ON THIS PAGE
Example: Configuring Multichassis Link Aggregation on the QFX Series
Example: Configuring Multichassis Link Aggregation on the MX Series
Example: Configuring Multichassis Link Aggregation Between QFX Series Switches and MX Series Routers
Example: Configure Optional Features For Multichassis Link Aggregation
Example: Configuring CoS for FCoE Transit Switch Traffic Across an MC-LAG
MC-LAG Examples
Example: Configuring Multichassis Link Aggregation on the QFX Series
Our content testing team has validated and updated this example.
This example shows how multichassis link aggregation groups (MC-LAGs) enable a client device to form a logical LAG interface between two switches to provide redundancy and load balancing between the two switches, multihoming support, and a loop-free Layer 2 network without running Spanning Tree Protocol (STP).
Requirements
This example uses the following hardware and software components:
-
Junos OS Release 13.2X51-D10 or later for the QFX5100 standalone switches, Release 15.1X53-D10 or later for QFX10002 standalone switches.
-
Revalidated on Junos OS Release 17.3R1 for QFX5100 and QFX10000 switches.
-
Revalidated on Junos OS Release 19.4R1 for QFX10000 switches.
-
Before you configure an MC-LAG, be sure that you understand how to:
-
Configure aggregated Ethernet interfaces on a switch. See Example: Configuring Link Aggregation Between a QFX Series Product and an Aggregation Switch.
-
Configure the Link Aggregation Control Protocol (LACP) on aggregated Ethernet interfaces on a switch. See Example: Configuring Link Aggregation with LACP Between a QFX Series Product and an Aggregation Switch.
Overview
In this example, you configure an MC-LAG across two switches, consisting of two aggregated Ethernet interfaces, an interchassis control link-protection link (ICL-PL), multichassis protection link for the ICL-PL, the Inter-Chassis Control Protocol for the peers hosting the MC-LAG, and Layer 3 connectivity between MC-LAG peers. Layer 3 connectivity is required for ICCP.
Topology
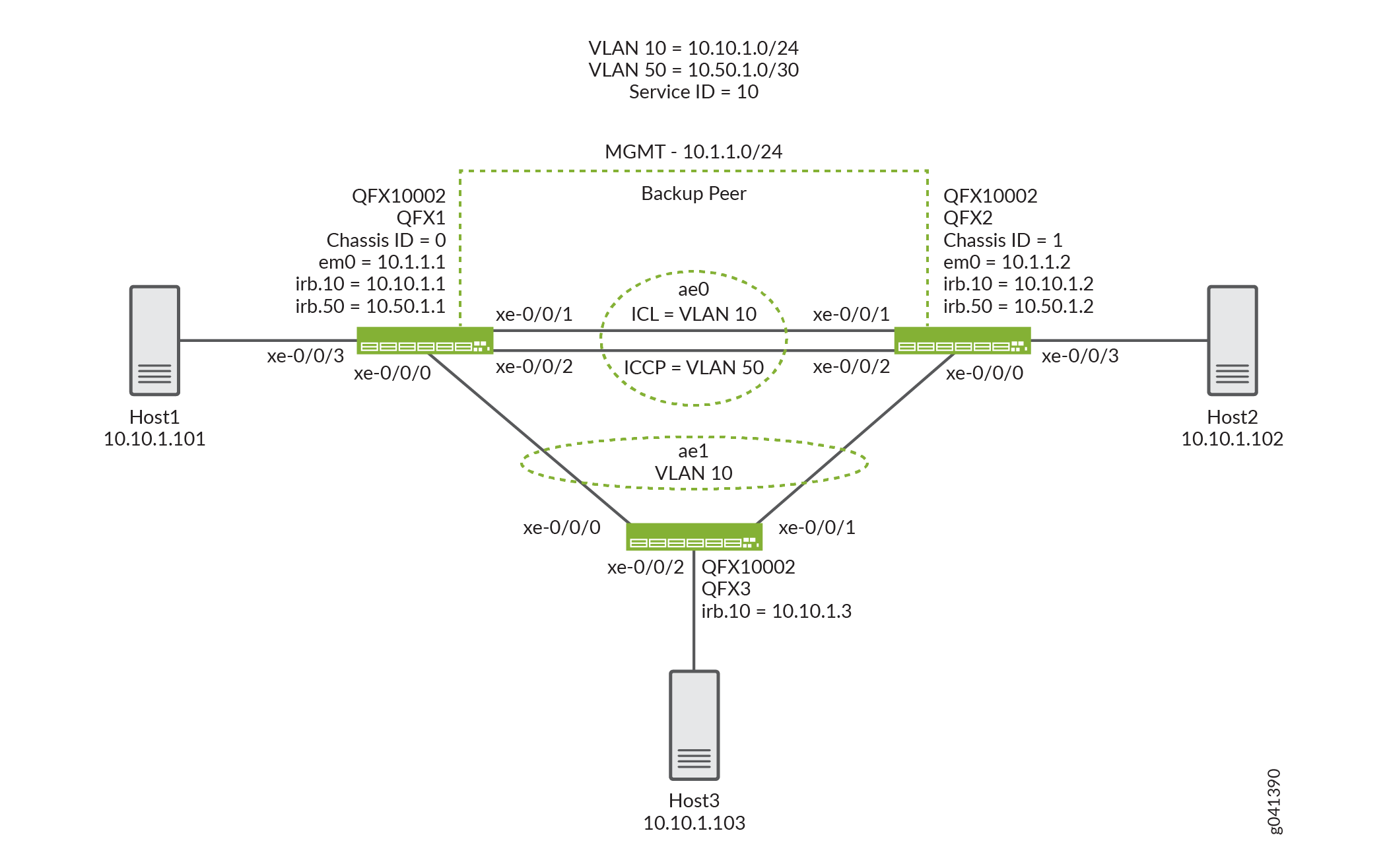
The topology used in this example consists of two switches hosting an MC-LAG. The two switches are connected to a server. Figure 1 shows the topology used in this example.
Configuration
CLI Quick Configuration
To quickly configure this example, copy the
following commands, paste them in a text file, remove any line breaks,
change any details necessary to match your network configuration,
copy and paste the commands into the CLI at the [edit] hierarchy
level, and then enter commit from configuration mode.
QFX1
set chassis aggregated-devices ethernet device-count 2 set interfaces xe-0/0/0 ether-options 802.3ad ae1 set interfaces xe-0/0/1 ether-options 802.3ad ae0 set interfaces xe-0/0/2 ether-options 802.3ad ae0 set interfaces xe-0/0/3 unit 0 family ethernet-switching interface-mode access set interfaces xe-0/0/3 unit 0 family ethernet-switching vlan members v10 set interfaces ae0 aggregated-ether-options lacp active set interfaces ae0 unit 0 family ethernet-switching interface-mode trunk set interfaces ae0 unit 0 family ethernet-switching vlan members v50 set interfaces ae0 unit 0 family ethernet-switching vlan members v10 set interfaces ae1 aggregated-ether-options lacp active set interfaces ae1 aggregated-ether-options lacp system-id 00:01:02:03:04:05 set interfaces ae1 aggregated-ether-options lacp admin-key 3 set interfaces ae1 aggregated-ether-options mc-ae mc-ae-id 3 set interfaces ae1 aggregated-ether-options mc-ae redundancy-group 1 set interfaces ae1 aggregated-ether-options mc-ae chassis-id 0 set interfaces ae1 aggregated-ether-options mc-ae mode active-active set interfaces ae1 aggregated-ether-options mc-ae status-control active set interfaces ae1 aggregated-ether-options mc-ae init-delay-time 240 set interfaces ae1 unit 0 family ethernet-switching interface-mode trunk set interfaces ae1 unit 0 family ethernet-switching vlan members v10 set interfaces em0 unit 0 family inet address 10.1.1.1/24 set interfaces irb unit 10 family inet address 10.10.1.1/24 set interfaces irb unit 50 family inet address 10.50.1.1/30 set multi-chassis multi-chassis-protection 10.50.1.2 interface ae0 set protocols iccp local-ip-addr 10.50.1.1 set protocols iccp peer 10.50.1.2 session-establishment-hold-time 340 set protocols iccp peer 10.50.1.2 redundancy-group-id-list 1 set protocols iccp peer 10.50.1.2 backup-liveness-detection backup-peer-ip 10.1.1.2 set protocols iccp peer 10.50.1.2 liveness-detection minimum-receive-interval 1000 set protocols iccp peer 10.50.1.2 liveness-detection transmit-interval minimum-interval 1000 set switch-options service-id 10 set vlans v10 vlan-id 10 set vlans v10 l3-interface irb.10 set vlans v50 vlan-id 50 set vlans v50 l3-interface irb.50
QFX2
set chassis aggregated-devices ethernet device-count 2 set interfaces xe-0/0/0 ether-options 802.3ad ae1 set interfaces xe-0/0/1 ether-options 802.3ad ae0 set interfaces xe-0/0/2 ether-options 802.3ad ae0 set interfaces xe-0/0/3 unit 0 family ethernet-switching interface-mode access set interfaces xe-0/0/3 unit 0 family ethernet-switching vlan members v10 set interfaces ae0 aggregated-ether-options lacp active set interfaces ae0 unit 0 family ethernet-switching interface-mode trunk set interfaces ae0 unit 0 family ethernet-switching vlan members v50 set interfaces ae0 unit 0 family ethernet-switching vlan members v10 set interfaces ae1 aggregated-ether-options lacp active set interfaces ae1 aggregated-ether-options lacp system-id 00:01:02:03:04:05 set interfaces ae1 aggregated-ether-options lacp admin-key 3 set interfaces ae1 aggregated-ether-options mc-ae mc-ae-id 3 set interfaces ae1 aggregated-ether-options mc-ae redundancy-group 1 set interfaces ae1 aggregated-ether-options mc-ae chassis-id 1 set interfaces ae1 aggregated-ether-options mc-ae mode active-active set interfaces ae1 aggregated-ether-options mc-ae status-control standby set interfaces ae1 aggregated-ether-options mc-ae init-delay-time 240 set interfaces ae1 unit 0 family ethernet-switching interface-mode trunk set interfaces ae1 unit 0 family ethernet-switching vlan members v10 set interfaces em0 unit 0 family inet address 10.1.1.2/24 set interfaces irb unit 10 family inet address 10.10.1.2/24 set interfaces irb unit 50 family inet address 10.50.1.2/30 set multi-chassis multi-chassis-protection 10.50.1.1 interface ae0 set protocols iccp local-ip-addr 10.50.1.2 set protocols iccp peer 10.50.1.1 session-establishment-hold-time 340 set protocols iccp peer 10.50.1.1 redundancy-group-id-list 1 set protocols iccp peer 10.50.1.1 backup-liveness-detection backup-peer-ip 10.1.1.1 set protocols iccp peer 10.50.1.1 liveness-detection minimum-receive-interval 1000 set protocols iccp peer 10.50.1.1 liveness-detection transmit-interval minimum-interval 1000 set switch-options service-id 10 set vlans v10 vlan-id 10 set vlans v10 l3-interface irb.10 set vlans v50 vlan-id 50 set vlans v50 l3-interface irb.50
QFX3
set chassis aggregated-devices ethernet device-count 2 set interfaces xe-0/0/0 ether-options 802.3ad ae1 set interfaces xe-0/0/1 ether-options 802.3ad ae1 set interfaces xe-0/0/2 unit 0 family ethernet-switching interface-mode access set interfaces xe-0/0/2 unit 0 family ethernet-switching vlan members v10 set interfaces ae1 aggregated-ether-options lacp active set interfaces ae1 unit 0 family ethernet-switching interface-mode trunk set interfaces ae1 unit 0 family ethernet-switching vlan members v10 set interfaces em0 unit 0 family inet address 10.1.1.3/24 set interfaces irb unit 10 family inet address 10.10.1.3/24 set vlans v10 vlan-id 10 set vlans v10 l3-interface irb.10
Configuring MC-LAG on Two Switches
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode.
To enable interfaces and multichassis protection link between MC-LAG peers:
-
Configure the number of LAGs on both QFX1 and QFX2.
[edit chassis] user@switch# set aggregated-devices ethernet device-count 2
-
Add member interfaces to the aggregated Ethernet interfaces on both QFX1 and QFX2.
QFX1 and QFX2: [edit interfaces] user@switch# set xe-0/0/0 ether-options 802.3ad ae1 [edit interfaces] user@switch# set xe-0/0/1 ether-options 802.3ad ae0 [edit interfaces] user@switch# set xe-0/0/2 ether-options 802.3ad ae0
-
Configure an access interface to the connected end host.
[edit interfaces] user@switch# set xe-0/0/3 unit 0 family ethernet-switching interface-mode access
-
Add member interfaces to VLAN v10.
[edit interfaces] user@switch# set interfaces xe-0/0/3 unit 0 family ethernet-switching vlan members v10
-
Configure a trunk interface between QFX1 and QFX2.
[edit interfaces] user@switch# set ae0 unit 0 family ethernet-switching interface-mode trunk
-
Enable VLANs on the MC-LAG between QFX1 and QFX2.
[edit] user@switch# set vlans v10 vlan-id 10
>[edit] user@switch# set vlans v50 vlan-id 50
>[edit interfaces] user@switch# set ae0 unit 0 family ethernet-switching vlan members v10
>[edit interfaces] user@switch# set ae0 unit 0 family ethernet-switching vlan members v50
-
Configure an IRB 50.
>[edit irb] user@switch# set irb.50
-
Assign VLAN 50 to irb.50.
>[edit] user@switch# set vlans v50 l3-interface irb.50
-
Configure an IRB 10.
>[edit irb] user@switch# set irb.10
-
Assign VLAN 10 irb.10.
>[edit] user@switch# set vlans v10 l3-interface irb.10
-
Enable LACP on the MC-LAG interface on QFX1 and QFX2.
Note:At least one end needs to be active. The other end can be either active or passive.
>[edit interfaces] user@switch# set ae0 aggregated-ether-options lacp active [edit interfaces] user@switch# set ae1 aggregated-ether-options lacp active
-
Specify the same LACP system ID for the MC-LAG on QFX1 and QFX2.
>[edit interfaces] user@switch# set ae1 aggregated-ether-options lacp system-ID 00:01:02:03:04:05
-
Specify the same LACP administration key on both QFX1 and QFX2.
>[edit interfaces] user@switch# set ae1 aggregated-ether-options lacp admin-key 3
-
Specify the same multichassis aggregated Ethernet identification number on both MC-LAG peers on QFX1 and QFX2.
>[edit interfaces] user@switch# set ae1 aggregated-ether-options mc-ae mc-ae-id 3
-
Specify a unique chassis ID for the MC-LAG on the MC-LAG peers on QFX1 and QFX2.
>QFX1: [edit interfaces] user@switch# set ae1 aggregated-ether-options mc-ae chassis-id 0
>QFX2: [edit interfaces] user@switch# set ae1 aggregated-ether-options mc-ae chassis-id 1
-
Specify the operating mode of the MC-LAG on both QFX1 and QFX2.
Note:Only active-active mode is supported at this time.
>[edit interfaces] user@switch# set ae1 aggregated-ether-options mc-ae mode active-active
-
Specify the status control for MC-LAG on QFX1 and QFX2.
Note:You must configure status control on both QFX1 and QFX2 hosting the MC-LAG. If one peer is in active mode, the other must be in standby mode.
>QFX1: [edit interfaces] user@switch# set ae1 aggregated-ether-options mc-ae status-control active
>QFX2: [edit interfaces] user@switch# set ae1 aggregated-ether-options mc-ae status-control standby
-
Specify the number of seconds by which the bring-up of the multichassis aggregated Ethernet interface should be deferred after you reboot QFX1 and QFX2.
Note:The recommended value for maximum VLAN configuration (for example, 4,000 VLANS) is 240 seconds. If IGMP snooping is enabled on all of the VLANs, the recommended value is 420 seconds.
>[edit interfaces] user@switch# set ae1 aggregated-ether-options mc-ae init-delay-time 240
-
Configure Layer 3 connectivity between the MC-LAG peers on both QFX1 and QFX2.
>[edit vlans] user@switch# set v50 vlan-id 50
>[edit vlans] user@switch# set v50 l3-interface irb.50
>[edit interfaces] user@switch# set ae0 unit 0 family ethernet-switching interface-mode trunk vlan members v50
-
Configure a multichassis protection link between QFX1 and QFX2.
>QFX1: [edit] user@switch# set multi-chassis multi-chassis-protection 10.50.1.2 interface ae0
>QFX2: [edit] user@switch# set multi-chassis multi-chassis-protection 10.50.1.1 interface ae0
-
Configure the local IP address to be in the ICCP connection on QFX1 and QFX2.
>QFX1: [edit protocols] user@switch# set iccp local-ip-addr 10.50.1.1
>QFX2: [edit protocols] user@switch# set iccp local-ip-addr 10.50.1.2
-
(Optional) Configure the time during which an ICCP connection must succeed between MC-LAG peers on QFX1 and QFX2.
Note:On QFX Series switches, the default session establishment hold time is 300 seconds. However, the session establishment time must be at least 100 seconds higher than the init delay time. You can optionally update the session establishment time to be 340 seconds and the init delay time to be 240 seconds.
>QFX1: [edit protocols] user@switch# set iccp peer 10.50.1.2 session-establishment-hold-time 340
>QFX2: [edit protocols] user@switch# set iccp peer 10.50.1.1 session-establishment-hold-time 340
-
Configure the redundancy groups for ICCP on QFX1 and QFX2.
>QFX1: [edit protocols] user@switch# set iccp peer 10.50.1.2 redundancy-group-id-list 1
>QFX2: [edit protocols] user@switch# set iccp peer 10.50.1.1 redundancy-group-id-list 1
-
(Optional) Configure the backup IP address to be used for backup liveness detection on both QFX1 and QFX2.
Note:By default, backup liveness detection is not enabled. Configuring a backup IP address helps achieve sub-second traffic loss during an MC-LAG peer reboot.
>QFX1: [edit protocols] user@switch# set iccp peer 10.50.1.2 backup-liveness-detection backup-peer-ip 10.1.1.2
>QFX2: [edit protocols] user@switch# set iccp peer 10.50.1.1 backup-liveness-detection backup-peer-ip 10.1.1.1
-
Configure the peer IP address and minimum receive interval for a BFD session for ICCP on QFX1 and QFX2.
>QFX1: [edit protocols] user@switch# set iccp peer 10.50.1.2 liveness-detection minimum-receive-interval 1000
>QFX2: [edit protocols] user@switch# set iccp peer 10.50.1.1 liveness-detection minimum-receive-interval 1000
-
Configure the peer IP address and minimum transmit interval for BFD session for ICCP on QFX1 and QFX2.
>QFX1: [edit protocols] user@switch# set iccp peer 10.50.1.2 liveness-detection transmit-interval minimum-interval 1000
>QFX2: [edit protocols] user@switch# set iccp peer 10.50.1.1 liveness-detection transmit-interval minimum-interval 1000
-
To enable the service ID on QFX1 and QFX2:
The switch service ID is used to synchronize applications, IGMP, ARP, and MAC learning across MC-LAG members.
>[edit switch-options] user@switch# set service-id 10
Results
Here are the results of your configuration on QFX1.
chassis {
aggregated-devices {
ethernet {
device-count 2;
}
}
}
interfaces {
xe-0/0/0 {
ether-options {
802.3ad ae1;
}
}
xe-0/0/1 {
ether-options {
802.3ad ae0;
}
}
xe-0/0/2 {
ether-options {
802.3ad ae0;
}
}
xe-0/0/3 {
unit 0 {
family ethernet-switching {
interface-mode access;
vlan {
members v10;
}
}
}
}
ae0 {
aggregated-ether-options {
lacp {
active;
}
}
unit 0 {
family ethernet-switching {
interface-mode trunk;
vlan {
members [ v50 v10 ];
}
}
}
}
ae1 {
aggregated-ether-options {
lacp {
active;
system-id 00:01:02:03:04:05;
admin-key 3;
}
mc-ae {
mc-ae-id 3;
redundancy-group 1;
chassis-id 0;
mode active-active;
status-control active;
init-delay-time 240;
}
}
unit 0 {
family ethernet-switching {
interface-mode trunk;
vlan {
members v10;
}
}
}
}
em0 {
unit 0 {
family inet {
address 10.1.1.1/24;
}
}
}
irb {
unit 10 {
family inet {
address 10.10.1.1/24;
}
}
unit 50 {
family inet {
address 10.50.1.1/30;
}
}
}
}
multi-chassis {
multi-chassis-protection 10.50.1.2 {
interface ae0;
}
}
protocols {
iccp {
local-ip-addr 10.50.1.1;
peer 10.50.1.2 {
session-establishment-hold-time 340;
redundancy-group-id-list 1;
backup-liveness-detection {
backup-peer-ip 10.1.1.2;
}
liveness-detection {
minimum-receive-interval 1000;
transmit-interval {
minimum-interval 1000;
}
}
}
}
}
switch-options {
service-id 10;
}
vlans {
v10 {
vlan-id 10;
l3-interface irb.10;
}
v50 {
vlan-id 50;
l3-interface irb.50;
}
}
Display the results of the configuration on QFX2.
chassis {
aggregated-devices {
ethernet {
device-count 2;
}
}
}
interfaces {
xe-0/0/0 {
ether-options {
802.3ad ae1;
}
}
xe-0/0/1 {
ether-options {
802.3ad ae0;
}
}
xe-0/0/2 {
ether-options {
802.3ad ae0;
}
}
xe-0/0/3 {
unit 0 {
family ethernet-switching {
interface-mode access;
vlan {
members v10;
}
}
}
}
ae0 {
aggregated-ether-options {
lacp {
active;
}
}
unit 0 {
family ethernet-switching {
interface-mode trunk;
vlan {
members [ v50 v10 ];
}
}
}
}
ae1 {
aggregated-ether-options {
lacp {
active;
system-id 00:01:02:03:04:05;
admin-key 3;
}
mc-ae {
mc-ae-id 3;
redundancy-group 1;
chassis-id 1;
mode active-active;
status-control standby;
init-delay-time 240;
}
}
unit 0 {
family ethernet-switching {
interface-mode trunk;
vlan {
members v10;
}
}
}
}
em0 {
unit 0 {
family inet {
address 10.1.1.2/24;
}
}
}
irb {
unit 10 {
family inet {
address 10.10.1.2/24;
}
}
unit 50 {
family inet {
address 10.50.1.2/30;
}
}
}
}
multi-chassis {
multi-chassis-protection 10.50.1.1 {
interface ae0;
}
}
protocols {
iccp {
local-ip-addr 10.50.1.2;
peer 10.50.1.1 {
session-establishment-hold-time 340;
redundancy-group-id-list 1;
backup-liveness-detection {
backup-peer-ip 10.1.1.1;
}
liveness-detection {
minimum-receive-interval 1000;
transmit-interval {
minimum-interval 1000;
}
}
}
}
}
switch-options {
service-id 10;
}
vlans {
v10 {
vlan-id 10;
l3-interface irb.10;
}
v50 {
vlan-id 50;
l3-interface irb.50;
}
}
Display the results of the configuration on QFX3.
chassis {
aggregated-devices {
ethernet {
device-count 2;
}
}
}
interfaces {
xe-0/0/0 {
ether-options {
802.3ad ae1;
}
}
xe-0/0/1 {
ether-options {
802.3ad ae1;
}
}
xe-0/0/2 {
unit 0 {
family ethernet-switching {
interface-mode access;
vlan {
members v10;
}
}
}
}
ae1 {
aggregated-ether-options {
lacp {
active;
}
}
unit 0 {
family ethernet-switching {
interface-mode trunk;
vlan {
members v10;
}
}
}
}
em0 {
unit 0 {
family inet {
address 10.1.1.3/24;
}
}
}
irb {
unit 10 {
family inet {
address 10.10.1.3/24;
}
}
}
}
vlans {
v10 {
vlan-id 10;
l3-interface irb.10;
}
}
Verification
Verify that the configuration is working properly.
- Verifying That ICCP Is Working on QFX1
- Verifying That LACP Is Active on QFX1
- Verifying That the MC-AE and ICL-PL Interfaces Are Up on QFX1
- Verifying That MAC Learning Is Occurring on QFX1
- Verifying That Host1 Can Connect to Host2
Verifying That ICCP Is Working on QFX1
Purpose
Verify that ICCP is running on QFX1.
Action
user@switch> show iccp
Redundancy Group Information for peer 10.50.1.2
TCP Connection : Established
Liveliness Detection : Up
Backup liveness peer status: Up
Redundancy Group ID Status
1 Up
Client Application: lacpd
Redundancy Group IDs Joined: 1
Client Application: l2ald_iccpd_client
Redundancy Group IDs Joined: 1 Meaning
This output shows that the TCP connection between the peers hosting the MC-LAG is up, liveness detection is up, and MCSNOOPD and ESWD client applications are running.
Verifying That LACP Is Active on QFX1
Purpose
Verify that LACP is active on QFX1.
Action
user@switch> show lacp interfaces
Aggregated interface: ae0
LACP state: Role Exp Def Dist Col Syn Aggr Timeout Activity
xe-0/0/1 Actor No No Yes Yes Yes Yes Fast Active
xe-0/0/1 Partner No No Yes Yes Yes Yes Fast Active
xe-0/0/2 Actor No No Yes Yes Yes Yes Fast Active
xe-0/0/2 Partner No No Yes Yes Yes Yes Fast Active
LACP protocol: Receive State Transmit State Mux State
xe-0/0/1 Current Fast periodic Collecting distributing
xe-0/0/2 Current Fast periodic Collecting distributing
Aggregated interface: ae1
LACP state: Role Exp Def Dist Col Syn Aggr Timeout Activity
xe-0/0/0 Actor No No Yes Yes Yes Yes Fast Active
xe-0/0/0 Partner No No Yes Yes Yes Yes Fast Active
LACP protocol: Receive State Transmit State Mux State
xe-0/0/0 Current Fast periodic Collecting distributingMeaning
This output shows that QFX1 is participating in LACP negotiation.
Verifying That the MC-AE and ICL-PL Interfaces Are Up on QFX1
Purpose
Verify that the MC-AE and ICL-PL interfaces are up on QFX1.
Action
user@switch> show interfaces mc-ae
Member Link : ae1
Current State Machine's State: mcae active state
Local Status : active
Local State : up
Peer Status : active
Peer State : up
Logical Interface : ae1.0
Topology Type : bridge
Local State : up
Peer State : up
Peer Ip/MCP/State : 10.50.1.2 ae0.0 upMeaning
This output shows that the MC-AE interface on QFX1 is up and active.
Verifying That MAC Learning Is Occurring on QFX1
Purpose
Verify that MAC learning is working on QFX1.
Action
user@switch> show ethernet-switching table
MAC flags (S - static MAC, D - dynamic MAC, L - locally learned, P - Persistent static, C - Control MAC
SE - statistics enabled, NM - non configured MAC, R - remote PE MAC, O - ovsdb MAC)
Ethernet switching table : 3 entries, 3 learned
Routing instance : default-switch
Vlan MAC MAC Age Logical NH RTR
name address flags interface Index ID
v10 00:50:56:93:73:cd DR - ae0.0 0 0
v10 00:50:56:93:87:58 DL - xe-0/0/3.0 0 0
v10 00:50:56:93:89:a0 DLR - ae1.0 0 0 Meaning
The output shows three learned MAC addresses entries.
Verifying That Host1 Can Connect to Host2
Purpose
Verify that Host1 can ping Host2.
Action
[edit] user@HOST1> ping 10.10.1.102 PING 10.10.1.102 (10.10.1.102): 56 data bytes 64 bytes from 10.10.1.102: icmp_seq=0 ttl=64 time=157.788 ms 64 bytes from 10.10.1.102: icmp_seq=1 ttl=64 time=153.965 ms 64 bytes from 10.10.1.102: icmp_seq=2 ttl=64 time=102.126 ms ...
Meaning
The output shows that HOST1 can successfully ping HOST2.
Troubleshooting
Troubleshooting a LAG That Is Down
Problem
The show interfaces terse command shows
that the MC-LAG is down.
Solution
Check the following:
-
Verify that there is no configuration mismatch.
-
Verify that all member ports are up.
-
Verify that the MC-LAG is part of family Ethernet switching (Layer 2 LAG).
-
Verify that the MC-LAG member is connected to the correct MC-LAG member at the other end.
Example: Configuring Multichassis Link Aggregation on the MX Series
This example shows how to configure a multichassis link aggregation group (MC-LAG) in an active-active scenario, which load balances traffic across the PEs.
- Requirements
- Overview
- Configuring the PE Routers
- Configuring the CE Device
- Configuring the Provider Router
- Verification
Requirements
This example uses the following hardware and software components:
This example also applies to QFX10002 and QFX10008 switches.
-
Four Juniper Networks MX Series routers (MX240, MX480, MX960)
-
Junos OS Release 11.2 or later running on all four routers
Overview
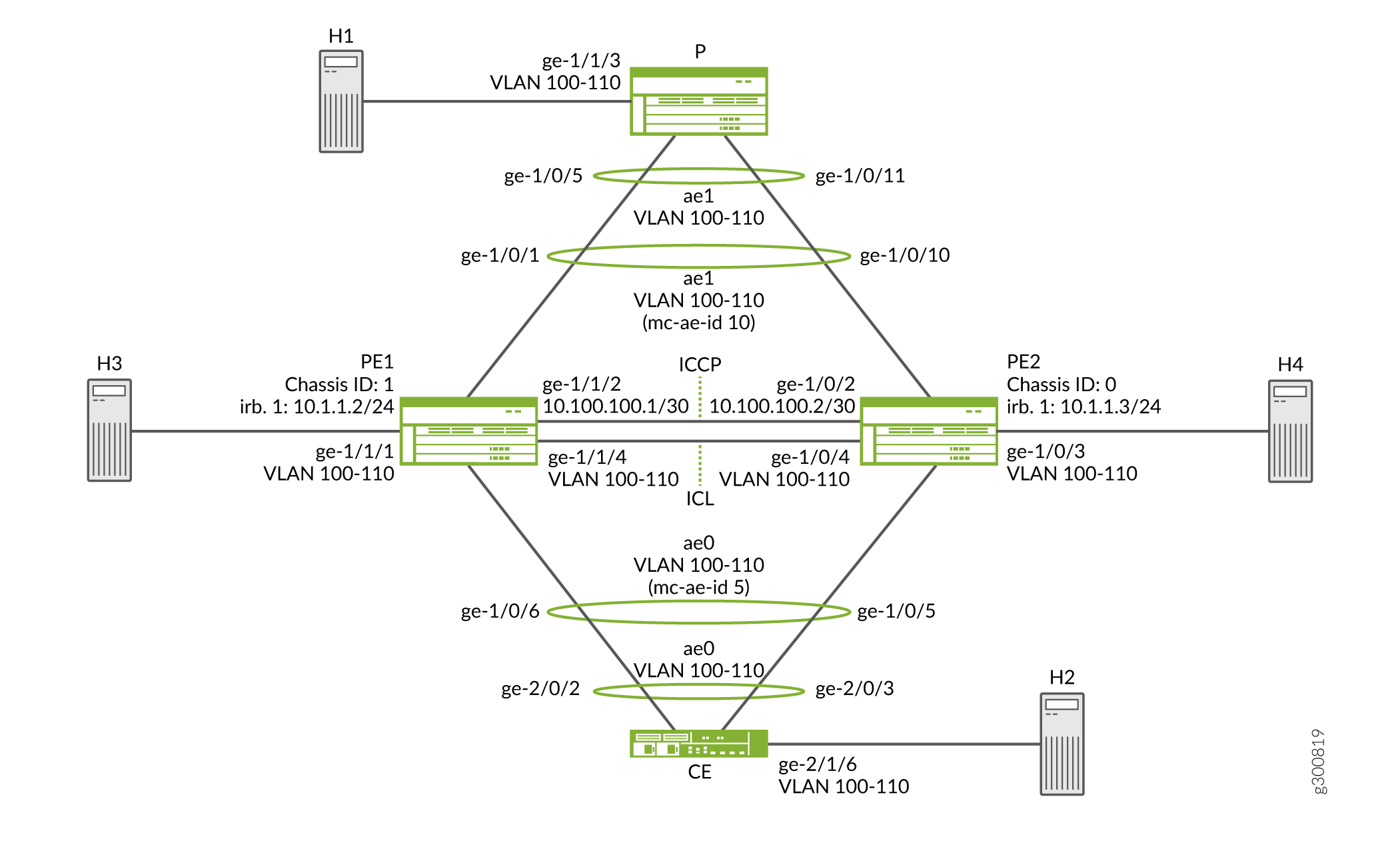
Consider a sample topology in which a customer edge router, CE, is connected to two provider edge (PE) routers, PE1 and PE2, respectively. The two PE devices each have a link aggregation group (LAG) connected to the CE device. The configured mode is active -active, meaning that both PE routers’ LAG ports are active and carrying traffic at the same time. PE1 and PE2 are connected to a single service provider router, P.
In this example, the CE router is not aware that its aggregated Ethernet links are connected to two separate PE devices. The two PE devices each have a LAG connected to the CE device. The configured mode is active-active, meaning that both PE routers’ LAG ports are active and carrying traffic at the same time.
In Figure 2, from the perspective of Router CE, all four ports belonging to a LAG are connected to a single service provider device. Because the configured mode is active-active, all four ports are active, and the CE device load-balances the traffic to the peering PE devices. On the PE routers, a regular LAG is configured facing the CE device.
On one end of an MC-LAG is an MC-LAG client device, such as a server, that has one or more physical links in a LAG. This client device does not need to detect the MC-LAG. On the other side of an MC-LAG are two MC-LAG routers. Each of the routers has one or more physical links connected to a single client device. The routers coordinate with each other to ensure that data traffic is forwarded properly.
ICCP messages are sent between the two PE devices. In this example, you configure an MC-LAG across two routers, consisting of two aggregated Ethernet interfaces, an interchassis link-protection link (ICL-PL), multichassis protection link for the ICL-PL, and ICCP for the peers hosting the MC-LAG.
Topology Diagram
Figure 2 shows the topology used in this example.
Configuring the PE Routers
CLI Quick Configuration
To quickly configure this example, copy the
following commands, paste them in a text file, remove any line breaks,
change any details necessary to match your network configuration,
copy and paste the commands into the CLI at the [edit] hierarchy
level, and then enter commit from configuration mode.
Router PE1
set chassis aggregated-devices ethernet device-count 5 set interfaces ge-1/0/1 gigether-options 802.3ad ae1 set interfaces ge-1/1/2 unit 0 family inet address 10.100.100.1/30 set interfaces ge-1/0/6 gigether-options 802.3ad ae0 set interfaces ge-1/1/1 flexible-vlan-tagging set interfaces ge-1/1/1 encapsulation flexible-ethernet-services set interfaces ge-1/1/1 unit 0 encapsulation vlan-bridge set interfaces ge-1/1/1 unit 0 vlan-id-range 100-110 set interfaces ge-1/1/4 flexible-vlan-tagging set interfaces ge-1/1/4 encapsulation flexible-ethernet-services set interfaces ge-1/1/4 unit 0 encapsulation vlan-bridge set interfaces ge-1/1/4 unit 0 vlan-id-range 100-110 set interfaces ae0 flexible-vlan-tagging set interfaces ae0 encapsulation flexible-ethernet-services set interfaces ae0 aggregated-ether-options lacp active set interfaces ae0 aggregated-ether-options lacp system-priority 100 set interfaces ae0 aggregated-ether-options lacp system-id 00:00:00:00:00:05 set interfaces ae0 aggregated-ether-options lacp admin-key 1 set interfaces ae0 aggregated-ether-options mc-ae mc-ae-id 5 set interfaces ae0 aggregated-ether-options mc-ae redundancy-group 10 set interfaces ae0 aggregated-ether-options mc-ae chassis-id 1 set interfaces ae0 aggregated-ether-options mc-ae mode active-active set interfaces ae0 aggregated-ether-options mc-ae status-control active set interfaces ae0 unit 0 encapsulation vlan-bridge set interfaces ae0 unit 0 vlan-id-range 100-110 set interfaces ae0 unit 0 multi-chassis-protection 10.100.100.2 interface ge-1/1/4.0 set interfaces ae1 flexible-vlan-tagging set interfaces ae1 encapsulation flexible-ethernet-services set interfaces ae1 aggregated-ether-options lacp active set interfaces ae1 aggregated-ether-options lacp system-priority 100 set interfaces ae1 aggregated-ether-options lacp system-id 00:00:00:00:00:05 set interfaces ae1 aggregated-ether-options lacp admin-key 1 set interfaces ae1 aggregated-ether-options mc-ae mc-ae-id 10 set interfaces ae1 aggregated-ether-options mc-ae redundancy-group 10 set interfaces ae1 aggregated-ether-options mc-ae chassis-id 1 set interfaces ae1 aggregated-ether-options mc-ae mode active-active set interfaces ae1 aggregated-ether-options mc-ae status-control active set interfaces ae1 unit 0 encapsulation vlan-bridge set interfaces ae1 unit 0 vlan-id-range 100-110 set interfaces ae1 unit 0 multi-chassis-protection 10.100.100.2 interface ge-1/1/4.0 set bridge-domains bd0 domain-type bridge set bridge-domains bd0 vlan-id all set bridge-domains bd0 service-id 20 set bridge-domains bd0 interface ae1.0 set bridge-domains bd0 interface ge-1/0/3.0 set bridge-domains bd0 interface ge-1/1/1.0 set bridge-domains bd0 interface ge-1/1/4.0 set bridge-domains bd0 interface ae0.0 set protocols iccp local-ip-addr 10.100.100.1 set protocols iccp peer 10.100.100.2 redundancy-group-id-list 10 set protocols iccp peer 10.100.100.2 liveness-detection minimum-interval 1000 set switch-options service-id 10
Router PE2
set chassis aggregated-devices ethernet device-count 5 set interfaces ge-1/0/2 unit 0 family inet address 10.100.100.2/30 set interfaces ge-1/0/3 flexible-vlan-tagging set interfaces ge-1/0/3 encapsulation flexible-ethernet-services set interfaces ge-1/0/3 unit 0 encapsulation vlan-bridge set interfaces ge-1/0/3 unit 0 vlan-id-range 100-110 set interfaces ge-1/0/4 flexible-vlan-tagging set interfaces ge-1/0/4 encapsulation flexible-ethernet-services set interfaces ge-1/0/4 unit 0 encapsulation vlan-bridge set interfaces ge-1/0/4 unit 0 vlan-id-range 100-110 set interfaces ge-1/0/5 gigether-options 802.3ad ae0 set interfaces ge-1/1/0 gigether-options 802.3ad ae1 set interfaces ae0 flexible-vlan-tagging set interfaces ae0 encapsulation flexible-ethernet-services set interfaces ae0 aggregated-ether-options lacp active set interfaces ae0 aggregated-ether-options lacp system-priority 100 set interfaces ae0 aggregated-ether-options lacp system-id 00:00:00:00:00:05 set interfaces ae0 aggregated-ether-options lacp admin-key 1 set interfaces ae0 aggregated-ether-options mc-ae mc-ae-id 5 set interfaces ae0 aggregated-ether-options mc-ae redundancy-group 10 set interfaces ae0 aggregated-ether-options mc-ae chassis-id 0 set interfaces ae0 aggregated-ether-options mc-ae mode active-active set interfaces ae0 aggregated-ether-options mc-ae status-control standby set interfaces ae0 unit 0 encapsulation vlan-bridge set interfaces ae0 unit 0 vlan-id-range 100-110 set interfaces ae0 unit 0 multi-chassis-protection 10.100.100.1 interface ge-1/0/4.0 set interfaces ae1 flexible-vlan-tagging set interfaces ae1 encapsulation flexible-ethernet-services set interfaces ae1 aggregated-ether-options lacp active set interfaces ae1 aggregated-ether-options lacp system-priority 100 set interfaces ae1 aggregated-ether-options lacp system-id 00:00:00:00:00:05 set interfaces ae1 aggregated-ether-options lacp admin-key 1 set interfaces ae1 aggregated-ether-options mc-ae mc-ae-id 10 set interfaces ae1 aggregated-ether-options mc-ae redundancy-group 10 set interfaces ae1 aggregated-ether-options mc-ae chassis-id 0 set interfaces ae1 aggregated-ether-options mc-ae mode active-active set interfaces ae1 aggregated-ether-options mc-ae status-control standby set interfaces ae1 unit 0 encapsulation vlan-bridge set interfaces ae1 unit 0 vlan-id-range 100-110 set interfaces ae1 unit 0 multi-chassis-protection 10.100.100.1 interface ge-1/0/4.0 set bridge-domains bd0 domain-type bridge set bridge-domains bd0 vlan-id all set bridge-domains bd0 service-id 20 set bridge-domains bd0 interface ae1.0 set bridge-domains bd0 interface ge-1/0/3.0 set bridge-domains bd0 interface ge-1/0/4.0 set bridge-domains bd0 interface ae0.0 set protocols iccp local-ip-addr 10.100.100.2 set protocols iccp peer 10.100.100.1 redundancy-group-id-list 10 set protocols iccp peer 10.100.100.1 liveness-detection minimum-interval 1000 set switch-options service-id 10
Configuring the PE1 Router
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode .
To configure Router PE1:
-
Specify the number of aggregated Ethernet interfaces to be created.
[edit chassis] user@PE1# set aggregated-devices ethernet device-count 5
-
Specify the members to be included within the aggregated Ethernet bundles.
[edit interfaces] user@PE1# set ge-1/0/1 gigether-options 802.3ad ae1 user@PE1# set ge-1/0/6 gigether-options 802.3ad ae0
-
Configure the interfaces that connect to senders or receivers, the ICL interfaces, and the ICCP interfaces.
[edit interfaces] user@PE1# set ge-1/1/1 flexible-vlan-tagging user@PE1# set ge-1/1/1 encapsulation flexible-ethernet-services user@PE1# set ge-1/1/1 unit 0 encapsulation vlan-bridge user@PE1# set ge-1/1/1 unit 0 vlan-id-range 100-110 user@PE1# set ge-1/1/4 flexible-vlan-tagging user@PE1# set ge-1/1/4 encapsulation flexible-ethernet-services user@PE1# set ge-1/1/4 unit 0 encapsulation vlan-bridge user@PE1# set ge-1/1/4 unit 0 vlan-id-range 100-110 user@PE1# set ge-1/1/2 unit 0 family inet address 10.100.100.1/30
-
Configure parameters on the aggregated Ethernet bundles.
