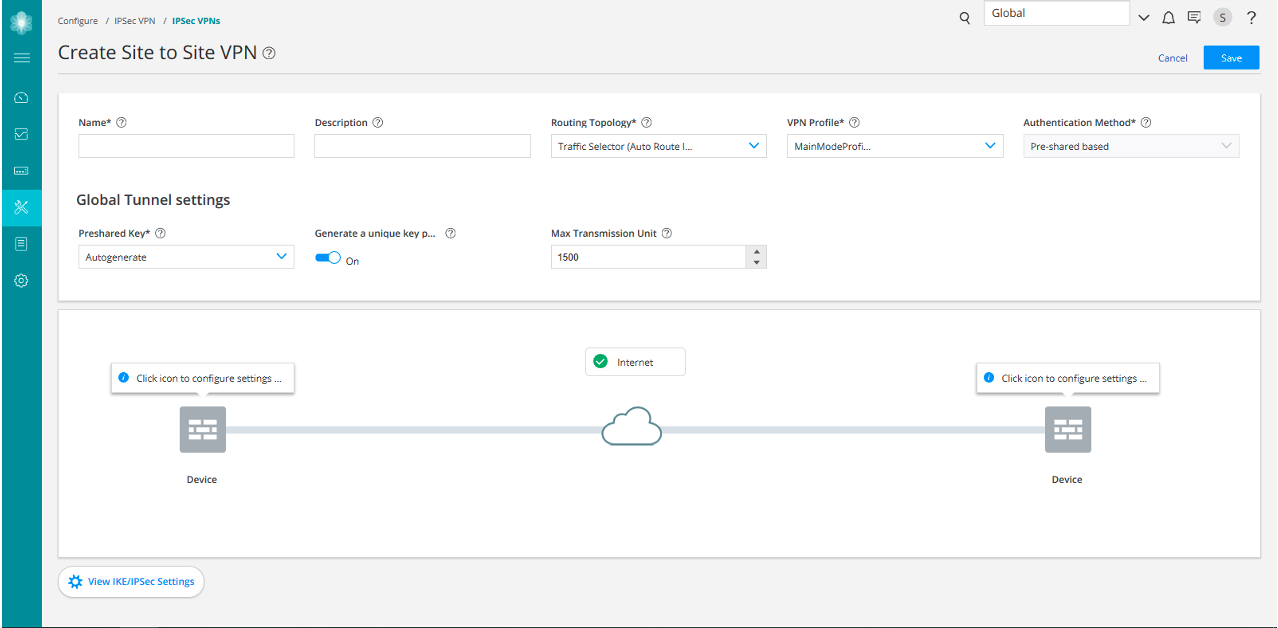
Create a Site-to-Site VPN
Before You Begin
-
Read the IPsec VPN Overview topic.
-
Review the IPsec VPN main page for an understanding of your current data set. See IPsec VPN Main Page Fields for field descriptions.
-
Create addresses and address sets. See Creating Addresses and Address Groups.
-
Create VPN profiles. See Creating VPN Profiles.
-
Define extranet devices. See Creating Extranet Devices.
A site-to-site VPN connects two sites in an organization and allows secure communications between the sites.
To configure a site-to-site VPN:
|
Settings |
Guidelines |
|---|---|
|
Name |
Enter a unique string of alphanumeric characters, colons, periods, dashes, and underscores; spaces are not allowed; maximum length is 62 characters. |
|
Description |
Enter a description for the VPN; maximum length is 255 characters. |
|
Routing Topology |
Select one of the following options:
Note:
Routing Topology is applicable only for Route-based VPNs. |
|
VPN Profile |
Select a VPN profile from the drop-down list based on the deployment scenario. Default profile is applicable to a particular IPsec VPN only. You can view and edit the details by clicking View IKE/IPsec settings on the Create VPN page. Shared profile can be used by one or more IPsec VPNs. You can only view the details of the shared profiles by clicking View IKE/IPsec settings. If you select the VPN Profile value as Default, then while saving the IPsec VPN, you can choose to save the new profile as either VPN specific or shared. If you are saving it as shared, then the profile will be listed on the VPN Profiles page. |
|
Authentication Method |
Select an authentication method from the list that the device uses to authenticate the source of Internet Key Exchange (IKE) messages.
