NGFW Deployment Architecture
This topic describes the next-generation firewall (NGFW) deployment architecture for standalone NGFW using SRX Series Security Gateways.
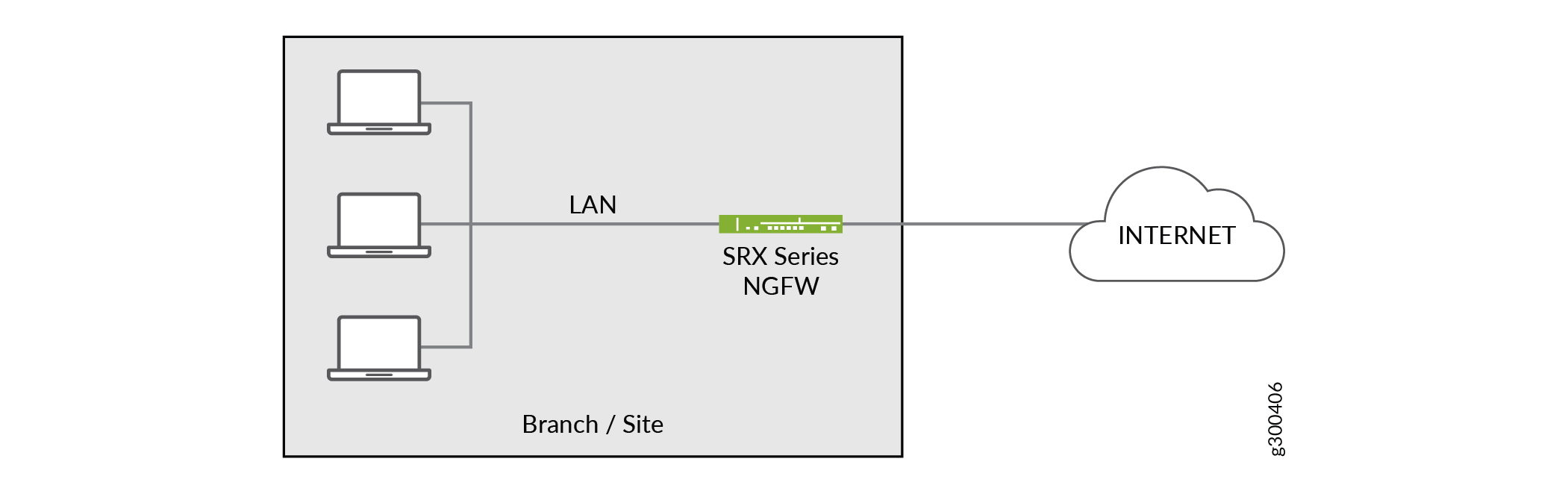
NGFW Architecture
The NGFW architecture offers strong security services for remote sites, along with WAN connectivity. When you use an SRX Series Firewall at an on-premises spoke site as a standalone NGFW, the WAN routing functions are performed on the SRX Series Firewall itself. This architecture allows the SRX Series Firewall to perform all of its built-in security functions (such as firewall and NAT) while providing visibility into the LANs that exist at your spoke sites. Figure 1 shows an SRX Series Firewall connected to both the WAN and an onsite LAN.
As mentioned previously, an NGFW site can exist on its own or be extended later with the addition of EX Series LAN switches or Virtual Chassis at any time after provisioning and deployment.
NGFW Devices
SRX Series Firewalls can be used as standalone firewalls, managed by CSO in the customer LAN. CSO supports the use of SRX300, SRX320, SRX340, SRX345, SRX550M, SRX1500, SRX4100, and SRX4200 Security Gateways as well as the vSRX Virtual Firewall for this purpose. In this next-generation firewall (NGFW) scenario, the SRX acts as a CPE device but provides no site–to–site or site–to–hub communications as with an SD-WAN solution.
NGFW Deployment Usage Notes
With an NGFW deployment you can:
Enable WAN connectivity for sites—When you provision NGFW service capabilities for a tenant, any site belonging to that tenant can use the NGFW device as its WAN link back to CSO.
Enable automatic LAN connectivity—The NGFW device can provide addressing for a connected LAN by using a built-in DHCP server.
Create custom application signatures in firewall policies—CSO supports custom application signatures in firewall policies, in addition to the existing support in SD-WAN policies.
Create customized IPS signatures, static groups, and dynamic groups—You can create, modify, or delete customized intrusion prevention system (IPS) signatures, IPS signature static groups, and IPS signature dynamic groups. In addition, you can clone predefined or customized IPS signatures, static groups, and dynamic groups. You can then use the IPS signatures, static groups, and dynamic groups in an IPS profile that can contain one or more IPS or exempt rules.
Import policy configurations—CSO supports the import of policy configurations from next-generation firewall devices. The following features are supported:
Manage next-generation firewall sites for enterprise customers with brown field deployments.
Discover existing policy configuration while onboarding NGFW devices (without enabling ZTP).
Import policy configurations from Firewall and NAT policy pages.
Deploy policies after import into CSO.
You enable an NGFW deployment in CSO by using the Customer Portal to add an NGFW site. A tenant assigned to the NGFW site must have the NGFW service available. To add the NGFW service, a tenant administrator includes the NGFW service in the tenant configuration during the onboarding process.