[edit interfaces ae0] user@PE1# set flexible-vlan-tagging user@PE1# set encapsulation flexible-ethernet-services user@PE1# set unit 0 encapsulation vlan-bridge user@PE1# set unit 0 vlan-id-range 100-110 user@PE1# set unit 0 multi-chassis-protection 10.100.100.2 interface ge-1/1/4.0 [edit interfaces ae1] user@PE1# set flexible-vlan-tagging user@PE1# set encapsulation flexible-ethernet-services user@PE1# set unit 0 encapsulation vlan-bridge user@PE1# set unit 0 vlan-id-range 100-110 user@PE1# set unit 0 multi-chassis-protection 10.100.100.2 interface ge-1/1/4.0
-
Configure LACP on the aggregated Ethernet bundles.
[edit interfaces ae0 aggregated-ether-options] user@PE1# set lacp active user@PE1# set lacp system-priority 100 user@PE1# set lacp system-id 00:00:00:00:00:05 user@PE1# set lacp admin-key 1 [edit interfaces ae1 aggregated-ether-options] user@PE1# set lacp active user@PE1# set lacp system-priority 100 user@PE1# set lacp system-id 00:00:00:00:00:05 user@PE1# set lacp admin-key 1
-
Configure the MC-LAG interfaces.
[edit interfaces ae0 aggregated-ether-options] user@PE1# set mc-ae mc-ae-id 5 user@PE1# set mc-ae redundancy-group 10 user@PE1# set mc-ae chassis-id 1 user@PE1# set mc-ae mode active-active user@PE1# set mc-ae status-control active [edit interfaces ae1 aggregated-ether-options] user@PE1# set mc-ae mc-ae-id 10 user@PE1# set mc-ae redundancy-group 10 user@PE1# set mc-ae chassis-id 1 user@PE1# set mc-ae mode active-active user@PE1# set mc-ae status-control active
The multichassis aggregated Ethernet identification number (mc-ae-id) specifies which link aggregation group the aggregated Ethernet interface belongs to. The ae0 interfaces on Router PE1 and Router PE2 are configured with mc-ae-id 5. The ae1 interfaces on Router PE1 and Router PE2 are configured with mc-ae-id 10.
The
redundancy-group 10statement is used by ICCP to associate multiple chassis that perform similar redundancy functions and to establish a communication channel so that applications on peering chassis can send messages to each other. The ae0 and ae1 interfaces on Router PE1 and Router PE2 are configured with the same redundancy group, redundancy-group 10.The
chassis-idstatement is used by LACP for calculating the port number of the MC-LAG's physical member links. Router PE1 uses chassid-id 1 to identify both its ae0 and ae1 interfaces. Router PE2 uses chassis-id 0 to identify both its ae0 and ae1 interfaces.The
modestatement indicates whether an MC-LAG is in active-standby mode or active-active mode. Chassis that are in the same group must be in the same mode. -
Configure a domain that includes the set of logical ports.
[edit bridge-domains bd0] user@PE1# set domain-type bridge user@PE1# set vlan-id all user@PE1# set service-id 20 user@PE1# set interface ae0.0 user@PE1# set interface ae1.0 user@PE1# set interface ge-1/1/1.0 user@PE1# set interface ge-1/1/4.0
The ports within a bridge domain share the same flooding or broadcast characteristics in order to perform Layer 2 bridging.
The bridge-level
service-idstatement is required to link related bridge domains across peers (in this case Router PE1 and Router PE2), and must be configured with the same value. -
Configure ICCP parameters.
[edit protocols iccp] user@PE1# set local-ip-addr 10.100.100.1 user@PE1# set peer 10.100.100.2 redundancy-group-id-list 10 user@PE1# set peer 10.100.100.2 liveness-detection minimum-interval 1000
-
Configure the service ID at the global level.
[edit switch-options] user@PE1# set service-id 10
You must configure the same unique network-wide configuration for a service in the set of PE routers providing the service. This service ID is required if the multichassis aggregated Ethernet interfaces are part of a bridge domain.
Results
From configuration mode, confirm your configuration
by entering the show bridge-domains, show chassis, show interfaces, show protocols, and show switch-options commands. If the output does not display
the intended configuration, repeat the instructions in this example
to correct the configuration.
user@PE1# show bridge-domains
bd0 {
domain-type bridge;
vlan-id all;
service-id 20;
interface ae1.0;
interface ge-1/1/1.0;
interface ge-1/1/4.0;
interface ae0.0;
}
user@PE1# show chassis
aggregated-devices {
ethernet {
device-count 5;
}
}
user@PE1# show interfaces
ge-1/0/1 {
gigether-options {
802.3ad ae1;
}
}
ge-1/0/6 {
gigether-options {
802.3ad ae0;
}
}
ge-1/1/2 {
unit 0 {
family inet {
address 10.100.100.1/30;
}
}
}
ge-1/1/1 {
flexible-vlan-tagging;
encapsulation flexible-ethernet-services;
unit 0 {
encapsulation vlan-bridge;
vlan-id-range 100-110;
}
}
ge-1/1/4 {
flexible-vlan-tagging;
encapsulation flexible-ethernet-services;
unit 0 {
encapsulation vlan-bridge;
vlan-id-range 100-110;
}
}
ae0 {
flexible-vlan-tagging;
encapsulation flexible-ethernet-services;
aggregated-ether-options {
lacp {
active;
system-priority 100;
system-id 00:00:00:00:00:05;
admin-key 1;
}
mc-ae {
mc-ae-id 5;
redundancy-group 10;
chassis-id 1;
mode active-active;
status-control active;
}
}
unit 0 {
encapsulation vlan-bridge;
vlan-id-range 100-110;
multi-chassis-protection 10.100.100.2 {
interface ge-1/1/4.0;
}
}
}
ae1 {
flexible-vlan-tagging;
encapsulation flexible-ethernet-services;
aggregated-ether-options {
lacp {
active;
system-priority 100;
system-id 00:00:00:00:00:05;
admin-key 1;
}
mc-ae {
mc-ae-id 10;
redundancy-group 10;
chassis-id 1;
mode active-active;
status-control active;
}
}
unit 0 {
encapsulation vlan-bridge;
vlan-id-range 100-110;
multi-chassis-protection 10.100.100.2 {
interface ge-1/1/4.0;
}
}
}
user@PE1# show protocols
iccp {
local-ip-addr 10.100.100.1;
peer 10.100.100.2 {
redundancy-group-id-list 10;
liveness-detection {
minimum-interval 1000;
}
}
}
user@PE1# show switch-options service-id 10;
If you are done configuring the device, enter commit from configuration mode.
Repeat the procedure for Router PE2, using the appropriate interface names and addresses.
Configuring the CE Device
CLI Quick Configuration
To quickly configure this example, copy the
following commands, paste them in a text file, remove any line breaks,
change any details necessary to match your network configuration,
copy and paste the commands into the CLI at the [edit] hierarchy
level , and then enter commit from configuration mode.
Device CE
set chassis aggregated-devices ethernet device-count 2 set interfaces ge-2/0/2 gigether-options 802.3ad ae0 set interfaces ge-2/0/3 gigether-options 802.3ad ae0 set interfaces ge-2/1/6 flexible-vlan-tagging set interfaces ge-2/1/6 encapsulation flexible-ethernet-services set interfaces ge-2/1/6 unit 0 encapsulation vlan-bridge set interfaces ge-2/1/6 unit 0 vlan-id-range 100-110 set interfaces ae0 flexible-vlan-tagging set interfaces ae0 encapsulation flexible-ethernet-services set interfaces ae0 aggregated-ether-options lacp active set interfaces ae0 aggregated-ether-options lacp system-priority 100 set interfaces ae0 unit 0 encapsulation vlan-bridge set interfaces ae0 unit 0 vlan-id-range 100-110 set bridge-domains bd0 domain-type bridge set bridge-domains bd0 vlan-id all set bridge-domains bd0 interface ge-2/1/6.0 set bridge-domains bd0 interface ae0.0
Configuring the CE Device
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode .
To configure the CE device:
-
Specify the number of aggregated Ethernet interfaces to be created.
[edit chassis] user@CE# set aggregated-devices ethernet device-count 2
-
Specify the members to be included within the aggregated Ethernet bundle.
[edit interfaces] user@CE# set ge-2/0/2 gigether-options 802.3ad ae0 user@CE# set ge-2/0/3 gigether-options 802.3ad ae0
-
Configure an interface that connects to senders or receivers.
[edit interfaces ge-2/1/6] user@CE# set flexible-vlan-tagging user@CE# set encapsulation flexible-ethernet-services user@CE# set unit 0 encapsulation vlan-bridge user@CE# set unit 0 vlan-id-range 100-110
-
Configure parameters on the aggregated Ethernet bundle.
[edit interfaces ae0] user@CE# set flexible-vlan-tagging user@CE# set encapsulation flexible-ethernet-services user@CE# set unit 0 encapsulation vlan-bridge user@CE# set unit 0 vlan-id-range 100-110
-
Configure LACP on the aggregated Ethernet bundle.
[edit interfaces ae0 aggregated-ether-options] user@CE# set lacp active user@CE# set lacp system-priority 100
The
activestatement initiates transmission of LACP packets.For the
system-prioritystatement, a smaller value indicates a higher priority. The device with the lower system priority value determines which links between LACP partner devices are active and which are in standby mode for each LACP group. The device on the controlling end of the link uses port priorities to determine which ports are bundled into the aggregated bundle and which ports are put in standby mode. Port priorities on the other device (the noncontrolling end of the link) are ignored. -
Configure a domain that includes the set of logical ports.
[edit bridge-domains bd0] user@CE# set domain-type bridge user@CE# set vlan-id all user@CE# set interface ge-2/1/6.0 user@CE# set interface ae0.0
The ports within a bridge domain share the same flooding or broadcast characteristics in order to perform Layer 2 bridging.
Results
From configuration mode, confirm your configuration
by entering the show bridge-domains, show chassis, and show interfaces commands. If the output does not
display the intended configuration, repeat the instructions in this
example to correct the configuration.
user@CE# show bridge-domains
bd0 {
domain-type bridge;
vlan-id all;
interface ge-2/1/6.0;
interface ae0.0;
}
user@CE# show chassis
aggregated-devices {
ethernet {
device-count 2;
}
}
user@CE# show interfaces
ge-2/0/2 {
gigether-options {
802.3ad ae0;
}
}
ge-2/0/3 {
gigether-options {
802.3ad ae0;
}
}
ge-2/1/6 {
flexible-vlan-tagging;
encapsulation flexible-ethernet-services;
unit 0 {
encapsulation vlan-bridge;
vlan-id-range 100-110;
}
}
ae0 {
flexible-vlan-tagging;
encapsulation flexible-ethernet-services;
aggregated-ether-options {
lacp {
active;
system-priority 100;
}
}
unit 0 {
encapsulation vlan-bridge;
vlan-id-range 100-110;
}
}
If you are done configuring the device, enter commit from configuration mode.
Configuring the Provider Router
CLI Quick Configuration
To quickly configure this example, copy the
following commands, paste them in a text file, remove any line breaks,
change any details necessary to match your network configuration,
copy and paste the commands into the CLI at the [edit] hierarchy
level, and then enter commit from configuration mode.
Router P
set chassis aggregated-devices ethernet device-count 2 set interfaces ge-1/0/5 gigether-options 802.3ad ae1 set interfaces ge-1/0/11 gigether-options 802.3ad ae1 set interfaces ge-1/1/3 flexible-vlan-tagging set interfaces ge-1/1/3 encapsulation flexible-ethernet-services set interfaces ge-1/1/3 unit 0 encapsulation vlan-bridge set interfaces ge-1/1/3 unit 0 vlan-id-range 100-110 set interfaces ae1 flexible-vlan-tagging set interfaces ae1 encapsulation flexible-ethernet-services set interfaces ae1 aggregated-ether-options lacp active set interfaces ae1 aggregated-ether-options lacp system-priority 100 set interfaces ae1 unit 0 encapsulation vlan-bridge set interfaces ae1 unit 0 vlan-id-range 100-110 set bridge-domains bd0 vlan-id all set bridge-domains bd0 domain-type bridge set bridge-domains bd0 interface ge-1/1/3.0 set bridge-domains bd0 interface ae1.0
Configuring the PE Router
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode .
To configure the P router:
-
Specify the number of aggregated Ethernet interfaces to be created.
[edit chassis] user@P# set aggregated-devices ethernet device-count 2
-
Specify the members to be included within the aggregated Ethernet bundle.
[edit interfaces] user@P# set ge-1/0/5 gigether-options 802.3ad ae1 user@P# set ge-1/0/11 gigether-options 802.3ad ae1
-
Configure an interface that connects to senders or receivers.
[edit interfaces ge-1/1/3] user@P# set flexible-vlan-tagging user@P# set encapsulation flexible-ethernet-services user@P# set unit 0 encapsulation vlan-bridge user@P# set unit 0 vlan-id-range 100-500
-
Configure parameters on the aggregated Ethernet bundle.
[edit interfaces ae1] user@P# set flexible-vlan-tagging user@P# set encapsulation flexible-ethernet-services user@P# set unit 0 encapsulation vlan-bridge user@P# set unit 0 vlan-id-range 100-110
-
Configure LACP on the aggregated Ethernet bundle.
[edit interfaces ae1 aggregated-ether-options] user@P# set lacp active user@P# set lacp system-priority 100
-
Configure a domain that includes the set of logical ports.
[edit bridge-domains bd0] user@P# set vlan-id all user@P# set domain-type bridge user@P# set interface ge-1/1/3.0 user@P# set interface ae1.0
Results
From configuration mode, confirm your configuration
by entering the show bridge-domains, show chassis, and show interfaces commands. If the output does not
display the intended configuration, repeat the instructions in this
example to correct the configuration.
user@P# show bridge-domains
bd0 {
domain-type bridge;
vlan-id all;
interface ge-1/1/3.0;
interface ae1.0;
}
user@P# show chassis
aggregated-devices {
ethernet {
device-count 2;
}
}
user@P# show interfaces
ge-1/0/5 {
gigether-options {
802.3ad ae1;
}
}
ge-1/0/11 {
gigether-options {
802.3ad ae1;
}
}
ge-1/1/3 {
flexible-vlan-tagging;
encapsulation flexible-ethernet-services;
unit 0 {
encapsulation vlan-bridge;
vlan-id-range 100-500;
}
}
ae1 {
flexible-vlan-tagging;
encapsulation flexible-ethernet-services;
aggregated-ether-options {
lacp {
active;
system-priority 100;
}
}
unit 0 {
encapsulation vlan-bridge;
vlan-id-range 100-110;
}
}
If you are done configuring the device, enter commit from configuration mode.
Verification
Confirm that the configuration is working properly by running the following commands:
-
show iccp -
show interfaces ae0 -
show interfaces ae1 -
show interfaces mc-ae -
show pim interfaces -
show vrrp -
show igmp -
show ospf -
show dhcp relay
Example: Configuring Multichassis Link Aggregation Between QFX Series Switches and MX Series Routers
This example shows how to configure multichassis link aggregation groups (MC-LAGs) between a QFX Series switch and a MX Series router using active-active mode to support Layer 2 bridging. In active-active mode all member links carry traffic allowing traffic to be load balanced to both MC-LAG peers.
Requirements
This example uses the following hardware and software components:
One Juniper Networks MX Series router (MX240, MX480, MX960)
One Juniper Networks QFX Series switch (QFX10000, QFX5110, QFX5120)
Two servers with LAG support; MX Series routers fill the server role in this example
Junos OS Release 19.4R1 or later on the MC-LAG peers
Overview
In the example topology two servers are connected to two provider edge (PE) devices, S0 and R1. S0 is a QFX Series switch while R1 is a MX Series router. Both PE devices have link aggregation groups (LAGs) connected to both servers. This example configures active-active mode for the MC-LAGs, meaning that both PE devices’ LAG ports are active and carrying traffic at the same time.
The servers are not aware that their aggregated Ethernet links are connected to multiple PE devices. MC-LAG operation is opaque to the servers and both have a conventional Ethernet LAG interface configured.
On one end of an MC-LAG is an MC-LAG client device, for example, a server or switching/routing device, that has one or more physical links in a LAG. The client devices do not need to support MC-LAG as these devices only need to support a standard LAG interface. On the other side of the MC-LAG are two MC-LAG devices (PEs). Each of the PEs has one or more physical links connected to the client device. The PE devices coordinate with each other to ensure that data traffic is forwarded properly even when all client links are actively forwarding traffic.
In Figure 3, the servers operate as if both LAG members were connected to a single provider device. Because the configured mode is active-active, all LAG members are in a forwarding state and the CE device load-balances the traffic to the peering PE devices.
The Interchassis Control Protocol (ICCP) sends messages between the PE devices to control the forwarding state of the MC-LAG. In addition, an interchassis link-protection link (ICL-PL) is used to forward traffic between the PE devices as needed when operating in active-active mode.
In this example you configure two MC-LAG on the PEs to support Layer 2 connectivity between the aggregated Ethernet interfaces on the servers. As part of the MC-LAG configuration you provision an aggregated Ethernet interface between the MC-LAG peers to support the ICL-PL and ICCP functionality.
Topology Diagram
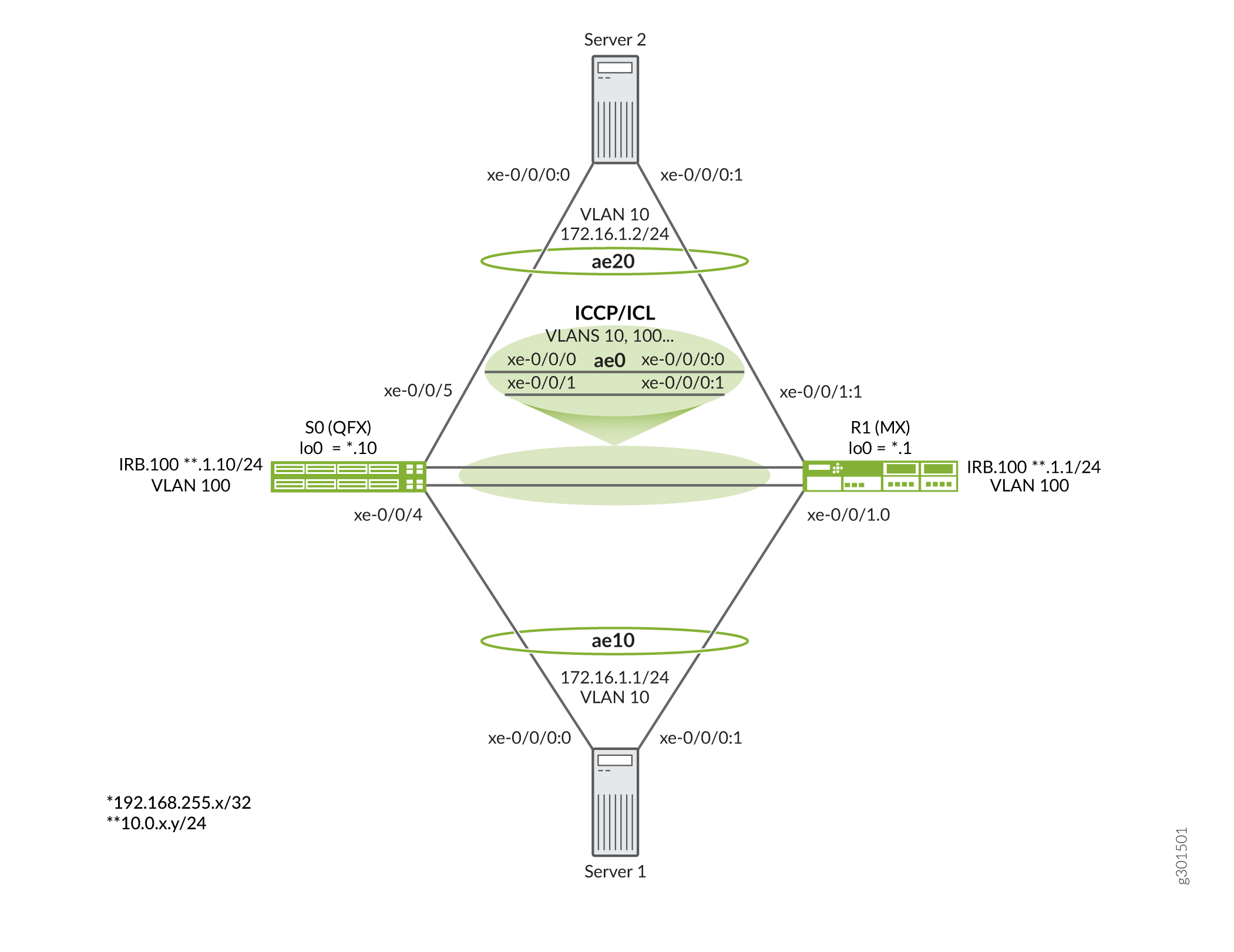
Figure 3 shows the topology used in this example.
Key points about the topology include:
- The S0 node is a QFX10000 switch while the R1 node is a MX960 router.
- MX Series routers are used to fill the role of the 2 servers. Any switch, router, or server device that supports a conventional LACP based LAG interface can be used in this example.
- The servers are assigned VLAN 10 and have a shared subnet. You expect Layer 2 connectivity between the servers.
- The ICCP session between the PEs is anchored to an IRB interface. This is akin to BGP peering between loopback interfaces to survive link failures. However, here the IRBs are placed in a shared VLAN (VLAN 100) that provides Layer 2 connectivity between the PEs. This means that an IGP or static route is not needed for connectivity between the IRBs. As a result the IRBs share an IP subnet.
- This example deploys a single LAG interface between the PEs (ae0) to support both the ICCP and ICL functionality. If desired you can run ICCP over a separate AE bundle. The use of multiple members in the AE bundle used for the ICCP/ICL links is highly recommended to ensure that they remain operational in the event of individual interface or link failures.
- While largely similar, the MC-LAG configuration differs slightly between the PE devices given they are different platforms. Demonstrating these configuration differences, and MC-LAG interoperability between the platforms, is the reason for this example. Be sure to keep track of which PE you are interacting with as you proceed through the example.
Configure the Devices
CLI Quick Configuration
To quickly configure this example, copy the following commands, paste them in a text file, remove any line breaks, change any details necessary to match your network configuration, copy and paste the commands into the CLI at the [edit] hierarchy level. When done enter commit from configuration mode to activate the changes.
Switch S0
In this example the S0 device is a QFX10000 switch.
set system host-name mc-lag_r0 set chassis aggregated-devices ethernet device-count 10 set interfaces xe-0/0/0 gigether-options 802.3ad ae0 set interfaces xe-0/0/1 gigether-options 802.3ad ae0 set interfaces xe-0/0/4 gigether-options 802.3ad ae10 set interfaces xe-0/0/5 gigether-options 802.3ad ae20 set interfaces ae0 aggregated-ether-options lacp active set interfaces ae0 unit 0 family ethernet-switching interface-mode trunk set interfaces ae0 unit 0 family ethernet-switching vlan members all set interfaces ae10 aggregated-ether-options lacp active set interfaces ae10 aggregated-ether-options lacp system-id 01:01:01:01:01:01 set interfaces ae10 aggregated-ether-options lacp admin-key 10 set interfaces ae10 aggregated-ether-options mc-ae mc-ae-id 10 set interfaces ae10 aggregated-ether-options mc-ae redundancy-group 1 set interfaces ae10 aggregated-ether-options mc-ae chassis-id 0 set interfaces ae10 aggregated-ether-options mc-ae mode active-active set interfaces ae10 aggregated-ether-options mc-ae status-control active set interfaces ae10 unit 0 family ethernet-switching vlan members vlan10 set interfaces ae20 aggregated-ether-options lacp active set interfaces ae20 aggregated-ether-options lacp system-id 02:02:02:02:02:02 set interfaces ae20 aggregated-ether-options lacp admin-key 20 set interfaces ae20 aggregated-ether-options mc-ae mc-ae-id 20 set interfaces ae20 aggregated-ether-options mc-ae redundancy-group 1 set interfaces ae20 aggregated-ether-options mc-ae chassis-id 1 set interfaces ae20 aggregated-ether-options mc-ae mode active-active set interfaces ae20 aggregated-ether-options mc-ae status-control standby set interfaces ae20 unit 0 family ethernet-switching vlan members vlan10 set interfaces irb unit 100 family inet address 10.0.1.10/24 set interfaces lo0 unit 0 family inet address 192.168.255.10/32 set multi-chassis multi-chassis-protection 10.0.1.1 interface ae0 set protocols iccp local-ip-addr 10.0.1.10 set protocols iccp peer 10.0.1.1 session-establishment-hold-time 50 set protocols iccp peer 10.0.1.1 redundancy-group-id-list 1 set protocols iccp peer 10.0.1.1 liveness-detection minimum-interval 1000 set switch-options service-id 100 set vlans vlan10 vlan-id 10 set vlans vlan100 vlan-id 100 set vlans vlan100 l3-interface irb.100
Router R1
In this example the R1 device is a MX Series router.
set system host-name mc-lag_r1 set chassis aggregated-devices ethernet device-count 10 set interfaces xe-0/0/0:0 gigether-options 802.3ad ae0 set interfaces xe-0/0/0:1 gigether-options 802.3ad ae0 set interfaces xe-0/0/1:0 gigether-options 802.3ad ae10 set interfaces xe-0/0/1:1 gigether-options 802.3ad ae20 set interfaces ae0 aggregated-ether-options lacp active set interfaces ae0 unit 0 family bridge interface-mode trunk set interfaces ae0 unit 0 family bridge vlan-id-list 1-1000 set interfaces ae10 aggregated-ether-options lacp active set interfaces ae10 aggregated-ether-options lacp system-id 01:01:01:01:01:01 set interfaces ae10 aggregated-ether-options lacp admin-key 10 set interfaces ae10 aggregated-ether-options mc-ae mc-ae-id 10 set interfaces ae10 aggregated-ether-options mc-ae redundancy-group 1 set interfaces ae10 aggregated-ether-options mc-ae chassis-id 1 set interfaces ae10 aggregated-ether-options mc-ae mode active-active set interfaces ae10 aggregated-ether-options mc-ae status-control standby set interfaces ae10 unit 0 multi-chassis-protection 10.0.1.10 interface ae0.0 set interfaces ae10 unit 0 family bridge interface-mode access set interfaces ae10 unit 0 family bridge vlan-id 10 set interfaces ae20 aggregated-ether-options lacp active set interfaces ae20 aggregated-ether-options lacp system-id 02:02:02:02:02:02 set interfaces ae20 aggregated-ether-options lacp admin-key 20 set interfaces ae20 aggregated-ether-options mc-ae mc-ae-id 20 set interfaces ae20 aggregated-ether-options mc-ae redundancy-group 1 set interfaces ae20 aggregated-ether-options mc-ae chassis-id 0 set interfaces ae20 aggregated-ether-options mc-ae mode active-active set interfaces ae20 aggregated-ether-options mc-ae status-control active set interfaces ae20 unit 0 multi-chassis-protection 10.0.1.10 interface ae0.0 set interfaces ae20 unit 0 family bridge interface-mode access set interfaces ae20 unit 0 family bridge vlan-id 10 set interfaces irb unit 100 family inet address 10.0.1.1/24 set interfaces lo0 unit 0 family inet address 192.168.255.1/32 set protocols iccp local-ip-addr 10.0.1.1 set protocols iccp peer 10.0.1.10 session-establishment-hold-time 50 set protocols iccp peer 10.0.1.10 redundancy-group-id-list 1 set protocols iccp peer 10.0.1.10 liveness-detection minimum-interval 1000 set bridge-domains vlan10 vlan-id 10 set bridge-domains vlan100 vlan-id 100 set bridge-domains vlan100 routing-interface irb.100 set switch-options service-id 10
Server 1
The servers in this example are MX routers. While this example focuses on configuring MC-LAG on the PE devices, the server configuration is provided for completeness. In this example server 2 has the same configuration, with the exception that it is assigned IPv4 address 172.16.1.2/24 and IPv6 address 2001:db8:172:16:1::2 .
set system host-name server1 set chassis aggregated-devices ethernet device-count 10 set interfaces xe-0/0/0:0 gigether-options 802.3ad ae10 set interfaces xe-0/0/0:1 gigether-options 802.3ad ae10 set interfaces ae10 aggregated-ether-options lacp active set interfaces ae10 unit 0 family inet address 172.16.1.1/24 set interfaces ae10 unit 0 family inet6 address 2001:db8:172:16:1::1/64
Configure the S0 Switch
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode.
To configure Switch S0:
Specify the number of aggregated Ethernet devices supported on the chassis. Only 3 LAGs are needed for the example, but having unused AE bundle capacity causes no issues.
[edit chassis] user@S0# set aggregated-devices ethernet device-count 10
Configure the loopback (if desired, it's not used in this example), and IRB interfaces, along with the IRB interface's VLAN. In this example the IRB interface is used to anchor the ICCP session and is assigned to VLAN 100.
[edit] user@S0# set interfaces lo0 unit 0 family inet address 192.168.255.10/32 user@S0# set interfaces irb unit 100 family inet address 10.0.1.10/24 user@S0# set vlans vlan100 vlan-id 100 user@S0# set vlans vlan100 l3-interface irb.100
Configure the ae0 interface to support ICCP and ICL. Be sure to include all MC-LAG VLANs, as well as the IRB VLAN used to support ICCP. You can specify a list of VLANs, but in this example the
allkeyword is used to quickly ensure all VLANs are supported over the ae0 interface. In this example only two VLANS are required on the ISL. The MC-LAG VLAN (10) and VLAN 100 that supports ICCP.For proper operation unit 0 must be used for the ICL link on the QFX Series switch because, unlike an MX Series router, they don't support unit-level specification of the ICL link.
Note:The QFX Series switch supports only interface level specification of the ICL link and assumes the use of unit 0. Its is therefore important that you list all MC-LAG VLANs under unit 0 as is shown. The MX Series router can support both global or unit level specification of the ICL. The latter method is shown later in this example.
[edit interfaces] user@S0# set xe-0/0/0 gigether-options 802.3ad ae0 user@S0# set xe-0/0/1 gigether-options 802.3ad ae0 user@S0# set ae0 aggregated-ether-options lacp active user@S0# set ae0 unit 0 family ethernet-switching interface-mode trunk user@S0# set ae0 unit 0 family ethernet-switching vlan members all
Specify the member interfaces used for the server facing aggregated Ethernet bundles.
[edit interfaces] user@S0# set xe-0/0/4 gigether-options 802.3ad ae10 user@S0# set xe-0/0/5 gigether-options 802.3ad ae20
Configure the LACP and MC-LAG parameters for the MC-LAG that connects to server 1 (ae10). The MC-LAG is set for active-active mode and, in this example, S0 is set to be the active MC-LAG node using the
status-control activestatement. If S0 fails R1 will take over as the active node. Thechassis-idstatement is used by LACP for calculating the port number of the MC-LAG's physical member links. By convention the active node is assigned a chassis ID of 0 while the standby node is assigned 1. In a later step you configure R1 to be the active node for the MC-LAG connected to server 2.The multichassis aggregated Ethernet identification number (mc-ae-id) specifies which link aggregation group the aggregated Ethernet interface belongs to. The ae10 interfaces on S0 and R1 are configured with mc-ae-id 10. In like fashion the ae20 interface is configured with mc-ae-id 20 .
The
redundancy-group 1statement is used by ICCP to associate multiple chassis that perform similar redundancy functions and to establish a communication channel so that applications on peering chassis can send messages to each other. The ae10 and ae20 interfaces on S0 and R1 are configured with the same redundancy group, redundancy-group 1.The
modestatement indicates whether an MC-LAG is in active-standby mode or active-active mode. Chassis that are in the same group must be in the same mode.[edit interfaces ae10] user@S0# set aggregated-ether-options lacp active user@S0# set aggregated-ether-options lacp system-id 01:01:01:01:01:01 user@S0# set aggregated-ether-options lacp admin-key 10 user@S0# set aggregated-ether-options mc-ae mc-ae-id 10 user@S0# set aggregated-ether-options mc-ae redundancy-group 1 user@S0# set aggregated-ether-options mc-ae chassis-id 0 user@S0# set aggregated-ether-options mc-ae mode active-active user@S0# set aggregated-ether-options mc-ae status-control active user@S0# set unit 0 family ethernet-switching vlan members vlan10
Configure the LACP and MC-LAG parameters for the MC-LAG that connects to server 2 (ae20). The MC-LAG is set for active-active mode and, in this example, S0 is set to be the standby MC-LAG node. In the event of R1 failure S0 takes over as the active node.
[edit interfaces ae20] user@S0# set aggregated-ether-options lacp active user@S0# set interfaces ae20 aggregated-ether-options lacp system-id 02:02:02:02:02:02 user@S0# set aggregated-ether-options lacp admin-key 20 user@S0# set aggregated-ether-options mc-ae mc-ae-id 20 user@S0# set aggregated-ether-options mc-ae redundancy-group 1 user@S0# set aggregated-ether-options mc-ae chassis-id 1 user@S0# set aggregated-ether-options mc-ae mode active-active user@S0# set aggregated-ether-options mc-ae status-control standby user@S0# set unit 0 family ethernet-switching vlan members v10
Configure the VLAN for the AE 10 and AE 20 bundles.
[edit] user@S0# set vlans vlan10 vlan-id 10
Configure the switch-options service ID.
The ports within a bridge domain share the same flooding or broadcast characteristics in order to perform Layer 2 bridging.
The global
service-idstatement is required to link related bridge domains across peers (in this case S0 and R1), and must be configured with the same value.[edit switch-options] user@S0# set service-id 100
Configure the ICCP parameters. The
localandpeerparameters are set to reflect the values configured previously for the local and remote IRB interfaces, respectively. Configuring ICCP peering to an IRB (or loopback) interface ensures that the ICCP session can remain up in the face of individual link failures.[edit protocols iccp] user@S0# set local-ip-addr 10.0.1.10 user@S0# set peer 10.0.1.1 session-establishment-hold-time 50 user@S0# set peer 10.0.1.1 redundancy-group-id-list 1 user@S0# set peer 10.0.1.10 liveness-detection minimum-interval 1000
Configure the service ID at the global level. You must configure the same unique network-wide service ID in the set of PE routers providing the service. This service ID is required when the multichassis aggregated Ethernet interfaces are part of a bridge domain.
[edit switch-options] user@S0# set service-id 100
Configure the ae0 interface to function as the ICL for the MC-LAG bundles supported by S0.
[edit multi-chassis] user@S0# set multi-chassis-protection 10.0.1.1 interface ae0
Note:On the QFX Series switch, you must specify a physical interface device as the ICL protection link. Logical unit level mapping of an ICL to a MC-LAG bundle is not supported. For proper operation you must ensure that unit 0 is used to support the bridging of the MC-LAG VLANs on the ICL.
S0 Results
From configuration mode, confirm your configuration by entering the show command. If the output does not display the intended configuration, repeat the instructions in this example to correct the configuration.
[edit]
user@S0# show
. . .chassis {
aggregated-devices {
ethernet {
device-count 10;
}
}
}
interfaces {
xe-0/0/0 {
gigether-options {
802.3ad ae0;
}
}
xe-0/0/1 {
gigether-options {
802.3ad ae0;
}
}
xe-0/0/4 {
gigether-options {
802.3ad ae10;
}
}
xe-0/0/5 {
gigether-options {
802.3ad ae20;
}
}
ae0 {
aggregated-ether-options {
lacp {
active;
}
}
unit 0 {
family ethernet-switching {
interface-mode trunk;
vlan {
members all;
}
}
}
}
ae10 {
aggregated-ether-options {
lacp {
active;
system-id 01:01:01:01:01:01;
admin-key 10;
}
mc-ae {
mc-ae-id 10;
redundancy-group 1;
chassis-id 0;
mode active-active;
status-control active;
}
}
unit 0 {
family ethernet-switching {
vlan {
members vlan10;
}
}
}
}
ae20 {
aggregated-ether-options {
lacp {
active;
system-id 02:02:02:02:02:02;
admin-key 20;
}
mc-ae {
mc-ae-id 20;
redundancy-group 1;
chassis-id 1;
mode active-active;
status-control standby;
}
}
unit 0 {
family ethernet-switching {
vlan {
members vlan10;
}
}
}
}
irb {
unit 100 {
family inet {
address 10.0.1.10/24;
}
}
}
lo0 {
unit 0 {
family inet {
address 192.168.255.10/32;
}
}
}
}
multi-chassis {
multi-chassis-protection 10.0.1.1 {
interface ae0;
}
}
protocols {
iccp {
local-ip-addr 10.0.1.10;
peer 10.0.1.1 {
session-establishment-hold-time 50;
redundancy-group-id-list 1;
liveness-detection {
minimum-interval 1000;
}
}
}
}
switch-options {
service-id 100;
}
vlans {
vlan10 {
vlan-id 10;
}
vlan100 {
vlan-id 100;
l3-interface irb.100;
}
}
Configure the R1 Router
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode.
To configure Router R1:
Specify the number of aggregated Ethernet interfaces to be created on the chassis. Only 3 LAGs are needed, but having additional LAG capacity causes no issue.
[edit chassis] user@R1# set aggregated-devices ethernet device-count 10
Configure the loopback (if desired, it's not needed in this example) and IRB interfaces, along with IRB interface's VLAN. In this example the IRB interface is used to anchor the ICCP session.
[edit] user@R1# set interfaces lo0 unit 0 family inet address 192.168.255.1/32 user@R1# set interfaces irb unit 100 family inet address 10.0.1.1/24 user@R1# set bridge-domains vlan100 vlan-id 100 user@R1# set bridge-domains vlan100 routing-interface irb.100
Configure the ae0 interface to support both ICL and ICCP functionality. A
vlan-id-listis used to support a range of VLANs that include VLAN 100 for ICCP and VLAN 10 for the MC-LAGs. Unlike the QFX Series switch, theallused as a shortcut to support all VLANs is not supported on MX Series routers.Note:The ICL link must support all MC-LAG VLANs as well as the VLAN used for ICCP. In this example this means at a minimum you must list VLAN 10 and VLAN 100 given the ae0 link supports both ISL and ICCP in this example.
[edit interfaces] user@R1# set xe-0/0/0:0 gigether-options 802.3ad ae0 user@R1# set xe-0/0/0:1 gigether-options 802.3ad ae0 user@R1# set ae0 aggregated-ether-options lacp active user@R1# set ae0 unit 0 family bridge interface-mode trunk user@R1# set ae0 unit 0 family bridge vlan-id-list 2-1000
Specify the members to be included within the server facing aggregated Ethernet bundles at R0.
[edit interfaces] user@R1# set xe-0/0/1:0 gigether-options 802.3ad ae10 user@R1# set xe-0/0/1:1 gigether-options 802.3ad ae20
Configure the LACP and MC-LAG parameters for the MC-LAG that connects to server 1 (ae10). The MC-LAG is set for active-active mode and, in this example, R1 is set to be the standby MC-LAG node using the
status-control standbystatement. This makes S0 the active MC-LAG node for ae10 when it's operational. If S0 fails R1 takes over as the active node. Thechassis-idstatement is used by LACP for calculating the port number of the MC-LAG's physical member links. By convention the active node is assigned chassis ID of 0 while the standby node is assigned 1.The multichassis aggregated Ethernet identification number (
mc-ae-id) specifies which link aggregation group the aggregated Ethernet interface belongs to. The ae10 interfaces on S0 and R1 are configured with mc-ae-id 10. In like fashion the ae20 interface is configured with mc-ae-id 20.The
redundancy-group 1statement is used by ICCP to associate multiple chassis that perform similar redundancy functions and to establish a communication channel so that applications on peering chassis can send messages to each other. The ae10 and ae20 interfaces on S0 and R1 are configured with the same redundancy group, redundancy-group 1.The
modestatement indicates whether an MC-LAG is in active-standby mode or active-active mode. Chassis that are in the same group must be in the same mode.This example demonstrates MX Series router support for the specification of the ICL interface at the unit level (under the MC-LAG unit as shown below). If desired the ICL protection link can be specified globally at the physical device level (with unit 0 assumed) at the
[edit multi-chassis multi-chassis-protection]hierarchy, as was shown for the QFX Series switch S0.[edit interfaces ae10] user@R1# set aggregated-ether-options lacp active user@R1# set aggregated-ether-options lacp system-id 01:01:01:01:01:01 user@R1# set aggregated-ether-options lacp admin-key 10 user@R1# set aggregated-ether-options mc-ae mc-ae-id 10 user@R1# set aggregated-ether-options mc-ae redundancy-group 1 user@R1# set aggregated-ether-options mc-ae chassis-id 1 user@R1# set aggregated-ether-options mc-ae mode active-active user@R1# set aggregated-ether-options mc-ae status-control standby user@R1# set ae10 unit 0 family bridge interface-mode access user@R1# set ae10 unit 0 family bridge vlan-id 10 user@R1# set ae10 unit 0 multi-chassis-protection 10.0.1.10 interface ae0.0
Note:On the MX platform you can specify the ICL interface using either a global level physical device declaration at the
edit multi-chassis multi-chassis-protectionhierarchy, or as shown here, at the logical unit level within the MC-LAG bundle. QFX Series switches support only global level specification of the physical device.Configure the LACP and MC-LAG parameters for the MC-LAG that connects to server 2 (ae20). The MC-LAG is set for active-active mode and, In this example, R1 is set to be the active MC-LAG node. In the event of R1 failure S0 takes over as the active node for the ae20 MC-LAG.
[edit interfaces ae20] user@R1# set aggregated-ether-options lacp active user@R1# set aggregated-ether-options lacp system-id 02:02:02:02:02:02 user@R1# set aggregated-ether-options lacp admin-key 20 user@R1# set aggregated-ether-options mc-ae mc-ae-id 20 user@R1# set aggregated-ether-options mc-ae redundancy-group 1 user@R1# set aggregated-ether-options mc-ae chassis-id 0 user@R1# set aggregated-ether-options mc-ae mode active-active user@R1# set aggregated-ether-options mc-ae status-control active user@R1# set unit 0 family bridge interface-mode access user@R1# set unit 0 family bridge vlan-id 10 user@R1# set unit 0 multi-chassis-protection 10.0.1.10 interface ae0.0
Configure the VLAN for the ae10 and ae20 bundles.
Note:On the MX Series router you define VLANs under the
[edit bridge-domains]hierarchy. On the QFX Series switch, this is done at the[edit vlans]hierarchy. This is one of the differences between the QFX Series switch and the MX Series router.[edit bridge-domains] user@R1# set vlan10 vlan-id 10
Configure the switch-options service ID.
The ports within a bridge domain share the same flooding or broadcast characteristics in order to perform Layer 2 bridging.
