuring the device, enter commit from configuration mode.
Example: Enabling DHCP Snooping Support for DHCPv6 Relay Agent
Snooping support for DHCPv6 relay agent is disabled on the router by default. This example shows how to override the default DHCPv6 relay agent snooping configuration to explicitly enable DHCPv6 snooping for a named group of interfaces and for a specific interface within a different named group.
You can also enable DHCPv6 snooping support globally by
using the allow-snooped-clients statement at the [edit
forwarding-options dhcp-relay dhcpv6 overrides] hierarchy level.
Requirements
This example uses the following hardware and software components:
MX Series 5G Universal Routing Platforms
Junos OS Release 12.1 or later
Before you begin:
Configure DHCPv6 relay agent.
Configure named DHCPv6 relay agent interface groups to which you want to apply a common DHCP configuration.
Overview
In this example, you override the default DHCPv6 relay agent snooping configuration to explicitly enable DHCP snooping for both of the following:
All of the interfaces in the group named
bostonInterface
ge-3/2/1.1in the group namedsunnyvale
Configuration
To override the default DHCPv6 relay agent snooping configuration to explicitly enable DHCPv6 snooping for a named group of interfaces and for a specific interface within a named group, perform these tasks:
- CLI Quick Configuration
- Enabling DHCPv6 Snooping Support for a Named Group of Interfaces
- Enabling DHCPv6 Snooping Support for a Specific Interface in a Named Group
CLI Quick Configuration
To quickly configure this example, copy the
following commands, paste them in a text file, remove any line breaks,
change any details necessary to match your network configuration,
and then copy and paste the commands into the CLI at the [edit] hierarchy level.
set forwarding-options dhcp-relay dhcpv6 group boston overrides allow-snooped-clients set forwarding-options dhcp-relay dhcpv6 group sunnyvale interface ge-3/2/1.1 overrides allow-snooped-clients
Enabling DHCPv6 Snooping Support for a Named Group of Interfaces
Step-by-Step Procedure
To enable DHCPv6 snooping support for a named group of interfaces:
Specify that you want to configure DHCPv6 relay agent.
[edit] user@host# edit forwarding-options dhcp-relay dhcpv6
Specify the named group of interfaces for which you want to enable DHCPv6 snooping.
[edit forwarding-options dhcp-relay dhcpv6] user@host# edit group boston
Specify that you want to override the default DHCPv6 configuration for the interfaces in that group.
[edit forwarding-options dhcp-relay dhcpv6 group boston] user@host# edit overrides
Enable DHCPv6 snooping support for all interfaces in group
boston.[edit forwarding-options dhcp-relay dhcpv6 group boston overrides] user@host# set allow-snooped-clients
Results
From configuration mode, confirm the results of your
configuration by issuing the show statement at the [edit forwarding-options dhcp-relay] hierarchy level. If the
output does not display the intended configuration, repeat the configuration
instructions in this example to correct it.
[edit forwarding-options dhcp-relay]
user@host# show
dhcpv6 {
group boston {
overrides {
allow-snooped-clients;
}
}
}
If you are done configuring the router, enter commit from configuration mode.
Enabling DHCPv6 Snooping Support for a Specific Interface in a Named Group
Step-by-Step Procedure
To enable DHCPv6 snooping support for a specific interface within a named group of interfaces:
Return to the
[edit forwarding-options dhcp-relay dhcpv6]hierarchy level to specify that you want to configure DHCPv6 relay agent.[edit forwarding-options dhcp-relay dhcpv6 group boston overrides] user@host# up 2
Specify the named group containing the interface.
[edit forwarding-options dhcp-relay dhcpv6] user@host# edit group sunnyvale
Specify the interface in group
sunnyvalefor which you want to enable DHCPv6 snooping.[edit forwarding-options dhcp-relay dhcpv6 group sunnyvale] user@host# edit interface ge-3/2/1.1
Specify that you want to override the default DHCPv6 configuration for interface
ge-3/2/1.1in groupsunnyvale.[edit forwarding-options dhcp-relay dhcpv6 group sunnyvale interface ge-3/2/1.1] user@host# edit overrides
Enable DHCPv6 snooping support for interface
ge-3/2/1.1in groupsunnyvale.[edit forwarding-options dhcp-relay dhcpv6 group sunnyvale interface ge-3/2/1.1 overrides] user@host# set allow-snooped-clients
Results
From configuration mode, confirm the results of your
configuration by issuing the show statement at the [edit forwarding-options dhcp-relay] hierarchy level. If the
output does not display the intended configuration, repeat the configuration
instructions in this example to correct it.