|
| Global Tunnel Settings | |
|
Pre-shared Key |
Establish a VPN connection using pre-shared keys, which is essentially a password that is same for both parties. Pre-shared keys are commonly deployed for site-to-site IPsec VPNs, either within a single organization or between different organizations. Select the type of pre-shared key you want to use:
Note:
This is applicable only if the authentication method is pre-shared based. |
|
Network IP |
Enter the IP address of the numbered tunnel interface. This is the subnet address from where the IP address is automatically assigned for tunnel interfaces. |
|
Max Transmission Unit |
Select the maximum transmission unit (MTU) in bytes. This defines the maximum size of an IP packet, including the IPsec overhead. You can specify the MTU value for the tunnel endpoint. The valid range is 68 to 9192 bytes. The default value is 1500 bytes. |
|
Settings |
Guidelines |
|---|---|
|
Endpoint |
Select either Devices or Extranet devices as endpoints. Note:
To add extranet devices inline, click Add Extranet Devices. |
|
Available |
View all devices from the current and child domains, with view parent enabled. Devices from the child domain with view parent disabled are not shown. You can select a device and add it as an endpoint. The following filter criteria are applied for the device selection:
|
|
Settings |
Guidelines |
|---|---|
|
External Interface |
Select the outgoing interface for IKE security associations (SAs). |
|
Tunnel Zone |
Select the tunnel zone. They are logical areas of address space that can support dynamic IP (DIP) address pools for NAT applications to pre and post-encapsulated IPsec traffic. Tunnel zones also provide great flexibility in combining tunnel interfaces with VPN tunnels. Note:
This is applicable for only route-based site-to-site VPN. |
|
Routing instance |
Select the required routing instance. Note:
This is applicable for only route-based site-to-site VPN. |
|
Initiator/Recipient |
Select an option:
Note:
This is applicable when the VPN profile is Aggressive Mode profile. |
|
Certificate |
Select a certificate to authenticate the virtual private network (VPN) initiator and recipient. This is applicable in one of the following scenarios:
|
|
Trusted CA/Group |
Select the certificate authority (CA) profile from the list to associate it with the local certificate. This is applicable in one of the following scenarios:
|
|
Export |
|
|
OSPF Area |
Select an OSPF area ID within the range of 0 to 4,294,967,295, where the tunnel interfaces of this VPN need to be configured. Note:
This is applicable when the routing topology is OSPF-Dynamic Routing in route-based site-to-site VPN. |
|
Max Retransmission Time |
Select the retransmission timer to limit the number of times the RIP demand circuit re-sends update messages to an unresponsive peer. If the configured retransmission threshold is reached, routes from the next-hop router are marked as unreachable and the hold-down timer starts. You must configure a pair of RIP demand circuits for this timer to take effect. The retransmission range is from 5 through 180 seconds and the default value is 50 seconds. Note:
This is applicable only when routing topology is RIP-Dynamic Routing in route-based site-to-site VPN. |
|
AS Number |
Select a unique number to assign to the autonomous system (AS). The AS number identifies an autonomous system and enables the system to exchange exterior routing information with other neighboring autonomous systems. The valid range is from 0 through 4294967294. Note:
This is applicable only when routing topology is e-BGP Dynamic Routing in route-based site-to-site VPN. |
|
Protected Networks |
Configure the addresses or interface type for the selected device to protect one area of the network from the other. When a dynamic routing protocol is selected, the interface option is displayed. You can also create addresses by clicking Add New Address. Note:
This is applicable for only route-based site-to-site VPN. |
|
Settings |
Guidelines |
|---|---|
| IKE Settings | |
|
IKE Version |
Select the required IKE version, either V1 or V2, that is used to negotiate dynamic security associations (SAs) for IPsec. By default, IKE V2 is used. |
|
Mode |
Select an IKE policy mode.