The global
service-idstatement is required to link related bridge domains across peers (in this case S0 and R1), and must be configured with the same value.[edit switch-options] user@R1# set service-id 100
Configure the ICCP parameters. The
localandpeerparameters are set to reflect the values configured previously on the local and remote IRB interfaces, respectively. Configuring ICCP peering to an IRB (or loopback) interface ensures that the ICCP session can remain up in the face of individual link failures.[edit protocols iccp] user@R1# set local-ip-addr 10.0.1.1 user@R1# set peer 10.0.1.10 session-establishment-hold-time 50 user@R1# set peer 10.0.1.10 redundancy-group-id-list 1 user@R1# set peer 10.0.1.10 liveness-detection minimum-interval 1000
Configure the service ID at the global level. You must configure the same unique network-wide configuration for a service in the set of PE devices providing the service. This service ID is required if the multichassis aggregated Ethernet interfaces are part of a bridge domain.
[edit switch-options] user@R1# set service-id 100
R1 Results
From configuration mode, confirm your configuration by entering the show command. If the output does not display the intended configuration, repeat the instructions in this example to correct the configuration.
[edit]
user@R1# show
. . .
chassis {
aggregated-devices {
ethernet {
device-count 10;
}
}
}
interfaces {
xe-0/0/0:0 {
gigether-options {
802.3ad ae0;
}
}
xe-0/0/0:1 {
gigether-options {
802.3ad ae0;
}
}
xe-0/0/0:2 {
gigether-options {
802.3ad ae1;
}
}
xe-0/0/0:3 {
gigether-options {
802.3ad ae1;
}
}
xe-0/0/1:0 {
gigether-options {
802.3ad ae10;
}
}
xe-0/0/1:1 {
gigether-options {
802.3ad ae20;
}
}
ae0 {
aggregated-ether-options {
lacp {
active;
}
}
unit 0 {
family bridge {
interface-mode trunk;
vlan-id-list 2-1000;
}
}
}
ae10 {
aggregated-ether-options {
lacp {
active;
system-id 01:01:01:01:01:01;
admin-key 10;
}
mc-ae {
mc-ae-id 10;
redundancy-group 1;
chassis-id 1;
mode active-active;
status-control standby;
}
}
unit 0 {
multi-chassis-protection 10.0.1.10 {
interface ae0.0;
}
family bridge {
interface-mode access;
vlan-id 10;
}
}
}
ae20 {
aggregated-ether-options {
lacp {
active;
system-id 02:02:02:02:02:02;
admin-key 20;
}
mc-ae {
mc-ae-id 20;
redundancy-group 1;
chassis-id 0;
mode active-active;
status-control active;
}
}
unit 0 {
multi-chassis-protection 10.0.1.10 {
interface ae0.0;
}
family bridge {
interface-mode access;
vlan-id 10;
}
}
}
irb {
unit 100 {
family inet {
address 10.0.1.1/24;
}
}
}
lo0 {
unit 0 {
family inet {
address 192.168.255.1/32;
}
}
}
}
protocols {
iccp {
local-ip-addr 10.0.1.1;
peer 10.0.1.10 {
session-establishment-hold-time 50;
redundancy-group-id-list 1;
liveness-detection {
minimum-interval 1000;
}
}
}
}
bridge-domains {
vlan10 {
vlan-id 10;
}
vlan100 {
vlan-id 100;
routing-interface irb.100;
}
}
switch-options {
service-id 100;
}
Verification
Confirm that the configuration is working properly by running the following operational mode commands:
show iccpshow interfaces mc-ae \show interfaces aeX (0, 10, and 20)On the QFX Series switch use the
show vlansand theshow ethernet-switching tablecommandsOn the MX Series router use the
show bridge mac-tablecommandVerify Layer 2 connectivity between the servers
Select verification commands are run to show the expected output. We start with the show iccp command on S0. If the ICCP session is not established issue the ping command between the IRB interfaces to ensure the expected Layer 2 connectivity over the ae0 ICCP/ICL link:
user@S0# show iccp
Redundancy Group Information for peer 10.0.1.1
TCP Connection : Established
Liveliness Detection : Up
Redundancy Group ID Status
1 Up
Client Application: l2ald_iccpd_client
Redundancy Group IDs Joined: 1
Client Application: lacpd
Redundancy Group IDs Joined: 1 Next, we run the show interfaces mc-ae extensive command on S0. The output confirms the expected active-active status and status control active/standby state for both MC-LAGs. Recall that S0 is the status control active node for ae10 and the standby node for ae20 in this example:
user@S0# show interfaces mc-lag extensive
Member Link : ae10
Current State Machine's State: mcae active state
Local Status : active
Local State : up
Peer Status : active
Peer State : up
Logical Interface : ae10.0
Topology Type : bridge
Local State : up
Peer State : up
Peer Ip/MCP/State : 10.0.1.1 ae0.0 up
MCAE Configuration
Redundancy Group : 1
MCAE ID : 10
MCAE Mode : active_active
Status Control : active
Chassis ID : 0
LACP Configuration
System ID : 01:01:01:01:01:01
Admin Key : 10
LACP Information
Local Partner System ID : 2c:6b:f5:20:55:c0
Peer Partner System ID : 2c:6b:f5:20:55:c0
Member Link : ae20
Current State Machine's State: mcae active state
Local Status : active
Local State : up
Peer Status : active
Peer State : up
Logical Interface : ae20.0
Topology Type : bridge
Local State : up
Peer State : up
Peer Ip/MCP/State : 10.0.1.1 ae0.0 up
MCAE Configuration
Redundancy Group : 1
MCAE ID : 20
MCAE Mode : active_active
Status Control : standby
Chassis ID : 1
LACP Configuration
System ID : 02:02:02:02:02:02
Admin Key : 20
LACP Information
Local Partner System ID : 2c:6b:f5:13:24:c0
Peer Partner System ID : 2c:6b:f5:13:24:c0
The show interfaces command is used to confirm the ICCP/ICL, and MC-LAG bundles are up. For brevity only the output for the ae10 bundle is shown. All AE interfaces (ae0, ae10, and ae20) should be up:
user@S0# show interfaces ae10
Physical interface: ae10 (MC-AE-10, active), Enabled, Physical link is Up
Interface index: 670, SNMP ifIndex: 561
Link-level type: Ethernet, MTU: 1514, Speed: 10Gbps, BPDU Error: None, Ethernet-Switching Error: None, MAC-REWRITE Error: None,
Loopback: Disabled, Source filtering: Disabled, Flow control: Disabled, Minimum links needed: 1, Minimum bandwidth needed: 1bps
Device flags : Present Running
Interface flags: SNMP-Traps Internal: 0x4000
Current address: 02:05:86:72:a9:f7, Hardware address: 02:05:86:72:a9:f7
Last flapped : 2021-04-08 11:56:43 PDT (02:37:24 ago)
Input rate : 0 bps (0 pps)
Output rate : 992 bps (0 pps)
Logical interface ae10.0 (Index 578) (SNMP ifIndex 562)
Flags: Up SNMP-Traps 0x24024000 Encapsulation: Ethernet-Bridge
Statistics Packets pps Bytes bps
Bundle:
Input : 9454 0 963310 776
Output: 9429 0 1204640 968
Adaptive Statistics:
Adaptive Adjusts: 0
Adaptive Scans : 0
Adaptive Updates: 0
Protocol eth-switch, MTU: 1514
The show vlans detail and show ethernet-switching table commands are used to confirm VLAN definition and mapping for the ICCP/ICL, and MC-LAG interfaces on the S0 device:
user@S0# show vlans detail
Routing instance: default-switch
VLAN Name: vlan10 State: Active
Tag: 10
Internal index: 3, Generation Index: 3, Origin: Static
MAC aging time: 300 seconds
VXLAN Enabled : No
Interfaces:
ae0.0*,tagged,trunk
ae10.0*,untagged,access
ae20.0*,untagged,access
Number of interfaces: Tagged 1 , Untagged 2
Total MAC count: 2
Routing instance: default-switch
VLAN Name: vlan100 State: Active
Tag: 100
Internal index: 2, Generation Index: 2, Origin: Static
MAC aging time: 300 seconds
Layer 3 interface: irb.100
VXLAN Enabled : No
Interfaces:
ae0.0*,tagged,trunk
Number of interfaces: Tagged 1 , Untagged 0
Total MAC count:
show ethernet-switching table
MAC flags (S - static MAC, D - dynamic MAC, L - locally learned, P - Persistent static, C - Control MAC
SE - statistics enabled, NM - non configured MAC, R - remote PE MAC, O - ovsdb MAC)
Ethernet switching table : 2 entries, 2 learned
Routing instance : default-switch
Vlan MAC MAC Age Logical NH RTR
name address flags interface Index ID
vlan10 2c:6b:f5:13:24:c2 DLR - ae20.0 0 0
vlan10 2c:6b:f5:20:55:c3 DL - ae10.0 0 0
Lastly, you ping between server 1 and 2 to confirm Layer 2 connectivity:
user@Server1# ping 172.16.1.2 count 2 PING 172.16.1.2 (172.16.1.2): 56 data bytes 64 bytes from 172.16.1.2: icmp_seq=0 ttl=64 time=56.529 ms 64 bytes from 172.16.1.2: icmp_seq=1 ttl=64 time=117.029 ms --- 172.16.1.2 ping statistics --- 2 packets transmitted, 2 packets received, 0% packet loss round-trip min/avg/max/stddev = 56.529/86.779/117.029/30.250 ms
user@Server1# ping 2001:db8:172:16:1::2 count 2 PING6(56=40+8+8 bytes) 2001:db8:172:16:1::1 --> 2001:db8:172:16:1::2 16 bytes from 2001:db8:172:16:1::2, icmp_seq=0 hlim=64 time=154.164 ms 16 bytes from 2001:db8:172:16:1::2, icmp_seq=1 hlim=64 time=167.032 ms --- 2001:db8:172:16:1::2 ping6 statistics --- 2 packets transmitted, 2 packets received, 0% packet loss round-trip min/avg/max/std-dev = 154.164/160.598/167.032/6.434 ms
Example: Configuring Multichassis Link Aggregation on EX9200 Switches in the Core for Campus Networks
MC-LAG in a campus configuration allows you to bond two or more physical links into a logical link between core-aggregation or aggregation-access switches. MC-LAG improves availability by providing active/active links between multiple switches over a standard Link Aggregation Group (LAG), eliminates the need for the Spanning Tree Protocol (STP), and provides faster Layer 2 convergence upon link and device failures. With multiple active network paths, MC-LAG enables you to load balance traffic across the multiple physical links. If a link fails, the traffic can be forwarded through the other available links and the aggregated link remains available.
- Requirements
- Overview
- Configuration
- (Optional) Configuring RSTP
- (Optional) Configuring IGMP Snooping
- (Optional) Configuring VRRP
- (Optional) Configuring MAC Address Synchronization
- (Optional) Configuring OSPF
- (Optional) Configuring PIM
- (Optional) Configuring DHCP Relay
- Verification
Requirements
This example uses the following hardware and software components:
-
Junos OS Release 13.2R5.10 for EX Series
-
Two EX9200 switches
This configuration example has been tested using the software release listed and is assumed to work on all later releases.
Before you configure an MC-LAG, be sure that you understand how to:
-
Configure aggregated Ethernet interfaces on a switch. See Configuring an Aggregated Ethernet Interface.
-
Configure the Link Aggregation Control Protocol (LACP) on aggregated Ethernet interfaces on a switch. See Configuring Aggregated Ethernet LACP (CLI Procedure).
Overview
In this example, you configure an MC-LAG across two switches, consisting of two aggregated Ethernet interfaces, an interchassis link-protection link (ICL-PL), multichassis protection link for the ICL-PL, ICCP for the peers hosting the MC-LAG, and Layer 3 connectivity between MC-LAG peers. Layer 3 connectivity is required for ICCP.
Topology
The topology used in this example consists of two switches hosting an MC-LAG. The two switches are connected to an EX4600 switch and an MX80 router. Figure 4 shows the topology of this example.
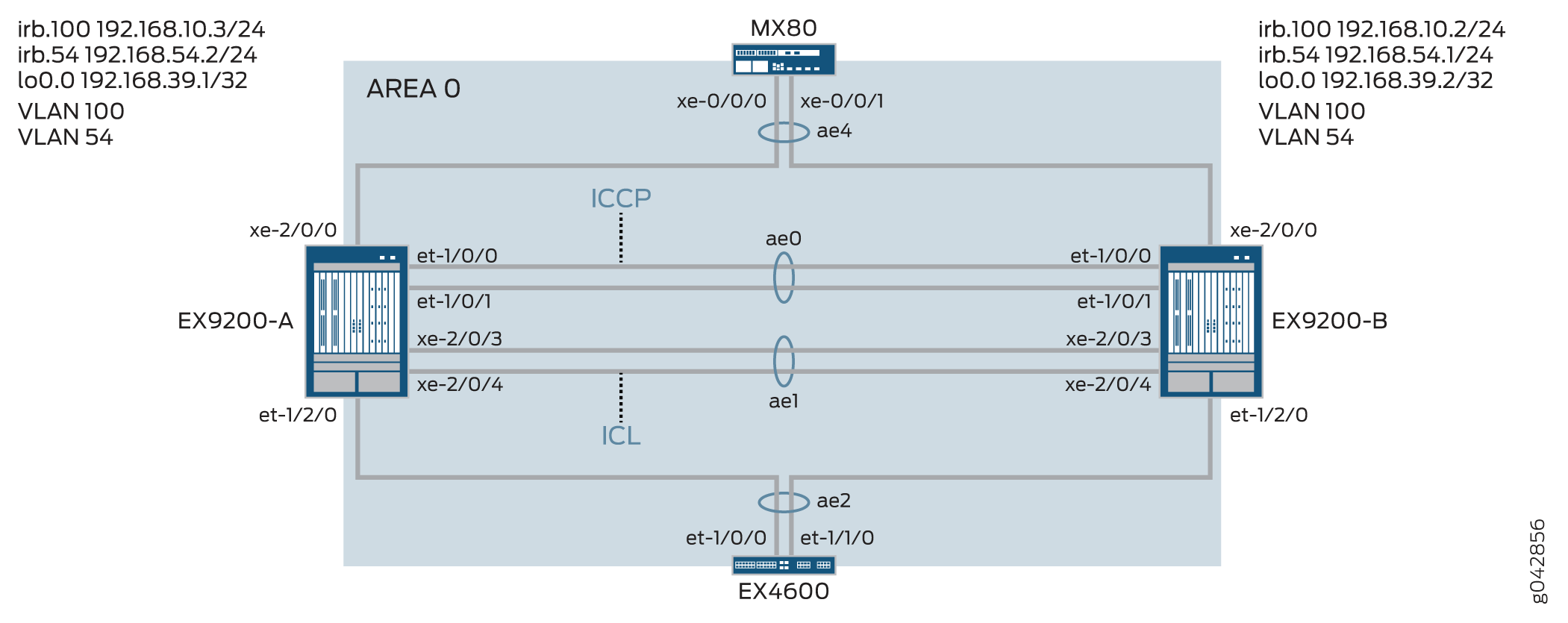
Table 1 details the topology used in this configuration example.
| Hostname | Base Hardware | Multichassis Link Aggregation Group |
|---|---|---|
|
EX9200-A EX9200-B |
EX9200 EX9200 |
ae0 is configured as an aggregated Ethernet interface, and is used as an ICCP link. The following interfaces are part of ae0: et-1/0/0 and et-1/0/1 on EX9200-A and et-1/0/0 and et-1/0/1 on EX9200-B. ae1 is configured as an aggregated Ethernet interface and is used as an ICL link, and the following two interfaces are part of ae1: xe-2/0/3 and xe-2/0/4 on EX9200-A and xe-2/0/3 and xe-2/0/4 on EX9200-B. ae2 is configured as an MC-LAG, and the following interfaces are part of ae2: et-1/2/0 on EX9200-A and et-1/2/0 on EX9200-B. ae4 is configured as an MC-LAG, and the following interfaces are part of ae4: xe-2/0/0 on EX9200-A and xe-2/0/0 on EX9200-B. |
Configuration
CLI Quick Configuration
To quickly configure this example, copy the
following commands, paste them in a text file, remove any line breaks,
change any details necessary to match your network configuration,
copy and paste the commands into the CLI at the [edit] hierarchy
level, and then enter commit from configuration
mode.
EX9200-A
set chassis aggregated-devices ethernet device-count 20 set interfaces et-1/0/0 ether-options 802.3ad ae0 set interfaces et-1/0/1 ether-options 802.3ad ae0 set interfaces et-1/2/0 ether-options 802.3ad ae2 set interfaces xe-2/0/3 hold-time up 100 set interfaces xe-2/0/3 hold-time down 9000 set interfaces xe-2/0/3 ether-options 802.3ad ae1 set interfaces xe-2/0/4 hold-time up 100 set interfaces xe-2/0/4 hold-time down 9000 set interfaces xe-2/0/4 ether-options 802.3ad ae1 set interfaces xe-2/0/0 ether-options 802.3ad ae4 set interfaces ae0 aggregated-ether-options lacp active set interfaces ae0 aggregated-ether-options lacp periodic fast set interfaces ae0 unit 0 family inet address 192.168.90.1/24 set interfaces ae1 description ICL-LINK set interfaces ae1 aggregated-ether-options lacp active set interfaces ae1 aggregated-ether-options lacp periodic fast set interfaces ae1 unit 0 family ethernet-switching interface-mode trunk set interfaces ae1 unit 0 family ethernet-switching vlan members all set interfaces ae2 aggregated-ether-options lacp active set interfaces ae2 aggregated-ether-options lacp periodic fast set interfaces ae2 aggregated-ether-options lacp system-id 00:01:02:03:04:05 set interfaces ae2 aggregated-ether-options lacp admin-key 3 set interfaces ae2 aggregated-ether-options mc-ae mc-ae-id 3 set interfaces ae2 aggregated-ether-options mc-ae redundancy-group 1 set interfaces ae2 aggregated-ether-options mc-ae chassis-id 0 set interfaces ae2 aggregated-ether-options mc-ae mode active-active set interfaces ae2 aggregated-ether-options mc-ae status-control active set interfaces ae2 aggregated-ether-options mc-ae init-delay-time 520 set interfaces ae2 aggregated-ether-options mc-ae events iccp-peer-down prefer-status-control-active set interfaces ae2 unit 0 family ethernet-switching interface-mode trunk set interfaces ae2 unit 0 family ethernet-switching vlan members all set interfaces ae4 aggregated-ether-options lacp active set interfaces ae4 aggregated-ether-options lacp periodic fast set interfaces ae4 aggregated-ether-options lacp system-id 00:01:02:03:04:06 set interfaces ae4 aggregated-ether-options lacp admin-key 7 set interfaces ae4 aggregated-ether-options mc-ae mc-ae-id 7 set interfaces ae4 aggregated-ether-options mc-ae redundancy-group 1 set interfaces ae4 aggregated-ether-options mc-ae chassis-id 0 set interfaces ae4 aggregated-ether-options mc-ae mode active-active set interfaces ae4 aggregated-ether-options mc-ae status-control active set interfaces ae4 aggregated-ether-options mc-ae init-delay-time 520 set interfaces ae4 aggregated-ether-options mc-ae events iccp-peer-down prefer-status-control-active set interfaces ae4 unit 0 family ethernet-switching interface-mode trunk set interfaces ae4 unit 0 family ethernet-switching vlan members v54 set vlans rack_1 vlan-id 100 set vlans rack_1 vlan-id 54 set vlans rack_1 l3-interface irb.100 set vlans v54 l3-interface irb.54 set interfaces irb unit 54 family inet address 192.168.54.2/24 arp 192.168.54.1 l2-interface ae1.0 set interfaces irb unit 54 family inet address 192.168.54.2/24 arp 192.168.54.1 mac 3c:8a:b0:85:78:70 set interfaces irb unit 100 family inet address 192.168.10.3/24 arp 192.168.10.2 l2-interface ae1.0 set interfaces irb unit 100 family inet address 192.168.10.3/24 arp 192.168.10.2 mac 3c:8a:b0:85:78:70 set interfaces lo0 unit 0 family inet address 192.168.39.1/32 set protocols iccp local-ip-addr 192.168.39.1 set protocols iccp peer 192.168.39.2 session-establishment-hold-time 50 set protocols iccp peer 192.168.39.2 redundancy-group-id-list 1 set protocols iccp peer 192.168.39.2 backup-liveness-detection backup-peer-ip 10.105.5.6 set protocols iccp peer 192.168.39.2 liveness-detection minimum-interval 2000 set protocols iccp peer 192.168.39.2 liveness-detection multiplier 4 set multi-chassis multi-chassis-protection 192.168.39.2 interface ae1 set switch-options service-id 1
EX9200-B
set chassis aggregated-devices ethernet device-count 20 set interfaces et-1/0/0 ether-options 802.3ad ae0 set interfaces et-1/0/1 ether-options 802.3ad ae0 set interfaces et-1/2/0 ether-options 802.3ad ae2 set interfaces xe-2/0/0 ether-options 802.3ad ae4 set interfaces xe-2/0/3 hold-time up 100 set interfaces xe-2/0/3 hold-time down 9000 set interfaces xe-2/0/3 ether-options 802.3ad ae1 set interfaces xe-2/0/4 hold-time up 100 set interfaces xe-2/0/4 hold-time down 9000 set interfaces xe-2/0/4 ether-options 802.3ad ae1 set interfaces ae0 aggregated-ether-options lacp active set interfaces ae0 aggregated-ether-options lacp periodic fast set interfaces ae0 unit 0 family inet address 192.168.90.2/24 set interfaces ae1 description ICL-LINK set interfaces ae1 aggregated-ether-options lacp active set interfaces ae1 aggregated-ether-options lacp periodic fast set interfaces ae1 unit 0 family ethernet-switching interface-mode trunk set interfaces ae1 unit 0 family ethernet-switching vlan members all set interfaces ae2 aggregated-ether-options lacp active set interfaces ae2 aggregated-ether-options lacp periodic fast set interfaces ae2 aggregated-ether-options lacp system-id 00:01:02:03:04:05 set interfaces ae2 aggregated-ether-options lacp admin-key 3 set interfaces ae2 aggregated-ether-options mc-ae mc-ae-id 3 set interfaces ae2 aggregated-ether-options mc-ae redundancy-group 1 set interfaces ae2 aggregated-ether-options mc-ae chassis-id 1 set interfaces ae2 aggregated-ether-options mc-ae mode active-active set interfaces ae2 aggregated-ether-options mc-ae init-delay-time 520 set interfaces ae2 aggregated-ether-options mc-ae events set interfaces ae2 aggregated-ether-options mc-ae status-control standby set interfaces ae2 unit 0 family ethernet-switching interface-mode trunk set interfaces ae2 unit 0 family ethernet-switching vlan members all set interfaces ae4 aggregated-ether-options lacp active set interfaces ae4 aggregated-ether-options lacp periodic fast set interfaces ae4 aggregated-ether-options lacp system-id 00:01:02:03:04:06 set interfaces ae4 aggregated-ether-options lacp admin-key 7 set interfaces ae4 aggregated-ether-options mc-ae mc-ae-id 7 set interfaces ae4 aggregated-ether-options mc-ae redundancy-group 1 set interfaces ae4 aggregated-ether-options mc-ae chassis-id 1 set interfaces ae4 aggregated-ether-options mc-ae mode active-active set interfaces ae4 aggregated-ether-options mc-ae status-control standby set interfaces ae4 aggregated-ether-options mc-ae init-delay-time 520 set interfaces ae4 unit 0 family ethernet-switching interface-mode trunk set interfaces ae4 unit 0 family ethernet-switching vlan members v54 set vlans rack_1 vlan-id 100 set vlans rack_1 l3-interface irb.100 set vlans v54 vlan-id 54 set vlans v54 l3-interface irb.54 set interfaces irb unit 54 family inet address 192.168.54.1/24 arp 192.168.54.2 l2-interface ae1.0 set interfaces irb unit 54 family inet address 192.168.54.1/24 arp 192.168.54.2 mac 00:1f:12:b6:6f:f0 set interfaces irb unit 100 family inet address 192.168.10.2/24 arp 192.168.10.3 l2-interface ae1.0 set interfaces irb unit 100 family inet address 192.168.10.2/24 arp 192.168.10.3 mac 00:1f:12:b6:6f:f0 set interfaces lo0 unit 0 family inet address 192.168.39.2/32 set protocols iccp local-ip-addr 192.168.39.2 set protocols iccp peer 192.168.39.1 session-establishment-hold-time 50 set protocols iccp peer 192.168.39.1 redundancy-group-id-list 1 set protocols iccp peer 192.168.39.1 backup-liveness-detection backup-peer-ip 10.105.5.5 set protocols iccp peer 192.168.39.1 liveness-detection minimum-interval 2000 set protocols iccp peer 192.168.39.1 liveness-detection multiplier 4 set multi-chassis multi-chassis-protection 192.168.39.1 interface ae1 set switch-options service-id 1
Configuring MC-LAG on Switch A
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy.
-
Configure the number of aggregated Ethernet interfaces to be created on Switch A.
[edit chassis] user@switch# set aggregated-devices ethernet device-count 20
-
Add member interfaces to the aggregated Ethernet interfaces that will be used for the Inter-Chassis Control Protocol (ICCP) interface.
[edit interfaces] user@switch# set et-1/0/0 ether-options 802.3ad ae0 user@switch# set et-1/0/1 ether-options 802.3ad ae0
-
Specify the member interfaces that belong to interface ae2.
[edit interfaces] user@switch# set et-1/2/0 ether-options 802.3ad ae2
-
Configure the member interfaces for the interchassis link (ICL) with a hold-time value that is higher than the configured BFD timer to prevent the ICL from being advertised as being down before the ICCP link is down.
If the ICL goes down before the ICCP link goes down, the MC-LAG interface configured as the standby status-control peer goes up and down. The interface going up and down causes a delay in convergence.
[edit interfaces] user@switch# set xe-2/0/3 hold-time up 100 user@switch# set xe-2/0/3 hold-time down 9000 user@switch# set xe-2/0/3 ether-options 802.3ad ae1 user@switch# set xe-2/0/4 hold-time up 100 user@switch# set xe-2/0/4 hold-time down 9000 user@switch# set xe-2/0/4 ether-options 802.3ad ae1
-
Specify the members that belong to ae4.
Specify the members that belong to ae4.
[edit interfaces] user@switch# set xe-2/0/0 ether-options 802.3ad ae4
-
Configure ae0 as a Layer 3 interface.
[edit interfaces] user@switch# set ae0 aggregated-ether-options lacp active user@switch# set ae0 aggregated-ether-options lacp periodic fast user@switch# set ae0 unit 0 family inet address 192.168.90.1/24
-
Configure ae1 as a Layer 2 interface.
[edit interfaces] user@switch# set ae1 description ICL-LINK user@switch# set ae1 aggregated-ether-options lacp active user@switch# set ae1 aggregated-ether-options lacp periodic fast
-
Configure a trunk interface between EX9200-A and EX9200-B.
[edit interfaces] user@switch# set ae1 unit 0 family ethernet-switching interface-mode trunk user@switch# set ae1 unit 0 family ethernet-switching vlan members all
-
Configure the LACP parameters on ae2.
[edit interfaces] user@switch# set ae2 aggregated-ether-options lacp active user@switch# set ae2 aggregated-ether-options lacp periodic fast
-
Configure the LACP system ID.
[edit interfaces] user@switch# set ae2 aggregated-ether-options lacp system-id 00:01:02:03:04:06
-
Configure the MC-AE interface properties.
[edit interfaces] user@switch# set ae2 aggregated-ether-options lacp admin-key 3 user@switch# set ae2 aggregated-ether-options mc-ae mc-ae-id 3 user@switch# set ae2 aggregated-ether-options mc-ae redundancy-group 1
-
Specify a unique chassis ID for the MC-LAG that the aggregated Ethernet interface belongs to.
[edit interfaces] user@switch# set ae2 aggregated-ether-options mc-ae chassis-id 0
-
Specify the mode of the MC-LAG that the aggregated Ethernet interface belongs to.
[edit interfaces] user@switch# set ae2 aggregated-ether-options mc-ae mode active-active
-
Configure the status control on the switch that hosts the MC-LAG.
If one switch is in active mode, then the other switch must be in standby mode.
[edit interfaces] user@switch# set ae2 aggregated-ether-options mc-ae status-control active
-
Specify the time in seconds by when routing adjacencies must form.
[edit interfaces] user@switch# set ae2 aggregated-ether-options mc-ae init-delay-time 520
-
Specify that if a peer of the MC-LAG group goes down, the peer that is configured as status-control active becomes the active peer.
[edit interfaces] user@switch# set ae2 aggregated-ether-options mc-ae events iccp-peer-down prefer-status-control-active
-
Configure ae2 as a trunk port with membership in all VLANs.
[edit interfaces] user@switch# set ae2 unit 0 family ethernet-switching interface-mode trunk user@switch# set ae2 unit 0 family ethernet-switching vlan members all
-
Configure the LACP parameters on ae4.
[edit interfaces] user@switch# set ae4 aggregated-ether-options lacp active user@switch# set ae4 aggregated-ether-options lacp periodic fast
-
Specify the LACP administration key.
[edit interfaces] user@switch# set ae4 aggregated-ether-options lacp system-id 00:01:02:03:04:06 user@switch# set ae4 aggregated-ether-options lacp admin-key 7 user@switch# set ae4 aggregated-ether-options mc-ae mc-ae-id 7 user@switch# set ae4 aggregated-ether-options mc-ae redundancy-group 1
-
Specify a unique chassis ID for the MC-LAG that the aggregated Ethernet interface belongs to.
[edit interfaces] user@switch# set ae4 aggregated-ether-options mc-ae chassis-id 0 user@switch# set ae4 aggregated-ether-options mc-ae mode active-active
-
Configure the status control on the switch that hosts the MC-LAG.
If one switch is in active mode, then the other switch must be in standby mode.
[edit interfaces] user@switch# set ae4 aggregated-ether-options mc-ae status-control active user@switch# set ae4 aggregated-ether-options mc-ae init-delay-time 520 user@switch# set ae4 aggregated-ether-options mc-ae events iccp-peer-down prefer-status-control-active
-
Configure ae4 as a Layer 2 interface.
[edit interfaces] user@switch# set ae4 unit 0 family ethernet-switching interface-mode trunk user@switch# set ae4 unit 0 family ethernet-switching vlan members v54
-
Configure VLAN rack_1 and configure a Layer 3 IRB interface on VLAN rack_1.
[edit vlans] user@switch# set rack_1 vlan-id 100 user@switch# set rack_1 l3-interface irb.100
-
Configure VLAN rack_1.
[edit vlans] user@switch# set rack_1 vlan-id 54
-
Configure VLAN 54 and configure a Layer 3 IRB on VLAN 54.
[edit vlans] user@switch# set v54 vlan-id 54 user@switch# set v54 l3-interface irb.54
-
Configure an IRB interface on VLAN 54.
You must configure static ARP on the MC-LAG peers to allow routing protocols to traverse over the IRB interface.
[edit interfaces] user@switch# set irb unit 54 family inet address 192.168.54.2/24 arp 192.168.54.1 l2-interface ae1.0 user@switch# set irb unit 54 family inet address 192.168.54.2/24 arp 192.168.54.1 mac 3c:8a:b0:85:78:70
-
Configure static ARP on the MC-LAG peers to allow routing protocols to traverse over the IRB interface
[edit interfaces] user@switch# set irb unit 100 family inet address 192.168.10.3/24 arp 192.168.10.2 l2-interface ae1.0 user@switch# set irb unit 100 family inet address 192.168.10.3/24 arp 192.168.10.2 mac 3c:8a:b0:85:78:70
-
Configure a loopback interface.
[edit interfaces] user@switch# set lo0 unit 0 family inet address 192.168.39.2/32
-
Configure ICCP using the loopback address.
[edit protocols] user@switch# set iccp local-ip-addr 192.168.39.1
-
Configure the session establishment hold time for ICCP to connect faster.
[edit protocols] user@switch# set iccp peer 192.168.39.2 session-establishment-hold-time 50 user@switch# set iccp peer 192.168.39.2 redundancy-group-id-list 1 user@switch# set iccp peer 192.168.39.2 backup-liveness-detection backup-peer-ip 10.105.5.6
-
To enable Bidirectional Forwarding Detection (BFD), configure the minimum receive interval.
We recommend a minimum receive interval value of 6 seconds.
[edit protocols] user@switch# set iccp peer 192.168.39.2 liveness-detection minimum-interval 2000 user@switch# set iccp peer 192.168.39.2 liveness-detection multiplier 4 [edit multi-chassis] user@switch# set multi-chassis-protection 192.168.39.2 interface ae1
-
Specify the switch service ID.
The switch service ID is used to synchronize applications, IGMP, ARP, and MAC learning across MC-LAG members.
[edit switch-options] user@switch# set service-id 1
Configuring MC-LAG on Switch B
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy.
-
Configure the number of aggregated Ethernet interfaces to be created on Switch A.
[edit chassis] user@switch# set aggregated-devices ethernet device-count 20
-
Add member interfaces to the aggregated Ethernet interfaces that will be used for the Inter-Chassis Control Protocol (ICCP) interface.
[edit interfaces] user@switch# set et-1/0/0 ether-options 802.3ad ae0 user@switch# set et-1/0/1 ether-options 802.3ad ae0
-
Specify the member interfaces that belong to interface ae2.
[edit interfaces] user@switch# set et-1/2/0 ether-options 802.3ad ae2
-
Configure the member interfaces for the interchassis link (ICL) with a hold-time value that is higher than the configured BFD timer to prevent the ICL from being advertised as being down before the ICCP link is down.
If the ICL goes down before the ICCP link goes down, the MC-LAG interface configured as the standby status-control peer goes up and down. The interface going up and down causes a delay in convergence.
[edit interfaces] user@switch# set xe-2/0/3 hold-time up 100 user@switch# set xe-2/0/3 hold-time down 9000 user@switch# set xe-2/0/3 ether-options 802.3ad ae1 user@switch# set xe-2/0/4 hold-time up 100 user@switch# set xe-2/0/4 hold-time down 9000 user@switch# set xe-2/0/4 ether-options 802.3ad ae1
-
Specify the members that belong to ae4.
[edit interfaces] user@switch# set xe-2/0/0 ether-options 802.3ad ae4
-
Configure ae0 as a Layer 3 interface.
[edit interfaces] user@switch# set ae0 aggregated-ether-options lacp active user@switch# set ae0 aggregated-ether-options lacp periodic fast user@switch# set ae0 unit 0 family inet address 192.168.90.2/24
-
Configure ae1 as a Layer 2 interface.
[edit interfaces] user@switch# set ae1 description ICL-LINK user@switch# set ae1 aggregated-ether-options lacp active user@switch# set ae1 aggregated-ether-options lacp periodic fast
-
Configure a trunk interface between EX9200-A and EX9200-B.
[edit interfaces] user@switch# set ae1 unit 0 family ethernet-switching interface-mode trunk user@switch# set ae1 unit 0 family ethernet-switching vlan members all
-
Configure the LACP parameters on ae2.
[edit interfaces] user@switch# set ae2 aggregated-ether-options lacp active user@switch# set ae2 aggregated-ether-options lacp periodic fast
-
Configure the LACP system ID.
[edit interfaces] user@switch# set ae2 aggregated-ether-options lacp system-id 00:01:02:03:04:05
-
Configure the MC-AE interface properties.
[edit interfaces] user@switch# set ae2 aggregated-ether-options lacp admin-key 3 user@switch# set ae2 aggregated-ether-options mc-ae mc-ae-id 3 user@switch# set ae2 aggregated-ether-options mc-ae redundancy-group 1
-
Specify a unique chassis ID for the MC-LAG that the aggregated Ethernet interface belongs to.
[edit interfaces] user@switch# set ae2 aggregated-ether-options mc-ae chassis-id 1
-
Specify the mode of the MC-LAG that the aggregated Ethernet interface belongs to.
[edit interfaces] user@switch# set ae2 aggregated-ether-options mc-ae mode active-active
-
Specify the time in seconds by when routing adjacencies must form.
[edit interfaces] user@switch# set ae2 aggregated-ether-options mc-ae init-delay-time 520
-
Configure the status control on the switch that hosts the MC-LAG.
If one switch is in active mode, then the other switch must be in standby mode.
[edit interfaces] user@switch# set ae2 aggregated-ether-options mc-ae status-control standby
-
Configure ae2 as a trunk port with membership in all VLANs.
[edit interfaces] user@switch# set ae2 unit 0 family ethernet-switching interface-mode trunk user@switch# set ae2 unit 0 family ethernet-switching vlan members all
-
Configure the LACP parameters on ae4.
[edit interfaces] user@switch# set ae4 aggregated-ether-options lacp active user@switch# set ae4 aggregated-ether-options lacp periodic fast
-
Specify the LACP administration key.
[edit interfaces] user@switch# set ae4 aggregated-ether-options lacp system-id 00:01:02:03:04:06 user@switch# set ae4 aggregated-ether-options lacp admin-key 7 user@switch# set ae4 aggregated-ether-options mc-ae mc-ae-id 7 user@switch# set ae4 aggregated-ether-options mc-ae redundancy-group 1
-
Specify a unique chassis ID for the MC-LAG that the aggregated Ethernet interface belongs to.
[edit interfaces] user@switch# set ae4 aggregated-ether-options mc-ae chassis-id 1 user@switch# set ae4 aggregated-ether-options mc-ae mode active-active
-
Configure the status control on the switch that hosts the MC-LAG.
If one switch is in active mode, then the other switch must be in standby mode.
[edit interfaces] user@switch# set ae4 aggregated-ether-options mc-ae status-control standby user@switch# set ae4 aggregated-ether-options mc-ae init-delay-time 520 user@switch# set ae4 aggregated-ether-options mc-ae events iccp-peer-down prefer-status-control-active
-
Configure ae4 as a Layer 2 interface.
[edit interfaces] user@switch# set ae4 unit 0 family ethernet-switching interface-mode trunk user@switch# set ae4 unit 0 family ethernet-switching vlan members v54
-
Configure VLAN rack_1 and configure a Layer 3 IRB interface on VLAN rack_1.
[edit vlans] user@switch# set rack_1 vlan-id 100 user@switch# set rack_1 l3-interface irb.100
-
Configure VLAN 54 and configure an IRB on VLAN 54.
[edit vlans] user@switch# set v54 vlan-id 54 user@switch# set v54 l3-interface irb.54
-
Configure static ARP on the MC-LAG peers to allow routing protocols to traverse over the IRB interface.
[edit interfaces] user@switch# set irb unit 54 family inet address 192.168.54.1/24 arp 192.168.54.2 l2-interface ae1.0 user@switch# set irb unit 54 family inet address 192.168.54.1/24 arp 192.168.54.2 mac mac 00:1f:12:b6:6f:f0
-
Configure static Address Resolution Protocol (ARP) on the MC-LAG IRB peers to allow routing protocols to traverse the IRB interface.
[edit interfaces] user@switch# set irb unit 100 family inet address 192.168.10.2/24 arp 192.168.10.3 l2-interface ae1.0 user@switch# set irb unit 100 family inet address 192.168.10.2/24 arp 192.168.10.3 mac 00:1f:12:b6:6f:f0
-
Configure a loopback interface.
[edit interfaces] user@switch# set lo0 unit 0 family inet address 192.168.39.2/32
-
Configure ICCP using the loopback address.
[edit protocols] user@switch# set iccp local-ip-addr 192.168.39.2
-
Configure the session establishment hold time for ICCP to connect faster.
[edit protocols] user@switch# set iccp peer 192.168.39.1 session-establishment-hold-time 50 user@switch# set iccp peer 192.168.39.1 redundancy-group-id-list 1 user@switch# set iccp peer 192.168.39.1 backup-liveness-detection backup-peer-ip 10.105.5.5
-
To enable Bidirectional Forwarding Detection (BFD), configure the minimum receive interval.
We recommend a minimum receive interval value of 6 seconds.
[edit protocols] user@switch# set iccp peer 192.168.39.1 liveness-detection minimum-interval 2000 user@switch# set iccp peer 192.168.39.1 liveness-detection multiplier 4 [edit multi-chassis] user@switch# set multi-chassis-protection 192.168.39.1 interface ae1
-
Specify the switch service ID.
The switch service ID is used to synchronize applications, IGMP, ARP, and MAC learning across MC-LAG members.