[edit forwarding-options dhcp-relay]
user@host# show
dhcpv6 {
group boston {
overrides {
allow-snooped-clients;
}
}
group sunnyvale {
interface ge-3/2/1.1 {
overrides {
allow-snooped-clients;
}
}
}
}
If you are done configuring the router, enter commit from configuration mode.
Verification
To verify the DHCPv6 configuration in a multi-relay topology, perform this task:
Verifying the Address Bindings for DHCPv6 Relay Agent Clients
Purpose
Verify the DHCPv6 address bindings in the Dynamic Host Configuration Protocol (DHCP) client table.
Action
Display detailed information about address bindings for DHCPv6 relay agent clients.
user@host > show dhcpv6 relay binding detail
Session Id: 13
Client IPv6 Prefix: 2001:db8:0:8001::5/128
Client DUID: LL0x1-00:00:5e:00:53:02
State: BOUND(DHCPV6_RELAY_STATE_BOUND)
Lease Expires: 2011-11-21 06:14:50 PST
Lease Expires in: 293 seconds
Lease Start: 2011-11-21 06:09:50 PST
Incoming Client Interface: ge-3/2/1.1
Server Address: unknown
Next Hop Server Facing Relay: 2001:db8::2
Server Interface: none
Client Id Length: 10
Client Id: /0x00030001/0x00006503/0x0102
Meaning
The Server Address field in the show
dhcpv6 relay binding detail command output typically displays
the IP address of the DHCPv6 server. In this example, the value unknown in the Server Address field indicates that
this is a multi-relay topology in which the DHCPv6 relay agent is
not directly adjacent to the DHCPv6 server, and does not detect the
IP address of the server.
In that case, the output instead includes the Next Hop
Server Facing Relay field, which displays the next-hop address
in the direction of the DHCPv6 server.
Preventing DHCP Spoofing
A problem that sometimes occurs with DHCP is DHCP spoofing. In DHCP spoofing, an untrusted client floods a network with DHCP messages. Often these attacks utilize source IP address spoofing to conceal the true source of the attack.
DHCP snooping helps prevent DHCP spoofing by copying DHCP messages to the control plane and using the information in the packets to create anti-spoofing filters. The anti-spoofing filters bind a client’s MAC address to its DHCP-assigned IP address and use this information to filter spoofed DHCP messages. In a typical topology, a carrier edge router (in this function also referred to as the broadband network gateway [BNG]) connects the DHCP server and the MX Series router (or broadband services aggregator [BSA]) performing the snooping. The MX Series router connects to the client and the BNG.
To configure DHCP snooping, you include the appropriate interfaces within a DHCP group. You can configure DHCP snooping for VPLS environments and bridge domains.
In a VPLS environment, DHCP requests are forwarded over pseudowires. You configure DHCP snooping over VPLS at the
[edit routing-instances routing-instance-name]hierarchy level.In bridge domains, DHCP snooping works on a per learning bridge basis. Each learning domain must have an upstream interface configured. This interface acts as the flood port for DHCP requests coming from the client side. DHCP requests are forwarded across learning domains in a bridge domain. You configure DHCP snooping on bridge domains at the
[edit routing-instances routing-instance-name bridge-domains bridge-domain-name]hierarchy level.
To configure DHCP relay to prevent DHCP spoofing:
You can explicitly enable and disable interface support for DHCP snooped clients. See Enabling and Disabling DHCP Snooped Packets Support for DHCP Relay Agent.
See Also
Change History Table
Feature support is determined by the platform and release you are using. Use Feature Explorer to determine if a feature is supported on your platform.
