cSRX in Bare-Metal Linux Server
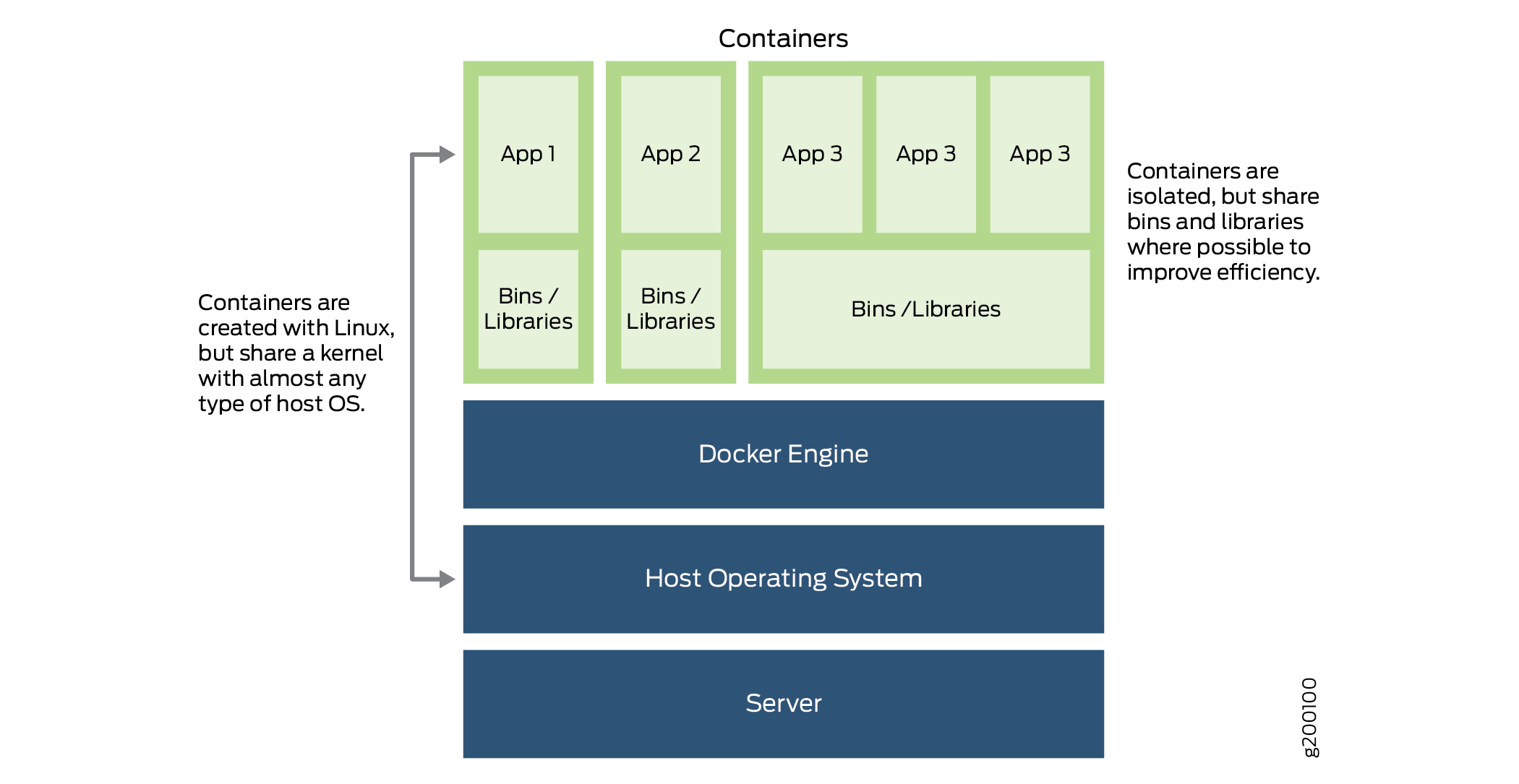
The cSRX Container Firewall is a containerized version of the SRX Series Firewall with a low memory footprint. cSRX is built on the the Junos® operating system (Junos OS) and delivers networking and security features similar to those available on the software releases for the SRX Series. cSRX provides advanced security services, including content security, AppSecure, and Content Security in a container form factor. A bare-metal Linux server uses a Docker container to allow the cSRX Container Firewall to substantially reduce overhead. This efficiency occurs because each container shares the Linux host's OS kernel. Regardless of the number of containers a Linux server hosts, only one OS instance can be in use. Also, because of the light weight of the containers, a server can host many more container instances than that by virtual machines (VMs), yielding tremendous improvements in utilization. With its small footprint and Docker as a container management system, the cSRX enables deployment of agile, high-density security service.
