Create an SQS Queue and Configure S3 ObjectCreated Notifications
Before you can add a log source in JSA, you must create an SQS queue and configure S3 ObjectCreated notifications in the AWS Management Console when using the Amazon AWS S3 REST API protocol.
Complete the following procedures:
Finding the S3 Bucket that contains the Data that you want to Collect
You must find and note the region for S3 bucket that contains the data that you want to collect.
- Log in to the AWS Management Console as an administrator.
- Click Services, and then go to S3.
- From the AWS Region column in the Buckets list, note the region where the bucket that you want to collect data from is located. You need the region for the Region Name parameter value when you add a log source in JSA.
- Enable the check box beside the bucket name, and then from the panel that opens to the right, click Copy Bucket ARN to copy the value to the clipboard. Save this value or leave it on the clipboard. You need this value when you set up SQS queue permissions.
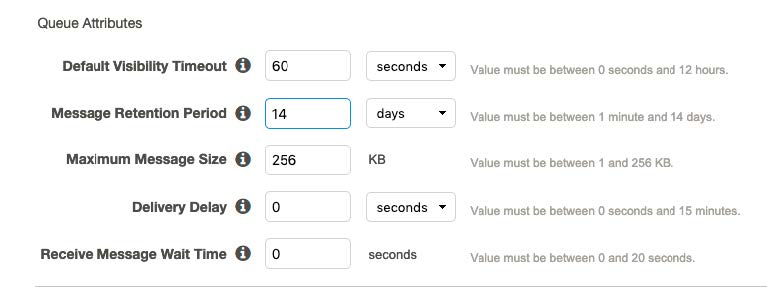
Creating the SQS Queue that is used to Receive ObjectCreated Notifications
You must create an SQS queue and configure S3 ObjectCreated notifications in the AWS Management Console when using the Amazon AWS REST API protocol.
You must complete Finding the S3 Bucket that contains the data that you want to collect. The SQS Queue must be in the same region as the AWS S3 bucket that the queue is collecting from.
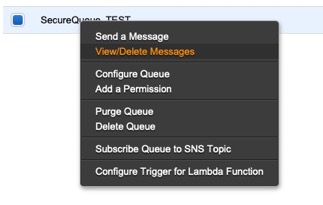
Setting up SQS Queue Permissions
You must set up SQS queue permissions for users to access the queue.
You must complete Creating the SQS Queue that is used to Receive ObjectCreated Notifications.
You can set the SQS queue permissions by using either the Permissions Editor or a JSON policy document.
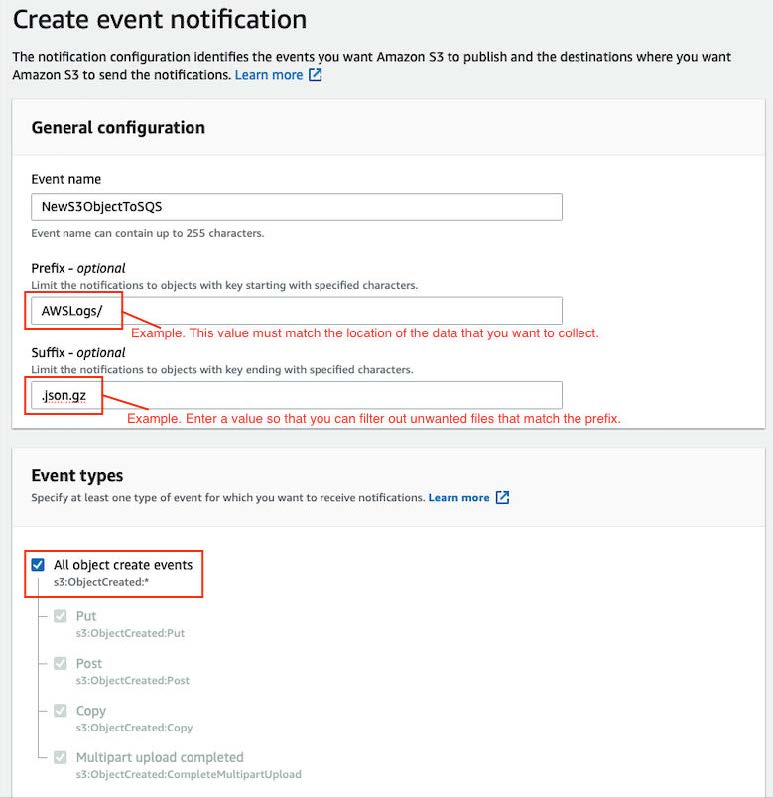
Creating ObjectCreated Notifications
Configure ObjectCreated notifications for the folders that you want to monitor in the bucket.