[edit switch-options] user@switch# set service-id 1
Results
Display the results of the configuration on EX9200-A.
user@switch> show chassis
chassis {
redundancy {
graceful-switchover;
}
aggregated-devices {
ethernet {
device-count 20;
}
}
}
user@switch> show interfaces
interfaces {
et-1/0/0 {
ether-options {
802.3ad ae0;
}
}
et-1/0/1 {
ether-options {
802.3ad ae0;
}
}
et-1/2/0 {
ether-options {
802.3ad ae2;
}
}
xe-2/0/3 {
hold-time up 100 down 7000;
ether-options {
802.3ad ae1;
}
}
xe-2/0/4 {
hold-time up 100 down 7000;
ether-options {
802.3ad ae1;
}
}
ae0 {
aggregated-ether-options {
lacp {
active;
periodic fast;
}
}
unit 0 {
family inet {
address 192.168.90.1/24;
}
}
}
ae1 {
description ICL-LINK;
aggregated-ether-options {
lacp {
active;
periodic fast;
}
}
unit 0 {
family ethernet-switching {
interface-mode trunk;
vlan {
members all;
}
}
}
}
ae2 {
aggregated-ether-options {
lacp {
active;
periodic fast;
system-id 00:01:02:03:04:05;
admin-key 3;
}
mc-ae {
mc-ae-id 3;
redundancy-group 1;
chassis-id 0;
mode active-active;
status-control active;
init-delay-time 520;
events {
iccp-peer-down {
prefer-status-control-active;
}
}
}
}
unit 0 {
family ethernet-switching {
interface-mode trunk;
vlan {
members all;
}
}
}
}
ae4 {
aggregated-ether-options {
lacp {
active;
periodic fast;
system-id 00:01:02:03:04:06;
admin-key 7;
}
mc-ae {
mc-ae-id 7;
redundancy-group 1;
chassis-id 0;
mode active-active;
status-control standby;
init-delay-time 520;
events {
iccp-peer-down {
prefer-status-control-active;
}
}
}
}
unit 0 {
family ethernet-switching {
interface-mode trunk;
vlan {
members [ rack_1 v54 ];
}
}
irb {
arp-l2-validate;
unit 54 {
family inet {
address 192.168.54.2/24 {
arp 192.168.54.1 l2-interface ae1.0 mac 3c:8a:b0:85:78:70;
}
}
}
unit 100 {
family inet {
address 192.168.10.3/24 {
arp 192.168.10.2 l2-interface ae1.0 mac 3c:8a:b0:85:78:70;
}
}
}
}
lo0 {
unit 0 {
family inet {
address 192.168.39.1/32;
}
}
}
user@switch> show multi-chassis
multi-chassis {
multi-chassis-protection 192.168.39.2 {
interface ae1;
}
}
user@switch> show protocols
protocols {
iccp {
local-ip-addr 192.168.39.1;
peer 192.168.39.2 {
session-establishment-hold-time 50;
redundancy-group-id-list 1;
backup-liveness-detection {
backup-peer-ip 10.105.5.6;
}
liveness-detection {
minimum-interval 2000;
multiplier 3;
}
}
}
lldp {
interface all;
}
layer2-control {
nonstop-bridging;
}
}
user@switch> show switch-options
switch-options {
service-id 1;
}
user@switch> show vlans
vlans {
rack_1 {
vlan-id 100;
l3-interface irb.100;
}
v54 {
vlan-id 54;
l3-interface irb.54;
}
}
Display the results of the configuration on EX9200-B.
user@switch> show chassis
chassis {
redundancy {
graceful-switchover;
}
aggregated-devices {
ethernet {
device-count 20;
}
}
}
user@switch> show interfaces
interfaces {
et-1/0/0 {
ether-options {
802.3ad ae0;
}
}
et-1/0/1 {
ether-options {
802.3ad ae0;
}
}
et-1/2/0 {
ether-options {
802.3ad ae2;
}
}
xe-2/0/3 {
hold-time up 100 down 7000;
ether-options {
802.3ad ae1;
}
}
xe-2/0/4 {
hold-time up 100 down 7000;
ether-options {
802.3ad ae1;
}
}
ae0 {
aggregated-ether-options {
lacp {
active;
periodic fast;
}
}
unit 0 {
family inet {
address 192.168.90.2/24;
}
}
ae1 {
description ICL-LINK;
aggregated-ether-options {
lacp {
active;
periodic fast;
}
}
unit 0 {
family ethernet-switching {
interface-mode trunk;
vlan {
members all;
}
}
}
}
ae2 {
aggregated-ether-options {
lacp {
active;
periodic fast;
system-id 00:01:02:03:04:05;
admin-key 3;
}
mc-ae {
mc-ae-id 3;
redundancy-group 1;
chassis-id 1;
mode active-active;
status-control active;
init-delay-time 520;
events {
iccp-peer-down {
prefer-status-control-active;
}
}
}
}
unit 0 {
family ethernet-switching {
interface-mode trunk;
vlan {
members all;
}
}
}
}
ae4 {
aggregated-ether-options {
lacp {
active;
periodic fast;
system-id 00:01:02:03:04:06;
admin-key 7;
}
mc-ae {
mc-ae-id 7;
redundancy-group 1;
chassis-id 1;
mode active-active;
status-control standby;
init-delay-time 520;
}
}
unit 0 {
family ethernet-switching {
interface-mode trunk;
vlan {
members [rack_1 v54 ];
}
}
irb {
arp-l2-validate;
unit 54 {
family inet {
address 192.168.54.1/24 {
arp 192.168.54.2 l2-interface ae1.0 mac 00:1f:12:b6:6f:f0;
}
}
}
unit 100 {
family inet {
address 192.168.10.2/24 {
arp 192.168.10.3 l2-interface ae1.0 mac 00:1f:12:b6:6f:f0;
}
}
}
lo0 {
unit 0 {
family inet {
address 192.168.39.2/32;
}
}
user@switch> show multi-chassis
multi-chassis {
multi-chassis-protection 192.168.39.1 {
interface ae1;
}
}
user@switch> show protocols
protocols {
iccp {
local-ip-addr 192.168.39.2;
peer 192.168.39.1 {
session-establishment-hold-time 50;
redundancy-group-id-list 1;
backup-liveness-detection {
backup-peer-ip 10.105.5.5;
}
liveness-detection {
minimum-interval 2000;
multiplier 3;
}
}
}
lldp {
interface all;
}
layer2-control {
nonstop-bridging;
}
}
user@switch> show switch-options
switch-options {
service-id 1;
}
user@switch> show vlans
vlans {
rack_1 {
vlan-id 100;
l3-interface irb.100;
}
v54 {
vlan-id 54;
l3-interface irb.54;
}
}
(Optional) Configuring RSTP
CLI Quick Configuration
Switch A and Switch B
set protocols rstp interface ae2 set protocols rstp interface ae4 set protocols rstp system-identifier 00:01:02:03:04:05 set protocols rstp bridge-priority 0
Configuring Switch A and Switch B
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode .
To configure Switch A and Switch B:
-
Enable the Rapid Spanning Tree Protocol on the ae2 and ae4 interfaces for optional loop prevention.
[edit protocols] user@switch# set rstp interface ae2 user@switch# set rstp interface ae4
-
Configure the system identifier.
[edit protocols] user@switch# set rstp system-identifier 00:01:02:03:04:05
-
Set Rapid Spanning Tree Protocol priority to 0. This will make the MC-AE node the highest priority.
[edit protocols] user@switch# set rstp bridge-priority 0
Switch A and Switch B
From configuration mode, confirm your configuration by entering
the show protocols rstp commands. If the output does not
display the intended configuration, repeat the instructions in this
example to correct the configuration.
user@switch> show protocols rstp
rstp {
system-identifier 00:01:02:03:04:05;
interface ae2;
interface ae4;
}
(Optional) Configuring IGMP Snooping
CLI Quick Configuration
Switch A and Switch B
set protocols igmp-snooping vlan rack_1 set protocols igmp-snooping vlan v54 set multicast-snooping-options multichassis-lag-replicate-state set protocols igmp-snooping vlan rack_1 interface ae1.0 multicast-router-interface set protocols igmp-snooping vlan v54 interface ae1.0 multicast-router-interface
Configuring Switch A and Switch B
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode .
To configure Switch A and Switch B:
-
Enable IGMP snooping for all VLANs.
[edit protocols] user@switch# set igmp-snooping vlan rack_1 user@switch# set igmp-snooping vlan v54
-
Synchronize multicast states across MC-LAG peers when bridge domains are configured.
At the global level, IGMP join and leave messages are replicated from the MC-LAG interface active link to the standby link to enable faster recovery of membership information after a failover.
[edit multicast-snooping-options] user@switch# set multichassis-lag-replicate-state
-
Configure the ICL-PL interface as a router-facing interface.
[edit protocols] user@switch# set igmp-snooping vlan rack_1 interface ae1.0 multicast-router-interface user@switch# set igmp-snooping vlan v54 interface ae1.0 multicast-router-interface
Switch A and Switch B
From configuration mode, confirm your configuration by entering
the show protocols igmp and show multicast-snooping-options commands. If the output does not display the intended configuration,
repeat the instructions in this example to correct the configuration.
user@switch> show protocols igmp
igmp-snooping {
vlan rack_1 {
interface ae1.0 {
multicast-router-interface;
}
}
vlan v54 {
interface ae1.0 {
multicast-router-interface;
}
}
}
user@switch> show multicast-snooping-options
multicast-snooping-options {
multichassis-lag-replicate-state;
}
(Optional) Configuring VRRP
You cannot configure both VRRP and MAC address synchronization.
CLI Quick Configuration
Switch A
set interfaces irb unit 100 family inet address 192.168.10.3/24 vrrp-group 1 virtual-address 192.168.10.1 set interfaces irb unit 100 family inet address 192.168.10.3/24 vrrp-group 1 priority 150 set interfaces irb unit 100 family inet address 192.168.10.3/24 vrrp-group 1 accept-data set interfaces irb unit 54 family inet address 192.168.54.2/24 vrrp-group 4 virtual-address 192.168.54.3 set interfaces irb unit 54 family inet address 192.168.54.2/24 vrrp-group 4 priority 200
Switch B
set interfaces irb unit 100 family inet address 192.168.10.2/24 vrrp-group 1 virtual-address 192.168.10.1 set interfaces irb unit 100 family inet address 192.168.10.2/24 vrrp-group 1 priority 200 set interfaces irb unit 100 family inet address 192.168.10.2/24 vrrp-group 1 accept-data set interfaces irb unit 54 family inet address 192.168.54.1/24 vrrp-group 4 virtual-address 192.168.54.3 set interfaces irb unit 54 family inet address 192.168.54.1/24 vrrp-group 4 priority 150
Configuring Switch A
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode .
To configure Switch A:
-
Enable VRRP on the MC-LAGs by creating an IRB interface for each MC-LAG, assign a virtual IP address that is shared between each switch in the VRRP group, and assign an individual IP address for each individual member in the VRRP group.
[edit interfaces] user@switch# set irb unit 100 family inet address 192.168.10.3/24 vrrp-group 1 virtual-address 192.168.10.1 user@switch# set irb unit 100 family inet address 192.168.10.3/24 vrrp-group 1 priority 150 user@switch# set irb unit 100 family inet address 192.168.10.3/24 vrrp-group 1 accept-data
-
Enable VRRP on the MC-LAGs by creating an IRB interface for each MC-LAG, assign a virtual IP address that is shared between each switch in the VRRP group, and assign an individual IP address for each individual member in the VRRP group.
[edit interfaces] user@switch# set irb unit 54 family inet address 192.168.54.2/24 vrrp-group 4 virtual-address 192.168.54.3 user@switch# set irb unit 54 family inet address 192.168.54.2/24 vrrp-group 4 priority 200
Switch A
From configuration mode, confirm your configuration by entering
the show interfaces irb unit 100 family inet address 192.168.10.3/24
vrrp-group and show interfaces irb unit 100 family inet
address 192.168.54.2/24 vrrp-group commands. If the output does
not display the intended configuration, repeat the instructions in
this example to correct the configuration.
user@switch> show interfaces irb unit 100 family inet address 192.168.10.3/24 vrrp-group
vrrp-group 1 {
virtual-address 192.168.10.1;
priority 150;
accept-data;
}
user@switch> show interfaces irb unit 100 family inet address 192.168.54.2/24 vrrp-group
vrrp-group 4 {
virtual-address 192.168.54.3;
priority 150;
}
Configuring Switch B
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode .
To configure Switch A:
-
Enable VRRP on the MC-LAGs by creating an IRB interface for each MC-LAG, assign a virtual IP address that is shared between each switch in the VRRP group, and assign an individual IP address for each individual member in the VRRP group.
[edit interfaces] user@switch# set irb unit 100 family inet address 192.168.10.2/24 vrrp-group 1 virtual-address 192.168.10.1 user@switch# set irb unit 100 family inet address 192.168.10.2/24 vrrp-group 1 priority 150 user@switch# set irb unit 100 family inet address 192.168.10.2/24 vrrp-group 1 accept-data
-
Enable VRRP on the MC-LAGs by creating an IRB interface for each MC-LAG, assign a virtual IP address that is shared between each switch in the VRRP group, and assign an individual IP address for each individual member in the VRRP group.
[edit interfaces] user@switch# set irb unit 54 family inet address 192.168.54.1/24 vrrp-group 4 virtual-address 192.168.54.3 user@switch# set irb unit 54 family inet address 192.168.54.1/24 vrrp-group 4 priority 150
Switch B
From configuration mode, confirm your configuration by entering
the show protocols rstp commands. If the output does not
display the intended configuration, repeat the instructions in this
example to correct the configuration.
user@switch> show interfaces irb unit 100 family inet address 192.168.10.2/24 vrrp-group
vrrp-group 1 {
virtual-address 192.168.10.1;
priority 200;
accept-data;
}
user@switch> show interfaces irb unit 100 family inet address 192.168.54.1/24 vrrp-group
vrrp-group 4 {
virtual-address 192.168.54.3;
priority 150;
}
(Optional) Configuring MAC Address Synchronization
You cannot configure both MAC synchronization and VRRP.
You must configure the same IP address on the IRB interface in the VLAN on both MC-LAG peers.
CLI Quick Configuration
Switch A and Switch B
set vlans v100 mcae-mac-synchronize set vlans v54 mcae-mac-synchronize
Configuring Switch A and Switch B
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode .
To configure Switch A:
-
Configure MAC address synchronization in the MC-LAG VLAN on both Switch A and Switch B.
[edit] user@switch# set vlans v100 mcae-mac-synchronize [edit] user@switch# set vlans v54 mcae-mac-synchronize
Switch A and Switch B
From configuration mode, confirm your configuration by entering
the show vlans v100 and show vlans v54 commands.
If the output does not display the intended configuration, repeat
the instructions in this example to correct the configuration.
user@switch> show vlans v100
v100 {
vlan-id 100;
l3-interface irb.100;
mcae-mac-synchronize;
}
user@switch> show vlans v54
v54 {
vlan-id 54;
l3-interface irb.54;
mcae-mac-synchronize;
}
(Optional) Configuring OSPF
CLI Quick Configuration
Switch A and Switch B
set protocols ospf area 0.0.0.0 interface lo0.0 set protocols ospf area 0.0.0.0 interface ae0.0 set protocols ospf area 0.0.0.0 interface irb.54 set protocols ospf area 0.0.0.0 interface irb.100
Configuring Switch A and Switch B
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode .
To configure Switch A and Switch B:
-
Configure an OSPF area.
[edit protocols] user@switch# set ospf area 0.0.0.0 interface lo0.0 user@switch# set ospf area 0.0.0.0 interface ae0.0 user@switch# set ospf area 0.0.0.0 interface irb.54 user@switch# set ospf area 0.0.0.0 interface irb.100
Switch A and Switch B
From configuration mode, confirm your configuration by entering
the show protocols ospf commands. If the output does not
display the intended configuration, repeat the instructions in this
example to correct the configuration.
user@switch> show protocols ospf
ospf {
area 0.0.0.0 {
interface lo0.0;
interface ae0.0;
interface irb.54;
interface irb.100;
}
}
(Optional) Configuring PIM
CLI Quick Configuration
Switch A
set protocols pim interface irb.54 set protocols pim interface irb.100 set protocols pim interface lo0.0 set protocols pim rp bootstrap-priority 150 set protocols pim rp local address 192.168.39.1
Switch B
set protocols pim interface irb.54 set protocols pim interface irb.100 set protocols pim interface lo0.0 set protocols pim rp bootstrap-priority 200 set protocols pim rp local address 192.168.39.2
Configuring Switch A
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode .
To configure Switch A:
-
Configure Protocol Independent Multicast (PIM) as the multicast protocol.
[edit protocols] user@switch# set pim interface irb.54 user@switch# set pim interface irb.100
-
Configure the loopback interface.
[edit protocols] user@switch# set pim interface lo0.0
-
Configure the switch as a secondary rendezvous point (RP).
A lower priority setting indicates that the secondary RP is in a bootstrap configuration.
[edit protocols] user@switch# set pim rp bootstrap-priority 150 user@switch# set pim rp local address 192.168.39.1
Switch A
From configuration mode, confirm your configuration by entering
the show protocols pim commands. If the output does not
display the intended configuration, repeat the instructions in this
example to correct the configuration.
user@switch> show protocols pim
pim {
rp {
bootstrap-priority 150;
local {
address 192.168.39.1;
}
}
interface irb.54;
interface irb.100;
interface lo0.0;
}
Configuring Switch B
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode .
To configure Switch A:
-
Configure Protocol Independent Multicast (PIM) as the multicast protocol.
[edit protocols] user@switch# set pim interface irb.54 user@switch# set pim interface irb.100
-
Configure the loopback interface.
[edit protocols] user@switch# set pim interface lo0.0
-
Configure the switch as a secondary rendezvous point (RP).
A lower priority setting indicates that the secondary RP is in a bootstrap configuration.
[edit protocols] user@switch# set pim rp bootstrap-priority 200 user@switch# set pim rp local address 192.168.39.2
Switch B
From configuration mode, confirm your configuration by entering
the show protocols pim commands. If the output does not
display the intended configuration, repeat the instructions in this
example to correct the configuration.
user@switch> show protocols pim
pim {
rp {
bootstrap-priority 200;
local {
address 192.168.39.2;
}
}
interface irb.54;
interface irb.100;
interface lo0.0;
}
(Optional) Configuring DHCP Relay
CLI Quick Configuration
Switch A and Switch B
set forwarding-options dhcp-relay forward-snooped-clients all-interfaces set forwarding-options dhcp-relay overrides allow-snooped-clients set forwarding-options dhcp-relay server-group GVP-DHCP 10.105.5.202 set forwarding-options dhcp-relay active-server-group GVP-DHCP set forwarding-options dhcp-relay route-suppression destination set forwarding-options dhcp-relay group Floor1 interface irb.100 set forwarding-options dhcp-relay relay-option-82 circuit-id use-interface-description device
Configuring Switch A and Switch B
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode .
To configure Switch A and Switch B:
-
Configure forward snooped unicast packets on all interfaces.
[edit fowarding-options] user@switch# set dhcp-relay forward-snooped-clients all-interfaces
-
Create a binding entry to snoop unicast clients.
[edit forwarding-options] user@switch# set dhcp-relay overrides allow-snooped-clients
-
Create a DHCP server group.
[edit forwarding-options] user@switch# set dhcp-relay server-group GVP-DHCP 10.105.5.202
-
Apply a DHCP relay agent configuration to the named group of DHCP server addresses.
[edit forwarding-options] user@switch# set dhcp-relay active-server-group GVP-DHCP
-
Configure the relay agent to suppress the installation of ARP and route entries for corresponding client binding.
[edit forwarding-options] user@switch# set dhcp-relay route-suppression destination
-
Create a DHCP relay group that includes at least one interface.
DHCP runs on the interfaces defined in the DHCP groups.
[edit forwarding-options] user@switch# set dhcp-relay group Floor1 interface irb.100
-
Configure DHCP relay with option 82.
[edit forwarding-options] user@switch# set dhcp-relay relay-option-82 circuit-id use-interface-description device
Switch A and Switch B
From configuration mode, confirm your configuration by entering
the show protocols pim commands. If the output does not
display the intended configuration, repeat the instructions in this
example to correct the configuration.
user@switch> show forwarding-options dhcp-relay
dhcp-relay {
forward-snooped-clients all-interfaces;
overrides {
allow-snooped-clients;
}
relay-option-82 {
circuit-id {
use-interface-description device;
}
}
server-group {
GVP-DHCP {
10.105.5.202;
}
}
active-server-group GVP-DHCP;
route-suppression {
destination;
}
group Floor1 {
interface irb.100;
}
}
Verification
Confirm that the configuration is working properly.
- Verifying ICCP on MC-LAG
- Verifying LACP on MC-LAG
- Verifying Aggregated Ethernet Interfaces in MC-LAG
- Verifying MAC Learning on MC-LAG
- Verifying VRRP in MC-LAG
- Verifying OSPF on MC-LAG
Verifying ICCP on MC-LAG
Purpose
Verify that ICCP is running on each device in the MC-LAG.
Action
-
Verify that ICCP is running on Switch A.
root@EX92000-A> show iccp Redundancy Group Information for peer 192.168.39.2 TCP Connection : Established Liveliness Detection : Up Backup liveness peer status: Up Redundancy Group ID Status 1 Up Client Application: l2ald_iccpd_client Redundancy Group IDs Joined: 1 Client Application: lacpd Redundancy Group IDs Joined: 1 Client Application: MCSNOOPD Redundancy Group IDs Joined: 1 -
Verify that ICCP is running on Switch B.
root@EX9200-B> show iccp Redundancy Group Information for peer 192.168.39.1 TCP Connection : Established Liveliness Detection : Up Backup liveness peer status: Up Redundancy Group ID Status 1 Up Client Application: lacpd Redundancy Group IDs Joined: 1 Client Application: l2ald_iccpd_client Redundancy Group IDs Joined: 1 Client Application: MCSNOOPD Redundancy Group IDs Joined: 1
Meaning
This output shows that the TCP connection between the peers hosting the MC-LAG is up, liveness detection is up, and MCSNOOPD and ESWD client applications are running.
Verifying LACP on MC-LAG
Purpose
Verify that LACP is working properly on each device in the MC-LAG.
Action
-
Verify that the LACP interfaces are up and running on Switch A.
root@EX9200-A> show lacp interfaces Aggregated interface: ae0 LACP state: Role Exp Def Dist Col Syn Aggr Timeout Activity et-1/0/0 Actor No No Yes Yes Yes Yes Fast Active et-1/0/0 Partner No No Yes Yes Yes Yes Fast Active et-1/0/1 Actor No No Yes Yes Yes Yes Fast Active et-1/0/1 Partner No No Yes Yes Yes Yes Fast Active LACP protocol: Receive State Transmit State Mux State et-1/0/0 Current Fast periodic Collecting distributing et-1/0/1 Current Fast periodic Collecting distributing Aggregated interface: ae1 LACP state: Role Exp Def Dist Col Syn Aggr Timeout Activity xe-2/0/3 Actor No No Yes Yes Yes Yes Fast Active xe-2/0/3 Partner No No Yes Yes Yes Yes Fast Active xe-2/0/4 Actor No No Yes Yes Yes Yes Fast Active xe-2/0/4 Partner No No Yes Yes Yes Yes Fast Active LACP protocol: Receive State Transmit State Mux State xe-2/0/3 Current Fast periodic Collecting distributing xe-2/0/4 Current Fast periodic Collecting distributing Aggregated interface: ae3 LACP state: Role Exp Def Dist Col Syn Aggr Timeout Activity xe-2/0/1 Actor No No Yes Yes Yes Yes Fast Active xe-2/0/1 Partner No No Yes Yes Yes Yes Fast Passive xe-2/0/2 Actor No No Yes Yes Yes Yes Fast Active xe-2/0/2 Partner No No Yes Yes Yes Yes Fast Passive LACP protocol: Receive State Transmit State Mux State xe-2/0/1 Current Fast periodic Collecting distributing xe-2/0/2 Current Fast periodic Collecting distributing Aggregated interface: ae4 LACP state: Role Exp Def Dist Col Syn Aggr Timeout Activity xe-2/0/0 Actor No No Yes Yes Yes Yes Fast Active xe-2/0/0 Partner No No Yes Yes Yes Yes Fast Active LACP protocol: Receive State Transmit State Mux State xe-2/0/0 Current Fast periodic Collecting distributing -
Verify that the LACP interfaces are up and running on Switch B.
root@EX9200-B> show lacp interfaces Aggregated interface: ae0 LACP state: Role Exp Def Dist Col Syn Aggr Timeout Activity et-1/0/0 Actor No No Yes Yes Yes Yes Fast Active et-1/0/0 Partner No No Yes Yes Yes Yes Fast Active et-1/0/1 Actor No No Yes Yes Yes Yes Fast Active et-1/0/1 Partner No No Yes Yes Yes Yes Fast Active LACP protocol: Receive State Transmit State Mux State et-1/0/0 Current Fast periodic Collecting distributing et-1/0/1 Current Fast periodic Collecting distributing Aggregated interface: ae1 LACP state: Role Exp Def Dist Col Syn Aggr Timeout Activity xe-2/0/3 Actor No No Yes Yes Yes Yes Fast Active xe-2/0/3 Partner No No Yes Yes Yes Yes Fast Active xe-2/0/4 Actor No No Yes Yes Yes Yes Fast Active xe-2/0/4 Partner No No Yes Yes Yes Yes Fast Active LACP protocol: Receive State Transmit State Mux State xe-2/0/3 Current Fast periodic Collecting distributing xe-2/0/4 Current Fast periodic Collecting distributing Aggregated interface: ae2 LACP state: Role Exp Def Dist Col Syn Aggr Timeout Activity et-1/2/0 Actor No No Yes Yes Yes Yes Fast Active et-1/2/0 Partner No No Yes Yes Yes Yes Fast Passive LACP protocol: Receive State Transmit State Mux State et-1/2/0 Current Fast periodic Collecting distributing Aggregated interface: ae4 LACP state: Role Exp Def Dist Col Syn Aggr Timeout Activity xe-2/0/0 Actor No No Yes Yes Yes Yes Fast Active xe-2/0/0 Partner No No Yes Yes Yes Yes Fast Active LACP protocol: Receive State Transmit State Mux State xe-2/0/0 Current Fast periodic Collecting distributing
Meaning
This output means that both devices and all related interfaces are properly participating in LACP negotiations.
Verifying Aggregated Ethernet Interfaces in MC-LAG
Purpose
Verify that all of the ae interfaces are configured properly in the MC�LAG.
Action
-
Verify the ae interfaces on Switch A.
user@EX9200-A> show interfaces mc-ae Member Link : ae2 Current State Machine's State: mcae active state Local Status : active Local State : up Peer Status : active Peer State : up Logical Interface : ae2.0 Topology Type : bridge Local State : up Peer State : up Peer Ip/MCP/State : 192.168.39.2 ae1.0 up Member Link : ae4 Current State Machine's State: mcae active state Local Status : active Local State : up Peer Status : active Peer State : up Logical Interface : ae4.0 Topology Type : bridge Local State : up Peer State : up Peer Ip/MCP/State : 192.168.39.2 ae1.0 up -
Verify the ae interfaces on Switch B.
root@EX9200-B> show interface mc-ae Member Link : ae2 Current State Machine's State: mcae active state Local Status : active Local State : up Peer Status : active Peer State : up Logical Interface : ae2.0 Topology Type : bridge Local State : up Peer State : up Peer Ip/MCP/State : 192.168.39.1 ae1.0 up Member Link : ae4 Current State Machine's State: mcae active state Local Status : active Local State : up Peer Status : active Peer State : up Logical Interface : ae4.0 Topology Type : bridge Local State : up Peer State : up Peer Ip/MCP/State : 192.168.39.1 ae1.0 up
Meaning
This output means that the mc-ae interfaces on each device are up and active.
Verifying MAC Learning on MC-LAG
Purpose
Verify that MAC learning between devices is happening in the MC-LAG.
Action
-
Show Ethernet switching table in Switch A.
root@EX9200-A> show ethernet-switching table MAC flags (S - static MAC, D - dynamic MAC, L - locally learned, P - Persistent static SE - statistics enabled, NM - non configured MAC, R - remote PE MAC) Ethernet switching table : 68 entries, 68 learned Routing instance : default-switch Vlan MAC MAC Age Logical name address flags interface dmzuplink 00:00:5e:00:01:ba DL - ae4.0 dmzuplink 00:10:db:bc:f5:9d DR - ae4.0 dmzuplink 00:10:db:ff:10:01 DL - ae3.0 dmzuplink 00:19:e2:57:33:81 DR - ae4.0 dmzuplink 00:26:88:92:ef:1d DR - ae4.0 dmzuplink 28:8a:1c:74:fb:07 DR - ae4.0 dmzuplink 28:8a:1c:75:05:1f DR - ae4.0 dmzuplink 28:c0:da:6a:1d:2a DR - ae4.0 dmzuplink 2c:21:72:7d:40:01 DL - ae4.0 dmzuplink 3c:8a:b0:77:a9:d6 DR - ae4.0 dmzuplink 5c:5e:ab:0e:cd:e0 DL - ae4.0 dmzuplink 84:18:88:8d:9d:2a DL - ae4.0 MAC flags (S - static MAC, D - dynamic MAC, L - locally learned, P - Persistent static SE - statistics enabled, NM - non configured MAC, R - remote PE MAC) Ethernet switching table : 68 entries, 68 learned Routing instance : default-switch Vlan MAC MAC Age Logical name address flags interface rack_1 00:50:56:9b:01:57 DR - ae2.0 rack_1 00:50:56:9b:09:95 DL - ae2.0 rack_1 00:50:56:9b:15:2e DL - ae2.0 rack_1 00:50:56:9b:20:44 DL - ae2.0 rack_1 00:50:56:9b:20:a7 DL - ae2.0 rack_1 00:50:56:9b:22:a8 DR - ae2.0 rack_1 00:50:56:9b:38:01 DL - ae2.0 rack_1 00:50:56:9b:66:dc DL - ae2.0 rack_1 00:50:56:9b:75:60 DR - ae2.0 MAC flags (S - static MAC, D - dynamic MAC, L - locally learned, P - Persistent static SE - statistics enabled, NM - non configured MAC, R - remote PE MAC) Ethernet switching table : 68 entries, 68 learned Routing instance : default-switch Vlan MAC MAC Age Logical name address flags interface v54 80:71:1f:c1:85:f0 DL - ae4.0 -
Show Ethernet switching table in Switch B.
root@EX9200-B> show ethernet-switching table MAC flags (S - static MAC, D - dynamic MAC, L - locally learned, P - Persistent static SE - statistics enabled, NM - non configured MAC, R - remote PE MAC) Ethernet switching table : 66 entries, 66 learned Routing instance : default-switch Vlan MAC MAC Age Logical name address flags interface rack_1 00:50:56:9b:01:57 DL - ae2.0 rack_1 00:50:56:9b:09:95 DR - ae2.0 rack_1 00:50:56:9b:15:2e DR - ae2.0 rack_1 00:50:56:9b:20:44 DR - ae2.0 rack_1 00:50:56:9b:20:a7 DR - ae2.0 rack_1 00:50:56:9b:22:a8 DL - ae2.0 rack_1 00:50:56:9b:38:01 DR - ae2.0 rack_1 00:50:56:9b:66:dc DR - ae2.0 rack_1 00:50:56:9b:75:60 DL - ae2.0 MAC flags (S - static MAC, D - dynamic MAC, L - locally learned, P - Persistent static SE - statistics enabled, NM - non configured MAC, R - remote PE MAC) Ethernet switching table : 66 entries, 66 learned Routing instance : default-switch Vlan MAC MAC Age Logical name address flags interface MAC flags (S - static MAC, D - dynamic MAC, L - locally learned, P - Persistent static SE - statistics enabled, NM - non configured MAC, R - remote PE MAC) Ethernet switching table : 66 entries, 66 learned Routing instance : default-switch Vlan MAC MAC Age Logical name address flags interface v54 80:71:1f:c1:85:f0 DR - ae4.0
Meaning
This output means that the MAC addresses are properly learned within the shared VLANs defined in the MC-LAG. This includes IRB interfaces to define the MC-LAG as well as the ICL interfaces used to configure VRRP.
Verifying VRRP in MC-LAG
Purpose
Verify that VRRP is up and active between the devices in the MC-LAG.
Action
-
Confirm that VRRP is up and active on Switch A.
root@EX9200-A> show vrrp Interface State Group VR state VR Mode Timer Type Address irb.54 up 4 backup Active D 3.090 lcl 192.168.54.1 vip 192.168.54.3 mas 192.168.54.2 irb.100 up 1 backup Active D 2.655 lcl 192.168.10.3 vip 192.168.10.1 mas 192.168.10.2In this example, Switch A is the backup VRRP member.
-
Confirm that VRRP is up and active on Switch B.
root@EX9200-B> show vrrp Interface State Group VR state VR Mode Timer Type Address irb.54 up 4 master Active A 0.900 lcl 192.168.54.2 vip 192.168.54.3 irb.100 up 1 master Active A 0.175 lcl 192.168.10.2 vip 192.168.10.1In this example, Switch B is the primary VRRP member.
Meaning
This output means that VRRP is up and running properly.
Verifying OSPF on MC-LAG
Purpose
Verify that OSPF is properly up and running with MC-LAG.
Action
-
Show OSPF neighbors on Switch A.
root@EX9200-A> show ospf neighbor Address Interface State ID Pri Dead 192.168.90.2 ae0.0 Full 192.168.39.2 128 35 192.168.10.2 irb.100 Full 192.168.39.2 128 33 192.168.54.2 irb.54 Full 192.168.39.2 128 38
-
Show OSPF routing table on Switch A.
root@EX9200-A> show ospf route Topology default Route Table: Prefix Path Route NH Metric NextHop Nexthop Type Type Type Interface Address/LSP 192.168.39.2 Intra Router IP 1 ae0.0 192.168.90.2 irb.100 192.168.10.2 irb.54 192.168.54.2 192.168.39.1/32 Intra Network IP 0 lo0.0 192.168.39.2/32 Intra Network IP 1 ae0.0 192.168.90.2 irb.100 192.168.10.2 irb.54 192.168.54.2 192.168.10.0/24 Intra Network IP 1 irb.100 192.168.54.0/24 Intra Network IP 1 irb.54 192.168.90.0/24 Intra Network IP 1 ae0.0 -
Show OSPF neighbors on Switch B.
root@EX9200-B> show ospf neighbor Address Interface State ID Pri Dead 192.168.90.1 ae0.0 Full 192.168.39.1 128 32 192.168.10.3 irb.100 Full 192.168.39.1 128 34 192.168.54.1 irb.54 Full 192.168.39.1 128 37
-
Show OSPF routing table on Switch B.
root@EX9200-B> show ospf route Topology default Route Table: Prefix Path Route NH Metric NextHop Nexthop Type Type Type Interface Address/LSP 192.168.39.1 Intra Router IP 1 ae0.0 192.168.90.1 irb.100 192.168.10.3 irb.54 192.168.54.1 192.168.39.1/32 Intra Network IP 1 ae0.0 192.168.90.1 irb.100 192.168.10.3 irb.54 192.168.54.1 192.168.39.2/32 Intra Network IP 0 lo0.0 192.168.10.0/24 Intra Network IP 1 irb.100 192.168.54.0/24 Intra Network IP 1 irb.54 192.168.90.0/24 Intra Network IP 1 ae0.0
Example: Configure Optional Features For Multichassis Link Aggregation
This example shows how to configure optional features that can be combined with MC LAG.
- (Optional) Configuring RSTP
- (Optional) Configuring IGMP Snooping
- (Optional) Configuring VRRP
- (Optional) Configuring MAC Address Synchronization
- (Optional) Configuring OSPF
- (Optional) Configuring PIM
- (Optional) Configuring DHCP Relay
(Optional) Configuring RSTP
CLI Quick Configuration
QFX1 and QFX2
set protocols rstp interface xe-0/0/3 edge set protocols rstp interface ae0 disable set protocols rstp interface all mode point-to-point set protocols rstp bpdu-block-on-edge
Configuring QFX1 and QFX2
Step-by-Step Procedure
To enable RSTP:
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode.
-
Configure the MC-LAG interfaces as edge ports on QFX1 and QFX2.
[edit] user@switch# set protocols rstp interface xe-0/0/3 edge
-
Disable RSTP on the ICL-PL interfaces on QFX1 and QFX2:
[edit] user@switch# set protocols rstp interface ae0 disable
-
Enable RSTP globally on all interfaces on QFX1 and QFX2.
[edit] user@switch# set protocols rstp interface all mode point-to-point
-
Enable BPDU blocking on all interfaces except for the ICL-PL interfaces on QFX1 and QFX2.
Note:The ae1 interface is a downstream interface. This is why RSTP and bpdu-block-on-edge need to be configured.
[edit] user@switch# set protocols rstp bpdu-block-on-edge
QFX1 and QFX2
From configuration mode, confirm your configuration by entering the
show protocols rstp commands. If the output does not
display the intended configuration, repeat the instructions in this example
to correct the configuration.
user@switch> show protocols rstp
rstp {
interface xe-0/0/3 {
edge;
}
interface ae0 {
disable;
}
interface all {
mode point-to-point;
}
bpdu-block-on-edge;
(Optional) Configuring IGMP Snooping
CLI Quick Configuration
QFX1 and QFX2
set protocols igmp-snooping vlan all
Configuring QFX1 and QFX2
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode .
To configure QFX1 and QFX2:
Enable IGMP snooping for all VLANs.
[edit protocols] user@switch# set igmp-snooping vlan all
QFX1 and QFX2
From configuration mode, confirm your configuration by entering
the show protocols igmp and show multicast-snooping-options commands. If the output does not display the intended configuration,
repeat the instructions in this example to correct the configuration.
user@switch> show protocols igmp
igmp-snooping {
vlan all;
}
(Optional) Configuring VRRP
CLI Quick Configuration
QFX1
set interfaces irb unit 50 family inet address 10.50.1.1/30 vrrp-group 1 virtual-address 10.50.1.10 set interfaces irb unit 50 family inet address 10.50.1.1/30 vrrp-group 1 priority 200 set interfaces irb unit 50 family inet address 10.50.1.1/30 vrrp-group 1 accept-data
QFX2
set interfaces irb unit 50 family inet address 10.50.1.2/30 vrrp-group 1 virtual-address 10.50.1.10 set interfaces irb unit 50 family inet address 10.50.1.2/30 vrrp-group 1 priority 150 set interfaces irb unit 50 family inet address 10.50.1.2/30 vrrp-group 1 accept-data
Configuring QFX1
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode .
To configure QFX1:
Enable VRRP on the MC-LAGs by creating an IRB interface for each MC-LAG, assign a virtual IP address that is shared between each switch in the VRRP group, and assign an individual IP address for each individual member in the VRRP group.
[edit interfaces] user@switch# set interfaces irb unit 50 family inet address 10.50.1.1/30 vrrp-group 1 virtual-address 10.50.1.10 user@switch# set interfaces irb unit 50 family inet address 10.50.1.1/30 vrrp-group 1 priority 200 user@switch# set interfaces irb unit 50 family inet address 10.50.1.2/30 vrrp-group 1 accept-data
QFX1
From configuration mode, confirm your configuration by entering the show interfaces irb
unit 50 family inet address 10.50.1.1/30 vrrp-group command. If
the output does not display the intended configuration, repeat the
instructions in this example to correct the configuration.
user@switch> show interfaces irb unit 50 family inet address 10.50.1.1/30 vrrp-group
vrrp-group 1 {
virtual-address 10.50.1.10;
priority 200;
accept-data;
}
Configuring QFX2
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode.
To configure QFX1:
Enable VRRP on the MC-LAGs by creating an IRB interface for each MC-LAG, assign a virtual IP address that is shared between each switch in the VRRP group, and assign an individual IP address for each individual member in the VRRP group.
[edit interfaces] user@switch# set interfaces irb unit 50 family inet address 10.50.1.2/30 vrrp-group 1 virtual-address 10.50.1.10 user@switch# set interfaces irb unit 50 family inet address 10.50.1.2/30 vrrp-group 1 priority 150 user@switch# set interfaces irb unit 50 family inet address 10.50.1.2/30 vrrp-group 1 accept-data
QFX2
From configuration mode, confirm your configuration by entering the show interfaces irb
unit 50 family inet address 10.50.1.2/30 vrrp-group commands.
If the output does not display the intended configuration, repeat the
instructions in this example to correct the configuration.
user@switch> show interfaces irb unit 50 family inet address 10.50.1.2/30 vrrp-group
vrrp-group 1 {
virtual-address 10.50.1.10;
priority 150;
accept-data;
}
(Optional) Configuring MAC Address Synchronization
You cannot configure both MAC synchronization and VRRP.
You must configure the same IP address on the IRB interface in the VLAN on both MC-LAG peers.
CLI Quick Configuration
QFX1 and QFX2
set vlans v10 mcae-mac-synchronize
Configuring QFX1 and QFX2
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode .
To configure QFX1:
Configure MAC address synchronization in the MC-LAG VLAN on both QFX1 and QFX2.
[edit] user@switch# set vlans v10 mcae-mac-synchronize
QFX1 and QFX2
From configuration mode, confirm your configuration by entering
the show vlans v10 command. If the output does not display
the intended configuration, repeat the instructions in this example
to correct the configuration.
user@switch> show vlans v10
v10 {
vlan-id 10;
l3-interface irb.10;
mcae-mac-synchronize;
}
(Optional) Configuring OSPF
CLI Quick Configuration
QFX1, QFX2, and QFX3
set protocols ospf area 0.0.0.0 interface irb.10
Configuring QFX1 and QFX2
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode .
To configure QFX1 and QFX2:
-
Configure an OSPF area on QFX1, QFX2.
[edit protocols] user@switch# set ospf area 0.0.0.0 interface irb.10
QFX1 and QFX2
From configuration mode, confirm your configuration by entering
the show protocols ospf commands. If the output does not
display the intended configuration, repeat the instructions in this
example to correct the configuration.
user@switch> show protocols ospf
ospf {
area 0.0.0.0 {
interface irb.10 {
}
}
}
(Optional) Configuring PIM
CLI Quick Configuration
QFX1
set protocols pim rp static address 10.0.0.3 group-ranges 224.0.0.0/4 set protocols pim interface irb.50 priority 200 set protocols pim interface irb.50 dual-dr set protocols pim interface irb.50 family inet bfd-liveness-detection minimum-receive-interval 700 set protocols pim interface irb.50 family inet bfd-liveness-detection transmit-interval minimum-interval 350 set protocols pim interface irb.50 family inet bfd-liveness-detection transmit-interval threshold 500
QFX2
set protocols pim rp static address 10.0.0.3 group-ranges 224.0.0.0/4 set protocols pim interface irb.50 priority 500 set protocols pim interface irb.50 dual-dr set protocols pim interface irb.50 family inet bfd-liveness-detection minimum-receive-interval 700 set protocols pim interface irb.50 family inet bfd-liveness-detection transmit-interval minimum-interval 350 set protocols pim interface irb.50 family inet bfd-liveness-detection transmit-interval threshold 500
Configuring QFX1 and QFX2
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode .
To configure PIM as the multicast protocol on QFX1:
Configure a static rendezvous point (RP) address on QFX1 and QFX2.
[edit protocols pim] user@switch# set rp static address 10.0.0.3
Configure the address ranges of the multicast groups for which QFX1 and QFX2 can be a rendezvous point (RP).
[edit protocols pim rp static address 10.0.0.3] user@switch# set group-ranges 224.0.0.0/4
Enable PIM on the VLAN interfaces for the MC-LAGs on QFX1 and QFX2.
[edit protocols pim] user@switch# set interface irb.500 dual-dr
Configure each PIM interface’s priority for being selected as the designated router (DR) on QFX1 and QFX2.
An interface with a higher priority value has a higher probability of being selected as the DR.
QFX1: [edit protocols pim] user@switch# set interface irb.500 priority 200
QFX2: [edit protocols pim] user@switch# set interface irb.500 priority 500
Configure the minimum receive interval, minimum transmit interval, and transmit interval threshold for a Bidirectional Forwarding Detection (BFD) session for the PIM interfaces on QFX1 and QFX2.
