Typical Network Use Cases
GBP is supported on different network topologies.
We support GBP on different topologies on IPv4 and IPv6 overlay networks, and on IPv4 (and IPv6 starting in Junos OS Release 25.4R1) underlay networks. Whether you're deploying a large campus network or a branch or small campus network, you can use GBP to provide a common microsegmentation solution.
GBP in Large Campus Networks
A large campus network is typically constructed as an IP Clos fabric consisting of an access layer, a distribution layer, and in the largest deployments, a distinct core layer. This arrangement allows high scale, non-blocking connectivity between end user devices. When coupled with an overlay technology such as EVPN-VXLAN, you can extend layer 2 connectivity across campus with no constraint on physical location while limiting excessive broadcasts and flooding.
EVPN-VXLAN delivers scalability and flexibility to your network by decoupling the virtual (overlay) topology from the physical (underlay) topology. This reduces operational overhead and time to deployment and increases portability. The IP Clos fabric provides the physical any-to-any connectivity while the EVPN-VXLAN network controls the virtual connectivity between end user equipment. More specifically, in the context of microsegmentation, EVPN-VXLAN allows you to extend Group Based Policies (GBP) to provide microsegmentation across the entire campus network.
The access switches act as VXLAN tunnel endpoints (VTEPs). On ingress, packets from the access link are encapsulated in VXLAN and forwarded through the appropriate tunnels. On egress, packets exiting from the VTEP are decapsulated and sent out the access link.
As the home to VTEPs, the access switches are perfectly positioned to support microsegmentation using GBP. The access switch classifies an incoming packet to obtain the GBP tag and inserts this tag into the VXLAN header prior to forwarding the VXLAN-encapsulated frame through the appropriate tunnel. The access switch at the remote end of the tunnel decapsulates the VXLAN-encapsulated frame and extracts the tag. The remote access switch can then use the local and remote tags to enforce policy.
This is shown in Figure 1.
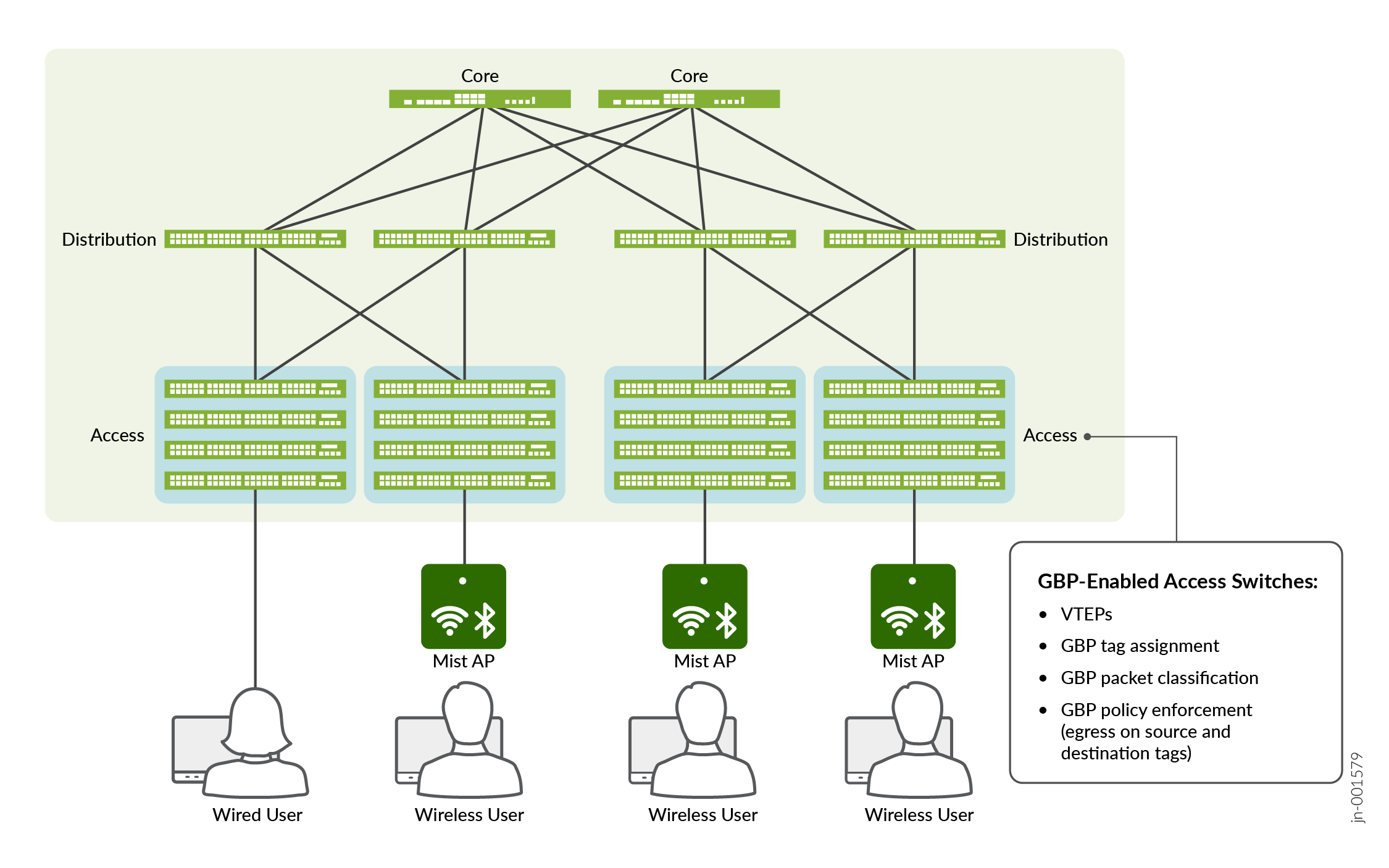
This type of architecture is ideal for large campus sites. By delegating all policy enforcement to the access switches, you can support layer 2 / layer 3 segmentation at scale. You enjoy the benefit of a fully-featured GBP microsegmentation solution on a highly scalable EVPN-VXLAN infrastructure.
While you can configure tag assignment using either the CLI or RADIUS authentication, using RADIUS authentication is the preferred approach for large networks. With RADIUS, you don't require prior knowledge of client networking configuration as you do for CLI. You simply configure your RADIUS server to offer the desired GBP tag to each client. The tag is conveyed in a special vendor-specific attribute (VSA) as part of authentication, compatible with any RADIUS server that supports VSAs. See Assigning Tags Using RADIUS for more information on the VSAs used for GBP configuration.
