JSA Vulnerability Manager Deployments
Locate and manage the vulnerabilities in your network by deploying JSA Vulnerability Manager.
JSA Vulnerability Manager discovers vulnerabilities on your network devices, applications, and software adds context to the vulnerabilities, prioritizes asset risk in your network, and supports the remediation of discovered vulnerabilities.
You can integrate JSA Risk Manager for added protection, which provides network topology, active attack paths and high-risk assets risk-score adjustment on assets based on policy compliance. JSA Vulnerability Manager and JSA Risk Manager are combined into one offering and both are enabled through a single base license.
Depending on the product that you install, and whether you upgrade JSA or install a new system, the Vulnerabilities tab might not be displayed. Access JSA Vulnerability Manager by using the Vulnerabilities tab. If you install JSA, the Vulnerabilities tab is enabled by default with a temporary license key. If you install Log Manager, the Vulnerabilities tab is not enabled. You can use the Try it Out option to try out JSA Vulnerability Manager for 30 days. You can purchase the license for JSA Vulnerability Manager separately and enable it by using a license key. For more information about upgrading, see the Upgrading Juniper Secure Analytics to 7.5.01 Guide.
JSA Vulnerability Manager Components
The following information describes the JSA Vulnerability Manager Processor.
The scan processor is responsible for the scheduling and managing scans, and delegating work to the scanners that might be distributed throughout your network.
You can have only one scan processor in a JSA deployment.
When you install and license JSA Vulnerability Manager on an All-in-One system, a vulnerability processor is automatically deployed on your JSA console and includes a scanning component.
The vulnerability processor provides a scanning component by default. If required, you can move the vulnerability processor to a different managed host in your deployment.
If you add a Vulnerability Processor managed host appliance, and JSA Vulnerability Manager is used for the first time, then the scan processor is assigned to the Vulnerability Processor managed host appliance.
The scanning processor is governed by the processing license, which determines the maximum number of assets that can be processed by JSA Vulnerability Manager.
The scan processor can run on the JSA console or a managed host.
The following information describes the JSA Vulnerability Manager scanner.
You can deploy a scanner on a virtual machine or as software only.
You can deploy a JSA Vulnerability Manager scanner dedicated scanner appliance, which is a Vulnerability Scanner appliance.
You can deploy a scanner on a JSA console or on the following managed hosts: Flow Processor, Flow Processor Event Collector, Event Processor, or Data Node.
The number of assets that you can scan with a scanner is determined by the scanner capacity and is not impacted by licensing.
Components and Scan Process
Scan jobs are completed by a processor and a scanner component. The following diagram shows the scan components and the processes that run.
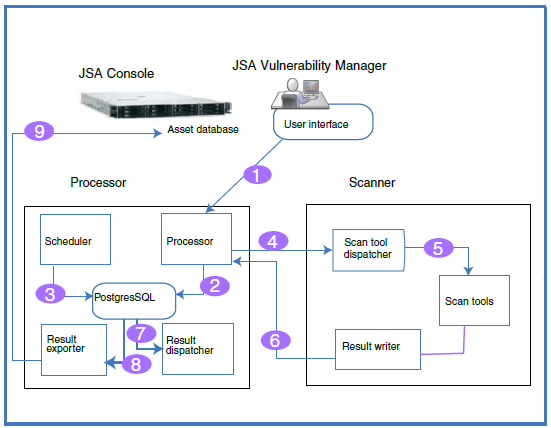
The following list describes the steps in the scan process:
You create a scan job by specifying parameters such as IP addresses of assets, type of scan, and required credentials for authenticated scans.
The scan job is accepted by the processor, logged, and added to the database along with scheduling information to determine when the job runs.
The scheduler component manages the scheduling of scans. When the scheduler initiates a scan, it determines the list of tools that are required and queues them for invocation, and then the tools are assigned to the relevant scanner.