[edit protocols pim] user@switch# set interface irb.500 family inet bfd-liveness-detection minimum-receive-interval 700 user@switch# set interface irb.500 family inet bfd-liveness-detection transmit-interval minimum-interval 350 user@switch# set interface irb.500 family inet bfd-liveness-detection transmit-interval threshold 500
Results
QFX1
From configuration mode, confirm your configuration by entering
the show protocols pim commands. If the output does not
display the intended configuration, repeat the instructions in this
example to correct the configuration.
user@QFX1> show protocols pim
rp {
static {
address 10.0.0.3 {
group-ranges {
224.0.0.0/4;
}
}
}
}
interface irb.50 {
family inet {
bfd-liveness-detection {
minimum-receive-interval 700;
transmit-interval {
minimum-interval 350;
threshold 500;
}
}
}
priority 200;
dual-dr;
}QFX2
From configuration mode, confirm your configuration by entering the show protocols
pim command. If the output does not display the intended
configuration, repeat the instructions in this example to correct the
configuration.
user@switch> show protocols pim
rp {
static {
address 10.0.0.3 {
group-ranges {
224.0.0.0/4;
}
}
}
}
interface irb.50 {
family inet {
bfd-liveness-detection {
minimum-receive-interval 700;
transmit-interval {
minimum-interval 350;
threshold 500;
}
}
}
priority 500;
dual-dr;
}(Optional) Configuring DHCP Relay
CLI Quick Configuration
QFX1 and QFX2
set forwarding-options dhcp-relay forward-snooped-clients all-interfaces set forwarding-options dhcp-relay overrides allow-snooped-clients set forwarding-options dhcp-relay server-group GVP-DHCP 10.105.5.202 set forwarding-options dhcp-relay active-server-group GVP-DHCP set forwarding-options dhcp-relay route-suppression destination set forwarding-options dhcp-relay group Floor1 interface irb.500 set forwarding-options dhcp-relay relay-option-82 circuit-id use-interface-description device
Configuring QFX1 and QFX2
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy. For information about navigating the CLI, see Using the CLI Editor in Configuration Mode .
To configure QFX1 and QFX2:
Configure forward snooped unicast packets on all interfaces.
[edit fowarding-options] user@switch# set dhcp-relay forward-snooped-clients all-interfaces
Create a binding entry to snoop unicast clients.
[edit forwarding-options] user@switch# set dhcp-relay overrides allow-snooped-clients
Create a DHCP server group.
[edit forwarding-options] user@switch# set dhcp-relay server-group GVP-DHCP 10.105.5.202
Apply a DHCP relay agent configuration to the named group of DHCP server addresses.
[edit forwarding-options] user@switch# set dhcp-relay active-server-group GVP-DHCP
Configure the relay agent to suppress the installation of ARP and route entries for corresponding client binding.
[edit forwarding-options] user@switch# set dhcp-relay route-suppression destination
Create a DHCP relay group that includes at least one interface.
DHCP runs on the interfaces defined in the DHCP groups.
[edit forwarding-options] user@switch# set dhcp-relay group Floor1 interface irb.500
Configure DHCP relay with option 82.
[edit forwarding-options] user@switch# set dhcp-relay relay-option-82 circuit-id use-interface-description device
QFX1 and QFX2
From configuration mode, confirm your configuration by entering
the show protocols pim commands. If the output does not
display the intended configuration, repeat the instructions in this
example to correct the configuration.
user@switch> show forwarding-options dhcp-relay
dhcp-relay {
forward-snooped-clients all-interfaces;
overrides {
allow-snooped-clients;
}
relay-option-82 {
circuit-id {
use-interface-description device;
}
}
server-group {
GVP-DHCP {
10.105.5.202;
}
}
active-server-group GVP-DHCP;
route-suppression {
destination;
}
group Floor1 {
interface irb.500;
}
}
Example: Simplifying Multichassis Link Aggregation on EX9200 Switches in the Core for Campus Networks
Requirements
This example uses the following hardware and software components:
-
Junos OS Release 16.1R1 for EX Series
-
Two EX9200 switches
This configuration example has been tested using the software release listed and is assumed to work on all later releases.
Before you configure an MC-LAG, be sure that you understand how to:
-
Configure aggregated Ethernet interfaces on a switch. See Configuring an Aggregated Ethernet Interface .
-
Configure the Link Aggregation Control Protocol (LACP) on aggregated Ethernet interfaces on a switch. See Configuring Aggregated Ethernet LACP (CLI Procedure) .
Overview
In this example, you configure an MC-LAG across two switches, consisting of two aggregated Ethernet interfaces, multichassis protection using the ICL, ICCP for the peers hosting the MC-LAG, and Layer 3 connectivity between MC-LAG peers. Layer 3 connectivity is required for ICCP.
To simplify the MC-LAG configuration process, you will enable configuration synchronization and configuration consistency check. Configuration synchronization enables you to easily propagate, synchronize, and commit configurations from one MC-LAG peer to another. You can log into any one of the MC-LAG peers to manage both MC-LAG peers, thus having a single point of management. Configuration consistency check uses the Inter-Chassis Control Protocol (ICCP) to exchange MC-LAG configuration parameters (chassis ID, service ID, and so on) and checks for any configuration inconsistencies across MC-LAG peers. When there is an inconsistency, you are notified and can take action to resolve it. Configuration consistency check is invoked after you issue a commit on an MC-LAG peer.
On the EX9200-A switch, you will configure the following configuration synchronization and configuration consistency check parameters:
-
Local, remote, and global configuration groups that are synchronized to the EX9200-B switch.
-
Conditional groups.
-
Apply groups.
-
NETCONF over SSH.
-
MC-LAG peer details and user authentication details for MC-LAG configuration synchronization.
-
peers-synchronizestatement to synchronize the configurations between local and remote MC-LAG peers by default. -
set multi-chassis mc-lag consistency-checkcommand for consistency check.
On the EX9200-B switch, the configuration process is much shorter and simpler. You will configure the following configuration synchronization and configuration consistency check parameters:
-
Apply groups.
-
NETCONF over SSH.
-
MC-LAG peer details and user authentication details for MC-LAG configuration synchronization.
-
peers-synchronizestatement to synchronize and commit the configurations between local and remote MC-LAG peers. -
multi-chassis mc-lag consistency-checkstatement to enable consistency check.
Topology
The topology used in this example consists of two switches hosting an MC-LAG. Figure 5 shows the topology of this example.
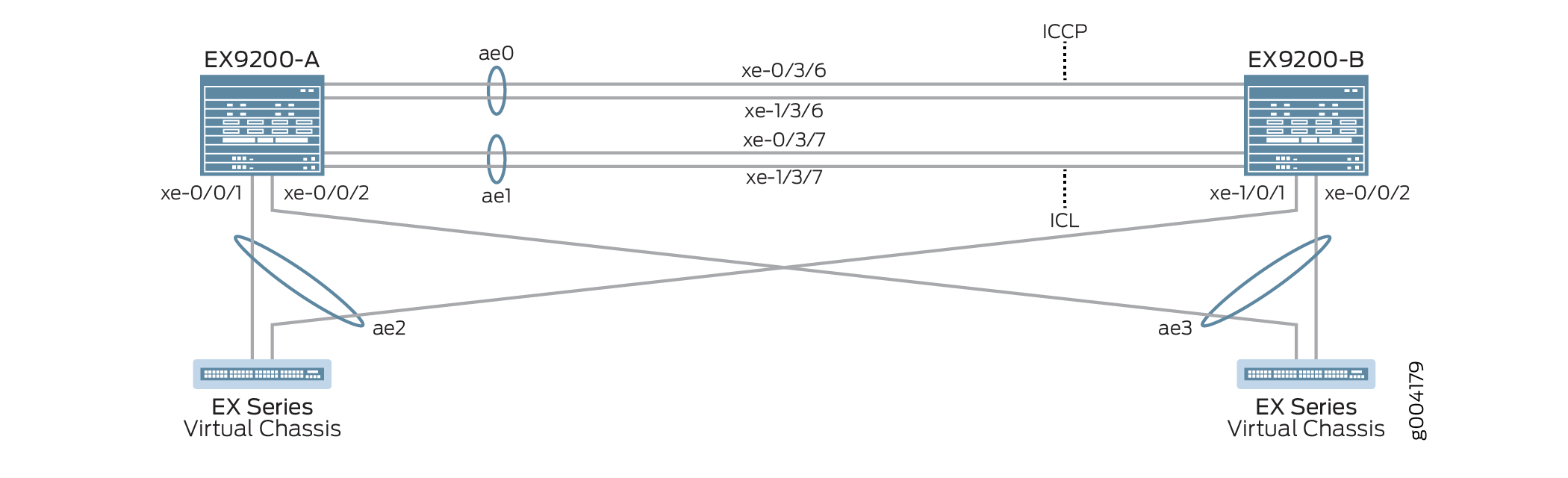
Table 2 details the topology used in this configuration example.
| Hostname | Base Hardware | Multichassis Link Aggregation Group |
|---|---|---|
|
EX9200-A EX9200-B |
EX9200 EX9200 |
ae0 is configured as an aggregated Ethernet interface, and is used as an ICCP link, and the following interfaces are part of ae0: xe-0/3/6 and xe-1/3/6. ae1 is configured as an aggregated Ethernet interface and is used as an ICL link, and the following interfaces are part of ae1: xe-0/3/7 and xe-1/3/7. ae2 is configured as an MC-LAG, and the following interfaces are part of ae2: xe-0/0/1 on Switch B and xe-1/0/1 on Switch A. ae3 is configured as an MC-LAG, and the following interface is part of ae3 on both Switch A and Switch B: xe-0/0/2. |
|
Virtual Chassis Virtual Chassis |
Not applicable. Virtual Chassis are shown only for illustration purposes. |
The Virtual Chassis are connected to the two EX9200 switches through LAG interfaces. The Virtual Chassis configuration is not included in this example and is only shown to illustrate a sample topology. |
Configuration
CLI Quick Configuration
To quickly configure this example, copy the
following commands, paste them in a text file, remove any line breaks,
change any details necessary to match your network configuration,
copy and paste the commands into the CLI at the [edit] hierarchy
level, and then enter commit from configuration
mode.
EX9200-A
set system login user MCLAG_Admin uid 2000 set system login user MCLAG_Admin class super-user set system login user MCLAG_Admin authentication encrypted-password "$ABC123" set system static-host-mapping EX9200-A inet 10.92.76.2 set system static-host-mapping EX9200-B inet 10.92.76.4 set system services netconf ssh set system commit peers-synchronize set system commit peers EX9200-B user MCLAG_Admin set system commit peers EX9200-B authentication "$ABC123" set interfaces irb unit 100 family inet address 192.168.100.2/24 arp 192.168.100.3 l2-interface ae1 set interfaces irb unit 100 family inet address 192.168.100.2/24 arp 192.168.100.3 mac 28:8a:1c:e5:3b:f0 set interfaces irb unit 100 family inet address 192.168.100.2/24 vrrp-group 1 virtual-address 192.168.100.1 set interfaces irb unit 100 family inet address 192.168.100.2/24 vrrp-group 1 priority 150 set interfaces irb unit 100 family inet address 192.168.100.2/24 vrrp-group 1 accept-data set interfaces lo0 unit 0 family inet address 172.16.32.5/32 set routing-options static route 0.0.0.0/0 next-hop 10.92.77.254 set protocols ospf area 0.0.0.0 interface lo0.0 passive set protocols ospf area 0.0.0.0 interface ae0.0 set protocols lldp interface all set chassis aggregated-devices ethernet device-count 20 set groups MC_Config_Global set groups MC_Config_Global when peers EX9200-A set groups MC_Config_Global when peers EX9200-B set groups MC_Config_Global interfaces xe-0/3/6 ether-options 802.3ad ae0 set groups MC_Config_Global interfaces xe-1/3/6 ether-options 802.3ad ae0 set groups MC_Config_Global interfaces ae0 description "ICCP Layer 3 Link with 2 members,xe-0/3/6,xe-1/3/6" set groups MC_Config_Global interfaces ae0 aggregated-ether-options lacp active set groups MC_Config_Global interfaces ae0 aggregated-ether-options lacp periodic fast set groups MC_Config_Global interfaces ae0 aggregated-ether-options lacp system-id 00:01:02:03:04:05 set groups MC_Config_Global interfaces ae0 aggregated-ether-options lacp admin-key 0 set groups MC_Config_Global interfaces xe-0/3/7 ether-options 802.3ad ae1 set groups MC_Config_Global interfaces xe-1/3/7 ether-options 802.3ad ae1 set groups MC_Config_Global interfaces ae1 description "ICL Layer 2 link with 2 members,xe-0/3/7,1/3/7" set groups MC_Config_Global interfaces ae1 unit 0 family ethernet-switching interface-mode trunk set groups MC_Config_Global interfaces ae1 unit 0 family ethernet-switching vlan members all set groups MC_Config_Global interfaces ae1 vlan-tagging set groups MC_Config_Global interfaces ae1 aggregated-ether-options lacp active set groups MC_Config_Global interfaces ae1 aggregated-ether-options lacp periodic fast set groups MC_Config_Global interfaces ae1 aggregated-ether-options lacp system-id 00:01:02:03:04:06 set groups MC_Config_Global interfaces ae1 aggregated-ether-options lacp admin-key 1 set groups MC_Config_Global interfaces xe-0/0/1 ether-options 802.3ad ae2 set groups MC_Config_Global interfaces xe-1/0/1 ether-options 802.3ad ae2 set groups MC_Config_Global interfaces ae2 unit 0 description “MC-LAG interface with members xe-0/0/1,xe-1/0/1” set groups MC_Config_Global interfaces ae2 unit 0 family ethernet-switching interface-mode trunk set groups MC_Config_Global interfaces ae2 unit 0 family ethernet-switching vlan members all set groups MC_Config_Global interfaces ae2 aggregated-ether-options lacp active set groups MC_Config_Global interfaces ae2 aggregated-ether-options lacp periodic fast set groups MC_Config_Global interfaces ae2 aggregated-ether-options lacp system-id 00:01:02:03:04:07 set groups MC_Config_Global interfaces ae2 aggregated-ether-options lacp admin-key 2 set groups MC_Config_Global interfaces ae2 aggregated-ether-options mc-ae mc-ae-id 2 set groups MC_Config_Global interfaces ae2 aggregated-ether-options mc-ae redundancy-group 1 set groups MC_Config_Global interfaces ae2 aggregated-ether-options mc-ae mode active-active set groups MC_Config_Global interfaces ae2 aggregated-ether-options mc-ae init-delay-time 520 set groups MC_Config_Global interfaces ae2 aggregated-ether-options mc-ae events iccp-peer-down prefer-status-control-active set groups MC_Config_Global interfaces xe-0/0/2 ether-options 802.3ad ae3 set groups MC_Config_Global interfaces ae3 unit 0 description “MC-LAG interface with members xe-0/0/2 on both switches” set groups MC_Config_Global interfaces ae3 unit 0 family ethernet-switching interface-mode trunk set groups MC_Config_Global interfaces ae3 unit 0 family ethernet-switching vlan members all set groups MC_Config_Global interfaces ae3 aggregated-ether-options lacp active set groups MC_Config_Global interfaces ae3 aggregated-ether-options lacp periodic fast set groups MC_Config_Global interfaces ae3 aggregated-ether-options lacp system-id 00:01:02:03:04:08 set groups MC_Config_Global interfaces ae3 aggregated-ether-options lacp admin-key 3 set groups MC_Config_Global interfaces ae3 aggregated-ether-options mc-ae mc-ae-id 3 set groups MC_Config_Global interfaces ae3 aggregated-ether-options mc-ae redundancy-group 1 set groups MC_Config_Global interfaces ae3 aggregated-ether-options mc-ae mode active-active set groups MC_Config_Global interfaces ae3 aggregated-ether-options mc-ae init-delay-time 520 set groups MC_Config_Global interfaces ae3 aggregated-ether-options mc-ae events iccp-peer-down prefer-status-control-active set groups MC_Config_Global vlans v100 vlan-id 100 set groups MC_Config_Global vlans v100 l3-interface irb.100 set groups MC_Config_Global multi-chassis mc-lag consistency-check set groups MC_Config_Global protocols rstp interface ae2 set groups MC_Config_Global protocols rstp interface ae3 set groups MC_Config_Global protocols rstp bridge-priority 0 set groups MC_Config_Global protocols rstp system-id 00:01:02:03:04:09 set groups MC_Config_Global switch-options service-id 1 set groups MC_Config_Local set groups MC_Config_Local interfaces ae0 unit 0 family inet address 172.16.32.9/30 set groups MC_Config_Local interfaces ae2 aggregated-ether-options mc-ae chassis-id 0 set groups MC_Config_Local interfaces ae2 aggregated-ether-options mc-ae status-control active set groups MC_Config_Local interfaces ae3 aggregated-ether-options mc-ae chassis-id 0 set groups MC_Config_Local interfaces ae3 aggregated-ether-options mc-ae status-control active set groups MC_Config_Remote set groups MC_Config_Remote interfaces ae0 unit 0 family inet address 172.16.32.10/30 set groups MC_Config_Remote interfaces ae2 aggregated-ether-options mc-ae chassis-id 1 set groups MC_Config_Remote interfaces ae2 aggregated-ether-options mc-ae status-control standby set groups MC_Config_Remote interfaces ae3 aggregated-ether-options mc-ae chassis-id 1 set groups MC_Config_Remote interfaces ae3 aggregated-ether-options mc-ae status-control standby set interfaces ae2 unit 0 multi-chassis-protection 172.16.32.6 interface ae1 set interfaces ae3 unit 0 multi-chassis-protection 172.16.32.6 interface ae1 set protocols iccp local-ip-addr 172.16.32.5 set protocols iccp peer 172.16.32.6 session-establishment-hold-time 50 set protocols iccp peer 172.16.32.6 redundancy-group-id-list 1 set protocols iccp peer 172.16.32.6 backup-liveness-detection backup-peer-ip 10.92.76.4 set protocols iccp peer 172.16.32.6 liveness-detection minimum-interval 2000 set protocols iccp peer 172.16.32.6 liveness-detection multiplier 4 set multi-chassis multi-chassis-protection 172.16.32.6 interface ae1 set apply-groups [ MC_Config_Global MC_Config_Local MC_Config_Remote ]
EX9200-B
set system login user MCLAG_Admin uid 2000 set system login user MCLAG_Admin class super-user set system login user MCLAG_Admin authentication encrypted-password "$ABC123" set system static-host-mapping EX9200-A inet 10.92.76.2 set system static-host-mapping EX9200-B inet 10.92.76.4 set system services netconf ssh set system commit peers-synchronize set system commit peers EX9200-A user MCLAG_Admin set system commit peers EX9200-A authentication "$ABC123" set interfaces irb unit 100 family inet address 192.168.100.3/24 arp 192.168.100.2 l2-interface ae1 set interfaces irb unit 100 family inet address 192.168.100.3/24 arp 192.168.100.2 mac 28:8a:1c:e3:f7:f0 set interfaces irb unit 100 family inet address 192.168.100.3/24 vrrp-group 1 virtual-address 192.168.100.1 set interfaces irb unit 100 family inet address 192.168.100.3/24 vrrp-group 1 priority 100 set interfaces irb unit 100 family inet address 192.168.100.3/24 vrrp-group 1 accept-data set interfaces lo0 unit 0 family inet address 172.16.32.6/32 set routing-options static route 0.0.0.0/0 next-hop 10.92.77.254 set protocols ospf area 0.0.0.0 interface lo0 passive set protocols ospf area 0.0.0.0 interface ae0 set protocols lldp interface all set chassis aggregated-devices ethernet device-count 20 set interfaces ae2 unit 0 multi-chassis-protection 172.16.32.5 interface ae1 set interfaces ae3 unit 0 multi-chassis-protection 172.16.32.5 interface ae1 set protocols iccp local-ip-addr 172.16.32.6 set protocols iccp peer 172.16.32.5 session-establishment-hold-time 50 set protocols iccp peer 172.16.32.5 redundancy-group-id-list 1 set protocols iccp peer 172.16.32.5 backup-liveness-detection backup-peer-ip 10.92.76.2 set protocols iccp peer 172.16.32.5 liveness-detection minimum-interval 2000 set protocols iccp peer 172.16.32.5 liveness-detection multiplier 4 set apply-groups [ MC_Config_Global MC_Config_Local MC_Config_Remote ]
Configuring MC-LAG on EX9200-A
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy.
-
Create a user account to access the switch, along with a user identifier (UID), a login class, and a password.
[edit system] user@EX9200-A# set login user MCLAG_Admin uid 2000 user@EX9200-A# set login user MCLAG_Admin class super-user user@EX9200-A# set login user MCLAG_Admin authentication encrypted-password “$ABC123”
-
Statically map EX9200-A to 10.92.76.2 and EX9200-B to 10.92.76.4.
[edit system] user@EX9200-A# set static-host-mapping EX9200-A inet 10.92.76.2 user@EX9200-A# set static-host-mapping EX9200-B inet 10.92.76.4
-
Enable NETCONF service using SSH.
[edit system] user@EX9200-A# set services netconf ssh
-
Enable the
peers-synchronizestatement to copy and load the MC-LAG configuration from EX9200-A to EX9200-B by default.[edit system] user@EX9200-A# set commit peers-synchronize
-
Configure the hostname, usernames, and authentication details for EX9200-B, the peer with which EX9200-A will be synchronizing the MC-LAG configuration.
[edit system] user@EX9200-A# set commit peers EX9200-B user MCLAG_Admin user@EX9200-A# set commit peers EX9200-B user authentication “$ABC123”
-
Configure an MC-LAG IRB and configure static Address Resolution Protocol (ARP) on the MC-LAG IRB peers to allow routing protocols to traverse the IRB interface.
[edit interfaces] user@EX9200-A# set irb unit 100 family inet address 192.168.100.2/24 arp 192.168.100.3 l2-interface ae1 user@EX9200-A# set irb unit 100 family inet address 192.168.100.2/24 arp 192.168.100.3 mac 28:8a:1c:e5:3b:f0
-
Enable VRRP on the MC-LAGs by assigning a virtual IP address that is shared between each switch in the VRRP group, and assigning an individual IP address for each individual member in the VRRP group.
[edit interfaces] user@EX9200-A# set irb unit 100 family inet address 192.168.100.2/24 vrrp-group 1 virtual-address 192.168.100.1 user@EX9200-A# set irb unit 100 family inet address 192.168.100.2/24 vrrp-group 1 priority 150 user@EX9200-A# set irb unit 100 family inet address 192.168.100.2/24 vrrp-group 1 accept-data
-
Configure a loopback interface.
[edit interfaces] user@EX9200-A# set lo0 unit 0 family inet address 172.16.32.5/32
-
Configure a default gateway.
[edit routing-options] user@EX9200-A# set static route 0.0.0.0 next-hop 10.92.77.254
-
Configure an OSPF area that includes the loopback interface and the ICCP interface.
[edit protocols] user@EX9200-A# set ospf area 0.0.0.0 interface lo0 passive user@EX9200-A# set ospf area 0.0.0.0 interface ae0
-
Configure Link Layer Discovery Protocol for all interfaces.
[edit protocols] user@EX9200-A# set lldp interface all
-
Configure the number of aggregated Ethernet interfaces to be created on EX9200-A.
[edit chassis] user@EX9200-A# set aggregated-devices ethernet device-count 20
-
Configure a configuration group for a global MC-LAG configuration that applies to both EX9200-A and EX9200-B.
The global configuration is synchronized between EX9200-A and EX9200-B.
[edit groups] user@EX9200-A# set MC_Config_Global
-
Specify the peers that will apply the MC_Config_Global configuration group.
[edit groups] user@EX9200-A# set MC_Config_Global when peers EX9200-A user@EX9200-A# set MC_Config_Global when peers EX9200-B
-
Add member interfaces to the aggregated Ethernet interfaces that will be used for the Inter-Chassis Control Protocol (ICCP) interface.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces xe-0/3/6 ether-options 802.3ad ae0 user@EX9200-A# set MC_Config_Global interfaces xe-1/3/6 ether-options 802.3ad ae0
-
Configure the aggregated Ethernet interface (ae0) that will be used for the Inter-Chassis Control Protocol (ICCP) interface.
Note:You will be configuring the IP address for ae0 in a later step.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae0 description "ICCP Layer 3 Link with 2 members,xe-0/3/6,xe-1/3/6"
-
Configure the LACP parameters on ae0.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae0 aggregated-ether-options lacp active user@EX9200-A# set MC_Config_Global interfaces ae0 aggregated-ether-options lacp periodic fast
-
Configure the LACP system ID on ae0.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae0 aggregated-ether-options lacp system-id 00:01:02:03:04:05
-
Configure the LACP administrative key on ae0.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae0 aggregated-ether-options lacp admin-key 0
-
Add member interfaces to the aggregated Ethernet interface (ae1) that will be used for the ICL.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces xe-0/3/7 ether-options 802.3ad ae1 user@EX9200-A# set MC_Config_Global interfaces xe-1/3/7 ether-options 802.3ad ae1
-
Configure the aggregated Ethernet interface that will be used for the ICL.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae1 description "ICL Layer 2 link with 2 members,xe-0/3/7,1/3/7"
-
Configure ae1 as a Layer 2 interface.
[edit groups] user@EX9200-A# set MC_Config_Global ae1 unit 0 family ethernet-switching interface-mode trunk user@EX9200-A# set MC_Config_Global ae1 unit 0 family ethernet-switching vlan members all
-
Enable the reception and transmission of 802.1Q VLAN-tagged frames on ae1.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae1 vlan-tagging
-
Configure the LACP parameters on ae1.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae1 aggregated-ether-options lacp active user@EX9200-A# set MC_Config_Global interfaces ae1 aggregated-ether-options lacp periodic fast
-
Configure the LACP system ID on ae1.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae1 aggregated-ether-options lacp system-id 00:01:02:03:04:06
-
Configure the LACP administrative key on ae1.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae1 aggregated-ether-options lacp admin-key 1
-
Add member interfaces to the aggregated Ethernet interface (ae2) that will be used as the MC-LAG interface.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces xe-0/0/1 ether-options 802.3ad ae2 user@EX9200-A# set MC_Config_Global interfaces xe-1/0/1 ether-options 802.3ad ae2
-
Configure the aggregated Ethernet interface (ae2) that will be used as an MC-LAG interface.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae2 description “MC-LAG interface with members xe-0/0/1,xe-1/0/1”
-
Configure ae2 as a Layer 2 interface.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae2 unit 0 family ethernet-switching interface-mode trunk user@EX9200-A# set MC_Config_Global interfaces ae2 unit 0 family ethernet-switching vlan members all
-
Configure the LACP parameters on ae2.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae2 aggregated-ether-options lacp active user@EX9200-A# set MC_Config_Global interfaces ae2 aggregated-ether-options lacp periodic fast
-
Configure the LACP system ID on ae2.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae2 aggregated-ether-options lacp system-id 00:01:02:03:04:07
-
Configure the LACP administrative key on ae2.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae2 aggregated-ether-options lacp admin-key 2
-
Configure the MC-AE interface properties on ae2.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae2 aggregated-ether-options mc-ae mc-ae-id 2 user@EX9200-A# set MC_Config_Global interfaces ae2 aggregated-ether-options mc-ae redundancy-group 1
-
Specify the mode of ae2 to be active-active.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae2 aggregated-ether-options mc-ae mode active-active
-
Specify the time in seconds to delay bringing the MC-AE interface to the up state after rebooting an MC-LAG peer.
By delaying the bring-up of the interface until after protocol convergence, you can prevent packet loss during the recovery of failed links and devices. This network configuration example uses a delay time of 520 seconds. This delay time might not be optimal for your network and should be adjusted to fit your network requirements.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae2 aggregated-ether-options mc-ae init-delay-time 520
-
Specify that if a peer of the MC-LAG group goes down, the peer that is configured as status-control active becomes the active peer.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae2 aggregated-ether-options mc-ae events iccp-peer-down prefer-status-control-active
-
Add member interfaces to the aggregated Ethernet interface (ae3) that will be used as the MC-LAG interface.
Note:EX9200-B uses the same interface name of xe-0/0/2.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces xe-0/0/2 ether-options 802.3ad ae3
-
Configure the aggregated Ethernet interface (ae3) that will be used as an MC-LAG interface.
[edit groups] user@EX9200-A# set groups MC_Config_Global interfaces ae3 description “MC-LAG interface with members xe-0/0/2 on both switches”
-
Configure ae3 as a Layer 2 interface.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae3 unit 0 family ethernet-switching interface-mode trunk user@EX9200-A# set MC_Config_Global interfaces ae3 unit 0 family ethernet-switching vlan members all
-
Configure the LACP parameters on ae3.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae3 aggregated-ether-options lacp active user@EX9200-A# set MC_Config_Global interfaces ae3 aggregated-ether-options lacp periodic fast
-
Configure the LACP system ID on ae3.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae3 aggregated-ether-options lacp system-id 00:01:02:03:04:08
-
Configure the LACP administrative key on ae3.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae3 aggregated-ether-options lacp admin-key 3
-
Configure the MC-AE interface properties on ae3.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae3 aggregated-ether-options mc-ae mc-ae-id 3 user@EX9200-A# set MC_Config_Global interfaces ae3 aggregated-ether-options mc-ae redundancy-group 1
-
Specify the mode of ae3 to be active-active.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae3 aggregated-ether-options mc-ae mode active-active
-
Specify the time in seconds to delay bringing the MC-AE interface to the up state after rebooting an MC-LAG peer.
By delaying the bring-up of the interface until after protocol convergence, you can prevent packet loss during the recovery of failed links and devices. This network configuration example uses a delay time of 520 seconds. This delay time might not be optimal for your network and should be adjusted to fit your network requirements.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae3 aggregated-ether-options mc-ae init-delay-time 520
-
Specify that if a peer of the MC-LAG group goes down, the peer that is configured as status-control active becomes the active peer.
[edit groups] user@EX9200-A# set MC_Config_Global interfaces ae3 aggregated-ether-options mc-ae events iccp-peer-down prefer-status-control-active
-
Configure VLAN 100 to connect end users.
[edit groups] user@EX9200-A# set MC_Config_Global vlans v100 vlan-id 100
-
Configure the routed VLAN interface for VLAN 100.
[edit groups] user@EX9200-A# set MC_Config_Global vlans v100 l3-interface irb.100
-
Enable consistency check.
[edit groups] user@EX9200-A# set MC_Config_Global multi-chassis mc-lag consistency-check
-
Enable the Rapid Spanning Tree Protocol on the ae2 and ae3 interfaces (MC-LAG interfaces) for optional loop prevention.
[edit groups] user@EX9200-A# set MC_Config_Global protocols rstp interfaces ae2 user@EX9200-A# set MC_Config_Global protocols rstp interfaces ae3
-
Configure the RSTP bridge priority.
Setting the bridge priority to 0 will make the MC-AE nodes of EX9200-A and EX9200-B the best priority.
[edit groups] user@EX9200-A# set MC_Config_Global protocols rstp bridge-priority 0
-
Configure the RSTP system identifier value.
[edit groups] user@EX9200-A# set MC_Config_Global protocols rstp system-id 00:01:02:03:04:09
-
Specify the switch service ID.
The switch service ID is used to synchronize applications, ARP, and MAC learning across MC-LAG members.
[edit groups] user@EX9200-A# set MC_Config_Global switch-options service-id 1
-
Configure a configuration group for an MC-LAG configuration that applies to the local peer.
[edit groups] user@EX9200-A# set MC_Config_Local
-
Configure the ICCP interface (ae0) as a Layer 3 interface.
[edit groups] user@EX9200-A# set MC_Config_Local interfaces ae0 unit 0 family inet address 172.16.32.9/30
-
Specify a unique chassis ID for the MC-LAG (ae2) that the aggregated Ethernet interface belongs to.
[edit groups] user@EX9200-A# set MC_Config_Local interfaces ae2 aggregated-ether-options mc-ae chassis-id 0
-
Specify the status-control setting of ae2 to be active.
[edit groups] user@EX9200-A# set MC_Config_Local interfaces ae2 aggregated-ether-options mc-ae status-control active
-
Specify a unique chassis ID for the MC-LAG (ae3) that the aggregated Ethernet interface belongs to.
[edit groups] user@EX9200-A# set MC_Config_Local interfaces ae3 aggregated-ether-options mc-ae chassis-id 0
-
Specify the status-control setting of ae3 to be active..
[edit groups] user@EX9200-A# set MC_Config_Local interfaces ae3 aggregated-ether-options mc-ae status-control active
-
Configure a configuration group for an MC-LAG configuration that applies to the remote peer.
[edit groups] user@EX9200-A# set MC_Config_Remote
-
Configure ae0 as a Layer 3 interface.
[edit groups] user@EX9200-A# set MC_Config_Remote interfaces ae0 unit 0 family inet address 172.16.32.10/30
-
Specify a unique chassis ID for the MC-LAG (ae2) that the aggregated Ethernet interface belongs to.
[edit groups] user@EX9200-A# set MC_Config_Remote interfaces ae2 aggregated-ether-options mc-ae chassis-id 1
-
Specify the status-control setting of ae2 to be standby.
[edit groups] user@EX9200-A# set MC_Config_Remote interfaces ae2 aggregated-ether-options mc-ae status-control standby
-
Specify a unique chassis ID for the MC-LAG (ae3) that the aggregated Ethernet interface belongs to.
[edit groups] user@EX9200-A# set MC_Config_Remote interfaces ae3 aggregated-ether-options mc-ae chassis-id 1
-
Specify the status-control setting of ae3 to be standby.
[edit interfaces] user@EX9200-A# set MC_Config_Remote interfaces ae3 aggregated-ether-options mc-ae status-control standby
-
Specify that if a peer of the MC-LAG group goes down, the peer that is configured as status-control active becomes the active peer.
[edit interfaces] user@EX9200-A# set MC_Config_Remote interfaces ae3 aggregated-ether-options mc-ae events iccp-peer-down prefer-status-control-standby
-
Enable link protection between the two MC-LAG peers.
Assign interface ae1 to act as the ICL to protect the MC-AE interfaces, ae2 and ae3, in case of failure.
[edit interfaces] user@EX9200-A# set ae2 unit 0 multi-chassis-protection 172.16.32.6 interface ae1
user@EX9200-A# set ae3 unit 0 multi-chassis-protection 172.16.32.6 interface ae1
-
Specify the local IP address of the ICCP interface.
[edit protocols] user@EX9200-A# set iccp local-ip-addr 172.16.32.5
-
Configure the session establishment hold time for ICCP to connect faster.
Note:We recommend 50 seconds as the session establishment hold time value.
[edit protocols] user@EX9200-A# set iccp peer 172.16.32.6 session-establishment-hold-time 50 user@EX9200-A# set iccp peer 172.16.32.6 redundancy-group-id-list 1 user@EX9200-A# set iccp peer 172.16.32.6 backup-liveness-detection backup-peer-ip 10.92.76.4
-
To enable BFD for ICCP, configure the minimum receive interval.
We recommend a minimum receive interval value of 6 seconds.
[edit protocols] user@EX9200-A# set iccp peer 172.16.32.6 liveness-detection minimum-interval 2000 user@EX9200-A# set iccp peer 172.16.32.6 liveness-detection multiplier 4
-
Apply the groups configured earlier, so that the Junos configuration will inherit the statements from the MC_Config_Global, MC_Config_Local, and MC_Config_Remote configuration groups.
[edit] user@EX9200-A# set apply-groups [ MC_Config_Global MC_Config_Local MC_Config_Remote ]
Configuring MC-LAG on EX9200-B
Step-by-Step Procedure
The following example requires you to navigate various levels in the configuration hierarchy.
-
Create a user account to access the switch, along with a user identifier (UID), a login class, and a password.
[edit system] user@EX9200-A# set login user MCLAG_Admin uid 2000 user@EX9200-B# set login user MCLAG_Admin class super-user user@EX9200-B# set login user MCLAG_Admin authentication encrypted-password “$ABC123”
-
Statically map EX9200-A to 10.92.76.2 and EX9200-B to 10.92.76.4.
[edit system] user@EX9200-B# set static-host-mapping EX9200-A inet 10.92.76.2 user@EX9200-B# set static-host-mapping EX9200-B inet 10.92.76.4
-
Enable NETCONF service using SSH.
[edit system] user@EX9200-B# set services netconf ssh
-
Enable the
peers-synchronizestatement to copy and load the MC-LAG configuration from EX9200-B to EX9200-A by default.[edit system] user@EX9200-B# set commit peers-synchronize
-
Configure the hostname, usernames, and authentication details for EX9200-A, the peer with which EX9200-B will be synchronizing the MC-LAG configuration.
[edit system] user@EX9200-B# set commit peers EX9200-A user MCLAG_Admin user@EX9200-A# set commit peers EX9200-A authentication "$ABC123"
-
Configure an MC-LAG IRB and configure static Address Resolution Protocol (ARP) on the MC-LAG IRB peers to allow routing protocols to traverse the IRB interface.
[edit interfaces] user@EX9200-B# set irb unit 100 family inet address 192.168.100.3/24 arp 192.168.100.2 l2-interface ae1 user@EX9200-B# set irb unit 100 family inet address 192.168.100.3/24 arp 192.168.100.2 mac 28:8a:1c:e3:f7:f0
-
Enable VRRP on the MC-LAGs by assigning a virtual IP address that is shared between each switch in the VRRP group, and assigning an individual IP address for each individual member in the VRRP group.
[edit interfaces] user@EX9200-B# set irb unit 100 family inet address 192.168.100.3/24 vrrp-group 1 virtual-address 192.168.100.1 user@EX9200-B# set irb unit 100 family inet address 192.168.100.3/24 vrrp-group 1 priority 100 user@EX9200-B# set irb unit 100 family inet address 192.168.100.3/24 vrrp-group 1 accept-data
-
Configure a loopback interface.
[edit interfaces] user@EX9200-B# set lo0 unit 0 family inet address 172.16.32.6/32
-
Configure a default gateway.
[edit routing-options] user@EX9200-B# set static route 0.0.0.0 next-hop 10.92.77.254
-
Configure an OSPF area that includes the loopback interface and the ICCP interface.
[edit protocols] user@EX9200-B# set ospf area 0.0.0.0 interface lo0 passive user@EX9200-B# set ospf area 0.0.0.0 interface ae0
-
Configure Link Layer Discovery Protocol for all interfaces.
[edit protocols] user@EX9200-B# set lldp interface all
-
Configure the number of aggregated Ethernet interfaces to be created on EX9200-B.
[edit chassis] user@EX9200-B# set aggregated-devices ethernet device-count 20
-
Enable link protection between the two MC-LAG peers.
Assign interface ae1 to act as the ICL to protect the MC-AE interfaces, ae2 and ae3, in case of failure.
[edit interfaces] user@EX9200-B# set ae2 unit 0 multi-chassis-protection 172.16.32.5 interface ae1 user@EX9200-B# set ae3 unit 0 multi-chassis-protection 172.16.32.5 interface ae1
-
Specify the local IP address of the ICCP interface.
[edit protocols] user@EX9200-B# set iccp local-ip-addr 172.16.32.6
-
Configure the session establishment hold time for ICCP to connect faster.
Note:We recommend 50 seconds as the session establishment hold time value.
[edit protocols] user@EX9200-B# set iccp peer 172.16.32.5 session-establishment-hold-time 50 user@EX9200-B# set iccp peer 172.16.32.5 redundancy-group-id-list 1 user@EX9200-B# set iccp peer 172.16.32.5 backup-liveness-detection backup-peer-ip 10.92.76.2
-
To enable BFD for ICCP, configure the minimum receive interval.
We recommend a minimum receive interval value of 6 seconds.
[edit protocols] user@EX9200-B# set iccp peer 172.16.32.5 liveness-detection minimum-interval 2000 user@EX9200-B# set iccp peer 172.16.32.5 liveness-detection multiplier 4
-
Apply the groups configured earlier, so that the Junos configuration will inherit the statements from the MC_Config_Global, MC_Config_Local, and MC_Config_Remote configuration groups.
