ON THIS PAGE
Create an SQS Queue and Configure S3 ObjectCreated Notifications
Finding the S3 Bucket that contains the Data that you want to Collect
Creating the SQS Queue that is used to Receive ObjectCreated Notifications
Creating an Identity and Access Management (IAM) User in the AWS Management Console
Amazon AWS S3 REST API Log Source Parameters for Amazon AWS Route 53 when using an SQS Queue
Configuring an Amazon AWS Route 53 Log Source by using an S3 Bucket with an SQS Queue
You can collect AWS Route 53 Resolver query logs from multiple accounts or regions in an Amazon S3 bucket. Configure a log source on the JSA Console so that Amazon AWS Route 53 can communicate with JSA by using the Amazon AWS S3 REST API protocol and a Simple Queue Service (SQS) queue.
Using the Amazon AWS S3 REST API protocol and a Simple Queue Service (SQS) queue instead of with a directory prefix has the following advantages:
-
You can use one log source for an S3 bucket, rather than one log source for each region and account.
-
There is a reduced chance of missing files because this method uses ObjectCreate notifications to determine when new files are ready.
-
It's easy to balance the load across multiple Event Collectors because the SQS queue supports connections from multiple clients.
-
Unlike the directory prefix method, the SQS queue method does not require that the file names in the folders be in a string that is sorted in ascending order based on the full path. File names from custom applications don't always conform to this method.
-
You can monitor the SQS queue and set up alerts if it gets over a certain number of records. These alerts provide information about whether JSA is either falling behind or not collecting events.
-
You can use IAM Role authentication with SQS, which is Amazon's best practice for security.
-
Certificate handling is improved with the SQS method and does not require the downloading of certificates to the Event Collector.
- Configure Resolver query logging. In Step 5 of that procedure , select S3 bucket as the destination for query logs.
- Create the SQS queue that is used to receive ObjectCreated notifications.
- Create an Amazon AWS Identity and Access Management (IAM) user and then apply the AmazonS3ReadOnlyAccess policy.
- Configure the security credentials for your AWS user account.
- Amazon AWS S3 REST API log source parameters for Amazon AWS Route 53 when using a SWS queue.
Configuring Resolver Query Logging
Create an SQS Queue and Configure S3 ObjectCreated Notifications
Before you can add a log source in JSA, you must create an SQS queue and configure S3 ObjectCreated notifications in the AWS Management Console when using the Amazon AWS S3 REST API protocol.
Complete the following procedures:
Finding the S3 Bucket that contains the Data that you want to Collect
You must find and note the region for S3 bucket that contains the data that you want to collect.
- Log in to the AWS Management Console as an administrator.
- Click Services, and then go to S3.
- From the AWS Region column in the Buckets list, note the region where the bucket that you want to collect data from is located. You need the region for the Region Name parameter value when you add a log source in JSA.
- Enable the check box beside the bucket name, and then from the panel that opens to the right, click Copy Bucket ARN to copy the value to the clipboard. Save this value or leave it on the clipboard. You need this value when you set up SQS queue permissions.
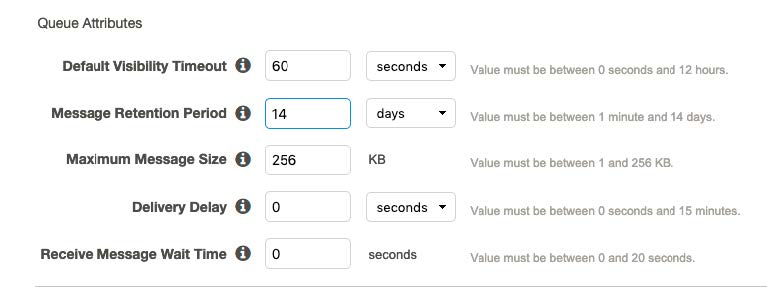
Creating the SQS Queue that is used to Receive ObjectCreated Notifications
You must create an SQS queue and configure S3 ObjectCreated notifications in the AWS Management Console when using the Amazon AWS S3 REST API protocol.
You must complete Finding the S3 Bucket that contains the data that you want to collect. The SQS Queue must be in the same region as the AWS S3 bucket that the queue is collecting from.
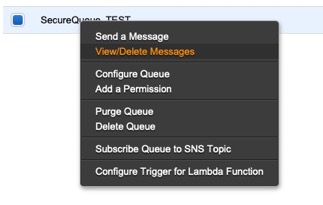
Setting up SQS Queue Permissions
You must set up SQS queue permissions for users to access the queue.
Before you begin
You must complete Creating the SQS queue that is used to receive ObjectCreated notifications.
You can set the SQS queue permissions by using either the Permissions Editor or a JSON policy document.