The cSRX enables you to quickly introduce new firewall services, customize services as per your requirements, and scale security services based on dynamic needs. The cSRX differs from VMs in several aspects. The cSRX does not require a guest OS to operate. It has a notably smaller memory footprint and is easier to migrate or download. The cSRX does not require a guest OS to operate. It has a notably smaller memory footprint and is easier to migrate or download. The boot time is reduced from several minutes with a VM-based environment to less than a few seconds with the cSRX container. The cSRX is ideal for public, private, and hybrid cloud environments.
Overview
The cSRX runs as a single container on a Linux bare-metal server which serves as the hosting platform for the Docker container environment. The cSRX container packages comprises all of the dependent processes (daemons) and libraries to support the different Linux host distribution methods (Ubuntu, Red Hat Enterprise Linux, or CentOS). You can use standard Docker commands to manage the cSRX container.
When the cSRX becomes active, several daemons inside the Docker container launch automatically. Some daemons support Linux features, providing the same services that they provide when running on a Linux host (for example,sshd, rsyslogd, and monit). You can compile and port other daemons from Junos OS to perform configuration and control jobs for security service (for example, and so on). SRX PFE is the data-plane daemon that receives and sends packets from the revenue ports of a cSRX container. The cSRX uses srxpfe for Layer 2 to Layer 3 forwarding functions (secure-wire forwarding or static routing forwarding) as well as for Layer 4 through Layer7 network security services.