Scanners poll the scan processor continuously for scan tools that it must run by sending a unique scanner ID. When the scheduler has queued tools that are relevant to the specific scanner the tools are sent to the scanner for invocation.
JSA Vulnerability Manager uses an attack tree methodology to manage scans and to determine which tools are launched. The phases are: asset discovery, port/service discovery, service scan, and patch scan.
The dispatcher runs and manages each scan tool in the list. For each tool that is run, the dispatcher sends a message to the processor that indicates when a scan tool starts and finishes.
The output from the scan tool is read by the result writer, which then passes these results back to the processor.
The result dispatcher processes the raw results from the scan tools and records them into the Postgres database.
The result exporter finds completed scans in the processor database and exports the results to the JSA console.
The exported results are added to the JSA database where users can view and manage the scan results.
All-in-one Deployment
You can run JSA Vulnerability Manager from an All-in-one system, where the scanning and processing functions are on the Console. The following information describes what you can do with a basic setup:
Scan up to 255 assets.
Unlimited discovery scans.
Use hosted scanner for DMZ scanning.
Manage scan data from third-party scanners that are integrated with JSA.
Deploy a scanner on any managed host.
Deploy unlimited stand-alone software or virtual scanners.
Expanding a Deployment
As your deployment grows, you might need to move the processing function off the JSA console to free up resources, and you might want to deploy scanners closer to your assets.
The following list describes reasons to add scanners to your deployment:
To scan assets in a different geographic region than the JSA Vulnerability Manager processor.
If you want to scan many assets concurrently within a short time frame.
You might want to add a scanner to avoid scanning through a firewall that is a log source. You might also consider adding the scanner directly to the network by adding an interface on the scanner host that by-passes the firewall.
The following diagram shows a scanning deployment with external scanning and scanners deployed on managed hosts.
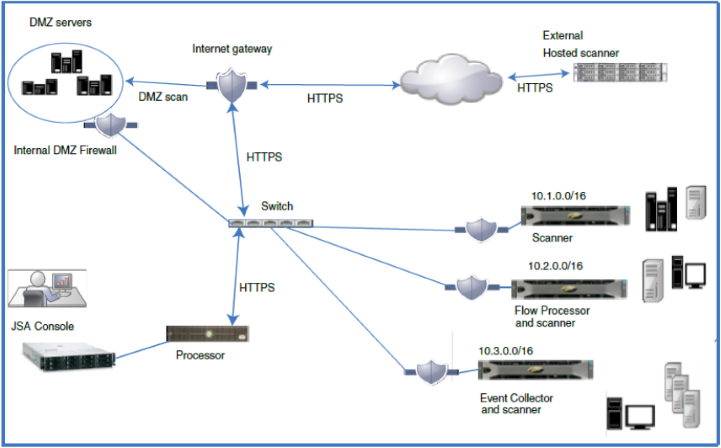
DMZ Hosted Scanner
A hosted scanner scans your DMZ from the Internet by using your public IP address. If you want to scan the assets in the DMZ for vulnerabilities, you do not need to deploy a scanner in your DMZ. You must configure JSA Vulnerability Manager with a hosted IBM scanner that is located outside your network. For more information, see the Juniper Secure Analytics Vulnerability Manager User Guide.
JSA Vulnerability Manager Integrations
JSA Vulnerability Manager integrates with HCL BigFix to help you filter and prioritize the vulnerabilities that can be fixed. BigFix provides shared visibility and control between IT operations and security. BigFix applies Fixlets to high priority vulnerabilities that are identified and sent by JSA Vulnerability Manager to BigFix. Fixlets are packages that you deploy to your assets or endpoints to remediate specific vulnerabilities.
JSA Vulnerability Manager integrates with IBM Security SiteProtector to help direct intrusion prevention system (IPS) policy. When you configure IBM Security SiteProtector, the vulnerabilities that are detected by scans are automatically forwarded to IBM Security SiteProtector. IBM Security SiteProtector receives vulnerability data from JSA Vulnerability Manager scans that are run only after the integration is configured. Connecting to IBM Security SiteProtector.