[edit] user@EX9200-B# set apply-groups [ MC_Config_Global MC_Config_Local MC_Config_Remote ]
Results
Display the results of the configuration on EX9200-A before you commit the configuration.
user@EX9200-A# show system services
netconf {
ssh;
}
user@EX9200-A# show system commit
peers-synchronize;
peers {
EX9200-B {
user MCLAG_Admin;
authentication "$ABC123”;
}
}
}
user@EX9200-A# show interfaces
ae2 {
unit 0 {
multi-chassis-protection 172.16.32.6 {
interface ae1;
}
}
}
ae3 {
unit 0 {
multi-chassis-protection 172.16.32.6 {
interface ae1;
}
}
}
irb {
unit 100 {
family inet {
address 192.168.100.2/24 {
arp 192.168.100.3 l2-interface ae1.0 mac 28:8a:1c:e5:3b:f0;
vrrp-group 1 {
virtual-address 192.168.100.1;
priority 150;
accept-data;
}
}
}
}
}
lo0 {
unit 0 {
family inet {
address 172.16.32.5/32;
}
}
}
user@EX9200-A# show routing-options
static {
route 0.0.0.0/0 next-hop 10.92.77.254;
}
user@EX9200-A# show protocols
ospf {
area 0.0.0.0 {
interface lo0.0 {
passive;
}
interface ae0.0;
}
}
iccp {
local-ip-addr 172.16.32.5;
peer 172.16.32.6 {
session-establishment-hold-time 50;
redundancy-group-id-list 1;
backup-liveness-detection {
backup-peer-ip 10.92.76.4;
}
liveness-detection {
minimum-interval 2000;
multiplier 4;
}
}
}
lldp {
interface all;
}
user@EX9200-A# show chassis
aggregated-devices {
ethernet {
device-count 20;
}
}
user@EX9200-A# show groups MC_Config_Global
when {
peers [ EX9200-A EX9200-B ];
}
interfaces {
xe-0/3/6 {
ether-options {
802.3ad ae0;
}
}
xe-1/3/6 {
ether-options {
802.3ad ae0;
}
}
ae0 {
description "ICCP Layer 3 Link with 2 members,xe-0/3/6,xe-1/3/6";
aggregated-ether-options {
lacp {
active;
periodic fast;
system-id 00:01:02:03:04:05;
admin-key 0;
}
}
}
xe-0/3/7 {
ether-options {
802.3ad ae1;
}
}
xe-1/3/7 {
ether-options {
802.3ad ae1;
}
}
ae1 {
description "ICL Layer 2 link with 2 members,xe-0/3/7,1/3/7";
vlan-tagging;
aggregated-ether-options {
lacp {
active;
periodic fast;
system-id 00:01:02:03:04:06;
admin-key 1;
}
}
unit 0 {
family ethernet-switching {
interface-mode trunk;
vlan {
members all;
}
}
}
}
xe-0/0/1 {
ether-options {
802.3ad ae2;
}
}
xe-1/0/1 {
ether-options {
802.3ad ae2;
}
}
ae2 {
description "MC-LAG interface with members xe-0/0/1,xe-1/0/1";
aggregated-ether-options {
lacp {
active;
periodic fast;
system-id 00:01:02:03:04:07;
admin-key 2;
}
mc-ae {
mc-ae-id 2;
redundancy-group 1;
mode active-active;
init-delay-time 520;
events {
iccp-peer-down {
prefer-status-control-active;
}
}
}
}
unit 0 {
family ethernet-switching {
interface-mode trunk;
vlan {
members all;
}
}
}
}
xe-0/0/2 {
ether-options {
802.3ad ae3;
}
}
ae3 {
description “MC-LAG interface with members xe-0/0/2 on both switches”
aggregated-ether-options {
lacp {
active;
periodic fast;
system-id 00:01:02:03:04:08;
admin-key 3;
}
mc-ae {
mc-ae-id 3;
redundancy-group 1;
mode active-active;
init-delay-time 520;
events {
iccp-peer-down {
prefer-status-control-active;
}
}
}
}
unit 0 {
family ethernet-switching {
interface-mode trunk;
vlan {
members all;
}
}
}
}
}
multi-chassis {
mc-lag {
consistency-check;
}
}
protocols {
rstp {
bridge-priority 0;
system-id 00:01:02:03:04:09;
interface ae2;
interface ae3;
}
}
switch-options {
service-id 1;
}
vlans {
v100 {
vlan-id 100;
l3-interface irb.100;
}
}
user@EX9200-A# show groups MC_Config_Local
interfaces {
ae0 {
unit 0 {
family inet {
address 172.16.32.9/30;
}
}
}
ae2 {
aggregated-ether-options {
mc-ae {
chassis-id 0;
status-control active;
}
}
}
ae3 {
aggregated-ether-options {
mc-ae {
chassis-id 0;
status-control active;
}
}
}
}
user@EX9200-A# show groups MC_Config_Remote
interfaces {
ae0 {
unit 0 {
family inet {
address 172.16.32.10/30;
}
}
}
ae2 {
aggregated-ether-options {
mc-ae {
chassis-id 1;
status-control standby;
}
}
}
ae3 {
aggregated-ether-options {
mc-ae {
chassis-id 1;
status-control standby;
}
}
}
}
user@EX9200-A# show apply-groups apply-groups [ MC_Config_Global MC_Config_Local MC_Config_Remote ];
Display the results of the configuration on EX9200-B before you commit the configuration.
user@EX9200-B# show system services
netconf {
ssh;
}
user@EX9200-B# show system commit
peers-synchronize;
peers {
EX9200-A {
user MCLAG_Admin;
authentication "$ABC123”;
}
}
user@EX9200-B# show interfaces
ae2 {
unit 0 {
multi-chassis-protection 172.16.32.5 {
interface ae1;
}
}
}
ae3 {
unit 0 {
multi-chassis-protection 172.16.32.5 {
interface ae1;
}
}
}
irb {
unit 100 {
family inet {
address 192.168.100.3/24 {
arp 192.168.100.2 l2-interface ae1.0 mac 28:8a:1c:e3:f7:f0;
vrrp-group 1 {
virtual-address 192.168.100.1;
priority 100;
accept-data;
}
}
}
}
}
lo0 {
unit 0 {
family inet {
address 172.16.32.6/32;
}
}
}
user@EX9200-B# show routing-options
static {
route 0.0.0.0/0 next-hop 10.92.77.254;
}
user@EX9200-B# show protocols
ospf {
area 0.0.0.0 {
interface lo0.0 {
passive;
}
interface ae0.0;
}
}
iccp {
local-ip-addr 172.16.32.6;
peer 172.16.32.5 {
session-establishment-hold-time 50;
redundancy-group-id-list 1;
backup-liveness-detection {
backup-peer-ip 10.92.76.2;
}
liveness-detection {
minimum-interval 2000;
multiplier 4;
}
}
}
lldp {
interface all;
}
user@EX9200-B# show chassis
aggregated-devices {
ethernet {
device-count 20;
}
}
user@EX9200-B# show apply-groups [ MC_Config_Global MC_Config_Local MC_Config_Remote ];
Verification
- Verifying ICCP on MC-LAG
- Verifying LACP on MC-LAG
- Verifying Aggregated Ethernet Interfaces in MC-LAG
- Verifying MAC Learning on MC-LAG
- Verifying VRRP in MC-LAG
- Verifying OSPF on MC-LAG
- Verifying that Configuration Consistency Check Passed
- Verifying the Configuration Consistency Check Status for the Global Configuration
- Verifying the Configuration Consistency Check Status for the Interchassis Control Link
- Verifying the Configuration Consistency Check Status for the MC-LAG Interfaces
- Verifying the Configuration Consistency Check Status for the VLAN Configuration
- Verifying the Configuration Consistency Check Status for VRRP
Verifying ICCP on MC-LAG
Purpose
Verify that ICCP is running on each device in the MC-LAG.
Action
-
Verify that ICCP is running on EX9200-A.
user@EX92000-A> show iccp Redundancy Group Information for peer 172.16.32.6 TCP Connection : Established Liveliness Detection : Up Backup liveness peer status: Up Redundancy Group ID Status 1 Up Client Application: lacpd Redundancy Group IDs Joined: 1 Client Application: l2ald_iccpd_client Redundancy Group IDs Joined: 1 Client Application: mclag_cfgchkd Redundancy Group IDs Joined: 1 -
Verify that ICCP is running on EX9200-B.
user@EX9200-B> show iccp Redundancy Group Information for peer 172.16.32.5 TCP Connection : Established Liveliness Detection : Up Backup liveness peer status: Up Redundancy Group ID Status 1 Up Client Application: lacpd Redundancy Group IDs Joined: 1 Client Application: l2ald_iccpd_client Redundancy Group IDs Joined: 1 Client Application: mclag_cfgchkd Redundancy Group IDs Joined: 1
Meaning
This output shows that the TCP connection between the peers hosting the MC-LAG is up, liveness detection is up, Backup liveness peer status is up, and LACPD, MCLAG_CFGCHKD,and L2ALD _ICCP_CLIENT client applications are running.
Verifying LACP on MC-LAG
Purpose
Verify that LACP is working properly on each device in the MC-LAG.
Action
-
Verify that the LACP interfaces are up and running on EX9200-A.
user@EX9200-A> show lacp interfaces Aggregated interface: ae0 LACP state: Role Exp Def Dist Col Syn Aggr Timeout Activity xe-0/3/6 Actor No No Yes Yes Yes Yes Fast Active xe-0/3/6 Partner No No Yes Yes Yes Yes Fast Active xe-1/3/6 Actor No No Yes Yes Yes Yes Fast Active xe-1/3/6 Partner No No Yes Yes Yes Yes Fast Active LACP protocol: Receive State Transmit State Mux State xe-0/3/6 Current Fast periodic Collecting distributing xe-1/3/6 Current Fast periodic Collecting distributing Aggregated interface: ae1 LACP state: Role Exp Def Dist Col Syn Aggr Timeout Activity xe-0/3/7 Actor No No Yes Yes Yes Yes Fast Active xe-0/3/7 Partner No No Yes Yes Yes Yes Fast Active xe-1/3/7 Actor No No Yes Yes Yes Yes Fast Active xe-1/3/7 Partner No No Yes Yes Yes Yes Fast Active LACP protocol: Receive State Transmit State Mux State xe-0/3/7 Current Fast periodic Collecting distributing xe-1/3/7 Current Fast periodic Collecting distributing Aggregated interface: ae2 LACP state: Role Exp Def Dist Col Syn Aggr Timeout Activity xe-0/0/1 Actor No Yes No No No Yes Fast Active xe-0/0/1 Partner No Yes No No No Yes Fast Passive LACP protocol: Receive State Transmit State Mux State xe-0/0/1 Current Fast periodic Collecting distributing xe-1/0/1 Port disabled Fast periodic Collecting distributing Aggregated interface: ae3 LACP state: Role Exp Def Dist Col Syn Aggr Timeout Activity xe-0/0/2 Actor No Yes No No No Yes Fast Active xe-0/0/2 Partner No Yes No No No Yes Fast Passive LACP protocol: Receive State Transmit State Mux State xe-0/0/2 Current Fast periodic Collecting distributing -
Verify that the LACP interfaces are up and running on EX9200-B.
user@EX9200-B> show lacp interfaces Aggregated interface: ae0 LACP state: Role Exp Def Dist Col Syn Aggr Timeout Activity xe-0/3/6 Actor No No Yes Yes Yes Yes Fast Active xe-0/3/6 Partner No No Yes Yes Yes Yes Fast Active xe-1/3/6 Actor No No Yes Yes Yes Yes Fast Active xe-1/3/6 Partner No No Yes Yes Yes Yes Fast Active LACP protocol: Receive State Transmit State Mux State xe-0/3/6 Current Fast periodic Collecting distributing xe-1/3/6 Current Fast periodic Collecting distributing Aggregated interface: ae1 LACP state: Role Exp Def Dist Col Syn Aggr Timeout Activity xe-0/3/7 Actor No No Yes Yes Yes Yes Fast Active xe-0/3/7 Partner No No Yes Yes Yes Yes Fast Active xe-1/3/7 Actor No No Yes Yes Yes Yes Fast Active xe-1/3/7 Partner No No Yes Yes Yes Yes Fast Active LACP protocol: Receive State Transmit State Mux State xe-0/3/7 Current Fast periodic Collecting distributing xe-1/3/7 Current Fast periodic Collecting distributing Aggregated interface: ae2 LACP state: Role Exp Def Dist Col Syn Aggr Timeout Activity xe-1/0/1 Actor No Yes No No No Yes Fast Active xe-1/0/1 Partner No Yes No No No Yes Fast Passive LACP protocol: Receive State Transmit State Mux State xe-0/0/1 Current Fast periodic Collecting distributing xe-1/0/1 Current Fast periodic Collecting distributing Aggregated interface: ae3 LACP state: Role Exp Def Dist Col Syn Aggr Timeout Activity xe-0/0/2 Actor No Yes No No No Yes Fast Active xe-0/0/2 Partner No Yes No No No Yes Fast Passive LACP protocol: Receive State Transmit State Mux State xe-0/0/2 Current Fast periodic Collecting distributing
Meaning
This output means that both devices and all related interfaces are properly participating in LACP negotiations.
Verifying Aggregated Ethernet Interfaces in MC-LAG
Purpose
Verify that all of the ae interfaces are configured properly in the MC–LAG.
Action
-
Verify the ae interfaces on EX9200-A.
user@EX9200-A> show interfaces mc-ae Member Link : ae2 Current State Machine's State: mcae active state Configuration Error Status : No Error Local Status : active Local State : up Peer Status : active Peer State : up Logical Interface : ae2.0 Topology Type : bridge Local State : up Peer State : up Peer Ip/MCP/State : 172.16.32.6 ae1.0 up Member Link : ae3 Current State Machine's State: mcae active state Configuration Error Status : No Error Local Status : active Local State : up Peer Status : active Peer State : up Logical Interface : ae3.0 Topology Type : bridge Local State : up Peer State : up Peer Ip/MCP/State : 172.16.32.6 ae1.0 up -
Verify the ae interfaces on EX9200-B.
user@EX9200-B> show interface mc-ae Member Link : ae2 Current State Machine's State: mcae active state Configuration Error Status : No Error Local Status : active Local State : up Peer Status : active Peer State : up Logical Interface : ae2.0 Topology Type : bridge Local State : up Peer State : up Peer Ip/MCP/State : 172.16.32.5 ae1.0 up Member Link : ae3 Current State Machine's State: mcae active state Configuration Error Status : No Error Local Status : active Local State : down Peer Status : active Peer State : down Logical Interface : ae3.0 Topology Type : bridge Local State : up Peer State : up Peer Ip/MCP/State : 172.16.32.5 ae1.0 up
Meaning
This output means that the mc-ae interfaces on each device are up and active.
Verifying MAC Learning on MC-LAG
Purpose
Verify that MAC learning between devices is happening in the MC-LAG.
Action
-
Show the Ethernet switching table on EX9200-A.
user@EX9200-A> show ethernet-switching table MAC flags (S - static MAC, D - dynamic MAC, L - locally learned, P - Persistent static, C - Control MAC SE - statistics enabled, NM - non configured MAC, R - remote PE MAC, O - ovsdb MAC) Ethernet switching table : 2 entries, 2 learned Routing instance : EVPN-2 Vlan MAC MAC Age Logical NH RTR name address flags interface Index ID v100 10:0e:7e:b1:01:80 DC - pip-7.040010000000 1048580 1048580 v100 4c:96:14:e7:fd:81 DRC - ae10.200 0 0 -
Show the Ethernet switching table on EX9200-B.
user@EX9200-B> show ethernet-switching table MAC flags (S - static MAC, D - dynamic MAC, L - locally learned, P - Persistent static, C - Control MAC SE - statistics enabled, NM - non configured MAC, R - remote PE MAC, O - ovsdb MAC) Ethernet switching table : 2 entries, 2 learned Routing instance : EVPN-2 Vlan name MAC address MAC flags Age Logical interface NH Index RTR ID v100 10:0e:7e:b1:01:80 DC - pip-7.060010000000 1048581 1048580 v100 4c:96:14:e7:fd:81 D - ae10.200 0 0
Meaning
This output means that the MAC addresses are properly learned within the shared VLANs defined in the MC-LAG.
Verifying VRRP in MC-LAG
Purpose
Verify that VRRP is up and active between the devices in the MC-LAG.
Action
-
Confirm that VRRP is up and active on EX9200-A.
user@EX9200-A> show vrrp Interface State Group VR state VR Mode Timer Type Address irb.100 up 1 master Active A 0.789 lcl 192.168.100.2 vip 192.168.100.1In this example, Switch A is the primary VRRP member.
-
Confirm that VRRP is up and active on EX9200-B.
user@EX9200-B> show vrrp Interface State Group VR state VR Mode Timer Type Address irb.100 up 1 backup Active D 2.887 lcl 192.168.100.3 vip 192.168.100.1 mas 192.168.100.2In this example, Switch B is the backup VRRP member.
Meaning
This output means that VRRP is up and running properly.
Verifying OSPF on MC-LAG
Purpose
Verify that OSPF is properly up and running with MC-LAG.
Action
-
Show the OSPF neighbors on EX9200-A.
user@EX9200-A> show ospf neighbor Address Interface State ID Pri Dead 172.16.32.10 ae0.0 Full 172.16.32.6 128 33
-
Show the OSPF routing table on EX9200-A.
user@EX9200-A> show ospf route Topology default Route Table: Prefix Path Route NH Metric NextHop Nexthop Type Type Type Interface Address/LSP 172.16.32.6 Intra Router IP 1 ae0.0 172.16.32.10 172.16.32.5/32 Intra Network IP 0 lo0.0 172.16.32.6/32 Intra Network IP 1 ae0.0 172.16.32.10 172.16.32.8/30 Intra Network IP 1 ae0.0 -
Show the OSPF neighbors on EX9200-B.
user@EX9200-B> show ospf neighbor Address Interface State ID Pri Dead 172.16.32.9 ae0.0 Full 172.16.32.5 128 31
-
Show the OSPF routing table on EX9200-B.
user@EX9200-B> show ospf route Topology default Route Table: Prefix Path Route NH Metric NextHop Nexthop Type Type Type Interface Address/LSP 172.16.32.5 Intra Router IP 1 ae0.0 172.16.32.9 172.16.32.5/32 Intra Network IP 1 ae0.0 172.16.32.9 172.16.32.6/32 Intra Network IP 0 lo0.0 172.16.32.8/30 Intra Network IP 1 ae0.0
Meaning
The output shows that the neighboring devices are fully adjacent.
Verifying that Configuration Consistency Check Passed
Purpose
View the list of committed MC-LAG parameters that are checked for inconsistencies, the consistency requirement (identical or unique), the enforcement level (mandatory or desired), and the result of the configuration consistency check. The results are either pass or fail.
Action
-
Show the list of committed MC-LAG parameters that passed or failed configuration consistency check on EX9200-A.
user@EX9200-A> show multi-chassis mc-lag configuration-consistency Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- ICL interface Mandatory ae1 ae1 PASS rstp-bridge-priority Desirable 0 0 PASS service-id Mandatory 1 1 PASS session-establishment-hold-time Mandatory 300 300 PASS local-ip-addr Mandatory 172.16.32.5 172.16.32.6 PASS backup-liveness-detection Mandatory 10.92.76.4 10.92.76.2 PASS iccp/bfd multiplier Mandatory 4 4 PASS bfd minimum-interval Mandatory 2000 2000 PASS session-establishment-hold-time Mandatory 50 50 PASS Local Physical Interface:ae2 Peer Physical Interface :ae2 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- lacp admin-key Mandatory 2 2 PASS lacp system-id Mandatory 00:01:02:03:04:07 00:01:02:03:04:07 PASS lacp periodic Mandatory 0 0 PASS lacp mode Mandatory 0 0 PASS prefer-status-control-active Desirable TRUE -- PASS mcae status-control Mandatory standby active PASS mcae deployment mode Mandatory active-active active-active PASS mcae chassis-id Mandatory 0 1 PASS mcae redundancy-group Mandatory 1 1 PASS Local Logical Interface:ae2.0 Peer Logical Interface :ae2.0 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- vlan membership Mandatory 100 100 PASS interface-mode Mandatory trunk trunk PASS Local Physical Interface:ae3 Peer Physical Interface :ae3 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- lacp admin-key Mandatory 3 3 PASS lacp system-id Mandatory 00:01:02:03:04:08 00:01:02:03:04:08 PASS lacp periodic Mandatory 0 0 PASS lacp mode Mandatory 0 0 PASS prefer-status-control-active Desirable TRUE -- PASS mcae status-control Mandatory standby active PASS mcae deployment mode Mandatory active-active active-active PASS mcae chassis-id Mandatory 0 1 PASS mcae redundancy-group Mandatory 1 1 PASS Local Logical Interface:ae3.0 Peer Logical Interface :ae3.0 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- vlan membership Mandatory 100 100 PASS interface-mode Mandatory trunk trunk PASS Local VLAN:v100 Peer VLAN :v100 Local IRB:irb.100 Peer IRB :irb.100 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- vrrp-group id Mandatory 1 1 PASS ipv4 address Mandatory 192.168.100.2/24 192.168.100.3/24 PASS -
Show the list of committed MC-LAG parameters that passed or failed configuration consistency check on EX9200-B.
user@EX9200-B> show multi-chassis mc-lag configuration-consistency Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- ICL interface Mandatory ae1 ae1 PASS rstp-bridge-priority Desirable 0 0 PASS service-id Mandatory 1 1 PASS session-establishment-hold-time Mandatory 300 300 PASS local-ip-addr Mandatory 172.16.32.6 172.16.32.5 PASS backup-liveness-detection Mandatory 10.92.76.2 10.92.76.4 PASS iccp/bfd multiplier Mandatory 4 4 PASS bfd minimum-interval Mandatory 2000 2000 PASS session-establishment-hold-time Mandatory 50 50 PASS Local Physical Interface:ae2 Peer Physical Interface :ae2 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- lacp admin-key Mandatory 2 2 PASS lacp system-id Mandatory 00:01:02:03:04:07 00:01:02:03:04:07 PASS lacp periodic Mandatory 0 0 PASS lacp mode Mandatory 0 0 PASS mcae status-control Mandatory active standby PASS mcae deployment mode Mandatory active-active active-active PASS mcae chassis-id Mandatory 1 0 PASS mcae redundancy-group Mandatory 1 1 PASS prefer-status-control-active Desirable -- TRUE PASS Local Logical Interface:ae2.0 Peer Logical Interface :ae2.0 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- vlan membership Mandatory 100 100 PASS interface-mode Mandatory trunk trunk PASS Local Physical Interface:ae3 Peer Physical Interface :ae3 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- lacp admin-key Mandatory 3 3 PASS lacp system-id Mandatory 00:01:02:03:04:08 00:01:02:03:04:08 PASS lacp periodic Mandatory 0 0 PASS lacp mode Mandatory 0 0 PASS mcae status-control Mandatory active standby PASS mcae deployment mode Mandatory active-active active-active PASS mcae chassis-id Mandatory 1 0 PASS mcae redundancy-group Mandatory 1 1 PASS prefer-status-control-active Desirable -- TRUE PASS Local Logical Interface:ae3.0 Peer Logical Interface :ae3.0 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- vlan membership Mandatory 100 100 PASS interface-mode Mandatory trunk trunk PASS Local VLAN:v100 Peer VLAN :v100 Local IRB:irb.100 Peer IRB :irb.100 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- vrrp-group id Mandatory 1 1 PASS ipv4 address Mandatory 192.168.100.3/24 192.168.100.2/24 PASS
Meaning
The output shows that all configured and committed MC-LAG parameters have passed configuration consistency check.
Verifying the Configuration Consistency Check Status for the Global Configuration
Purpose
View configuration consistency check status for all committed global configuration related to MC-LAG functionality, the consistency requirement (identical or unique), the enforcement level (mandatory or desired), and the result of the configuration consistency check. The results are either pass or fail.
This command shows only a subset of what is shown in the show multi-chassis mc-lag configuration-consistency command.
The following parameters related to the global configuration are checked
for consistency.
-
ICL interface
-
RSTP bridge priority
-
service ID
-
session establishment hold time
-
local IP address of the ICCP interface
-
backup liveness detection peer IP address
-
ICCP/BFD multiplier
Parameters specific to the ICL, MC-LAG interfaces, and VLAN and VRRP configurations are shown later in this document.
Action
-
Show the list of committed global configuration parameters that passed or failed configuration consistency check on EX9200-A.
The output below shows all of the parameters that directly affect the MC-LAG configuration.
user@EX9200-A> show multi-chassis mc-lag configuration-consistency global-config Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- ICL interface Mandatory ae1 ae1 PASS rstp-bridge-priority Desirable 0 0 PASS service-id Mandatory 1 1 PASS session-establishment-hold-time Mandatory 300 300 PASS local-ip-addr Mandatory 172.16.32.5 172.16.32.6 PASS backup-liveness-detection Mandatory 10.92.76.4 10.92.76.2 PASS iccp/bfd multiplier Mandatory 4 4 PASS bfd minimum-interval Mandatory 2000 2000 PASS session-establishment-hold-time Mandatory 50 50 PASS
-
Show the list of committed global configuration parameters that passed or failed configuration consistency check on EX9200-B
user@EX9200-B> show multi-chassis mc-lag configuration-consistency global-config Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- ICL interface Mandatory ae1 ae1 PASS rstp-bridge-priority Desirable 0 0 PASS service-id Mandatory 1 1 PASS session-establishment-hold-time Mandatory 300 300 PASS local-ip-addr Mandatory 172.16.32.6 172.16.32.5 PASS backup-liveness-detection Mandatory 10.92.76.2 10.92.76.4 PASS iccp/bfd multiplier Mandatory 4 4 PASS bfd minimum-interval Mandatory 2000 2000 PASS session-establishment-hold-time Mandatory 50 50 PASS
Meaning
The output shows that the committed global configuration related to MC-LAG have passed configuration consistency check.
Verifying the Configuration Consistency Check Status for the Interchassis Control Link
Purpose
View configuration consistency check status for parameters related to the ICL, the consistency requirement (identical or unique), the enforcement level (mandatory or desired), and the result of the configuration consistency check. The results are either pass or fail. Some example of parameters related to the ICL interface are the interface mode and which VLAN the interface belongs to.
This command shows only a subset of what is shown in the show multi-chassis mc-lag configuration-consistency command.
The following parameters related to the ICL configuration are checked
for consistency check:
-
VLAN membership
-
interface mode
Action
-
Show the list of committed ICL configuration parameters that passed or failed configuration consistency check on EX9200-A
user@EX9200-A> show multi-chassis mc-lag configuration-consistency icl-config Local Physical Interface:ae1 Peer Physical Interface :ae1 Local Logical Interface:ae1.0 Peer Logical Interface :ae1.0 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- vlan membership Mandatory 100 100 PASS interface-mode Mandatory trunk trunk PASS
-
Show the list of committed ICL configuration parameters that passed or failed configuration consistency check on EX9200-B
user@EX9200-B> show multi-chassis mc-lag configuration-consistency icl-config Local Physical Interface:ae1 Peer Physical Interface :ae1 Local Logical Interface:ae1.0 Peer Logical Interface :ae1.0 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- vlan membership Mandatory 100 100 PASS interface-mode Mandatory trunk trunk PASS
Meaning
The output shows that the committed MC-LAG parameters related to the ICL have passed configuration consistency check.
Verifying the Configuration Consistency Check Status for the MC-LAG Interfaces
Purpose
View configuration consistency check status for committed parameters related to the multichassis aggregated Ethernet interfaces, the consistency requirement (identical or unique), the enforcement level (mandatory or desired), and the result of the configuration consistency check. The results are either pass or fail.
This command shows only a subset of what is shown in the show multi-chassis mc-lag configuration-consistency command.
The following parameters related to the MC-AE interfaces are checked
for consistency:
-
LACP administrative key
-
LACP system ID
-
LACP periodic interval
-
prefer status control setting
-
status control setting
-
mode
-
chassis ID
-
redundancy group ID
-
VLAN membership of the ICL
-
interface mode of the ICL
Action
-
Show the list of committed MC-LAG interface configuration parameters that passed or failed configuration consistency check on EX9200-A.
user@EX9200-A> show multi-chassis mc-lag configuration-consistency mcae-config Local Physical Interface:ae2 Peer Physical Interface :ae2 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- lacp admin-key Mandatory 2 2 PASS lacp system-id Mandatory 00:01:02:03:04:07 00:01:02:03:04:07 PASS lacp periodic Mandatory 0 0 PASS lacp mode Mandatory 0 0 PASS prefer-status-control-active Desirable TRUE -- PASS mcae status-control Mandatory standby active PASS mcae deployment mode Mandatory active-active active-active PASS mcae chassis-id Mandatory 0 1 PASS mcae redundancy-group Mandatory 1 1 PASS Local Logical Interface:ae2.0 Peer Logical Interface :ae2.0 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- vlan membership Mandatory 100 100 PASS interface-mode Mandatory trunk trunk PASS Local Physical Interface:ae3 Peer Physical Interface :ae3 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- lacp admin-key Mandatory 3 3 PASS lacp system-id Mandatory 00:01:02:03:04:05 00:01:02:03:04:05 PASS lacp periodic Mandatory 0 0 PASS lacp mode Mandatory 0 0 PASS prefer-status-control-active Desirable TRUE -- PASS mcae status-control Mandatory standby active PASS mcae deployment mode Mandatory active-active active-active PASS mcae chassis-id Mandatory 0 1 PASS mcae redundancy-group Mandatory 1 1 PASS Local Logical Interface:ae3.0 Peer Logical Interface :ae3.0 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- vlan membership Mandatory 100 100 PASS interface-mode Mandatory trunk trunk PASS
-
Show the list of committed MC-LAG interface configuration parameters that passed or failed configuration consistency check on EX9200-B.
user@EX9200-B> show multi-chassis mc-lag configuration-consistency mcae-config Local Physical Interface:ae2 Peer Physical Interface :ae2 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- lacp admin-key Mandatory 2 2 PASS lacp system-id Mandatory 00:01:02:03:04:05 00:01:02:03:04:05 PASS lacp periodic Mandatory 0 0 PASS lacp mode Mandatory 0 0 PASS mcae status-control Mandatory active standby PASS mcae deployment mode Mandatory active-active active-active PASS mcae chassis-id Mandatory 1 0 PASS mcae redundancy-group Mandatory 1 1 PASS prefer-status-control-active Desirable -- TRUE PASS Local Logical Interface:ae2.0 Peer Logical Interface :ae2.0 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- vlan membership Mandatory 100 100 PASS interface-mode Mandatory trunk trunk PASS Local Physical Interface:ae3 Peer Physical Interface :ae3 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- lacp admin-key Mandatory 3 3 PASS lacp system-id Mandatory 00:01:02:03:04:08 00:01:02:03:04:08 PASS lacp periodic Mandatory 0 0 PASS lacp mode Mandatory 0 0 PASS mcae status-control Mandatory active standby PASS mcae deployment mode Mandatory active-active active-active PASS mcae chassis-id Mandatory 1 0 PASS mcae redundancy-group Mandatory 1 1 PASS prefer-status-control-active Desirable -- TRUE PASS Local Logical Interface:ae3.0 Peer Logical Interface :ae3.0 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- vlan membership Mandatory 100 100 PASS interface-mode Mandatory trunk trunk PASS
Meaning
The output shows that the committed MC-LAG parameters related to the MC-AE interfaces have passed configuration consistency check.
Verifying the Configuration Consistency Check Status for the VLAN Configuration
Purpose
View configuration consistency check status for committed parameters related to MC-LAG VLAN configuration, the consistency requirement (identical or unique), the enforcement level (mandatory or desired), and the result of the configuration consistency check. The results are either pass or fail.
This command shows only a subset of what is shown in the show multi-chassis mc-lag configuration-consistency command.
The following parameters related to the VLAN and IRB configuration
are checked for consistency:
-
VRRP group ID
-
IP address of IRB interface
Action
-
Show the list of committed VLAN configuration parameters that passed or failed configuration consistency check on EX9200-A.
user@EX9200-A> show multi-chassis mc-lag configuration-consistency vlan-config Local VLAN:v100 Peer VLAN :v100 Local IRB:irb.100 Peer IRB :irb.100 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- vrrp-group id Mandatory 1 1 PASS ipv4 address Mandatory 192.168.100.2/24 192.168.100.3/24 PASS
-
Show the list of committed VLAN configuration parameters that passed or failed configuration consistency check on EX9200-B.
user@EX9200-B> show multi-chassis mc-lag configuration-consistency vlan-config Peer VLAN :v100 Local IRB:irb.100 Peer IRB :irb.100 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- vrrp-group id Mandatory 1 1 PASS ipv4 address Mandatory 192.168.100.3/24 192.168.100.2/24 PASS
Meaning
The output shows that the committed MC-LAG parameters related to the VLAN and IRB configurations have passed configuration consistency check.
Verifying the Configuration Consistency Check Status for VRRP
Purpose
View configuration consistency check status for committed parameters related to VRRP configuration, the consistency requirement (identical or unique), the enforcement level (mandatory or desired), and the result of the configuration consistency check. The results are either pass or fail.
This command shows only a subset of what is shown in the show multi-chassis mc-lag configuration-consistency command.
The following parameters related to the VRRP configuration are checked
for consistency: VRRP group virtual IP address and VRRP group priority
value.
Action
-
Show the list of committed VRRP configuration parameters that passed or failed configuration consistency check on EX9200-A.
user@EX9200-A> show multi-chassis mc-lag configuration-consistency vrrp-config Local VRRP Group:1 Peer VRRP Group :1 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- vrrp-group virtual-address Mandatory 192.168.100.001 192.168.100.001 PASS vrrp-group priority Mandatory 150 100 PASS
-
Show the list of committed VRRP configuration parameters that passed or failed configuration consistency check on EX9200-B.
user@EX9200-B> show multi-chassis mc-lag configuration-consistency vrrp-config Local VRRP Group:1 Peer VRRP Group :1 Configuration Item Enforcement Level Local Value Peer Value Result ------------------ ----------------- ----------- ---------- ------- vrrp-group virtual-address Mandatory 192.168.100.001 192.168.100.001 PASS vrrp-group priority Mandatory 100 150 PASS
Meaning
The output shows that the committed MC-LAG parameters related to VRRP configuration have passed configuration consistency check.
Example: Configuring CoS for FCoE Transit Switch Traffic Across an MC-LAG
Multichassis link aggregation groups (MC-LAGs) provide redundancy and load balancing between two switches, multihoming support for client devices such as servers, and a loop-free Layer 2 network without running Spanning Tree Protocol (STP).
This example uses Junos OS without support for the Enhanced Layer 2 Software (ELS) configuration style. If your switch runs software that does support ELS, see Example: Configuring CoS Using ELS for FCoE Transit Switch Traffic Across an MC-LAG. For ELS details, see Using the Enhanced Layer 2 Software CLI.
You can use an MC-LAG to provide a redundant aggregation layer for Fibre Channel over Ethernet (FCoE) traffic in an inverted-U topology. To support lossless transport of FCoE traffic across an MC-LAG, you must configure the appropriate class of service (CoS) on both of the switches with MC-LAG port members. The CoS configuration must be the same on both of the MC-LAG switches because an MC-LAG does not carry forwarding class and IEEE 802.1p priority information.
This example describes how to configure CoS to provide lossless transport for FCoE traffic across an MC-LAG that connects two switches. It also describes how to configure CoS on the FCoE transit switches that connect FCoE hosts to the two switches that form the MC-LAG.
This example does not describe how to configure the MC-LAG itself. However, this example includes a subset of MC-LAG configuration that only shows how to configure interface membership in the MC-LAG.
Ports that are part of an FCoE-FC gateway configuration (a virtual FCoE-FC gateway fabric) do not support MC-LAGs. Ports that are members of an MC-LAG act as FCoE pass-through transit switch ports.
Requirements
This example uses the following hardware and software components:
Two Juniper Networks switches that form an MC-LAG for FCoE traffic.
Two Juniper Networks switches that provide FCoE server access in transit switch mode and that connect to the MC-LAG switches.
FCoE servers (or other FCoE hosts) connected to the transit switches.
Junos OS Release 12.2 or later for the QFX Series.
Overview
FCoE traffic requires lossless transport. This example shows you how to:
Configure CoS for FCoE traffic on the two switches that form the MC-LAG, including priority-based flow control (PFC) and enhanced transmission selection (ETS; hierarchical scheduling of resources for the FCoE forwarding class priority and for the forwarding class set priority group).
Note:Configuring or changing PFC on an interface blocks the entire port until the PFC change is completed. After a PFC change is completed, the port is unblocked and traffic resumes. Blocking the port stops ingress and egress traffic, and causes packet loss on all queues on the port until the port is unblocked.
Configure CoS for FCoE on the two FCoE transit switches that connect FCoE hosts to the MC-LAG switches and enable FIP snooping on the FCoE VLAN at the FCoE transit switch access ports.
Disable IGMP snooping on the FCoE VLAN.
Configure the appropriate port mode, MTU, and FCoE trusted or untrusted state for each interface to support lossless FCoE transport.
Topology
Switches that act as transit switches support MC-LAGs for FCoE traffic in an inverted-U network topology, as shown in Figure 6.
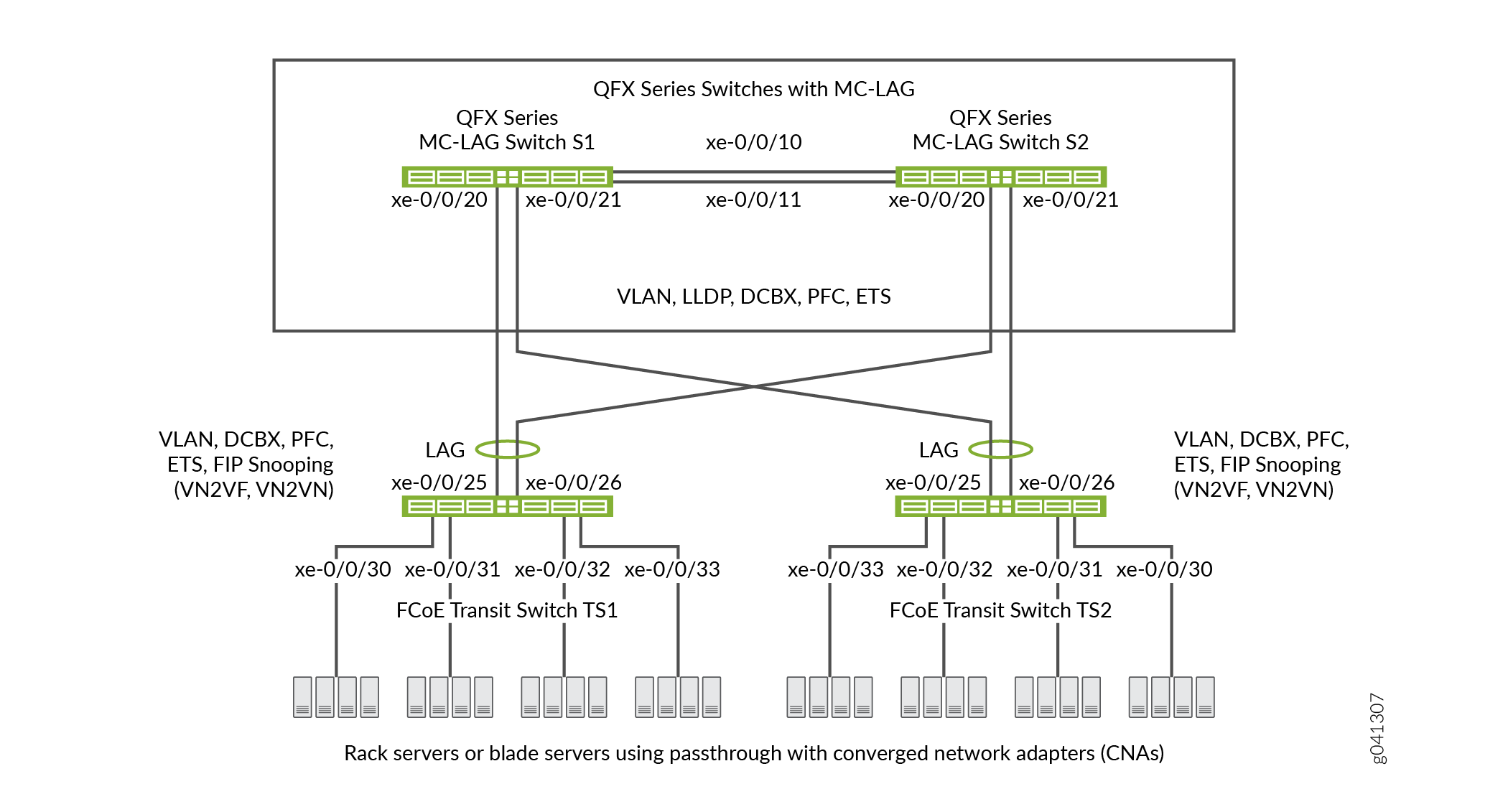
Table 3 shows the configuration components for this example.
Component |
Settings |
|---|---|
Hardware |
Four switches (two to form the MC-LAG as pass-through transit switches and two transit switches for FCoE access). |
Forwarding class (all switches) |
Default |
Classifier (forwarding class mapping of incoming traffic to IEEE priority) |
Default IEEE 802.1p trusted classifier on all FCoE interfaces. |
LAGs and MC-LAG |
S1—Ports xe-0/0/10 and x-0/0/11 are members of
LAG ae0, which connects Switch S1 to Switch S2.Ports
xe-0/0/20 and xe-0/0/21 are members of MC-LAG ae1.All
ports are configured in S2—Ports xe-0/0/10 and x-0/0/11 are members of LAG ae0,
which connects Switch S2 to Switch S1.Ports xe-0/0/20
and xe-0/0/21 are members of MC-LAG ae1.All ports
are configured in Note:
Ports xe-0/0/20 and xe-0/0/21 on Switches S1 and S2 are the members of the MC-LAG. TS1—Ports xe-0/0/25 and x-0/0/26 are members of LAG ae1,
configured in TS2—Ports xe-0/0/25 and x-0/0/26 are members of LAG ae1,
configured in |
FCoE queue scheduler (all switches) |
|
Forwarding class-to-scheduler mapping (all switches) |
Scheduler map |
Forwarding class set (FCoE priority group, all switches) |
Egress interfaces:
|
Traffic control profile (all switches) |
|
PFC congestion notification profile (all switches) |
Ingress interfaces:
|
FCoE VLAN name and tag ID |
Name— Include the FCoE VLAN on the interfaces that carry FCoE traffic on all four switches. Disable IGMP snooping on the interfaces that belong to the FCoE VLAN on all four switches. |
FIP snooping |
Enable FIP snooping on Transit Switches TS1 and TS2 on the FCoE VLAN. Configure the LAG interfaces that connect to the MC-LAG switches as FCoE trusted interfaces so that they do not perform FIP snooping. This example enables VN2VN_Port FIP snooping on the FCoE transit switch interfaces connected to the FCoE servers. The example is equally valid with VN2VF_Port FIP snooping enabled on the transit switch access ports. The method of FIP snooping you enable depends on your network configuration. |
This example uses the default IEEE 802.1p trusted BA classifier, which is automatically applied to trunk mode and tagged access mode ports if you do not apply an explicitly configured classifier.
To configure CoS for FCoE traffic across an MC-LAG:
Use the default FCoE forwarding class and forwarding-class-to-queue mapping (do not explicitly configure the FCoE forwarding class or output queue). The default FCoE forwarding class is
fcoe, and the default output queue is queue3.Note:You can include the no-loss packet drop attribute in the explicit forwarding class configuration to configure a lossless forwarding class.
Use the default trusted BA classifier, which maps incoming packets to forwarding classes by the IEEE 802.1p code point (CoS priority) of the packet. The trusted classifier is the default classifier for interfaces in trunk and tagged-access port modes. The default trusted classifier maps incoming packets with the IEEE 802.1p code point 3 (
011) to the FCoE forwarding class. If you choose to configure the BA classifier instead of using the default classifier, you must ensure that FCoE traffic is classified into forwarding classes in exactly the same way on both MC-LAG switches. Using the default classifier ensures consistent classifier configuration on the MC-LAG ports.Configure a congestion notification profile that enables PFC on the FCoE code point (code point
011in this example). The congestion notification profile configuration must be the same on both MC-LAG switches.Apply the congestion notification profile to the interfaces.
Configure enhanced transmission selection (ETS, also known as hierarchical scheduling) on the interfaces to provide the bandwidth required for lossless FCoE transport. Configuring ETS includes configuring bandwidth scheduling for the FCoE forwarding class, a forwarding class set (priority group) that includes the FCoE forwarding class, and a traffic control profile to assign bandwidth to the forwarding class set that includes FCoE traffic.
Apply the ETS scheduling to the interfaces.
Configure the port mode, MTU, and FCoE trusted or untrusted state for each interface to support lossless FCoE transport.
In addition, this example describes how to enable FIP snooping on the Transit Switch TS1 and TS2 ports that are connected to the FCoE servers and how to disable IGMP snooping on the FCoE VLAN. To provide secure access, FIP snooping must be enabled on the FCoE access ports.
This example focuses on the CoS configuration to support lossless FCoE transport across an MC-LAG. This example does not describe how to configure the properties of MC-LAGs and LAGs, although it does show you how to configure the port characteristics required to support lossless transport and how to assign interfaces to the MC-LAG and to the LAGs.
Before you configure CoS, configure:
The MC-LAGs that connect Switches S1 and S2 to Switches TS1 and TS2.
The LAGs that connect the Transit Switches TS1 and TS2 to MC-LAG Switches S1 and S2.
The LAG that connects Switch S1 to Switch S2.
Configuration
To configure CoS for lossless FCoE transport across an MC-LAG, perform these tasks:
- CLI Quick Configuration
- Configuring MC-LAG Switches S1 and S2
- Configuring FCoE Transit Switches TS1 and TS2
- Results
CLI Quick Configuration
To quickly configure CoS for lossless FCoE
transport across an MC-LAG, copy the following commands, paste them
in a text file, remove line breaks, change variables and details to
match your network configuration, and then copy and paste the commands
into the CLI for MC-LAG Switch S1 and MC-LAG Switch S2 at the [edit] hierarchy level. The configurations on Switches S1 and
S2 are identical because the CoS configuration must be identical,
and because this example uses the same ports on both switches.
