ON THIS PAGE
Overview
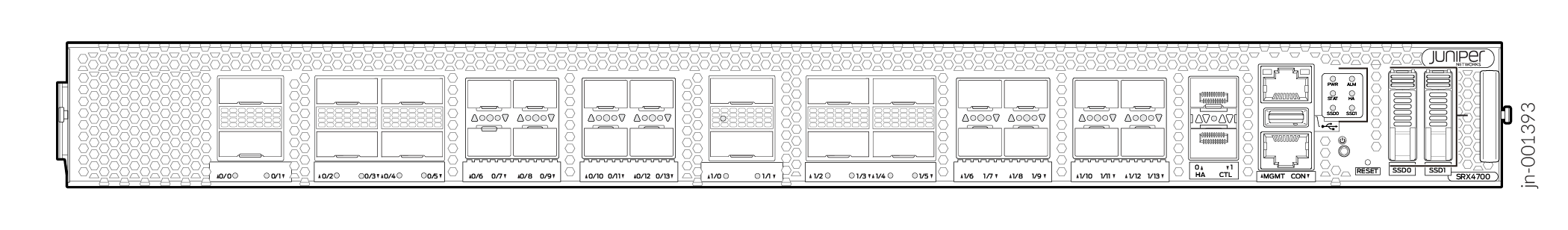
This topic provides a high-level overview of the SRX4700 Firewall, including its hardware and software architecture, market positioning, and key features designed for modern data centers, cloud environments, and service provider networks.
The Juniper Networks® SRX4700 Firewall is a high-performance firewall designed for service providers, cloud providers, and large enterprises that require high throughput in a compact 1-U form factor. In addition, enterprises can deploy the SRX4700 as data center core and edge firewalls, and as a secure SD-WAN hub.
The SRX4700 is a compact, power-efficient 1 rack unit (1-U) solution that delivers exceptional performance with up to 1.4-Tbps firewall throughput.
The SRX4700 supports two 400-Gbps interfaces with wire-speed MACsec for robust data protection and two field-replaceable solid-state drives (SSDs): a 1-TB SSD and a 2-TB SSD.
You must install the 1-TB SSD in slot SSD0 (primary slot) and the 2-TB SSD in slot SSD1 (secondary slot).
SSD0 and SSD1 are not interchangeable. SSD0 slot can only house 1-TB drive and SSD1 can only house 2-TB drive.
SSD0 (1 TB) is the primary boot device, containing the factory-default Junos OS image and configuration. SSD1 (2 TB) provides additional storage capacity, with both SSDs functioning as part of the integrated storage system. You can synchronize Junos OS images and configurations between SSD0 and SSD1.
Combining networking and security, the SRX4700 integrates zero trust capabilities, EVPN-VXLAN, and AI Predictive Threat Prevention for advanced threat detection. It also offers high-performance IPsec VPN, carrier-grade NAT, and unified policy management. These features ensure a cost-effective, reliable, and efficient security posture for modern data centers and enterprise networks.
The SRX4700 Firewall is powered by Junos® OS and incorporates the following security services and networking functions.
These advanced functionalities collectively contribute to the operational efficiency and scalability required to meet the evolving demands of enterprise networks and data centers.
SRX4700 Key Features
-
Integration with the Junos OS—Integrates multiple security services and networking functions on top of Junos OS, providing highly customizable threat protection, automation, and integration capabilities.
-
Scalable architecture—Supports active/active and active/backup deployment scenarios, providing cost-effective security in a compact, scalable 1-U form factor.
-
Distributed security services architecture—Juniper integrates the SRX4700 into its Connected Security Distributed Services (CSDS) architecture, enabling the firewall to scale horizontally by creating a logical firewall across multiple SRX Series Firewalls. This architecture supports enhanced operational scalability, simplicity, reliability, and costs effectiveness. See Connected Security Distributed Services Architecture documentation and Connected Security Distributed Services (CSDS) Architecture Datasheet.
- Juniper Secure Access Service Edge (SASE) integration—The SRX4700 supports setups with Juniper Security Director Cloud, a solution enabling the integration of SASE architecture. This integration is especially useful for organizations migrating to distributed secure service environments.
-
High firewall throughput—Delivers the industry's highest firewall throughput per rack unit, up to 1.4 Tbps, and supports 400 Gbps interfaces and a combination of 100 G and 50 G ports with wire speed MACsec.
It features total onboard ports including 2x400GbE (QSFP56-DD), 10x100GbE (QSFP28), and 16x50GbE (SFP56), enabling flexible, high-density deployments.