Third-party Scanners
JSA Vulnerability Manager delivers an effective vulnerability management platform, regardless of the source of the scan data. JSA Vulnerability Manager integrates seamlessly with third-party scanners such as Nessus, nCircle, and Rapid 7.
You require JSA Vulnerability Manager scanning to get the following options:
Event driven and on-demand scanning
Asset database and watchlist based scanning
Scanning from existing JSA appliances and managed hosts
Detection of newly published vulnerabilities that are not present in any scan results
You require JSA Risk Manager to get the following options:
Asset, vulnerability, and traffic-based vulnerability management
Adjusted vulnerability scores and context aware risk scoring.
JSA Risk Manager and JSA Vulnerability Manager
Enhance your network security by integrating JSA Risk Manager with JSA Vulnerability Manager. Data sources, such as scan data, enable JSA Risk Manager to identify security, policy, and compliance risks in your network and calculate the probability of risk exploitation.
JSA Vulnerability Manager and JSA Risk Manager are combined into one offering and both are enabled through a single base license.
Add a JSA Risk Manager appliance to get the following capabilities:
Compliance assessment
Risk policies that are based on vulnerability data and risk scores that help you quickly identify high-risk vulnerabilities.
Visibility into potential exploit paths from potential threats and untrusted networks through the network topology view.
Risk policy-based filtering.
Topology visualization
False positives reduction in vulnerability assessments.
Visibility into what vulnerabilities are blocked by firewalls and Intrusion Prevention Systems (IPS).
JSA Risk Manager Appliance
Install JSA Risk Manager separately on a JSA Risk Manager appliance.
You must install JSA Console before you set up and configure the JSA Risk Manager appliance. It is a good practice to install JSA and JSA Risk Manager on the same network switch.
You require only one JSA Risk Manager appliance per deployment.
The following diagram shows a deployment that has a scanner and JSA Risk Manager.
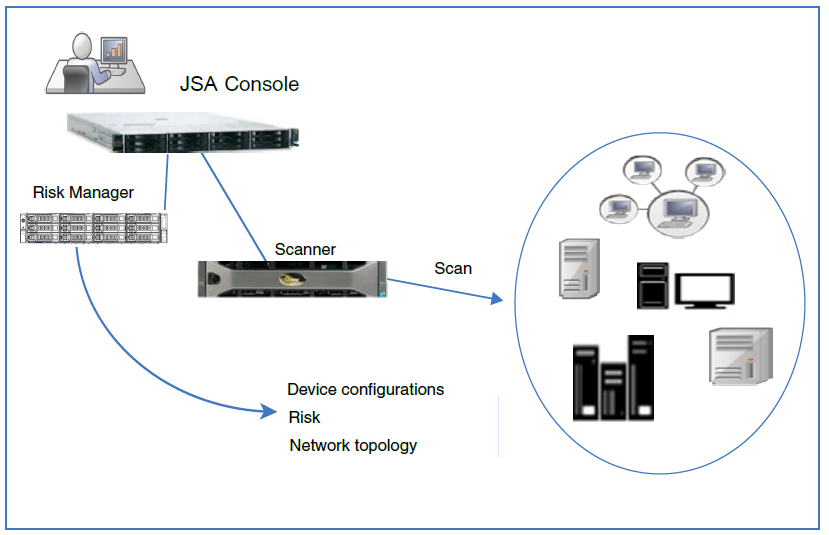
Use Risk Manager to complete the following tasks:
Centralized risk management.
View and filter your network topology
Import and compare device configurations
View connections between network devices.
Search firewall rules.
View existing rules and the event count for triggered rules.
Search devices and paths
Query network connections
Simulate the possible outcomes of updating device configurations.
Monitor and audit your network to ensure compliance.
Simulate threats or attacks against a virtual model.
Search for vulnerabilities.
