Media Access Control Security (MACsec) over WAN
Media Access Control Security (MACsec) is a link layer solution for point-to-point encryption. MACsec can be used to encrypt Layer 2 connections over a service provider WAN to ensure data transmission integrity and confidentiality.
Use Feature Explorer to confirm platform and release support for specific features.
Review the Platform-Specific Behavior for MACsec over WAN section for notes related to your platform.
Overview of Carrying MACsec over Multiple Hops
To establish a MACsec session, MACsec Key Agreement (MKA) is used to exchange the required keys between the peer nodes. MKA PDUs are transmitted using Extensible Authentication Protocol over LAN (EAPoL) as a transport protocol. EAPoL is a Layer 2 protocol and would normally be locally processed by the switch or router and not propagated further.
In the case where nodes are connected through a service provider network, this presents a challenge. Figure 1 shows MACsec carried over a service provider network. MKA must exchange keys between customer devices A and B. The edge routers, or intermediate devices, should not process the EAPoL packets. Instead, they should transparently forward them to the next hop.
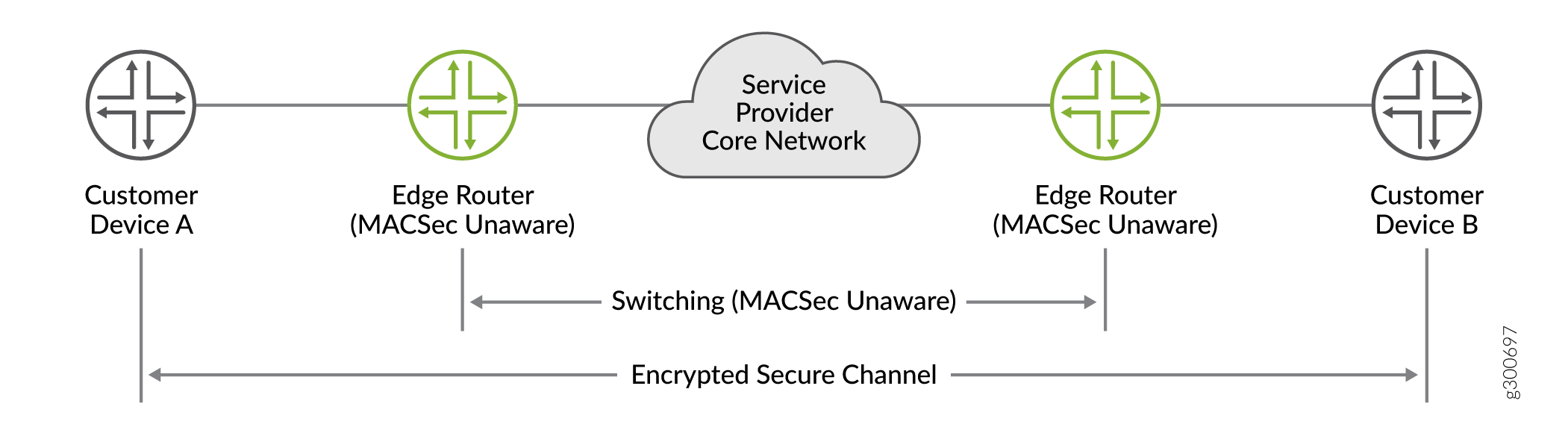
The default destination MAC address for an EAPoL packet is a multicast address of 01:80:C2:00:00:03. In a service provider network, there might be devices that consume these packets, assuming the packets are meant for them. EAPoL is used by 802.1X and other authentication methods, which might cause the devices to drop the packets, depending on their configuration. This would cause the MKA session to fail between the intended endpoints. To ensure that the EAPoL packet reaches the intended endpoint, you can change attributes of the packet such as the destination MAC address, the VLAN ID, and the EtherType so that the service provider network tunnels the packet instead of consuming it.
Configure IFL-level MACsec on Logical Interfaces
MACsec at the level of a logical interface (IFL) allows multiple MKA sessions on a single physical port. This enables service multiplexing with MACsec encryption of point-to-multipoint connections over service provider WANs.
To support IFL-level MACsec, the MKA protocol packets are sent out with the VLAN tags configured on the logical interface. VLAN tags are transmitted in clear text, which allows intermediate switches that are MACsec-unaware to switch the packets based on the VLAN tags.