-
Zero trust security—Provides built-in zero trust security, ensuring that all traffic is treated as untrusted until verified.
-
Advanced Threat Prevention (ATP)—Features AI Predictive Threat Prevention, which keeps known and zero-day threats off the network at line rate for the entire attack life cycle, ensuring that the network stays safe from initial and subsequent attacks.
-
Intrusion detection and prevention (IDP)—Includes IDP capabilities, which have been proven effective in objective third-party tests by CyberRatings.org to protect users and Layer 7 applications.
-
VPN performance—It offers high-performance IPsec VPN with dedicated crypto engines, providing diverse VPN options for various network designs, including remote access and dynamic site-to-site communications. Its 500 Gbps Inline IPsec high speed function offers an ASIC based acceleration for IPsec VPN traffic using AES-GCM-128 or 256 bits.
-
Follow-the-user and follow-the-application access—Supports follow-the-user and follow-the-application access, ensuring that security policies follow users and devices wherever they go.
-
Security Technologies—It incorporates three key security technologies: Trusted Platform Module (TPM) 2.0, Device Identity (DevID), and secure zero-touch provisioning (SZTP) capabilities that work together to establish zero trust device authentication.
-
Trusted Platform Module (TPM) 2.0—It features an embedded TPM 2.0 chip, a secure crypto-processor designed to provide hardware-based security functions. The TPM serves as a secure storage location for cryptographic keys and certificates, protecting sensitive data from unauthorized access. This hardware-based approach ensures that security credentials remain isolated from the main OS.
-
Device Identifier or Digital Device ID (DevID)—Features a unique, cryptographically signed 802.1AR-standard device identity (DevID) stored in Trusted Platform Module (TPM) 2.0, mitigation the risk of supply chain attacks.
-
Secure zero-touch provisioning (SZTP)—It supports RFC-compliant SZTP to enable efficient remote deployment. SZTP uses the DevID embedded in the TPM 2.0 to generate a unique digital voucher that enables mutual authentication between the bootstrap server and the device before initiating provisioning. This approach allows secure, remote deployment without manual intervention while maintaining cryptographic verification of device authenticity.
-
-
Layer 4 (L4) through Layer 7 (L7) services—Provides line-rate hardware acceleration for L4 through L7 services, including IDP, application ID, stateful firewall, and Network Address Translation (NAT), with no performance or security trade-offs.
-
Advanced features for AI workloads—The SRX4700 supports EVPN-VXLAN (EVPN Type 5 routes) for secure fabric integration in spine-leaf data centers, enabling Layer 4-7 security on VXLAN encapsulated traffic to protect high-scale workloads such as AI-generated east-west traffic.