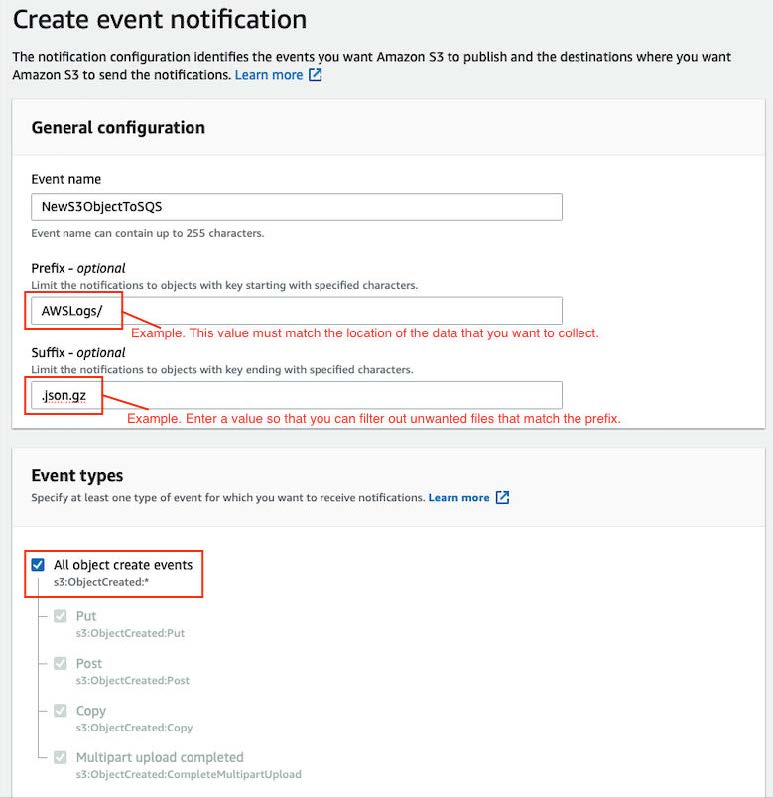
Creating ObjectCreated Notifications
Creating an Identity and Access Management (IAM) User in the AWS Management Console
An Amazon administrator must create a user and then apply the s3:listBucket and s3:getObject permissions to that user in the AWS Management Console. The JSA user can then create a log source in JSA.
The minimum required permissions are s3:listBucket and s3:getObject. You can assign other permissions to the user as needed.
Sample policy:
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "VisualEditor0",
"Effect": "Allow",
"Action": [
"s3:GetObject",
"s3:ListBucket"
],
"Resource": [
"arn:aws:s3:::<bucket_name>",
"arn:aws:s3:::<bucket_name>/AWSLogs/<AWS_account_number>/<DSM_name>/us-east-1/*"
]
}
]
}For more information about permissions that are related to bucket operations, go to the AWS documentation website.
- Log in to the AWS Management Console as an administrator.
- Click Services.
- From the list, select IAM.
- Click Users > Add user.
- Create an Amazon AWS IAM user and then apply the AmazonS3ReadOnlyAccess policy.
Configuring Security Credentials for your AWS User Account
Amazon AWS S3 REST API Log Source Parameters for Amazon AWS Route 53 when using an SQS Queue
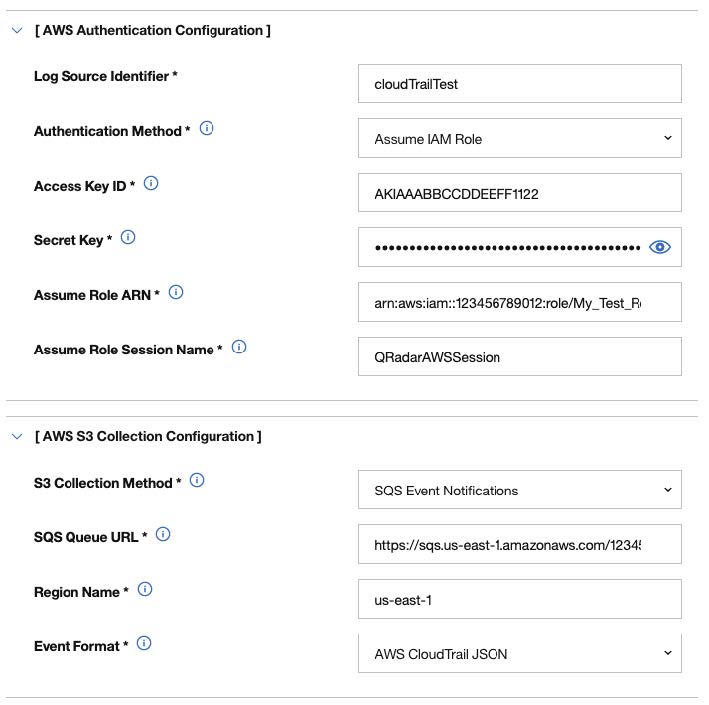
If you want to collect AWS Route 53 Resolver query logs from multiple accounts or regions in an Amazon S3 bucket, add an Amazon AWS Route 53 log source on the JSA Console by using the Amazon AWS S3 REST API protocol and a Simple Queue Service (SQS) queue.