When you configure MACsec, you must bind the connectivity association to an interface. To enable IFL-level MACsec, bind the connectivity association to a logical interface using the following command:
[edit security macsec] user@switch# set interfaces interface-names unit unit-number connectivity-association connectivity-association-name
For complete configuration details, see Configuring MACsec in Static CAK Mode.
Configure the EAPoL Destination MAC Address for MACsec
MACsec transmits MKA PDUs using EAPoL packets to establish a secure session. By default, EAPoL uses a destination multicast MAC address of 01:80:C2:00:00:03. To prevent these packets from being consumed in a service provider network, you can change the destination MAC address.
To configure the EAPoL destination MAC address, enter one of the following commands.
The configuration must match on both endpoints of a security association or secure connection in order to establish the MACsec session.
The options are mapped to MAC addresses as follows:
|
EAPoL Address |
MAC Address |
|---|---|
|
|
01:80:C2:00:00:03 |
|
|
01:80:C2:00:00:00 |
|
|
01:80:C2:00:00:0E |
|
|
configurable unicast address |
Configure the EAPoL EtherType for MACsec
MACsec uses EAPoL as a transport protocol to establish sessions. When you configure a custom MAC destination address for EAPoL packets, in most cases the network tunnels the packet based on the destination address. However, some networks filter packets based on EtherType value instead. The EtherType is a field in an Ethernet frame. The value of the EtherType field identifies the protocol of the packet encapsulated in the frame. By default, the EtherType for EAPoL is 0x888e as defined by the IEEE 802.1X standard. Some networks intercept untagged packets with this EtherType automatically. To ensure the network tunnels MACsec packets properly to the endpoint, you can set a custom EtherType for EAPoL.
When MACsec is enabled on an interface, the device traps untagged EAPoL packets passing through that interface and forwards tagged EAPoL packets. By default, the device traps these packets only if they have the default EtherType 0x888e. When you configure a custom EtherType, the device traps packets that have that custom EtherType instead; it does not trap packets with EtherType 0x888e.
Choose the EAPoL EtherType Value
If you configure a custom EtherType value, it must be:
-
Different in each EAPoL profile. Do not configure the same EtherType for multiple profiles. If you need only one EtherType, use only one profile.
-
Valid (greater than or equal to 0x600).
-
Available (not reserved for another use).
Using a reserved EtherType can interfere with data traffic. Reserved EtherTypes fall into three categories:
EtherTypes values reserved by the IEEE 802.1X standard, which are listed on the IEEE EtherTypes standards page.
EtherType values used in traffic data.
EtherType values reserved specifically on Junos devices. This category include values like 0x9100 and 0x9200, which are not listed on the standards page. To confirm the EtherType is not in this category, review the table below or commit the configuration. If the EtherType value is in the following table, the commit check detects the reserved value and the commit fails.
| EtherType | Reserved For | EtherType | Reserved For |
|---|---|---|---|
| 0x22F3 | TRILL | 0x88B6 | EXP2 |
| 0x0800 | IPv4 | 0x88B7 | EXP3 |
| 0x0806 | ARP | 0x88cc | LLDP |
| 0x8035 | RARP | 0x88E5 | 802.1AE |
| 0x8100 | VLAN | 0x88E7 | PBB |
| 0x86dd | IPv6 | 0x88EE | ELMI |
| 0x8809 | SLOW | 0x88F5 | MVRP |
| 0x8847 | TAG | 0x88F6 | MMRP |
| 0x8848 | Multicast MPLS | 0x88F7 | PTP |
| 0x8863 | PPPoE DISC | 0x8902 | Ethernet OAM CFM |
| 0x8864 | PPPoE SESS | 0x8906 | FCOE |
| 0x888e | 802.1X | 0x8914 | FIP |
| 0x88a8 | PVLAN | 0x9100 | 9100 |
| 0x88B5 | EXP1 | 0x9200 | 9200 |
Configuration
The originating and endpoint devices can only establish a MACsec session if both devices are configured with the same EAPoL EtherType. Repeat the configuration on both devices.
To configure a custom EtherType value for EAPoL packets:
Platform-Specific Behavior for MACsec over WAN
Use the following table to review platform-specific behaviors for your platforms.
|
Platform |
Difference |
|---|---|
|
ACX Series |
|
|
PTX Series |
|