SRX4700 Positioning
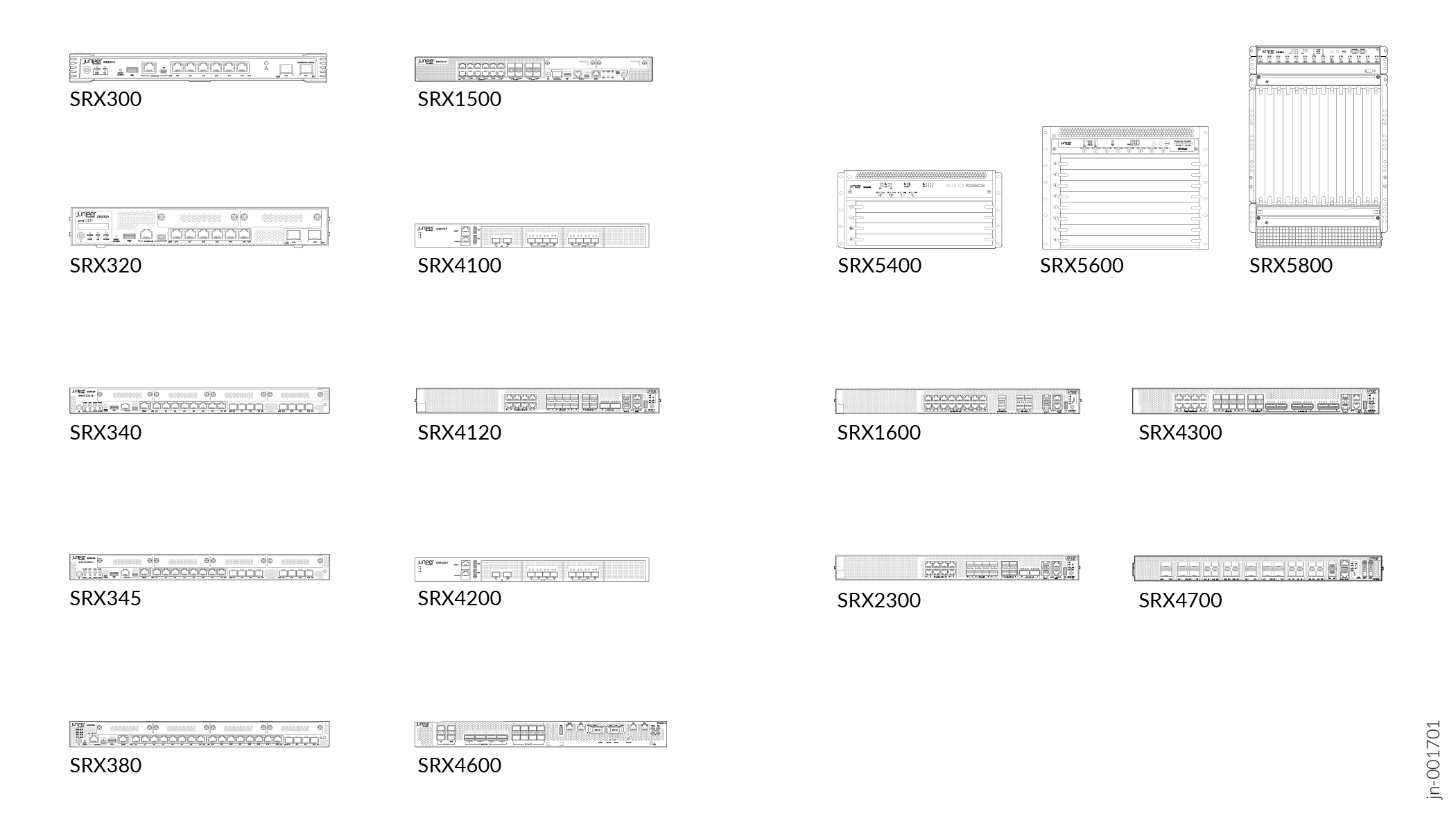
The SRX4700 Firewall represents Juniper’s next‑generation refresh of the SRX4600 platform, delivering a major advancement in performance, security, and operational efficiency.
For more information, see Juniper SRX Series Firewalls
SRX4700 Firewall addresses the following needs:
- Significant uplifts in firewall performance to support rapidly increasing traffic volumes.
- Enhanced cryptographic capabilities with improved IPsec and SSL Proxy scalability and a higher setup rate.
- Increased computing capacity to power advanced security services and future growth.
The SRX4700 offers the following key market positioning elements:
-
Performance—The SRX4700 Firewall emphasizes its leadership in high-density, secure throughput for demanding environments.
-
Target use cases—The SRX4700 Firewall is optimized for a broad range of deployment scenarios, including:
-
Service provider mobile core and RAN environments
-
Cloud provider infrastructure protection
-
Secure SD‑WAN hub deployments
-
Data center core and edge firewall use cases requiring high scalability and versatility
Table 1: Data Center Use Cases Use Case Description Benefits Data center WAN gateway Data center access protection, north-south traffic - Enforces legitimate data center access
- Stops threats from entering the data center
- Aligns data center security policies with user access policies
- Provides security without sacrificing performance
Intra-data center firewall East-west traffic and segmentation - Allows microsegmentation between servers
- Stops lateral movement
- Enforces legitimate data movement between applications
- Supports and manages modern applications easily
- Reduces complexity and operations
-
Integrates with EVPN-VXLAN fabric and performs east-west security policy enforcement
Cloud and Data Center Interconnect Application connectivity and data exchange - Scales secure data transactions from cloud to cloud
- Prevents threats from moving between data center locations
- Reduces downtime
Public cloud Application access and data exchange - Scales security across any and all clouds
- Automates changing application security requirements
- Seamlessly migrates to a new infrastructure
- Minimizes time-consuming tasks and misconfigurations
-
-
Advanced security architecture—Delivers predictable high-performance security processing with consistent throughput across L4 through L7 services through its flow-based processing, hardware acceleration, and integration with Juniper's Connected Security Distributed Services (CSDS) architecture.
-
Modern fabric integration—Integrates seamlessly into modern automated data center fabrics, operating as a secure, fabric‑aware leaf in spine‑leaf architectures.
-
Security effectiveness—Provides high exploit protection with zero false positives, ensuring consistent security results.