The following table describes the parameters for an Amazon AWS Route 53 log source that uses the Amazon AWS S3 REST API protocol:
|
Parameter |
Value |
|---|---|
|
Log Source type |
Amazon AWS Route 53 |
|
Protocol Configuration |
Amazon AWS S3 REST API |
|
Log Source Identifier |
Type a unique name for the log source. The Log Source Identifier can be any valid value and does not need to reference a specific server. The Log Source Identifier can be the same value as the Log Source Name. If you have more than one Amazon AWS Route 53 log source that is configured, you might want to identify the first log source as awsroute53-1, the second log source as awsroute53-2, and the third log source as awsroute53-3. |
|
Authentication Method |
Access Key ID / Secret Key Standard authentication that can be used from anywhere. For more information about configuring security credentials, see Configuring security credentials for your AWS user account. Assume IAM Role Authenticate with keys and then temporarily assume a role for access. This option is available only when you use the SQS Event Notifications collection method. For more information about creating IAM users and assigning roles, see Creating an Identity and Access Management (IAM) user in the AWS Management Console. |
|
Access Key ID |
If you selected Access Key ID / Secret Key for the Authentication Method, the Access Key ID parameter is displayed. The Access Key ID that was generated when you configured the security credentials for your AWS user account. This value is also the Access Key ID that is used to access the AWS S3 bucket. |
|
Secret Key ID |
If you selected Access Key ID / Secret Key for the Authentication Method, the Secret Key ID parameter is displayed. The Secret Key that was generated when you configured the security credentials for your AWS user account. This value is also the Decret Key ID that is used to access the AWS S3 bucket. |
|
Event Format |
Select LINEBYLINE. The log source collects JSON formatted events. |
|
S3 Collection Method |
Select SQS Event Notifications. |
|
SQS Queue URL |
Enter the full URL, starting with https://, of the SQS queue that is set up to receive notifications for ObjectCreate events from S3. |
|
Region Name |
The region that the SQS Queue or the S3 Bucket is in. Example: us-east-1, eu-west-1, ap-northeast-3 |
|
Use as a Gateway Log Source |
Select this option for the collected events to flow through the JSA traffic analysis engine and for JSA to automatically detect one or more log sources. |
|
Log Source Identifier Pattern |
This option is available when Use as a Gateway Log Source is set to yes. Use this option if you want to define a custom Log Source Identifier for events being processed. This field accepts key value pairs to define the custom Log Source Identifier, where the key is the Identifier Format String, and the value is the associated regex pattern. You can define multiple key value pairs by entering a pattern on a new line. When multiple patterns are used, they are evaluated in order until a match is found and a custom Log Source Identifier can be returned. |
|
Show Advanced Options |
Select this option if you want to customize the event data. |
|
File Pattern |
This option is available when you set Show Advanced Options to Yes. Type a regex for the file pattern that matches the files that you want to pull; for example, .*? \.json\.gz |
|
Local Directory |
This option is available when you set Show Advanced Options to Yes. The local directory on the Target Event Collector. The directory must exist before the AWS S3 REST API PROTOCOL attempts to retrieve events. |
|
S3 Endpoint URL |
This option is available when you set Show Advanced Options to Yes. The endpoint URL that is used to query the AWS REST API. If your endpoint URL is different from the default, type your endpoint URL. The default is http:/s3.amazonaws.com |
|
Use S3 Path-Style Access |
Forces S3 requests to use path-style access. This method is deprecated by AWS. However, it might be required when you use other S3 compatible APIs. For example, the https://s3.region.amazonaws.com/bucket-name/key- name path-style is automatically used when a bucket name contains a period (.). Therefore, this option is not required, but can be used. |
|
Use Proxy |
If JSA accesses the Amazon Web Service by using a proxy, enable Use Proxy. If the proxy requires authentication, configure the Proxy Server, Proxy Port, Proxy Username, and Proxy Password fields. If the proxy does not require authentication, configure the Proxy IP or Hostname field. |
|
Recurrence |
How often a poll is made to scan for new data. When using the SQS event collection method, SQS Event Notifications can have a minimum value of 10 (seconds). Because SQS Queue polling can occur more often, a lower value can be used. Type a time interval to determine how frequently the poll is made for new data. The time interval can include values in hours (H), minutes (M), or days (D). For example, 2H = 2 hours, 15M = 15 minutes, 30 = seconds. |
|
EPS Throttle |
The maximum number of events per second that are sent to the flow pipeline. The default is 5000. Ensure that the EPS Throttle value is higher than the incoming rate or data processing might fall behind. |
For more information about the Amazon AWS S3 REST API protocol, see Amazon AWS S3 REST API Protocol Configuration Options.