Switch S1 and Switch S2
set class-of-service schedulers fcoe-sched priority low transmit-rate 3g set class-of-service schedulers fcoe-sched shaping-rate percent 100 set class-of-service scheduler-maps fcoe-map forwarding-class fcoe scheduler fcoe-sched set class-of-service forwarding-class-sets fcoe-pg class fcoe set class-of-service traffic-control-profiles fcoe-tcp scheduler-map fcoe-map guaranteed-rate 3g set class-of-service traffic-control-profiles fcoe-tcp shaping-rate percent 100 set class-of-service interfaces ae0 forwarding-class-set fcoe-pg output-traffic-control-profile fcoe-tcp set class-of-service interfaces ae1 forwarding-class-set fcoe-pg output-traffic-control-profile fcoe-tcp set class-of-service congestion-notification-profile fcoe-cnp input ieee-802.1 code-point 011 pfc set class-of-service interfaces ae0 congestion-notification-profile fcoe-cnp set class-of-service interfaces ae1 congestion-notification-profile fcoe-cnp set vlans fcoe_vlan vlan-id 100 set protocols igmp-snooping vlan fcoe_vlan disable set interfaces xe-0/0/10 ether-options 802.3ad ae0 set interfaces xe-0/0/11 ether-options 802.3ad ae0 set interfaces xe-0/0/20 ether-options 802.3ad ae1 set interfaces xe-0/0/21 ether-options 802.3ad ae1 set interfaces ae0 unit 0 family ethernet-switching port-mode trunk vlan members fcoe_vlan set interfaces ae1 unit 0 family ethernet-switching port-mode trunk vlan members fcoe_vlan set interfaces ae0 mtu 2180 set interfaces ae1 mtu 2180 set ethernet-switching-options secure-access-port interface ae0 fcoe-trusted set ethernet-switching-options secure-access-port interface ae1 fcoe-trusted
To quickly configure CoS for lossless FCoE transport across
an MC-LAG, copy the following commands, paste them in a text file,
remove line breaks, change variables and details to match your network
configuration, and then copy and paste the commands into the CLI for
Transit Switch TS1 and Transit Switch TS2 at the [edit] hierarchy level. The configurations on Switches TS1 and TS2 are
identical because the CoS configuration must be identical, and because
this example uses the same ports on both switches.
Switch TS1 and Switch TS2
set class-of-service schedulers fcoe-sched priority low transmit-rate 3g set class-of-service schedulers fcoe-sched shaping-rate percent 100 set class-of-service scheduler-maps fcoe-map forwarding-class fcoe scheduler fcoe-sched set class-of-service forwarding-class-sets fcoe-pg class fcoe set class-of-service traffic-control-profiles fcoe-tcp scheduler-map fcoe-map guaranteed-rate 3g set class-of-service traffic-control-profiles fcoe-tcp shaping-rate percent 100 set class-of-service interfaces ae1 forwarding-class-set fcoe-pg output-traffic-control-profile fcoe-tcp set class-of-service interfaces xe-0/0/30 forwarding-class-set fcoe-pg output-traffic-control-profile fcoe-tcp set class-of-service interfaces xe-0/0/31 forwarding-class-set fcoe-pg output-traffic-control-profile fcoe-tcp set class-of-service interfaces xe-0/0/32 forwarding-class-set fcoe-pg output-traffic-control-profile fcoe-tcp set class-of-service interfaces xe-0/0/33 forwarding-class-set fcoe-pg output-traffic-control-profile fcoe-tcp set class-of-service congestion-notification-profile fcoe-cnp input ieee-802.1 code-point 011 pfc set class-of-service interfaces ae1 congestion-notification-profile fcoe-cnp set class-of-service interfaces xe-0/0/30 congestion-notification-profile fcoe-cnp set class-of-service interfaces xe-0/0/31 congestion-notification-profile fcoe-cnp set class-of-service interfaces xe-0/0/32 congestion-notification-profile fcoe-cnp set class-of-service interfaces xe-0/0/33 congestion-notification-profile fcoe-cnp set vlans fcoe_vlan vlan-id 100 set protocols igmp-snooping vlan fcoe_vlan disable set interfaces xe-0/0/25 ether-options 802.3ad ae1 set interfaces xe-0/0/26 ether-options 802.3ad ae1 set interfaces ae1 unit 0 family ethernet-switching port-mode trunk vlan members fcoe_vlan set interfaces xe-0/0/30 unit 0 family ethernet-switching port-mode tagged-access vlan members fcoe_vlan set interfaces xe-0/0/31 unit 0 family ethernet-switching port-mode tagged-access vlan members fcoe_vlan set interfaces xe-0/0/32 unit 0 family ethernet-switching port-mode tagged-access vlan members fcoe_vlan set interfaces xe-0/0/33 unit 0 family ethernet-switching port-mode tagged-access vlan members fcoe_vlan set interfaces ae1 mtu 2180 set interfaces xe-0/0/30 mtu 2180 set interfaces xe-0/0/31 mtu 2180 set interfaces xe-0/0/32 mtu 2180 set interfaces xe-0/0/33 mtu 2180 set ethernet-switching-options secure-access-port interface ae1 fcoe-trusted set ethernet-switching-options secure-access-port vlan fcoe_vlan examine-fip examine-vn2v2 beacon-period 90000
Configuring MC-LAG Switches S1 and S2
Step-by-Step Procedure
To configure CoS resource scheduling (ETS), PFC, the
FCoE VLAN, and the LAG and MC-LAG interface membership and characteristics
to support lossless FCoE transport across an MC-LAG (this example
uses the default fcoe forwarding class and the default
classifier to map incoming FCoE traffic to the FCoE IEEE 802.1p code
point 011, so you do not configure them):
Configure output scheduling for the FCoE queue.
[edit class-of-service schedulers fcoe-sched] user@switch# set priority low transmit-rate 3g user@switch# set shaping-rate percent 100
Map the FCoE forwarding class to the FCoE scheduler (
fcoe-sched).[edit class-of-service] user@switch# set scheduler-maps fcoe-map forwarding-class fcoe scheduler fcoe-sched
Configure the forwarding class set (
fcoe-pg) for the FCoE traffic.[edit class-of-service] user@switch# set forwarding-class-sets fcoe-pg class fcoe
Define the traffic control profile (
fcoe-tcp) to use on the FCoE forwarding class set.[edit class-of-service traffic-control-profiles fcoe-tcp] user@switch# set scheduler-map fcoe-map guaranteed-rate 3g user@switch# set shaping-rate percent 100
Apply the FCoE forwarding class set and traffic control profile to the LAG and MC-LAG interfaces.
[edit class-of-service] user@switch# set interfaces ae0 forwarding-class-set fcoe-pg output-traffic-control-profile fcoe-tcp user@switch# set interfaces ae1 forwarding-class-set fcoe-pg output-traffic-control-profile fcoe-tcp
Enable PFC on the FCoE priority by creating a congestion notification profile (
fcoe-cnp) that applies FCoE to the IEEE 802.1 code point011.[edit class-of-service] user@switch# set congestion-notification-profile fcoe-cnp input ieee-802.1 code-point 011 pfc
Apply the PFC configuration to the LAG and MC-LAG interfaces.
[edit class-of-service] user@switch# set interfaces ae0 congestion-notification-profile fcoe-cnp user@switch# set interfaces ae1 congestion-notification-profile fcoe-cnp
Configure the VLAN for FCoE traffic (
fcoe_vlan).[edit vlans] user@switch# set fcoe_vlan vlan-id 100
Disable IGMP snooping on the FCoE VLAN.
[edit protocols] user@switch# set igmp-snooping vlan fcoe_vlan disable
Add the member interfaces to the LAG between the two MC-LAG switches.
[edit interfaces] user@switch# set xe-0/0/10 ether-options 802.3ad ae0 user@switch# set xe-0/0/11 ether-options 802.3ad ae0
Add the member interfaces to the MC-LAG.
[edit interfaces] user@switch# set xe-0/0/20 ether-options 802.3ad ae1 user@switch# set xe-0/0/21 ether-options 802.3ad ae1
Configure the port mode as
trunkand membership in the FCoE VLAN (fcoe_vlan)for the LAG (ae0) and for the MC-LAG (ae1).[edit interfaces] user@switch# set ae0 unit 0 family ethernet-switching port-mode trunk vlan members fcoe_vlan user@switch# set ae1 unit 0 family ethernet-switching port-mode trunk vlan members fcoe_vlan
Set the MTU to
2180for the LAG and MC-LAG interfaces.2180 bytes is the minimum size required to handle FCoE packets because of the payload and header sizes. You can configure the MTU to a higher number of bytes if desired, but not less than 2180 bytes.
[edit interfaces] user@switch# set ae0 mtu 2180 user@switch# set ae1 mtu 2180
Set the LAG and MC-LAG interfaces as FCoE trusted ports.
Ports that connect to other switches should be trusted and should not perform FIP snooping.
[edit ethernet-switching-options secure-access-port interface] user@switch# set ae0 fcoe-trusted user@switch# set ae1 fcoe-trusted
Configuring FCoE Transit Switches TS1 and TS2
Step-by-Step Procedure
The CoS configuration on FCoE Transit Switches TS1 and TS2 is similar to the CoS configuration on MC-LAG Switches S1 and S2. However, the port configurations differ, and you must enable FIP snooping on the Switch TS1 and Switch TS2 FCoE access ports.
To configure resource scheduling (ETS), PFC, the FCoE VLAN,
and the LAG interface membership and characteristics to support lossless
FCoE transport across the MC-LAG (this example uses the default fcoe forwarding class and the default classifier to map incoming
FCoE traffic to the FCoE IEEE 802.1p code point 011, so
you do not configure them):
Configure output scheduling for the FCoE queue.
[edit class-of-service schedulers fcoe-sched] user@switch# set priority low transmit-rate 3g user@switch# set shaping-rate percent 100
Map the FCoE forwarding class to the FCoE scheduler (
fcoe-sched).[edit class-of-service] user@switch# set scheduler-maps fcoe-map forwarding-class fcoe scheduler fcoe-sched
Configure the forwarding class set (
fcoe-pg) for the FCoE traffic.[edit class-of-service] user@switch# set forwarding-class-sets fcoe-pg class fcoe
Define the traffic control profile (
fcoe-tcp) to use on the FCoE forwarding class set.[edit class-of-service] user@switch# set traffic-control-profiles fcoe-tcp scheduler-map fcoe-map guaranteed-rate 3g user@switch# set traffic-control-profiles fcoe-tcp shaping-rate percent 100
Apply the FCoE forwarding class set and traffic control profile to the LAG interface and to the FCoE access interfaces.
[edit class-of-service] user@switch# set interfaces ae1 forwarding-class-set fcoe-pg output-traffic-control-profile fcoe-tcp user@switch# set interfaces xe-0/0/30 forwarding-class-set fcoe-pg output-traffic-control-profile fcoe-tcp user@switch# set interfaces xe-0/0/31 forwarding-class-set fcoe-pg output-traffic-control-profile fcoe-tcp user@switch# set interfaces xe-0/0/32 forwarding-class-set fcoe-pg output-traffic-control-profile fcoe-tcp user@switch# set interfaces xe-0/0/33 forwarding-class-set fcoe-pg output-traffic-control-profile fcoe-tcp
Enable PFC on the FCoE priority by creating a congestion notification profile (
fcoe-cnp) that applies FCoE to the IEEE 802.1 code point011.[edit class-of-service] user@switch# set congestion-notification-profile fcoe-cnp input ieee-802.1 code-point 011 pfc
Apply the PFC configuration to the LAG interface and to the FCoE access interfaces.
[edit class-of-service] user@switch# set interfaces ae1 congestion-notification-profile fcoe-cnp user@switch# set interfaces xe-0/0/30 congestion-notification-profile fcoe-cnp user@switch# set interfaces xe-0/0/31 congestion-notification-profile fcoe-cnp user@switch# set interfaces xe-0/0/32 congestion-notification-profile fcoe-cnp user@switch# set interfaces xe-0/0/33 congestion-notification-profile fcoe-cnp
Configure the VLAN for FCoE traffic (
fcoe_vlan).[edit vlans] user@switch# set fcoe_vlan vlan-id 100
Disable IGMP snooping on the FCoE VLAN.
[edit protocols] user@switch# set igmp-snooping vlan fcoe_vlan disable
Add the member interfaces to the LAG.
[edit interfaces] user@switch# set xe-0/0/25 ether-options 802.3ad ae1 user@switch# set xe-0/0/26 ether-options 802.3ad ae1
On the LAG (
ae1), configure the port mode astrunkand membership in the FCoE VLAN (fcoe_vlan).[edit interfaces] user@switch# set ae1 unit 0 family ethernet-switching port-mode trunk vlan members fcoe_vlan
On the FCoE access interfaces (
xe-0/0/30,xe-0/0/31,xe-0/0/32,xe-0/0/33), configure the port mode astagged-accessand membership in the FCoE VLAN (fcoe_vlan).[edit interfaces] user@switch# set xe-0/0/30 unit 0 family ethernet-switching port-mode tagged-access vlan members fcoe_vlan user@switch# set xe-0/0/31 unit 0 family ethernet-switching port-mode tagged-access vlan members fcoe_vlan user@switch# set xe-0/0/32 unit 0 family ethernet-switching port-mode tagged-access vlan members fcoe_vlan user@switch# set xe-0/0/33 unit 0 family ethernet-switching port-mode tagged-access vlan members fcoe_vlan
Set the MTU to
2180for the LAG and FCoE access interfaces.2180 bytes is the minimum size required to handle FCoE packets because of the payload and header sizes; you can configure the MTU to a higher number of bytes if desired, but not less than 2180 bytes.
[edit interfaces] user@switch# set ae1 mtu 2180 user@switch# set xe-0/0/30 mtu 2180 user@switch# set xe-0/0/31 mtu 2180 user@switch# set xe-0/0/32 mtu 2180 user@switch# set xe-0/0/33 mtu 2180
Set the LAG interface as an FCoE trusted port. Ports that connect to other switches should be trusted and should not perform FIP snooping:
[edit ethernet-switching-options] user@switch# set secure-access-port interface ae1 fcoe-trusted
Note:Access ports xe-0/0/30, xe-0/0/31, xe-0/0/32, and xe-0/0/33 are not configured as FCoE trusted ports. The access ports remain in the default state as untrusted ports because they connect directly to FCoE devices and must perform FIP snooping to ensure network security.
Enable FIP snooping on the FCoE VLAN to prevent unauthorized FCoE network access (this example uses VN2VN_Port FIP snooping; the example is equally valid if you use VN2VF_Port FIP snooping).
[edit ethernet-switching-options] user@switch# set secure-access-port vlan fcoe_vlan examine-fip examine-vn2vn beacon-period 90000
Results
Display the results of the CoS configuration on MC-LAG Switch S1 and on MC-LAG Switch S2 (the results on both switches are the same).
user@switch> show configuration class-of-service
traffic-control-profiles {
fcoe-tcp {
scheduler-map fcoe-map;
shaping-rate percent 100;
guaranteed-rate 3g;
}
}
forwarding-class-sets {
fcoe-pg {
class fcoe;
}
}
congestion-notification-profile {
fcoe-cnp {
input {
ieee-802.1 {
code-point 011 {
pfc;
}
}
}
}
}
interfaces {
ae0 {
forwarding-class-set {
fcoe-pg {
output-traffic-control-profile fcoe-tcp;
}
}
congestion-notification-profile fcoe-cnp;
}
ae1 {
forwarding-class-set {
fcoe-pg {
output-traffic-control-profile fcoe-tcp;
}
}
congestion-notification-profile fcoe-cnp;
}
}
scheduler-maps {
fcoe-map {
forwarding-class fcoe scheduler fcoe-sched;
}
}
schedulers {
fcoe-sched {
transmit-rate 3g;
shaping-rate percent 100;
priority low;
}
}
The forwarding class and classifier configurations are
not shown because the show command does not display default
portions of the configuration.
Display the results of the CoS configuration on FCoE Transit Switch TS1 and on FCoE Transit Switch TS2 (the results on both transit switches are the same).
user@switch> show configuration class-of-service
traffic-control-profiles {
fcoe-tcp {
scheduler-map fcoe-map;
shaping-rate percent 100;
guaranteed-rate 3g;
}
}
forwarding-class-sets {
fcoe-pg {
class fcoe;
}
}
congestion-notification-profile {
fcoe-cnp {
input {
ieee-802.1 {
code-point 011 {
pfc;
}
}
}
}
}
interfaces {
xe-0/0/30 {
forwarding-class-set {
fcoe-pg {
output-traffic-control-profile fcoe-tcp;
}
}
congestion-notification-profile fcoe-cnp;
}
xe-0/0/31 {
forwarding-class-set {
fcoe-pg {
output-traffic-control-profile fcoe-tcp;
}
}
congestion-notification-profile fcoe-cnp;
}
xe-0/0/32 {
forwarding-class-set {
fcoe-pg {
output-traffic-control-profile fcoe-tcp;
}
}
congestion-notification-profile fcoe-cnp;
}
xe-0/0/33 {
forwarding-class-set {
fcoe-pg {
output-traffic-control-profile fcoe-tcp;
}
}
congestion-notification-profile fcoe-cnp;
}
ae1 {
forwarding-class-set {
fcoe-pg {
output-traffic-control-profile fcoe-tcp;
}
}
congestion-notification-profile fcoe-cnp;
}
}
scheduler-maps {
fcoe-map {
forwarding-class fcoe scheduler fcoe-sched;
}
}
schedulers {
fcoe-sched {
transmit-rate 3g;
shaping-rate percent 100;
priority low;
}
}
Verification
To verify that the CoS components and FIP snooping
have been configured and are operating properly, perform these tasks.
Because this example uses the default fcoe forwarding class
and the default IEEE 802.1p trusted classifier, the verification of
those configurations is not shown.
- Verifying That the Output Queue Schedulers Have Been Created
- Verifying That the Priority Group Output Scheduler (Traffic Control Profile) Has Been Created
- Verifying That the Forwarding Class Set (Priority Group) Has Been Created
- Verifying That Priority-Based Flow Control Has Been Enabled
- Verifying That the Interface Class of Service Configuration Has Been Created
- Verifying That the Interfaces Are Correctly Configured
- Verifying That FIP Snooping Is Enabled on the FCoE VLAN on FCoE Transit Switches TS1 and TS2 Access Interfaces
- Verifying That the FIP Snooping Mode Is Correct on FCoE Transit Switches TS1 and TS2
- Verifying That IGMP Snooping Is Disabled on the FCoE VLAN
Verifying That the Output Queue Schedulers Have Been Created
Purpose
Verify that the output queue scheduler for FCoE traffic has the correct bandwidth parameters and priorities, and is mapped to the correct forwarding class (output queue). Queue scheduler verification is the same on each of the four switches.
Action
List the scheduler map using the operational mode command show class-of-service scheduler-map fcoe-map:
user@switch> show class-of-service scheduler-map fcoe-map
Scheduler map: fcoe-map, Index: 9023
Scheduler: fcoe-sched, Forwarding class: fcoe, Index: 37289
Transmit rate: 3000000000 bps, Rate Limit: none, Buffer size: remainder,
Buffer Limit: none, Priority: low
Excess Priority: unspecified
Shaping rate: 100 percent,
drop-profile-map-set-type: mark
Drop profiles:
Loss priority Protocol Index Name
Low any 1 <default-drop-profile>
Medium high any 1 <default-drop-profile>
High any 1 <default-drop-profile>
Meaning
The show class-of-service scheduler-map fcoe-map command lists the properties of the scheduler map fcoe-map. The command output includes:
The name of the scheduler map (
fcoe-map)The name of the scheduler (
fcoe-sched)The forwarding classes mapped to the scheduler (
fcoe)The minimum guaranteed queue bandwidth (transmit rate
3000000000 bps)The scheduling priority (
low)The maximum bandwidth in the priority group the queue can consume (shaping rate
100 percent)The drop profile loss priority for each drop profile name. This example does not include drop profiles because you do not apply drop profiles to FCoE traffic.
Verifying That the Priority Group Output Scheduler (Traffic Control Profile) Has Been Created
Purpose
Verify that the traffic control profile fcoe-tcp has been created with the correct bandwidth parameters and scheduler
mapping. Priority group scheduler verification is the same on each
of the four switches.
Action
List the FCoE traffic control profile properties using
the operational mode command show class-of-service traffic-control-profile
fcoe-tcp:
user@switch> show class-of-service traffic-control-profile fcoe-tcp Traffic control profile: fcoe-tcp, Index: 18303 Shaping rate: 100 percent Scheduler map: fcoe-map Guaranteed rate: 3000000000
Meaning
The show class-of-service traffic-control-profile
fcoe-tcp command lists all of the configured traffic control
profiles. For each traffic control profile, the command output includes:
The name of the traffic control profile (
fcoe-tcp)The maximum port bandwidth the priority group can consume (shaping rate
100 percent)The scheduler map associated with the traffic control profile (
fcoe-map)The minimum guaranteed priority group port bandwidth (guaranteed rate
3000000000in bps)
Verifying That the Forwarding Class Set (Priority Group) Has Been Created
Purpose
Verify that the FCoE priority group has been created
and that the fcoe priority (forwarding class) belongs to
the FCoE priority group. Forwarding class set verification is the
same on each of the four switches.
Action
List the forwarding class sets using the operational
mode command show class-of-service forwarding-class-set fcoe-pg:
user@switch> show class-of-service forwarding-class-set fcoe-pg Forwarding class set: fcoe-pg, Type: normal-type, Forwarding class set index: 31420 Forwarding class Index fcoe 1
Meaning
The show class-of-service forwarding-class-set
fcoe-pg command lists all of the forwarding classes (priorities)
that belong to the fcoe-pg priority group, and the internal
index number of the priority group. The command output shows that
the forwarding class set fcoe-pg includes the forwarding
class fcoe.
Verifying That Priority-Based Flow Control Has Been Enabled
Purpose
Verify that PFC is enabled on the FCoE code point. PFC verification is the same on each of the four switches.
Action
List the FCoE congestion notification profile using
the operational mode command show class-of-service congestion-notification
fcoe-cnp:
user@switch> show class-of-service congestion-notification fcoe-cnp
Type: Input, Name: fcoe-cnp, Index: 6879
Cable Length: 100 m
Priority PFC MRU
000 Disabled
001 Disabled
010 Disabled
011 Enabled 2500
100 Disabled
101 Disabled
110 Disabled
111 Disabled
Type: Output
Priority Flow-Control-Queues
000
0
001
1
010
2
011
3
100
4
101
5
110
6
111
7
Meaning
The show class-of-service congestion-notification
fcoe-cnp command lists all of the IEEE 802.1p code points in
the congestion notification profile that have PFC enabled. The command
output shows that PFC is enabled on code point 011 (fcoe queue) for the fcoe-cnp congestion notification
profile.
The command also shows the default cable length (100 meters), the default maximum receive unit (2500 bytes),
and the default mapping of priorities to output queues because this
example does not include configuring these options.
Verifying That the Interface Class of Service Configuration Has Been Created
Purpose
Verify that the CoS properties of the interfaces are correct. The verification output on MC-LAG Switches S1 and S2 differs from the output on FCoE Transit Switches TS1 and TS2.
Action
List the interface CoS configuration on MC-LAG Switches
S1 and S2 using the operational mode command show configuration
class-of-service interfaces:
user@switch> show configuration class-of-service interfaces
ae0 {
forwarding-class-set {
fcoe-pg {
output-traffic-control-profile fcoe-tcp;
}
}
congestion-notification-profile fcoe-cnp;
}
ae1 {
forwarding-class-set {
fcoe-pg {
output-traffic-control-profile fcoe-tcp;
}
}
congestion-notification-profile fcoe-cnp;
}
List the interface CoS configuration on FCoE Transit Switches
TS1 and TS2 using the operational mode command show configuration
class-of-service interfaces:
user@switch> show configuration class-of-service interfaces
xe-0/0/30 {
forwarding-class-set {
fcoe-pg {
output-traffic-control-profile fcoe-tcp;
}
}
congestion-notification-profile fcoe-cnp;
}
xe-0/0/31 {
forwarding-class-set {
fcoe-pg {
output-traffic-control-profile fcoe-tcp;
}
}
congestion-notification-profile fcoe-cnp;
}
xe-0/0/32 {
forwarding-class-set {
fcoe-pg {
output-traffic-control-profile fcoe-tcp;
}
}
congestion-notification-profile fcoe-cnp;
}
xe-0/0/33 {
forwarding-class-set {
fcoe-pg {
output-traffic-control-profile fcoe-tcp;
}
}
congestion-notification-profile fcoe-cnp;
}
ae1 {
forwarding-class-set {
fcoe-pg {
output-traffic-control-profile fcoe-tcp;
}
}
congestion-notification-profile fcoe-cnp;
}
Meaning
The show configuration class-of-service interfaces command lists the class of service configuration for all interfaces.
For each interface, the command output includes:
The name of the interface (for example,
ae0orxe-0/0/30)The name of the forwarding class set associated with the interface (
fcoe-pg)The name of the traffic control profile associated with the interface (output traffic control profile,
fcoe-tcp)The name of the congestion notification profile associated with the interface (
fcoe-cnp)
Interfaces that are members of a LAG are not shown individually.
The LAG or MC-LAG CoS configuration is applied to all interfaces that
are members of the LAG or MC-LAG. For example, the interface CoS configuration
output on MC-LAG Switches S1 and S2 shows the LAG CoS configuration
but does not show the CoS configuration of the member interfaces separately.
The interface CoS configuration output on FCoE Transit Switches TS1
and TS2 shows the LAG CoS configuration but also shows the configuration
for interfaces xe-0/0/30, xe-0/0/31, xe-0/0/32, and xe-0/0/33, which are not members of a LAG.
Verifying That the Interfaces Are Correctly Configured
Purpose
Verify that the LAG membership, MTU, VLAN membership, and port mode of the interfaces are correct. The verification output on MC-LAG Switches S1 and S2 differs from the output on FCoE Transit Switches TS1 and TS2.
Action
List the interface configuration on MC-LAG Switches
S1 and S2 using the operational mode command show configuration
interfaces:
user@switch> show configuration interfaces
xe-0/0/10 {
ether-options {
802.3ad ae0;
}
}
xe-0/0/11 {
ether-options {
802.3ad ae0;
}
}
xe-0/0/20 {
ether-options {
802.3ad ae1;
}
}
xe-0/0/21 {
ether-options {
802.3ad ae1;
}
}
ae0 {
mtu 2180;
unit 0 {
family ethernet-switching {
port-mode trunk;
vlan {
members fcoe_vlan;
}
}
}
}
ae1 {
mtu 2180;
unit 0 {
family ethernet-switching {
port-mode trunk;
vlan {
members fcoe_vlan;
}
}
}
}
List the interface configuration on FCoE Transit Switches TS1
and TS2 using the operational mode command show configuration
interfaces:
user@switch> show configuration interfaces
xe-0/0/25 {
ether-options {
802.3ad ae1;
}
}
xe-0/0/26 {
ether-options {
802.3ad ae1;
}
}
xe-0/0/30 {
mtu 2180;
unit 0 {
family ethernet-switching {
port-mode tagged-access;
vlan {
members fcoe_vlan;
}
}
}
}
xe-0/0/31 {
mtu 2180;
unit 0 {
family ethernet-switching {
port-mode tagged-access;
vlan {
members fcoe_vlan;
}
}
}
}
xe-0/0/32 {
mtu 2180;
unit 0 {
family ethernet-switching {
port-mode tagged-access;
vlan {
members fcoe_vlan;
}
}
}
}
xe-0/0/33 {
mtu 2180;
unit 0 {
family ethernet-switching {
port-mode tagged-access;
vlan {
members fcoe_vlan;
}
}
}
}
ae1 {
mtu 2180;
unit 0 {
family ethernet-switching {
port-mode trunk;
vlan {
members fcoe_vlan;
}
}
}
}
Meaning
The show configuration interfaces command
lists the configuration of each interface by interface name.
For each interface that is a member of a LAG, the command lists only the name of the LAG to which the interface belongs.
For each LAG interface and for each interface that is not a member of a LAG, the command output includes:
The MTU (
2180)The unit number of the interface (
0)The port mode (
trunkmode for interfaces that connect two switches,tagged-accessmode for interfaces that connect to FCoE hosts)The name of the VLAN in which the interface is a member (
fcoe_vlan)
Verifying That FIP Snooping Is Enabled on the FCoE VLAN on FCoE Transit Switches TS1 and TS2 Access Interfaces
Purpose
Verify that FIP snooping is enabled on the FCoE VLAN access interfaces. FIP snooping is enabled only on the FCoE access interfaces, so it is enabled only on FCoE Transit Switches TS1 and TS2. FIP snooping is not enabled on MC-LAG Switches S1 and S2 because FIP snooping is done at the Transit Switch TS1 and TS2 FCoE access ports.
Action
List the port security configuration on FCoE Transit
Switches TS1 and TS2 using the operational mode command show
configuration ethernet-switching-options secure-access-port:
user@switch> show configuration ethernet-switching-options secure-access-port
interface ae1.0 {
fcoe-trusted;
}
vlan fcoe_vlan {
examine-fip {
examine-vn2vn {
beacon-period 90000;
}
}
}Meaning
The show configuration ethernet-switching-options secure-access-port command lists port security information, including whether a port
is trusted. The command output shows that:
LAG port
ae1.0, which connects the FCoE transit switch to the MC-LAG switches, is configured as an FCoE trusted interface. FIP snooping is not performed on the member interfaces of the LAG (xe-0/0/25 and xe-0/0/26).FIP snooping is enabled (
examine-fip) on the FCoE VLAN (fcoe_vlan), the type of FIP snooping is VN2VN_Port FIP snooping (examine-vn2vn), and the beacon period is set to90000milliseconds. On Transit Switches TS1 and TS2, all interface members of the FCoE VLAN perform FIP snooping unless the interface is configured as FCoE trusted. On Transit Switches TS1 and TS2, interfaces xe-0/0/30, xe-0/0/31, xe-0/0/32, and xe-0/0/33 perform FIP snooping because they are not configured as FCoE trusted. The interface members of LAG ae1 (xe-0/0/25 and xe-0/0/26) do not perform FIP snooping because the LAG is configured as FCoE trusted.
Verifying That the FIP Snooping Mode Is Correct on FCoE Transit Switches TS1 and TS2
Purpose
Verify that the FIP snooping mode is correct on the FCoE VLAN. FIP snooping is enabled only on the FCoE access interfaces, so it is enabled only on FCoE Transit Switches TS1 and TS2. FIP snooping is not enabled on MC-LAG Switches S1 and S2 because FIP snooping is done at the Transit Switch TS1 and TS2 FCoE access ports.
Action
List the FIP snooping configuration on FCoE Transit
Switches TS1 and TS2 using the operational mode command show
fip snooping brief:
user@switch> show fip snooping brief VLAN: fcoe_vlan, Mode: VN2VN Snooping FC-MAP: 0e:fd:00 …
The output has been truncated to show only the relevant information.
Meaning
The show fip snooping brief command lists
FIP snooping information, including the FIP snooping VLAN and the
FIP snooping mode. The command output shows that:
The VLAN on which FIP snooping is enabled is
fcoe_vlanThe FIP snooping mode is VN2VN_Port FIP snooping (
VN2VN Snooping)
Verifying That IGMP Snooping Is Disabled on the FCoE VLAN
Purpose
Verify that IGMP snooping is disabled on the FCoE VLAN on all four switches.
Action
List the IGMP snooping protocol information on each
of the four switches using the show configuration protocols igmp-snooping command:
user@switch> show configuration protocols igmp-snooping
vlan fcoe_vlan {
disable;
}
Meaning
The show configuration protocols igmp-snooping command lists the IGMP snooping configuration for the VLANs configured
on the switch. The command output shows that IGMP snooping is disabled
on the FCoE VLAN (fcoe_vlan).
Example: EVPN-MPLS Interworking With an MC-LAG Topology
This example shows how to use Ethernet VPN (EVPN) to extend a multichassis link aggregation (MC-LAG) network over an MPLS network to a data center network or geographically distributed campus network.
EVPN-MPLS interworking is supported with an MC-LAG topology in which two MX Series routers, two EX9200 switches, or a mix of the two Juniper Networks devices function as MC-LAG peers, which use the Inter-Chassis Control Protocol (ICCP) and an interchassis link (ICL) to connect and maintain the topology. The MC-LAG peers are connected to a provider edge (PE) device in an MPLS network. The PE device can be either an MX Series router or an EX9200 switch.
This example shows how to configure the MC-LAG peers and PE device in the MPLS network to interwork with each other.
Requirements
This example uses the following hardware and software components:
Three EX9200 switches:
PE1 and PE2, which both function as MC-LAG peers in the MC-LAG topology and EVPN BGP peers in the EVPN-MPLS overlay network.
PE3, which functions as an EVPN BGP peer in the EVPN-MPLS overlay network.
The EX9200 switches are running Junos OS Release 17.4R1 or later software.
Although the MC-LAG topology includes two customer edge (CE) devices, this example focuses on the configuration of the PE1, PE2, and PE3.
Overview and Topology
Figure 7 shows an MC-LAG topology with provider edge devices PE1 and PE2 that are configured as MC-LAG peers. The MC-LAG peers exchange control information over an ICCP link and data traffic over an ICL. In this example, the ICL is an aggregated Ethernet interface that is comprised of two interfaces.
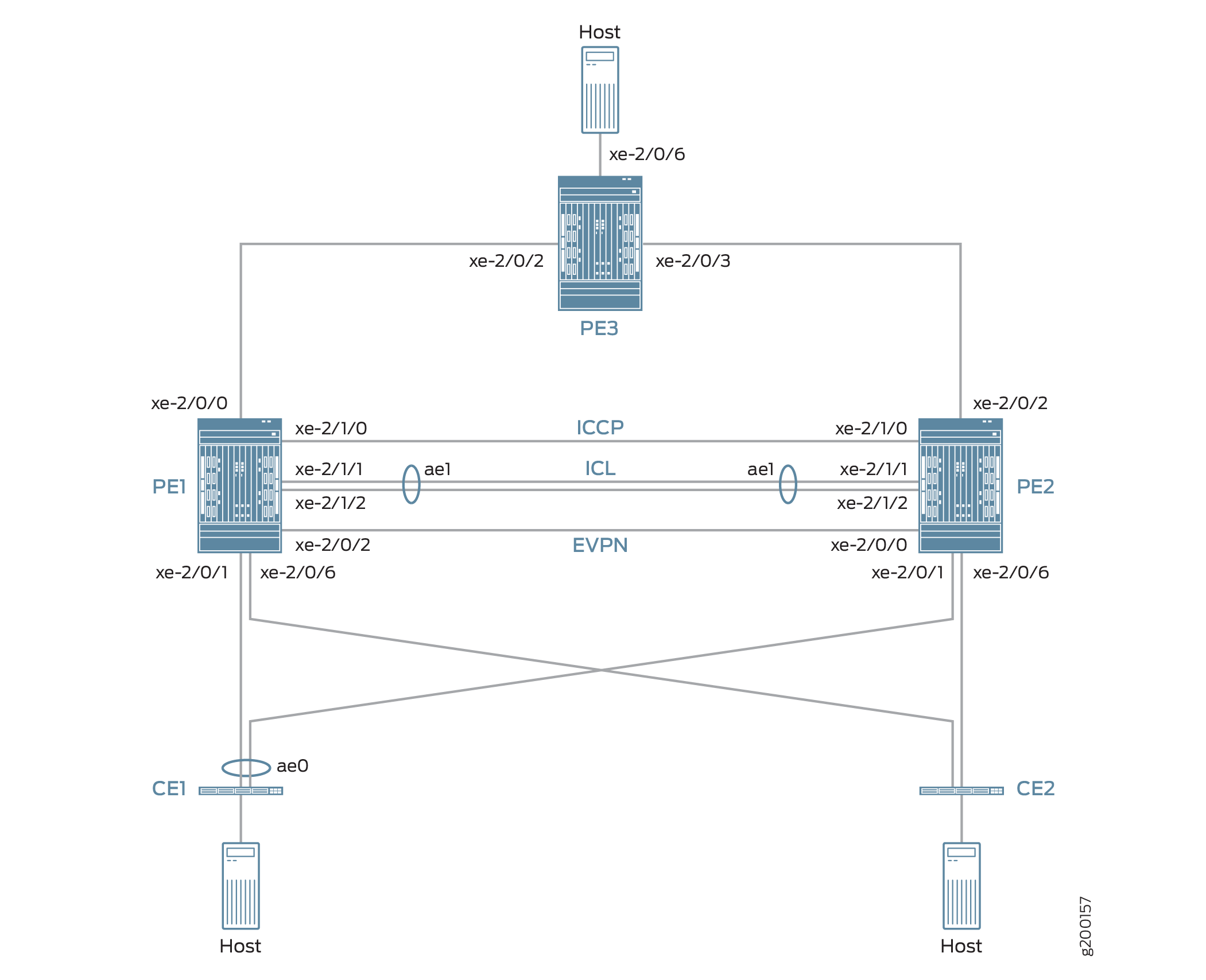
The topology in Figure 7 also includes CE devices CE1 and CE2, which are both multihomed to each PE device. The links between CE1 and the two PE devices are bundled as an aggregated Ethernet interface on which MC-LAG in active-active mode is configured.
The topology in Figure 7 also includes PE3 at the edge of an MPLS network. PE3 functions as the gateway between the MC-LAG network and either a data center or a geographically distributed campus network. PE1, PE2, and PE3 run EVPN, which enables hosts in the MC-LAG network to communicate with hosts in the data center or other campus network by way of an intervening MPLS network.
From the perspective of the EVPN-MPLS interworking feature, PE3 functions solely as an EVPN BGP peer, and PE1 and PE2 in the MC-LAG topology have dual roles:
MC-LAG peers in the MC-LAG network.
EVPN BGP peers in the EVPN-MPLS network.
Because of the dual roles, PE1 and PE2 are configured with MC-LAG, EVPN, BGP, and MPLS attributes.
Table 4 outlines key MC-LAG and EVPN (BGP and MPLS) attributes configured on PE1, PE2, and PE3.
Key Attributes |
PE1 |
PE2 |
PE3 |
|---|---|---|---|
MC-LAG Attributes |
|||
Interfaces |
ICL: aggregated Ethernet interface ae1, which is comprised of xe-2/1/1 and xe-2/1/2 ICCP: xe-2/1/0 |
ICL: aggregated Ethernet interface ae1, which is comprised of xe-2/1/1 and xe-2/1/2 ICCP: xe-2/1/0 |
Not applicable |
EVPN-MPLS |
|||
Interfaces |
Connection to PE3: xe-2/0/0 Connection to PE2: xe-2/0/2 |
Connection to PE3: xe-2/0/2 Connection to PE1: xe-2/0/0 |
Connection to PE1: xe-2/0/2 Connection to PE2: xe-2/0/3 |
IP addresses |
BGP peer address: 198.51.100.1 |
BGP peer address: 198.51.100.2 |
BGP peer address: 198.51.100.3 |
Autonomous system |
65000 |
65000 |
65000 |
Virtual switch routing instances |
evpn1, evpn2, evpn3 |
evpn1, evpn2, evpn3 |
evpn1, evpn2, evpn3 |
Note the following about the EVPN-MPLS interworking feature and its configuration:
You must configure Ethernet segment identifiers (ESIs) on the dual-homed interfaces in the MC-LAG topology. The ESIs enable EVPN to identify the dual-homed interfaces.
The only type of routing instance that is supported is the virtual switch instance (
set routing-instances name instance-type virtual-switch).On the MC-LAG peers, you must include the
bgp-peerconfiguration statement in the[edit routing-instances name protocols evpn mclag]hierarchy level. This configuration statement enables the interworking of EVPN-MPLS with MC-LAG on the MC-LAG peers.Address Resolution Protocol (ARP) suppression is not supported.