Note:
Mode is applicable when the IKE Version is V1. |
|
Dead Peer Detection |
Enable to permit the two gateways to determine if the peer gateway is up and responding to the Dead Peer Detection (DPD) messages that are negotiated during IPsec establishment. |
|
DPD Mode |
Select a DPD Mode.
|
|
DPD Interval |
Select an interval in seconds to send dead peer detection messages. The default interval is 10 seconds, with a permissible range of 2 to 60 seconds. |
|
DPD Threshold |
Select the failure DPD threshold value. This specifies the maximum number of times the DPD messages must be sent when there is no response from the peer. The default number of transmissions is 5 times, with a permissible range of 1 to 5. |
| Custom Proposal | |
|
Name |
Enter a name for the VPN. |
|
Deffie Hellman group |
Select a group. Diffie-Hellman (DH) groups determine the strength of the key used in the key exchange process. |
|
Authentication-algorithm |
Select an algorithm. The device uses this algorithm to verify the authenticity and integrity of a packet. |
|
Encryption-algorithm |
Select the appropriate encryption mechanism. |
|
Lifetime-seconds |
Select a lifetime of an IKE security association (SA). The valid range is from 180 through 86,400 seconds. |
| Advance Configuration | |
|
General IKE ID |
Enable this option to accept peer IKE ID. This option is disabled by default. If General IKE ID is enabled, the IKE ID option is disabled automatically. |
|
IKEv2 Re Authentication |
Select a reauthentication frequency. Reauthentication can be disabled by setting the reauthentication frequency to 0. Range is 0 to 100. |
|
IKEv2 Re Fragmentation Support |
IKEv2 fragmentation splits a large IKEv2 message into a set of smaller ones so that there is no fragmentation at the IP level. |
|
IKE ID |
Select an option:
IKE ID is applicable only when General IKE ID is disabled. |
|
NAT-T |
Enable Network Address Translation-Traversal (NAT-T) if the dynamic endpoint is behind a NAT device. |
|
Keep Alive |
Select a value. NAT Keepalives are required to maintain the NAT translation during the connection between the VPN peers. Range is from 1 to 300 seconds. |
| IPSec Settings | |
|
Perfect Forward Secrecy |
Select Perfect Forward Secrecy (PFS) as the method that the device uses to generate the encryption key. The PFS generates each new encryption key independently from the previous key. The higher numbered groups provide more security but require more processing time. |
|
Establish Tunnel |
Select an option to specify when IKE is activated.
|
| Custom Proposal | |
|
Name |
Enter a name for the VPN. |
|
Authentication Algorithm |
Select an algorithm. The device uses these algorithms to verify the authenticity and integrity of a packet. |
|
Protocol |
Select the required protocol to establish the VPN.
|
|
Encryption Algorithm |
Select the necessary encryption method. This is applicable if the Protocol is ESP. |
|
Lifetime Seconds |
Select a lifetime of an IKE security association (SA). The valid range is from 180 through 86,400 seconds. |
|
Lifetime kilobytes |
Select the lifetime (in kilobytes) of an IPsec security association (SA). The range is from 64 through 4294967294 kilobytes. |
| Advance Configuration | |
|
VPN Monitor |
Enable this option to send Internet Control Message Protocol (ICMP) to determine if the VPN is up. |
|
Anti Replay |
By default, Anti-Replay detection is enabled. IPsec protects against a VPN attack by using a sequence of numbers that are built into the IPsec packet—the system does not accept a packet for which it has already seen the same sequence number. It checks the sequence numbers and enforces the check, rather than just ignoring the sequence numbers. Disable it if there is an error with the IPsec mechanism that results in out-of-order packets, preventing proper functionality. |
|
Install interval |
Select the maximum number of seconds to allow for the installation of a re-keyed outbound security association (SA) on the device. |
|
Idle Time |
Select the appropriate idle time interval. The sessions and their corresponding translations typically time out after a certain period if no traffic is received. |
|
DF Bit |
Select an option to process the Don’t Fragment (DF) bit in IP messages.
|
|
Copy Outer DSCP |
Enable copying of Differentiated Services Code Point (DSCP) field from the outer IP header encrypted packet to the inner IP header plain text message on the decryption path. The benefit in enabling this feature is that after IPsec decryption, clear text packets can follow the inner class-of-service (CoS) rules. |