The cSRX enables advanced security at the network edge in a multitenant virtualized environment. cSRX provides Layer 4 through Layer 7 advanced security features such as firewall, IPS and AppSecure. When cSRX in Layer 2 secure wire mode, incoming Layer 2 frames from one interface go through Layer 4 through Layer 7 processing based on the configured cSRX services. cSRX then sends the frames out of the other interface.
Launch the cSRX instance in secure-wire mode using the following command:
root@csrx-ubuntu3:~/csrx# docker run -d --privileged
--network=mgt_bridge -e CSRX_FORWARD_MODE="wire" --name=<csrx-container-name> <csrx-image-name>
As part of your Docker container configuration, you must connect the cSRX container to three virtual networks: one virtual network for out-of-band management sessions and two to receive and transmit data traffic. See Install cSRX in Bare-Metal Linux Server.
Figure 1 illustrates the cSRX operation in a secure-wire mode. It is an example of how a cSRX container is bridged with an external network. In this illustration, cSRX eth1 is bridged with host physical NIC eth1 and cSRX eth2 is bridged with host physical NIC eth2.
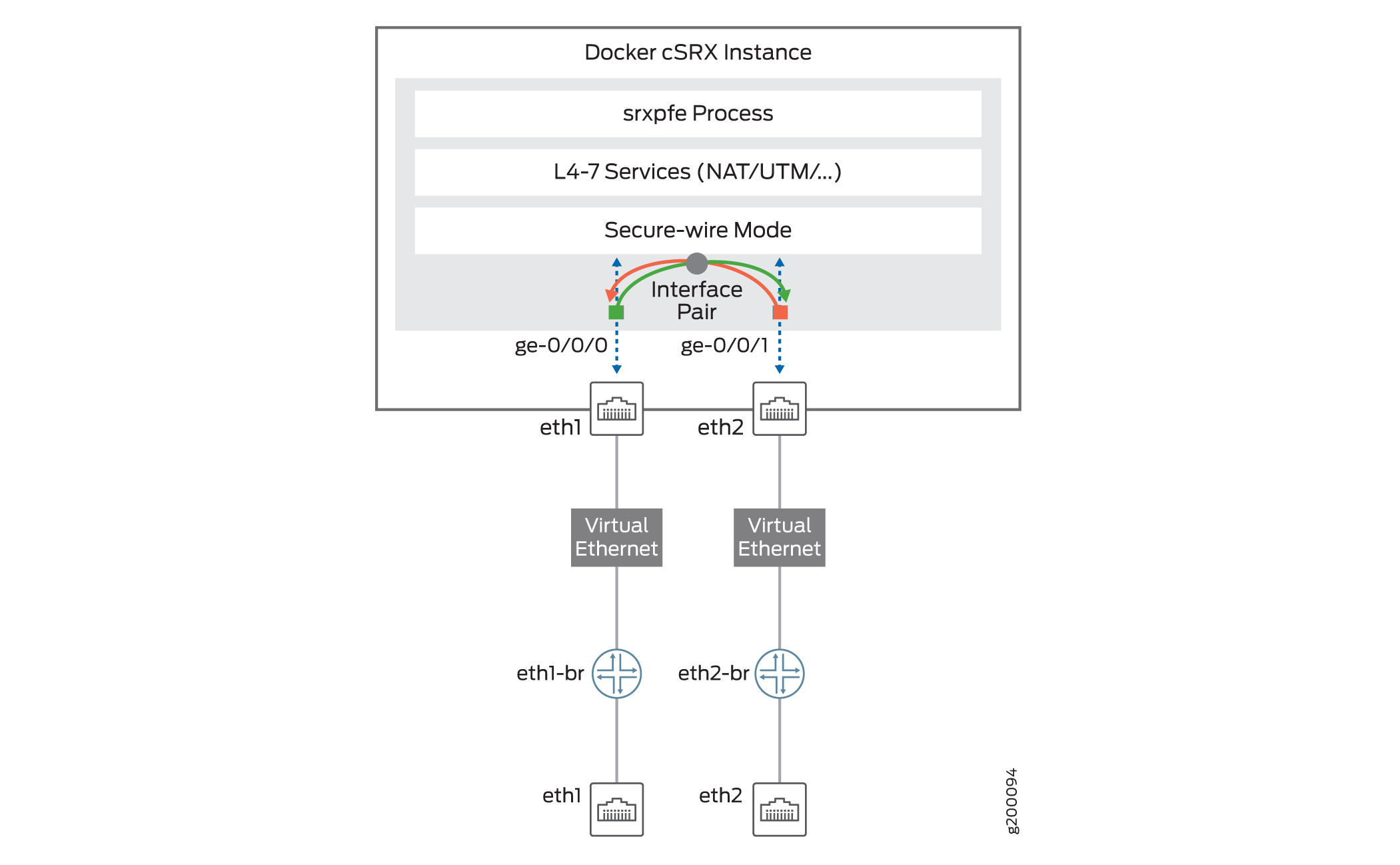
Figure 2 illustrates the cSRX operating in routing mode.
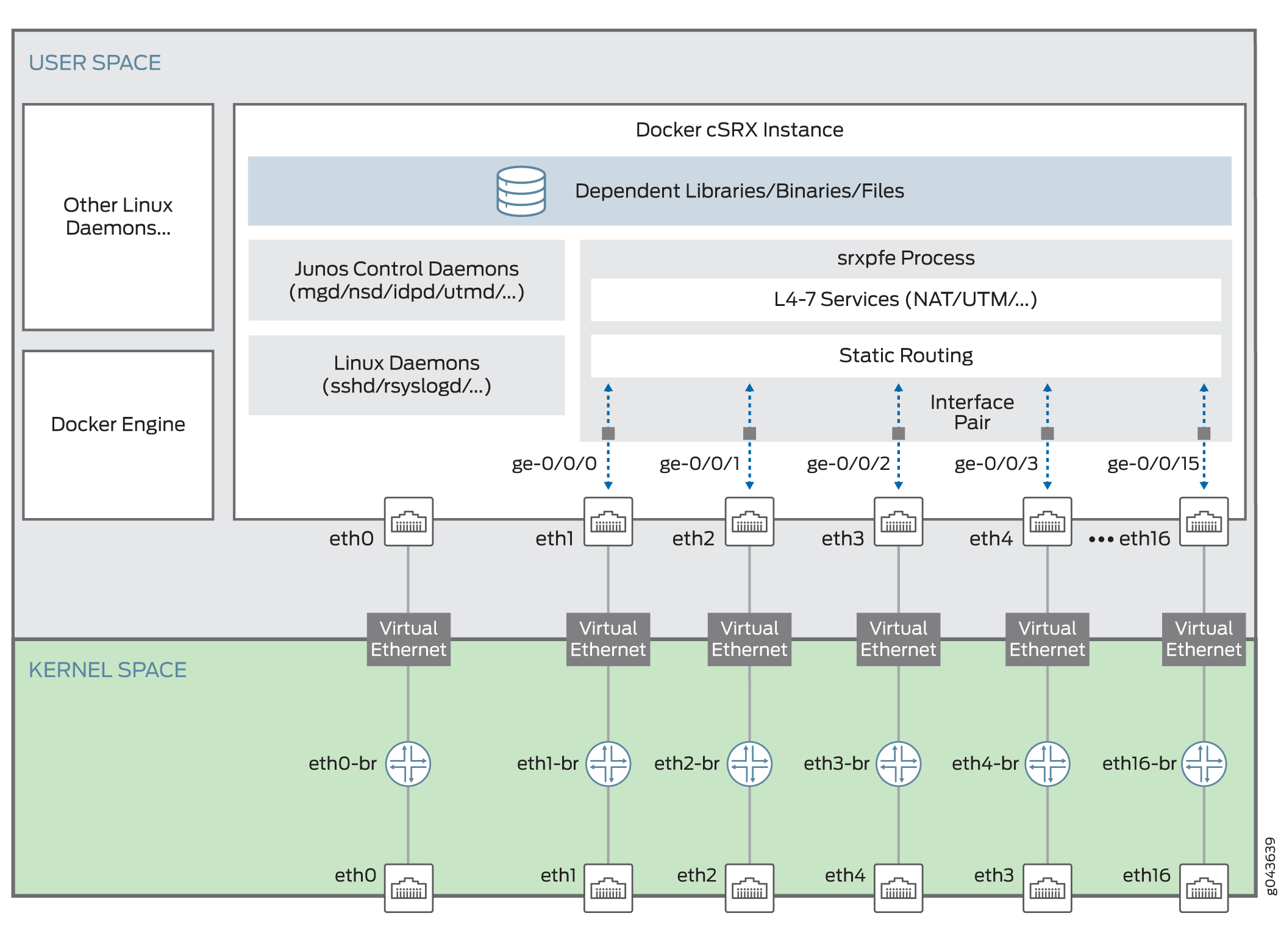
Starting in Junos OS Release 19.2R1, in routing mode, with the increase in the number of supported interfaces, the mapping of ge interfaces are reordered as:
Prior to Junos OS Release 19.2R1, in routing mode, eth0 was mapped as out-of-band management interface—eth1 as ge-0/0/1 and eth2 as ge-0/0/0.