PE1 and PE2 Configuration
To configure PE1 and PE2, perform these tasks:
- CLI Quick Configuration
- PE1: Configuring MC-LAG
- PE1: Configuring EVPN-MPLS
- PE2: Configuring MC-LAG
- PE2: Configuring EVPN-MPLS
CLI Quick Configuration
PE1: MC-LAG Configuration
set chassis aggregated-devices ethernet device-count 3 set interfaces xe-2/0/1 gigether-options 802.3ad ae0 set interfaces ae0 flexible-vlan-tagging set interfaces ae0 encapsulation flexible-ethernet-services set interfaces ae0 aggregated-ether-options lacp active set interfaces ae0 aggregated-ether-options lacp periodic fast set interfaces ae0 aggregated-ether-options lacp system-id 00:00:11:11:11:11 set interfaces ae0 aggregated-ether-options lacp admin-key 1 set interfaces ae0 aggregated-ether-options mc-ae mc-ae-id 1 set interfaces ae0 aggregated-ether-options mc-ae redundancy-group 2 set interfaces ae0 aggregated-ether-options mc-ae chassis-id 0 set interfaces ae0 aggregated-ether-options mc-ae mode active-active set interfaces ae0 aggregated-ether-options mc-ae status-control active set interfaces ae0 unit 1 esi 00:11:22:33:44:55:66:77:88:99 set interfaces ae0 unit 1 esi all-active set interfaces ae0 unit 1 family ethernet-switching interface-mode trunk set interfaces ae0 unit 1 family ethernet-switching vlan members 1 set interfaces ae0 unit 2 esi 00:11:11:11:11:11:11:11:11:11 set interfaces ae0 unit 2 esi all-active set interfaces ae0 unit 2 family ethernet-switching interface-mode trunk set interfaces ae0 unit 2 family ethernet-switching vlan members 2 set interfaces ae0 unit 3 esi 00:11:22:22:22:22:22:22:22:22 set interfaces ae0 unit 3 esi all-active set interfaces ae0 unit 3 family ethernet-switching interface-mode trunk set interfaces ae0 unit 3 family ethernet-switching vlan members 3 set interfaces xe-2/0/6 enable set interfaces xe-2/0/6 flexible-vlan-tagging set interfaces xe-2/0/6 encapsulation flexible-ethernet-services set interfaces xe-2/0/6 unit 1 family ethernet-switching interface-mode trunk set interfaces xe-2/0/6 unit 1 family ethernet-switching vlan members 1 set interfaces xe-2/0/6 unit 2 family ethernet-switching interface-mode trunk set interfaces xe-2/0/6 unit 2 family ethernet-switching vlan members 2 set interfaces xe-2/0/6 unit 3 family ethernet-switching interface-mode trunk set interfaces xe-2/0/6 unit 3 family ethernet-switching vlan members 3 set interfaces xe-2/1/0 unit 0 family inet address 203.0.113.1/24 set interfaces xe-2/1/1 gigether-options 802.3ad ae1 set interfaces xe-2/1/2 gigether-options 802.3ad ae1 set interfaces ae1 flexible-vlan-tagging set interfaces ae1 encapsulation flexible-ethernet-services set interfaces ae1 aggregated-ether-options lacp active set interfaces ae1 unit 1 family ethernet-switching interface-mode trunk set interfaces ae1 unit 1 family ethernet-switching vlan members 1 set interfaces ae1 unit 2 family ethernet-switching interface-mode trunk set interfaces ae1 unit 2 family ethernet-switching vlan members 2 set interfaces ae1 unit 3 family ethernet-switching interface-mode trunk set interfaces ae1 unit 3 family ethernet-switching vlan members 3 set multi-chassis multi-chassis-protection 203.0.113.2 interface ae1 set protocols iccp local-ip-addr 203.0.113.1 set protocols iccp peer 203.0.113.2 session-establishment-hold-time 600 set protocols iccp peer 203.0.113.2 redundancy-group-id-list 2 set protocols iccp peer 203.0.113.2 liveness-detection minimum-interval 10000 set protocols iccp peer 203.0.113.2 liveness-detection multiplier 3
PE1: EVPN-MPLS Configuration
set interfaces lo0 unit 0 family inet address 198.51.100.1/32 primary set interfaces xe-2/0/0 unit 0 family inet address 192.0.2.2/24 set interfaces xe-2/0/0 unit 0 family mpls set interfaces xe-2/0/2 unit 0 family inet address 192.0.2.111/24 set interfaces xe-2/0/2 unit 0 family mpls set interfaces irb unit 1 family inet address 10.2.1.1/24 virtual-gateway-address 10.2.1.254 set interfaces irb unit 2 family inet address 10.2.2.1/24 virtual-gateway-address 10.2.2.254 set interfaces irb unit 3 family inet address 10.2.3.1/24 virtual-gateway-address 10.2.3.254 set routing-options router-id 198.51.100.1 set routing-options autonomous-system 65000 set routing-options forwarding-table export evpn-pplb set protocols mpls interface xe-2/0/0.0 set protocols mpls interface xe-2/0/2.0 set protocols bgp group evpn type internal set protocols bgp group evpn local-address 198.51.100.1 set protocols bgp group evpn family evpn signaling set protocols bgp group evpn local-as 65000 set protocols bgp group evpn neighbor 198.51.100.2 set protocols bgp group evpn neighbor 198.51.100.3 set protocols ospf area 0.0.0.0 interface lo0.0 set protocols ospf area 0.0.0.0 interface xe-2/0/0.0 set protocols ospf area 0.0.0.0 interface xe-2/0/2.0 set protocols ldp interface xe-2/0/0.0 set protocols ldp interface xe-2/0/2.0 set protocols ldp interface lo0.0 set policy-options policy-statement evpn-pplb from protocol evpn set policy-options policy-statement evpn-pplb then load-balance per-packet set routing-instances evpn1 instance-type virtual-switch set routing-instances evpn1 interface xe-2/0/6.1 set routing-instances evpn1 interface ae0.1 set routing-instances evpn1 interface ae1.1 set routing-instances evpn1 route-distinguisher 1:10 set routing-instances evpn1 vrf-target target:1:5 set routing-instances evpn1 protocols evpn extended-vlan-list 1 set routing-instances evpn1 protocols evpn mclag bgp-peer 198.51.100.2 set routing-instances evpn1 switch-options service-id 1 set routing-instances evpn1 vlans v1 vlan-id 1 set routing-instances evpn1 vlans v1 l3-interface irb.1 set routing-instances evpn2 instance-type virtual-switch set routing-instances evpn2 interface xe-2/0/6.2 set routing-instances evpn2 interface ae0.2 set routing-instances evpn2 interface ae1.2 set routing-instances evpn2 route-distinguisher 1:20 set routing-instances evpn2 vrf-target target:1:6 set routing-instances evpn2 protocols evpn extended-vlan-list 2 set routing-instances evpn2 protocols evpn mclag bgp-peer 198.51.100.2 set routing-instances evpn2 switch-options service-id 2 set routing-instances evpn2 vlans v1 vlan-id 2 set routing-instances evpn2 vlans v1 l3-interface irb.2 set routing-instances evpn3 instance-type virtual-switch set routing-instances evpn3 interface xe-2/0/6.3 set routing-instances evpn3 interface ae0.3 set routing-instances evpn3 interface ae1.3 set routing-instances evpn3 route-distinguisher 1:30 set routing-instances evpn3 vrf-target target:1:7 set routing-instances evpn3 protocols evpn extended-vlan-list 3 set routing-instances evpn3 protocols evpn mclag bgp-peer 198.51.100.2 set routing-instances evpn3 switch-options service-id 3 set routing-instances evpn3 vlans v1 vlan-id 3 set routing-instances evpn3 vlans v1 l3-interface irb.3
PE2: MC-LAG Configuration
set chassis aggregated-devices ethernet device-count 3 set interfaces xe-2/0/1 gigether-options 802.3ad ae0 set interfaces xe-2/0/6 enable set interfaces xe-2/0/6 flexible-vlan-tagging set interfaces xe-2/0/6 encapsulation flexible-ethernet-services set interfaces xe-2/0/6 unit 1 family ethernet-switching interface-mode trunk set interfaces xe-2/0/6 unit 1 family ethernet-switching vlan members 1 set interfaces xe-2/0/6 unit 2 family ethernet-switching interface-mode trunk set interfaces xe-2/0/6 unit 2 family ethernet-switching vlan members 2 set interfaces xe-2/0/6 unit 3 family ethernet-switching interface-mode trunk set interfaces xe-2/0/6 unit 3 family ethernet-switching vlan members 3 set interfaces xe-2/1/0 unit 0 family inet address 203.0.113.2/24 set interfaces xe-2/1/1 gigether-options 802.3ad ae1 set interfaces xe-2/1/2 gigether-options 802.3ad ae1 set interfaces ae0 flexible-vlan-tagging set interfaces ae0 encapsulation flexible-ethernet-services set interfaces ae0 aggregated-ether-options lacp active set interfaces ae0 aggregated-ether-options lacp periodic fast set interfaces ae0 aggregated-ether-options lacp system-id 00:00:11:11:11:11 set interfaces ae0 aggregated-ether-options lacp admin-key 1 set interfaces ae0 aggregated-ether-options mc-ae mc-ae-id 1 set interfaces ae0 aggregated-ether-options mc-ae redundancy-group 2 set interfaces ae0 aggregated-ether-options mc-ae chassis-id 1 set interfaces ae0 aggregated-ether-options mc-ae mode active-active set interfaces ae0 aggregated-ether-options mc-ae status-control standby set interfaces ae0 unit 1 esi 00:11:22:33:44:55:66:77:88:99 set interfaces ae0 unit 1 esi all-active set interfaces ae0 unit 1 family ethernet-switching interface-mode trunk set interfaces ae0 unit 1 family ethernet-switching vlan members 1 set interfaces ae0 unit 2 esi 00:11:11:11:11:11:11:11:11:11 set interfaces ae0 unit 2 esi all-active set interfaces ae0 unit 2 family ethernet-switching interface-mode trunk set interfaces ae0 unit 2 family ethernet-switching vlan members 2 set interfaces ae0 unit 3 esi 00:11:22:22:22:22:22:22:22:22 set interfaces ae0 unit 3 esi all-active set interfaces ae0 unit 3 family ethernet-switching interface-mode trunk set interfaces ae0 unit 3 family ethernet-switching vlan members 3 set interfaces ae1 flexible-vlan-tagging set interfaces ae1 encapsulation flexible-ethernet-services set interfaces ae1 aggregated-ether-options lacp active set interfaces ae1 unit 1 family ethernet-switching interface-mode trunk set interfaces ae1 unit 1 family ethernet-switching vlan members 1 set interfaces ae1 unit 2 family ethernet-switching interface-mode trunk set interfaces ae1 unit 2 family ethernet-switching vlan members 2 set interfaces ae1 unit 3 family ethernet-switching interface-mode trunk set interfaces ae1 unit 3 family ethernet-switching vlan members 3 set multi-chassis multi-chassis-protection 203.0.113.1 interface ae1 set protocols iccp local-ip-addr 203.0.113.2 set protocols iccp peer 203.0.113.1 session-establishment-hold-time 600 set protocols iccp peer 203.0.113.1 redundancy-group-id-list 2 set protocols iccp peer 203.0.113.1 liveness-detection minimum-interval 10000 set protocols iccp peer 203.0.113.1 liveness-detection multiplier 3
PE2: EVPN-MPLS Configuration
set interfaces xe-2/0/0 unit 0 family inet address 192.0.2.222/24 set interfaces xe-2/0/0 unit 0 family mpls set interfaces xe-2/0/2 unit 0 family inet address 192.0.2.22/24 set interfaces xe-2/0/2 unit 0 family mpls set interfaces lo0 unit 0 family inet address 198.51.100.2/32 primary set interfaces irb unit 1 family inet address 10.2.1.2/24 virtual-gateway-address 10.2.1.254 set interfaces irb unit 2 family inet address 10.2.2.2/24 virtual-gateway-address 10.2.2.254 set interfaces irb unit 3 family inet address 10.2.3.2/24 virtual-gateway-address 10.2.3.254 set routing-options router-id 198.51.100.2 set routing-options autonomous-system 65000 set routing-options forwarding-table export evpn-pplb set protocols mpls interface xe-2/0/2.0 set protocols mpls interface xe-2/0/0.0 set protocols bgp group evpn type internal set protocols bgp group evpn local-address 198.51.100.2 set protocols bgp group evpn family evpn signaling set protocols bgp group evpn local-as 65000 set protocols bgp group evpn neighbor 198.51.100.1 set protocols bgp group evpn neighbor 198.51.100.3 set protocols ospf area 0.0.0.0 interface lo0.0 set protocols ospf area 0.0.0.0 interface xe-2/0/0.0 set protocols ospf area 0.0.0.0 interface xe-2/0/2.0 set protocols ldp interface xe-2/0/0.0 set protocols ldp interface xe-2/0/2.0 set protocols ldp interface lo0.0 set policy-options policy-statement evpn-pplb from protocol evpn set policy-options policy-statement evpn-pplb then load-balance per-packet set routing-instances evpn1 instance-type virtual-switch set routing-instances evpn1 interface xe-2/0/6.1 set routing-instances evpn1 interface ae0.1 set routing-instances evpn1 interface ae1.1 set routing-instances evpn1 route-distinguisher 1:11 set routing-instances evpn1 vrf-target target:1:5 set routing-instances evpn1 protocols evpn extended-vlan-list 1 set routing-instances evpn1 protocols evpn mclag bgp-peer 198.51.100.1 set routing-instances evpn1 switch-options service-id 1 set routing-instances evpn1 vlans v1 vlan-id 1 set routing-instances evpn1 vlans v1 l3-interface irb.1 set routing-instances evpn2 instance-type virtual-switch set routing-instances evpn2 interface xe-2/0/6.2 set routing-instances evpn2 interface ae0.2 set routing-instances evpn2 interface ae1.2 set routing-instances evpn2 route-distinguisher 1:21 set routing-instances evpn2 vrf-target target:1:6 set routing-instances evpn2 protocols evpn extended-vlan-list 2 set routing-instances evpn2 protocols evpn mclag bgp-peer 198.51.100.1 set routing-instances evpn2 switch-options service-id 2 set routing-instances evpn2 vlans v1 vlan-id 2 set routing-instances evpn2 vlans v1 l3-interface irb.2 set routing-instances evpn3 instance-type virtual-switch set routing-instances evpn3 interface xe-2/0/6.3 set routing-instances evpn3 interface ae0.3 set routing-instances evpn3 interface ae1.3 set routing-instances evpn3 route-distinguisher 1:31 set routing-instances evpn3 vrf-target target:1:7 set routing-instances evpn3 protocols evpn extended-vlan-list 3 set routing-instances evpn3 protocols evpn mclag bgp-peer 198.51.100.1 set routing-instances evpn3 switch-options service-id 3 set routing-instances evpn3 vlans v1 vlan-id 3 set routing-instances evpn3 vlans v1 l3-interface irb.3
PE1: Configuring MC-LAG
Step-by-Step Procedure
Set the number of aggregated Ethernet interfaces on PE1.
[edit] user@switch# set chassis aggregated-devices ethernet device-count 3
Configure aggregated Ethernet interface ae0 on interface xe-2/0/1, and configure LACP and MC-LAG on ae0. Divide aggregated Ethernet interface ae0 into three logical interfaces (ae0.1, ae0.2, and ae0.3). For each logical interface, specify an ESI, place the logical interface is in MC-LAG active-active mode, and map the logical interface to a VLAN.
[edit] user@switch# set interfaces xe-2/0/1 gigether-options 802.3ad ae0 user@switch# set interfaces ae0 flexible-vlan-tagging user@switch# set interfaces ae0 encapsulation flexible-ethernet-services user@switch# set interfaces ae0 aggregated-ether-options lacp active user@switch# set interfaces ae0 aggregated-ether-options lacp periodic fast user@switch# set interfaces ae0 aggregated-ether-options lacp system-id 00:00:11:11:11:11 user@switch# set interfaces ae0 aggregated-ether-options lacp admin-key 1 user@switch# set interfaces ae0 aggregated-ether-options mc-ae mc-ae-id 1 user@switch# set interfaces ae0 aggregated-ether-options mc-ae redundancy-group 2 user@switch# set interfaces ae0 aggregated-ether-options mc-ae chassis-id 0 user@switch# set interfaces ae0 aggregated-ether-options mc-ae mode active-active user@switch# set interfaces ae0 aggregated-ether-options mc-ae status-control active user@switch# set interfaces ae0 unit 1 esi 00:11:22:33:44:55:66:77:88:99 user@switch# set interfaces ae0 unit 1 esi all-active user@switch# set interfaces ae0 unit 1 family ethernet-switching interface-mode trunk user@switch# set interfaces ae0 unit 1 family ethernet-switching vlan members 1 user@switch# set interfaces ae0 unit 2 esi 00:11:11:11:11:11:11:11:11:11 user@switch# set interfaces ae0 unit 2 esi all-active user@switch# set interfaces ae0 unit 2 family ethernet-switching interface-mode trunk user@switch# set interfaces ae0 unit 2 family ethernet-switching vlan members 2 user@switch# set interfaces ae0 unit 3 esi 00:11:22:22:22:22:22:22:22:22 user@switch# set interfaces ae0 unit 3 esi all-active user@switch# set interfaces ae0 unit 3 family ethernet-switching interface-mode trunk user@switch# set interfaces ae0 unit 3 family ethernet-switching vlan members 3
Configure physical interface xe-2/0/6, and divide it into three logical interfaces (xe-2/0/6.1, xe-2/0/6.2, and xe-2/0/6.3). Map each logical interface to a VLAN.
[edit] user@switch# set interfaces xe-2/0/6 enable user@switch# set interfaces xe-2/0/6 flexible-vlan-tagging user@switch# set interfaces xe-2/0/6 encapsulation flexible-ethernet-services user@switch# set interfaces xe-2/0/6 unit 1 family ethernet-switching interface-mode trunk user@switch# set interfaces xe-2/0/6 unit 1 family ethernet-switching vlan members 1 user@switch# set interfaces xe-2/0/6 unit 2 family ethernet-switching interface-mode trunk user@switch# set interfaces xe-2/0/6 unit 2 family ethernet-switching vlan members 2 user@switch# set interfaces xe-2/0/6 unit 3 family ethernet-switching interface-mode trunk user@switch# set interfaces xe-2/0/6 unit 3 family ethernet-switching vlan members 3
Configure physical interface xe-2/1/0 as a Layer 3 interface, on which you configure ICCP. Specify the interface with the IP address of 203.0.113.2 on PE2 as the ICCP peer to PE1.
[edit] user@switch# set interfaces xe-2/1/0 unit 0 family inet address 203.0.113.1/24 user@switch# set protocols iccp local-ip-addr 203.0.113.1 user@switch# set protocols iccp peer 203.0.113.2 session-establishment-hold-time 600 user@switch# set protocols iccp peer 203.0.113.2 redundancy-group-id-list 2 user@switch# set protocols iccp peer 203.0.113.2 liveness-detection minimum-interval 10000 user@switch# set protocols iccp peer 203.0.113.2 liveness-detection multiplier 3
Configure aggregated Ethernet interface ae1 on interfaces xe-2/1/1 and xe-2/1/2, and configure LACP on ae1. Divide aggregated Ethernet interface ae1 into three logical interfaces (ae1.1, ae1.2, and ae1.3), and map each logical interface to a VLAN. Specify ae1 as the multichassis protection link between PE1 and PE2.
[edit] user@switch# set interfaces xe-2/1/1 gigether-options 802.3ad ae1 user@switch# set interfaces xe-2/1/2 gigether-options 802.3ad ae1 user@switch# set interfaces ae1 flexible-vlan-tagging user@switch# set interfaces ae1 encapsulation flexible-ethernet-services user@switch# set interfaces ae1 aggregated-ether-options lacp active user@switch# set interfaces ae1 unit 1 family ethernet-switching interface-mode trunk user@switch# set interfaces ae1 unit 1 family ethernet-switching vlan members 1 user@switch# set interfaces ae1 unit 2 family ethernet-switching interface-mode trunk user@switch# set interfaces ae1 unit 2 family ethernet-switching vlan members 2 user@switch# set interfaces ae1 unit 3 family ethernet-switching interface-mode trunk user@switch# set interfaces ae1 unit 3 family ethernet-switching vlan members 3 user@switch# set multi-chassis multi-chassis-protection 203.0.113.2 interface ae1
PE1: Configuring EVPN-MPLS
Step-by-Step Procedure
Configure the loopback interface, and the interfaces connected to the other PE devices.
[edit] user@switch# set interfaces lo0 unit 0 family inet address 198.51.100.1/32 primary user@switch# set interfaces xe-2/0/0 unit 0 family inet address 192.0.2.2/24 user@switch# set interfaces xe-2/0/0 unit 0 family mpls user@switch# set interfaces xe-2/0/2 unit 0 family inet address 192.0.2.111/24 user@switch# set interfaces xe-2/0/2 unit 0 family mpls
Configure IRB interfaces irb.1, irb.2, and irb.3.
[edit] user@switch# set interfaces irb unit 1 family inet address 10.2.1.1/24 virtual-gateway-address 10.2.1.254 user@switch# set interfaces irb unit 2 family inet address 10.2.2.1/24 virtual-gateway-address 10.2.2.254 user@switch# set interfaces irb unit 3 family inet address 10.2.3.1/24 virtual-gateway-address 10.2.3.254
Assign a router ID and the autonomous system in which PE1, PE2, and PE3 reside.
[edit] user@switch# set routing-options router-id 198.51.100.1 user@switch# set routing-options autonomous-system 65000
Enable per-packet load-balancing for EVPN routes when EVPN multihoming active-active mode is used.
[edit] user@switch# set routing-options forwarding-table export evpn-pplb user@switch# set policy-options policy-statement evpn-pplb from protocol evpn user@switch# set policy-options policy-statement evpn-pplb then load-balance per-packet
Enable MPLS on interfaces xe-2/0/0.0 and xe-2/0/2.0.
[edit] user@switch# set protocols mpls interface xe-2/0/0.0 user@switch# set protocols mpls interface xe-2/0/2.0
Configure an IBGP overlay that includes PE1, PE2, and PE3.
[edit] user@switch# set protocols bgp group evpn type internal user@switch# set protocols bgp group evpn local-address 198.51.100.1 user@switch# set protocols bgp group evpn family evpn signaling user@switch# set protocols bgp group evpn local-as 65000 user@switch# set protocols bgp group evpn neighbor 198.51.100.2 user@switch# set protocols bgp group evpn neighbor 198.51.100.3
Configure OSPF as the internal routing protocol for EVPN by specifying an area ID and interfaces on which EVPN-MPLS is enabled.
[edit] user@switch# set protocols ospf area 0.0.0.0 interface lo0.0 user@switch# set protocols ospf area 0.0.0.0 interface xe-2/0/0.0 user@switch# set protocols ospf area 0.0.0.0 interface xe-2/0/2.0
Configure the Label Distribution Protocol (LDP) on the loopback interface and the interfaces on which EVPN-MPLS is enabled.
[edit] user@switch# set protocols ldp interface lo0.0 user@switch# set protocols ldp interface xe-2/0/0.0 user@switch# set protocols ldp interface xe-2/0/2.0
Configure virtual switch routing instances for VLAN v1, which is assigned VLAN IDs of 1, 2, and 3, and include the interfaces and other entities associated with the VLAN.
[edit] user@switch# set routing-instances evpn1 instance-type virtual-switch user@switch# set routing-instances evpn1 interface xe-2/0/6.1 user@switch# set routing-instances evpn1 interface ae0.1 user@switch# set routing-instances evpn1 interface ae1.1 user@switch# set routing-instances evpn1 route-distinguisher 1:10 user@switch# set routing-instances evpn1 vrf-target target:1:5 user@switch# set routing-instances evpn1 protocols evpn extended-vlan-list 1 user@switch# set routing-instances evpn1 protocols evpn mclag bgp-peer 198.51.100.2 user@switch# set routing-instances evpn1 switch-options service-id 1 user@switch# set routing-instances evpn1 vlans v1 vlan-id 1 user@switch# set routing-instances evpn1 vlans v1 l3-interface irb.1 user@switch# set routing-instances evpn2 instance-type virtual-switch user@switch# set routing-instances evpn2 interface xe-2/0/6.2 user@switch# set routing-instances evpn2 interface ae0.2 user@switch# set routing-instances evpn2 interface ae1.2 user@switch# set routing-instances evpn2 route-distinguisher 1:20 user@switch# set routing-instances evpn2 vrf-target target:1:6 user@switch# set routing-instances evpn2 protocols evpn extended-vlan-list 2 user@switch# set routing-instances evpn2 protocols evpn mclag bgp-peer 198.51.100.2 user@switch# set routing-instances evpn2 switch-options service-id 2 user@switch# set routing-instances evpn2 vlans v1 vlan-id 2 user@switch# set routing-instances evpn2 vlans v1 l3-interface irb.2 user@switch# set routing-instances evpn3 instance-type virtual-switch user@switch# set routing-instances evpn3 interface xe-2/0/6.3 user@switch# set routing-instances evpn3 interface ae0.3 user@switch# set routing-instances evpn3 interface ae1.3 user@switch# set routing-instances evpn3 route-distinguisher 1:30 user@switch# set routing-instances evpn3 vrf-target target:1:7 user@switch# set routing-instances evpn3 protocols evpn extended-vlan-list 3 user@switch# set routing-instances evpn3 protocols evpn mclag bgp-peer 198.51.100.2 user@switch# set routing-instances evpn3 switch-options service-id 3 user@switch# set routing-instances evpn3 vlans v1 vlan-id 3 user@switch# set routing-instances evpn3 vlans v1 l3-interface irb.3
PE2: Configuring MC-LAG
Step-by-Step Procedure
Set the number of aggregated Ethernet interfaces on PE2.
[edit] user@switch# set chassis aggregated-devices ethernet device-count 3
Configure aggregated Ethernet interface ae0 on interface xe-2/0/1, and configure LACP and MC-LAG on ae0. Divide aggregated Ethernet interface ae0 into three logical interfaces (ae0.1, ae0.2, and ae0.3). For each logical interface, specify an ESI, place the logical interface is in MC-LAG active-active mode, and map the logical interface to a VLAN.
[edit] user@switch# set interfaces xe-2/0/1 gigether-options 802.3ad ae0 user@switch# set interfaces ae0 flexible-vlan-tagging user@switch# set interfaces ae0 encapsulation flexible-ethernet-services user@switch# set interfaces ae0 aggregated-ether-options lacp active user@switch# set interfaces ae0 aggregated-ether-options lacp periodic fast user@switch# set interfaces ae0 aggregated-ether-options lacp system-id 00:00:11:11:11:11 user@switch# set interfaces ae0 aggregated-ether-options lacp admin-key 1 user@switch# set interfaces ae0 aggregated-ether-options mc-ae mc-ae-id 1 user@switch# set interfaces ae0 aggregated-ether-options mc-ae redundancy-group 2 user@switch# set interfaces ae0 aggregated-ether-options mc-ae chassis-id 1 user@switch# set interfaces ae0 aggregated-ether-options mc-ae mode active-active user@switch# set interfaces ae0 aggregated-ether-options mc-ae status-control standby user@switch# set interfaces ae0 unit 1 esi 00:11:22:33:44:55:66:77:88:99 user@switch# set interfaces ae0 unit 1 esi all-active user@switch# set interfaces ae0 unit 1 family ethernet-switching interface-mode trunk user@switch# set interfaces ae0 unit 1 family ethernet-switching vlan members 1 user@switch# set interfaces ae0 unit 2 esi 00:11:11:11:11:11:11:11:11:11 user@switch# set interfaces ae0 unit 2 esi all-active user@switch# set interfaces ae0 unit 2 family ethernet-switching interface-mode trunk user@switch# set interfaces ae0 unit 2 family ethernet-switching vlan members 2 user@switch# set interfaces ae0 unit 3 esi 00:11:22:22:22:22:22:22:22:22 user@switch# set interfaces ae0 unit 3 esi all-active user@switch# set interfaces ae0 unit 3 family ethernet-switching interface-mode trunk user@switch# set interfaces ae0 unit 3 family ethernet-switching vlan members 3
Configure physical interface xe-2/0/6, and divide it into three logical interfaces (xe-2/0/6.1, xe-2/0/6.2, and xe-2/0/6.3). Map each logical interface to a VLAN.
[edit] set interfaces xe-2/0/6 enable set interfaces xe-2/0/6 flexible-vlan-tagging set interfaces xe-2/0/6 encapsulation flexible-ethernet-services set interfaces xe-2/0/6 unit 1 family ethernet-switching interface-mode trunk set interfaces xe-2/0/6 unit 1 family ethernet-switching vlan members 1 set interfaces xe-2/0/6 unit 2 family ethernet-switching interface-mode trunk set interfaces xe-2/0/6 unit 2 family ethernet-switching vlan members 2 set interfaces xe-2/0/6 unit 3 family ethernet-switching interface-mode trunk set interfaces xe-2/0/6 unit 3 family ethernet-switching vlan members 3
Configure physical interface xe-2/1/0 as a Layer 3 interface, on which you configure ICCP. Specify the interface with the IP address of 203.0.113.1 on PE1 as the ICCP peer to PE2.
[edit] set interfaces xe-2/1/0 unit 0 family inet address 203.0.113.2/24 set protocols iccp local-ip-addr 203.0.113.2 set protocols iccp peer 203.0.113.1 session-establishment-hold-time 600 set protocols iccp peer 203.0.113.1 redundancy-group-id-list 2 set protocols iccp peer 203.0.113.1 liveness-detection minimum-interval 10000 set protocols iccp peer 203.0.113.1 liveness-detection multiplier 3
Configure aggregated Ethernet interface ae1 on interfaces xe-2/1/1 and xe-2/1/2, and configure LACP on ae1. Divide aggregated Ethernet interface ae1 into three logical interfaces (ae1.1, ae1.2, and ae1.3), and map each logical interface to a VLAN. Specify ae1 as the multichassis protection link between PE1 and PE2.
[edit] set interfaces xe-2/1/1 gigether-options 802.3ad ae1 set interfaces xe-2/1/2 gigether-options 802.3ad ae1 set interfaces ae1 flexible-vlan-tagging set interfaces ae1 encapsulation flexible-ethernet-services set interfaces ae1 aggregated-ether-options lacp active set interfaces ae1 unit 1 family ethernet-switching interface-mode trunk set interfaces ae1 unit 1 family ethernet-switching vlan members 1 set interfaces ae1 unit 2 family ethernet-switching interface-mode trunk set interfaces ae1 unit 2 family ethernet-switching vlan members 2 set interfaces ae1 unit 3 family ethernet-switching interface-mode trunk set interfaces ae1 unit 3 family ethernet-switching vlan members 3 set multi-chassis multi-chassis-protection 203.0.113.1 interface ae1
PE2: Configuring EVPN-MPLS
Step-by-Step Procedure
Configure the loopback interface, and the interfaces connected to the other PE devices.
[edit] user@switch# set interfaces lo0 unit 0 family inet address 198.51.100.2/32 primary user@switch# set interfaces xe-2/0/0 unit 0 family inet address 192.0.2.222/24 user@switch# set interfaces xe-2/0/0 unit 0 family mpls user@switch# set interfaces xe-2/0/2 unit 0 family inet address 192.0.2.22/24 user@switch# set interfaces xe-2/0/2 unit 0 family mpls
Configure IRB interfaces irb.1, irb.2, and irb.3.
[edit] user@switch# set interfaces irb unit 1 family inet address 10.2.1.2/24 virtual-gateway-address 10.2.1.254 user@switch# set interfaces irb unit 2 family inet address 10.2.2.2/24 virtual-gateway-address 10.2.2.254 user@switch# set interfaces irb unit 3 family inet address 10.2.3.2/24 virtual-gateway-address 10.2.3.254
Assign a router ID and the autonomous system in which PE1, PE2, and PE3 reside.
[edit] user@switch# set routing-options router-id 198.51.100.2 user@switch# set routing-options autonomous-system 65000
Enable per-packet load-balancing for EVPN routes when EVPN multihoming active-active mode is used.
[edit] user@switch# set routing-options forwarding-table export evpn-pplb user@switch# set policy-options policy-statement evpn-pplb from protocol evpn user@switch# set policy-options policy-statement evpn-pplb then load-balance per-packet
Enable MPLS on interfaces xe-2/0/0.0 and xe-2/0/2.0.
[edit] user@switch# set protocols mpls interface xe-2/0/0.0 user@switch# set protocols mpls interface xe-2/0/2.0
Configure an IBGP overlay that includes PE1, PE2, and PE3.
[edit] user@switch# set protocols bgp group evpn type internal user@switch# set protocols bgp group evpn local-address 198.51.100.2 user@switch# set protocols bgp group evpn family evpn signaling user@switch# set protocols bgp group evpn local-as 65000 user@switch# set protocols bgp group evpn neighbor 198.51.100.1 user@switch# set protocols bgp group evpn neighbor 198.51.100.3
Configure OSPF as the internal routing protocol for EVPN by specifying an area ID and interfaces on which EVPN-MPLS is enabled.
[edit] user@switch# set protocols ospf area 0.0.0.0 interface lo0.0 user@switch# set protocols ospf area 0.0.0.0 interface xe-2/0/0.0 user@switch# set protocols ospf area 0.0.0.0 interface xe-2/0/2.0
Configure the Label Distribution Protocol (LDP) on the loopback interface and the interfaces on which EVPN-MPLS is enabled.
[edit] user@switch# set protocols ldp interface lo0.0 user@switch# set protocols ldp interface xe-2/0/0.0 user@switch# set protocols ldp interface xe-2/0/2.0
Configure virtual switch routing instances for VLAN v1, which is assigned VLAN IDs of 1, 2, and 3, and include the interfaces and other entities associated with the VLAN.
[edit] user@switch# set routing-instances evpn1 instance-type virtual-switch user@switch# set routing-instances evpn1 interface xe-2/0/6.1 user@switch# set routing-instances evpn1 interface ae0.1 user@switch# set routing-instances evpn1 interface ae1.1 user@switch# set routing-instances evpn1 route-distinguisher 1:11 user@switch# set routing-instances evpn1 vrf-target target:1:5 user@switch# set routing-instances evpn1 protocols evpn extended-vlan-list 1 user@switch# set routing-instances evpn1 protocols evpn mclag bgp-peer 198.51.100.1 user@switch# set routing-instances evpn1 switch-options service-id 1 user@switch# set routing-instances evpn1 vlans v1 vlan-id 1 user@switch# set routing-instances evpn1 vlans v1 l3-interface irb.1 user@switch# set routing-instances evpn2 instance-type virtual-switch user@switch# set routing-instances evpn2 interface xe-2/0/6.2 user@switch# set routing-instances evpn2 interface ae0.2 user@switch# set routing-instances evpn2 interface ae1.2 user@switch# set routing-instances evpn2 route-distinguisher 1:21 user@switch# set routing-instances evpn2 vrf-target target:1:6 user@switch# set routing-instances evpn2 protocols evpn extended-vlan-list 2 user@switch# set routing-instances evpn2 protocols evpn mclag bgp-peer 198.51.100.1 user@switch# set routing-instances evpn2 switch-options service-id 2 user@switch# set routing-instances evpn2 vlans v1 vlan-id 2 user@switch# set routing-instances evpn2 vlans v1 l3-interface irb.2 user@switch# set routing-instances evpn3 instance-type virtual-switch user@switch# set routing-instances evpn3 interface xe-2/0/6.3 user@switch# set routing-instances evpn3 interface ae0.3 user@switch# set routing-instances evpn3 interface ae1.3 user@switch# set routing-instances evpn3 route-distinguisher 1:31 user@switch# set routing-instances evpn3 vrf-target target:1:7 user@switch# set routing-instances evpn3 protocols evpn extended-vlan-list 3 user@switch# set routing-instances evpn3 protocols evpn mclag bgp-peer 198.51.100.1 user@switch# set routing-instances evpn3 switch-options service-id 3 user@switch# set routing-instances evpn3 vlans v1 vlan-id 3 user@switch# set routing-instances evpn3 vlans v1 l3-interface irb.3
PE3 Configuration
CLI Quick Configuration
PE3: EVPN-MPLS Configuration
set interfaces lo0 unit 0 family inet address 198.51.100.3/32 primary set interfaces xe-2/0/2 unit 0 family inet address 192.0.2.1/24 set interfaces xe-2/0/2 unit 0 family mpls set interfaces xe-2/0/3 unit 0 family inet address 192.0.2.11/24 set interfaces xe-2/0/3 unit 0 family mpls set interfaces xe-2/0/6 enable set interfaces xe-2/0/6 flexible-vlan-tagging set interfaces xe-2/0/6 encapsulation flexible-ethernet-services set interfaces xe-2/0/6 unit 1 family ethernet-switching interface-mode trunk set interfaces xe-2/0/6 unit 1 family ethernet-switching vlan members 1 set interfaces xe-2/0/6 unit 2 family ethernet-switching interface-mode trunk set interfaces xe-2/0/6 unit 2 family ethernet-switching vlan members 2 set interfaces xe-2/0/6 unit 3 family ethernet-switching interface-mode trunk set interfaces xe-2/0/6 unit 3 family ethernet-switching vlan members 3 set interfaces irb unit 1 family inet address 10.2.1.3/24 virtual-gateway-address 10.2.1.254 set interfaces irb unit 2 family inet address 10.2.2.3/24 virtual-gateway-address 10.2.2.254 set interfaces irb unit 3 family inet address 10.2.3.3/24 virtual-gateway-address 10.2.3.254 set routing-options router-id 198.51.100.3 set routing-options autonomous-system 65000 set routing-options forwarding-table export evpn-pplb set protocols mpls interface xe-2/0/2.0 set protocols mpls interface xe-2/0/3.0 set protocols bgp group evpn type internal set protocols bgp group evpn local-address 198.51.100.3 set protocols bgp group evpn family evpn signaling set protocols bgp group evpn local-as 65000 set protocols bgp group evpn neighbor 198.51.100.1 set protocols bgp group evpn neighbor 198.51.100.2 set protocols ospf area 0.0.0.0 interface lo0.0 set protocols ospf area 0.0.0.0 interface xe-2/0/2.0 set protocols ospf area 0.0.0.0 interface xe-2/0/3.0 set protocols ldp interface lo0.0 set protocols ldp interface xe-2/0/2.0 set protocols ldp interface xe-2/0/3.0 set policy-options policy-statement evpn-pplb from protocol evpn set policy-options policy-statement evpn-pplb then load-balance per-packet set routing-instances evpn1 instance-type virtual-switch set routing-instances evpn1 interface xe-2/0/6.1 set routing-instances evpn1 route-distinguisher 1:12 set routing-instances evpn1 vrf-target target:1:5 set routing-instances evpn1 protocols evpn extended-vlan-list 1 set routing-instances evpn1 switch-options service-id 1 set routing-instances evpn1 vlans v1 vlan-id 1 set routing-instances evpn1 vlans v1 l3-interface irb.1 set routing-instances evpn2 instance-type virtual-switch set routing-instances evpn2 interface xe-2/0/6.2 set routing-instances evpn2 route-distinguisher 1:22 set routing-instances evpn2 vrf-target target:1:6 set routing-instances evpn2 protocols evpn extended-vlan-list 2 set routing-instances evpn2 switch-options service-id 2 set routing-instances evpn2 vlans v1 vlan-id 2 set routing-instances evpn2 vlans v1 l3-interface irb.2 set routing-instances evpn3 instance-type virtual-switch set routing-instances evpn3 interface xe-2/0/6.3 set routing-instances evpn3 route-distinguisher 1:32 set routing-instances evpn3 vrf-target target:1:7 set routing-instances evpn3 protocols evpn extended-vlan-list 3 set routing-instances evpn3 switch-options service-id 3 set routing-instances evpn3 vlans v1 vlan-id 3 set routing-instances evpn3 vlans v1 l3-interface irb.3
PE3: Configuring EVPN-MPLS
Step-by-Step Procedure
Configure the loopback interface, and the interfaces connected to the other PE devices.
[edit] user@switch# set interfaces lo0 unit 0 family inet address 198.51.100.3/32 primary user@switch# set interfaces xe-2/0/2 unit 0 family inet address 192.0.2.1/24 user@switch# set interfaces xe-2/0/2 unit 0 family mpls user@switch# set interfaces xe-2/0/3 unit 0 family inet address 192.0.2.11/24 user@switch# set interfaces xe-2/0/3 unit 0 family mpls
Configure interface xe-2/0/6, which is connected to the host.
[edit] user@switch# set interfaces xe-2/0/6 enable user@switch# set interfaces xe-2/0/6 flexible-vlan-tagging user@switch# set interfaces xe-2/0/6 encapsulation flexible-ethernet-services user@switch# set interfaces xe-2/0/6 unit 1 family ethernet-switching interface-mode trunk user@switch# set interfaces xe-2/0/6 unit 1 family ethernet-switching vlan members 1 user@switch# set interfaces xe-2/0/6 unit 2 family ethernet-switching interface-mode trunk user@switch# set interfaces xe-2/0/6 unit 2 family ethernet-switching vlan members 2 user@switch# set interfaces xe-2/0/6 unit 3 family ethernet-switching interface-mode trunk user@switch# set interfaces xe-2/0/6 unit 3 family ethernet-switching vlan members 3
Configure IRB interfaces irb.1, irb.2, and irb.3.
[edit] user@switch# set interfaces irb unit 1 family inet address 10.2.1.3/24 virtual-gateway-address 10.2.1.254 user@switch# set interfaces irb unit 2 family inet address 10.2.2.3/24 virtual-gateway-address 10.2.2.254 user@switch# set interfaces irb unit 3 family inet address 10.2.3.3/24 virtual-gateway-address 10.2.3.254
Assign a router ID and the autonomous system in which PE1, PE2, and PE3 reside.
[edit] user@switch# set routing-options router-id 198.51.100.3 user@switch# set routing-options autonomous-system 65000
Enable per-packet load-balancing for EVPN routes when EVPN multihoming active-active mode is used.
[edit] user@switch# set routing-options forwarding-table export evpn-pplb user@switch# set policy-options policy-statement evpn-pplb from protocol evpn user@switch# set policy-options policy-statement evpn-pplb then load-balance per-packet
Enable MPLS on interfaces xe-2/0/2.0 and xe-2/0/3.0.
[edit] user@switch# set protocols mpls interface xe-2/0/2.0 user@switch# set protocols mpls interface xe-2/0/3.0
Configure an IBGP overlay that includes PE1, PE2, and PE3.
[edit] user@switch# set protocols bgp group evpn type internal user@switch# set protocols bgp group evpn local-address 198.51.100.3 user@switch# set protocols bgp group evpn family evpn signaling user@switch# set protocols bgp group evpn local-as 65000 user@switch# set protocols bgp group evpn neighbor 198.51.100.1 user@switch# set protocols bgp group evpn neighbor 198.51.100.2
Configure OSPF as the internal routing protocol for EVPN by specifying an area ID and interfaces on which EVPN-MPLS is enabled.
[edit] user@switch# set protocols ospf area 0.0.0.0 interface lo0.0 user@switch# set protocols ospf area 0.0.0.0 interface xe-2/0/2.0 user@switch# set protocols ospf area 0.0.0.0 interface xe-2/0/3.0
Configure the LDP on the loopback interface and the interfaces on which EVPN-MPLS is enabled.
[edit] user@switch# set protocols ldp interface lo0.0 user@switch# set protocols ldp interface xe-2/0/2.0 user@switch# set protocols ldp interface xe-2/0/3.0
Configure virtual switch routing instances for VLAN v1, which is assigned VLAN IDs of 1, 2, and 3, and include the interfaces and other entities associated with the VLAN.
[edit] user@switch# set routing-instances evpn1 instance-type virtual-switch user@switch# set routing-instances evpn1 interface xe-2/0/6.1 user@switch# set routing-instances evpn1 route-distinguisher 1:12 user@switch# set routing-instances evpn1 vrf-target target:1:5 user@switch# set routing-instances evpn1 protocols evpn extended-vlan-list 1 user@switch# set routing-instances evpn1 switch-options service-id 1 user@switch# set routing-instances evpn1 vlans v1 vlan-id 1 user@switch# set routing-instances evpn1 vlans v1 l3-interface irb.1 user@switch# set routing-instances evpn2 instance-type virtual-switch user@switch# set routing-instances evpn2 interface xe-2/0/6.2 user@switch# set routing-instances evpn2 route-distinguisher 1:22 user@switch# set routing-instances evpn2 vrf-target target:1:6 user@switch# set routing-instances evpn2 protocols evpn extended-vlan-list 2 user@switch# set routing-instances evpn2 switch-options service-id 2 user@switch# set routing-instances evpn2 vlans v1 vlan-id 2 user@switch# set routing-instances evpn2 vlans v1 l3-interface irb.2 user@switch# set routing-instances evpn3 instance-type virtual-switch user@switch# set routing-instances evpn3 interface xe-2/0/6.3 user@switch# set routing-instances evpn3 route-distinguisher 1:32 user@switch# set routing-instances evpn3 vrf-target target:1:7 user@switch# set routing-instances evpn3 protocols evpn extended-vlan-list 3 user@switch# set routing-instances evpn3 switch-options service-id 3 user@switch# set routing-instances evpn3 vlans v1 vlan-id 3 user@switch# set routing-instances evpn3 vlans v1 l3-interface irb.3
