Security Implementation and Recommendations
General Security Guidelines
- Use HTTPS with a public CA certificate. You'll need a publicly resolvable hostname and public CA certificate.
- Configure the firewall to allow only specific ports for inbound traffic.
- Configure the firewall to allow inbound traffic from only Juniper Mist™ public source IPs.
- Configure the firewall to allow only specific ports for outbound traffic.
- Update the VMs with all required security patches.
- Restrict the Juniper Alert Format Relay VM access to authorized users only.
- Allow VM and SSH access only to the internal/management network.
SSL Certificate
You need to specify a publicly resolvable FQDN for the Juniper Alert Format Relay public IP. We recommend SSL certificate validation using a public Certificate Authority (CA). If a certificate isn't available, you can disable the certificate verification requirement during the installation process.
By default, Juniper Alert Format Relay can generate and install self-signed certificates. However, it's recommended to use publicly resolvable FQDN with a public CA certificate.
Allow Inbound Traffic from Webhooks Public Source IP Addresses
Add firewall rules to allow webhooks traffic from Juniper Mist.
Juniper Mist generates the webhooks with static public IP addresses, which will not change. For the complete list of source IPs for webhooks, see ../../../mist-management/topics/ref/firewall-ports-to-open.html#section_cx4_bxp_yxb in the Juniper Mist Management Guide.
As a second layer of check, Juniper Alert Format Relay allows traffic only from Juniper Mist source IPs.
VM Internet Access
You can disable Internet access to the Juniper Alert Format Relay VMs and provide conditional access only when necessary. Juniper Alert Format Relay runs API queries to fetch inventory details, so the VMs should be able to access the Juniper Mist URL. For a complete list, see Mist Cloud IP Addresses and Ports in the Juniper Mist Management Guide.
On the VMs, enable APT/YUM and allow access to these repositories/mirror.
Firewall and NAT Configuration
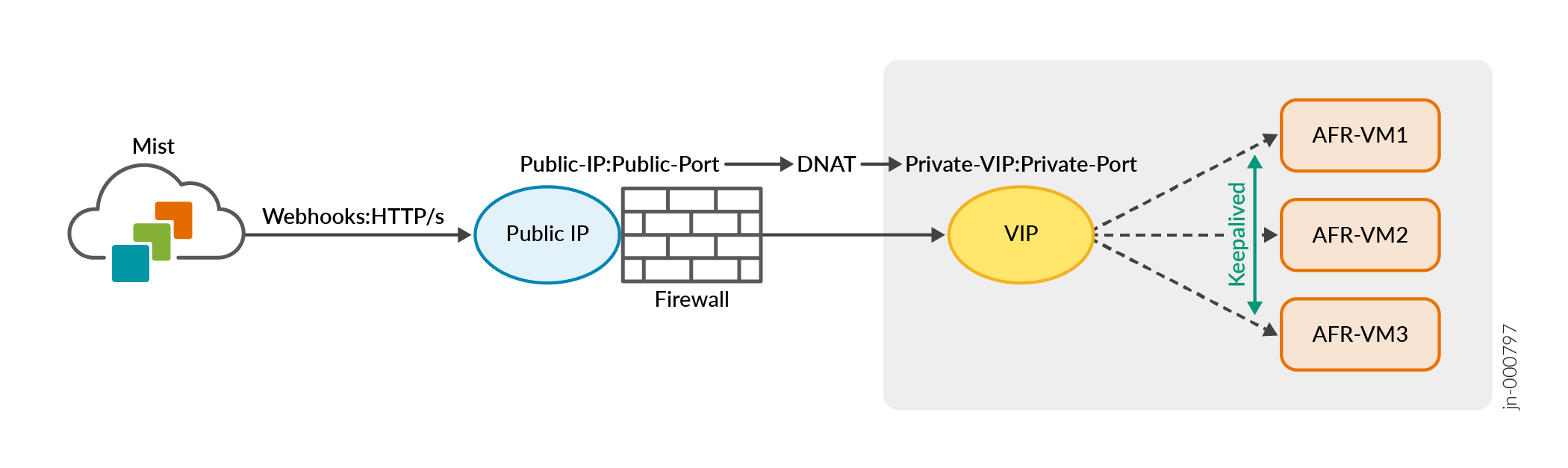
You can configure Juniper Mist to forward the webhooks to a public IP/FDQN. This public IP can be on the firewall. Configure NAT to forward the webhook messages to the private VIP for Juniper Alert Format Relay. Juniper Alert Format Relay will respond with the HTTP status code for webhook HTTP post messages. You'll need to configure the required static/source NAT settings to allow this communication.
Here's an illustration of how the traffic from Juniper Mist moves through a firewall to the virtual IP and VMs.
Security Hardening
Here are a few ways that Juniper Alert Format Relay hardens your Juniper Mist network to make it more resistant to attacks.
- Only specific web endpoints are exposed to the Internet.
- Web endpoints are configured to receive traffic from specific Juniper Mist public IPs.
- Sensitive information is stored locally in encrypted format.