There are two situations to consider when assigning tags using RADIUS:
-
The client device is directly connected to the access switch. In this situation, the access switch acts as the authenticator and processes RADIUS messages to and from the authentication server. The access switch can therefore extract the assigned GBP tag from the authentication server's response and automatically configure it locally on the switch.
-
The client device connects to a wireless access point (AP). The wireless AP then connects to the access switch. In this situation, we can authenticate the AP as if it were a client device directly connected to the access switch. However, this only provides authentication (and GBP tag assignment) at the AP level, which means that all wireless clients of the AP are authenticated and grouped together.
In order to provide granularity down to the client level, we must perform authentication and assign GBP tags at the client level. In order to do this, the wireless AP must act as the authenticator, not the access switch. As the authenticator, the wireless AP has knowledge of the GBP tag assigned to each of its clients, but it needs a way to convey this tag to the upstream access switch.
Starting in Junos OS Release 25.4R1, if the wireless access point is a Mist AP, the Mist AP can use proprietary messaging to convey the assigned GBP tag to the upstream access switch. Upon receiving this notification, the access switch configures the assigned tag as if it were configured or learned locally. See Unified Access Policy for more information on this scenario.
GBP in Branch and Small Campus Networks
A branch or small campus environment may not have the infrastructure to run a full EVPN-VXLAN implementation. The network may simply consist of VLANs running on a collection of layer 2 switches. Fortunately, this does not preclude you from using Juniper's GBP solution to segment your network. Starting in Junos OS Release 25.4R1, Juniper's GBP solution can work (with some restrictions) in this type of pure layer 2 environment.
Figure 2 shows layer 2 access switches connected to external networks through a WAN router. You configure the access switches to assign GBP tags based on layer 2 fields. Since there is no VXLAN encapsulation or EVPN signaling, the assigned GBP tags are not propagated through the network. Policy enforcement, therefore, takes place purely using locally available layer 2 and layer 3 information at the ingress.
Even with this restriction, the ability to use GBP to segment traffic in small networks like this provides a lot of the same benefits that the full GBP solution offers: operational simplicity, consistent policy application, and high scalability.
