What is unified threat management?
What is unified threat management?
Originally called unified threat management (UTM), these capabilities better known as a Next-Generation Firewall (NGFW) today, provide multiple security features and services in a single device or service on the network, protecting users from security threats in a simplified way. NGFW includes functions such as anti-virus, anti-spam, content filtering, and web filtering.
How Does NGFW Protect Users and Networks?
IT teams are constantly faced with the challenge of protecting their companies’ productivity and digital assets against evolving and sophisticated threats, including spam and phishing attacks, viruses, trojans and spyware infected files, unapproved website access, and unapproved content. They have to address these challenges with limited budgets and resources. Having multiple separate devices, each designed to perform a specialized function such as spam filtering, web content filtering, or antivirus protection does not make this task easier. Rather, it adds to the cost and complexity of managing multiple boxes and multiple operating systems.
An NGFW is a single system that provides the answer to all of these challenges and more:
- It secures the network from viruses, malware, or malicious attachments by scanning the incoming data using Deep Packet Inspection.
- It prevents attacks before they enter the network by inspecting the packet headers.
- It prevents access to unwanted websites by installing enhanced web filtering.
- It provides ability to update automatically with the latest security updates, anti-virus definitions, and new features so that minimal manual intervention is required beyond initial set-up.
- It enables administrators to manage a wide range of security functions with a single management console.
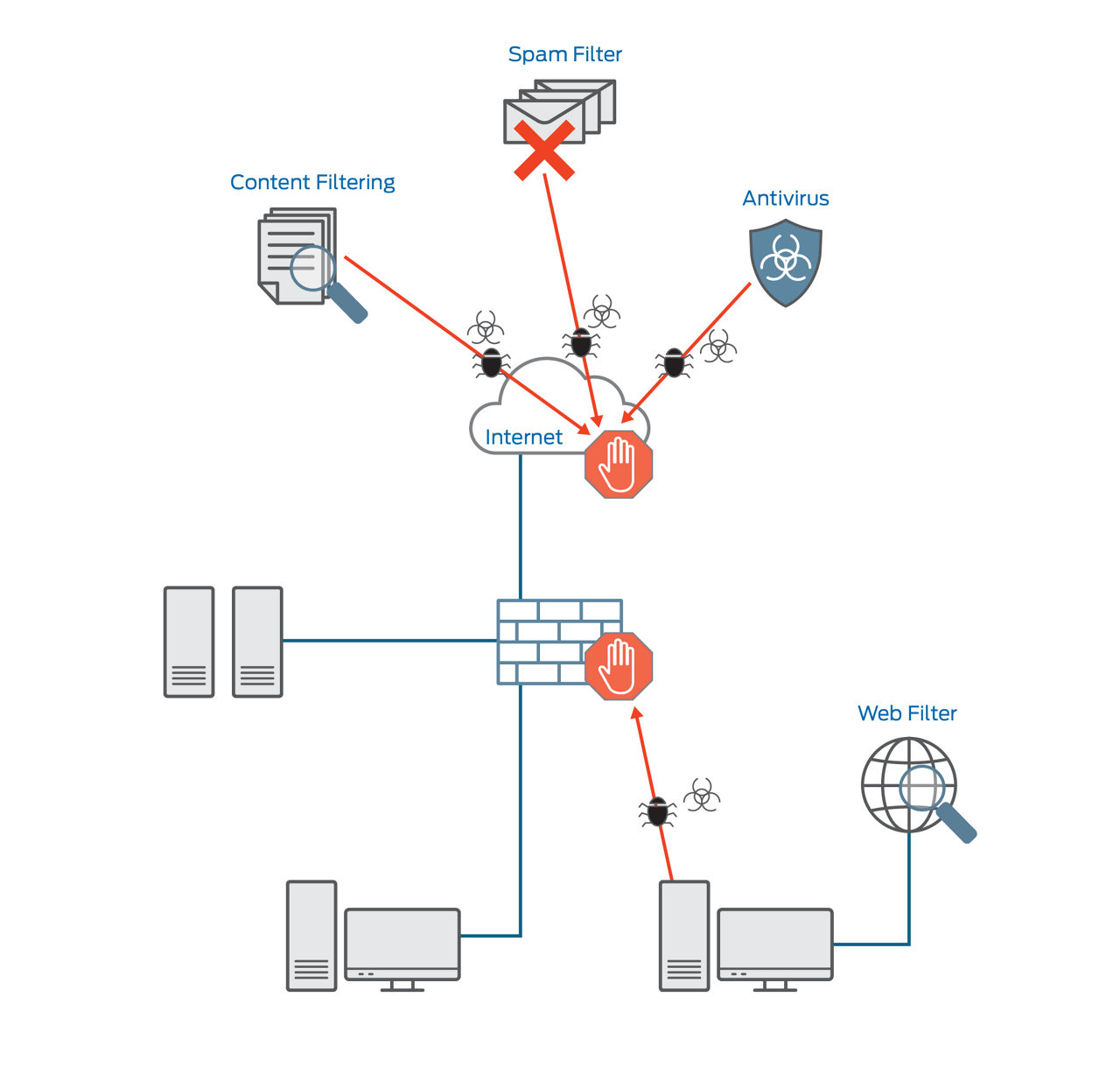
Figure 1: NGFW Deployment in Network
Juniper Networks Implementation
SRX Series Next-Generation Firewalls and the vSRX Virtual Firewall include best-in-class content security against malware, viruses, phishing attacks, intrusion attempts, spam, and other threats through unified threat management, protecting against network-level attacks, application-level attacks, and content-based attacks. The components provided in various NGFW systems include:
- Anti-spam – Tags or blocks unwanted e-mail traffic by scanning inbound and outbound SMTP e-mail traffic. Antispam filtering allows you to use both a third-party server-based spam block list (SBL) and to optionally create your own local whitelists and blacklists for filtering against e-mail messages.
- Anti-virus – Uses a scanning engine and virus signature databases to protect against virus-infected files, worms, trojans, spyware, and other malware over POP3 HTTP, SMTP, IMAP, and FTP protocols. By using Juniper Advanced Threat Prevention (ATP), you can combine traditional signature-based detection with latest anti-malware technologies to detect threats and mitigate them.
- Content Filtering – Provides basic data loss prevention functionality. Content filtering filters traffic based on MIME type, file extension, and protocol commands. You can also use the content filter module to block ActiveX, Java Applets, and other types of content. Content filtering does not require a separate license.
- Web Filtering – Provides URL filtering capability by using either a local Websense server or Internet-based SurfControl server. Web filtering is critical as a service for tracking productivity and corporate user behavior.