Starting in Junos OS Release 19.2R1, in routing mode, the default number of interfaces supported are 3 and the maximum number of interfaces supported are 17 (1 management interface and 16 data interfaces). With this increase in the number of interfaces supported, the mapping of ge interfaces is reordered as:
eth0 - out-of-band management interface
eth1 - ge-0/0/0
eth2 - ge-0/0/1
eth3 - ge-0/0/2
eth4 - ge-0/0/3 and so on
cSRX Container Firewall Benefits and Uses
Some of the key benefits of cSRX Container Firewall in a containerized private or public cloud multitenant environment include:
Stateful firewall protection at the tenant edge.
Faster deployment of containerized firewall services into new sites.
With a small footprint and minimum resource reservation requirements, the cSRX can easily scale to keep up with customers’ peak demand.
Provides significantly higher density without requiring resource reservation on the host than what is offered by VM-based firewall solutions.
Flexibility to run on a bare-metal Linux server or Juniper Networks Contrail.
In the Contrail Networking cloud platform, cSRX can be used to provide differentiated Layer 4 through 7 security services for multiple tenants as part of a service chain.
With the Contrail orchestrator, cSRX can be deployed as a large scale security service.
Application security features (including IPS and AppSecure).
Content Security features (including antispam, Sophos Antivirus, web filtering, and content filtering).
Authentication and integrated user firewall features.
While the security services features between cSRX and vSRX Virtual Firewall are similar, there are scenarios in which each product is the optimal option in your environment. For example, the cSRX does not support routing instances and protocols, switching features, MPLS LSPs and MPLS applications, chassis cluster, and software upgrade features. For environments that require routing or switching, a vSRX Virtual Firewall VM provides the best feature set. For environments focused on security services in a Docker containerized deployment, cSRX is a better fit.
See Supported SRX Series Firewall Features on cSRX Container Firewall for a summary of the feature categories supported on cSRX, and also for a summary of features not supported on cSRX.
You can deploy the cSRX in the following scenarios:
Cloud CPE–For service providers (SPs) and managed security service providers (MSSPs) where there is a large subscriber base of branch offices or residential subscribers. MSSPs can offer differentiated services to individual subscribers.
Contrail microsegmentation–Within a Contrail environment running mixed workloads of VMs and containers, cSRX can provide security for Layer 4 through 7 traffic, managed by Security Director.
Private clouds–cSRX can provide security services in a private cloud running containerized workloads and can include Contrail integration.
Docker Overview
Docker is an open-source software platform that simplifies the creation, management, and teardown of a virtual container that can run on any Linux server. A Docker container packages applications in “containers” making them portable among any system running the Linux OS.
Figure 3 provides an overview of a typical Docker container environment.
cSRX Container Firewall Scale-Up Performance
You can scale the performance and capacity of a cSRX Container Firewall container by increasing the allocated amount of virtual memory or the number of flow sessions. Table 1 shows the cSRX scale-up performance applied to a cSRX container based on its supported sizes. The default size for a cSRX container is large.
See Changing the Size of a cSRX Container for the procedure on how to scale the performance and capacity of a cSRX container by changing the container size.
|
cSRX Container Firewall Size |
Specification |
Junos OS Release Introduced |
|---|---|---|
| vCPUs/Memory |
2 vCPU / 4 GB RAM |
Junos OS Release 23.2R1 |
|
4 vCPU / 8 GB RAM |
||
|
6 vCPU / 12 GB RAM |
||
|
8 vCPU / 16 GB RAM |
||
|
12 vCPU / 24 GB RAM |
||
|
16 vCPU / 32 GB RAM |
||
|
20 vCPU / 48 GB RAM |
||
|
32 vCPU / 64 GB RAM |