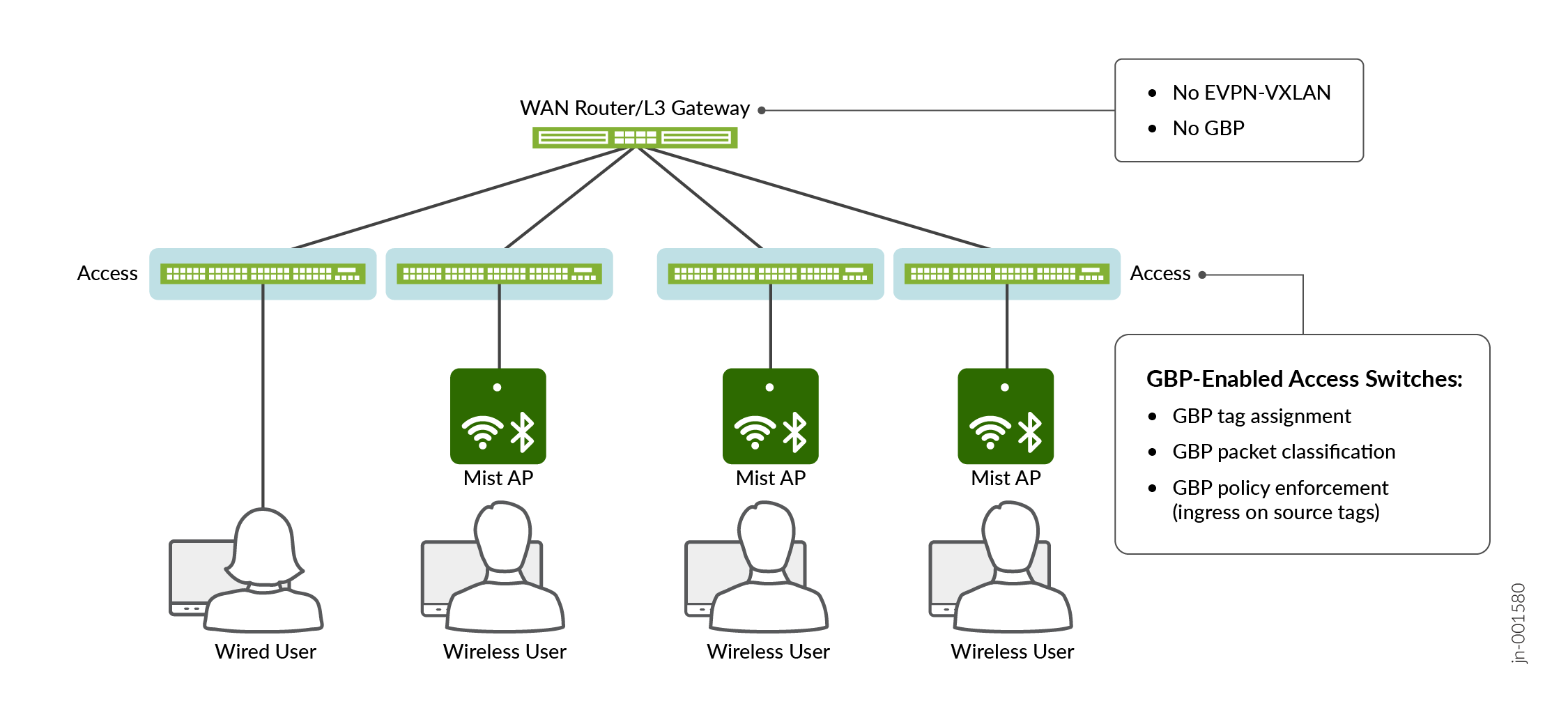
Similar to GBP in large campus networks, you configure tag assignment using the CLI or RADIUS authentication.
There are restrictions on what GBP microsegmentation filters you can configure using the CLI for this use case. See Using the GBP Pure L2 Profile for more details.
When using RADIUS authentication, the behavior is the same as for large campus networks:
-
The access switch acts as the authenticator for wired users and configures the tag assignment automatically when the wired user is authenticated.
-
The Mist AP acts as the authenticator for wireless users and notifies the access switch of the tag assignment using proprietary messaging. Upon receiving this notification, the access switch configures the tag assignment into its MAC address tables and internal data structures.
For more information on deploying GBP in branch and small campus networks, see Unified Access Policy.
