vCenter Virtual Infra
VMware vSphere Integration Overview
With Apstra vCenter integration, you have VM visibility of your virtualized environments. This feature helps to troubleshoot various VM connectivity issues. Inconsistencies between virtual network settings (VMware Port Groups) and physical networks (Apstra Virtual Networks) that might affect VM connectivity are flagged.
To accomplish this, the Apstra software identifies the ESX/ESXi hosts and thereby the VMs connected to Apstra-managed leaf switches. LLDP information transmitted by the ESX/ESXi hosts is used to associate host interfaces with leaf interfaces. For this feature to work, LLDP transmit must be enabled on the VMware distributed virtual switch.
The Apstra software also connects to vCenter to collect information about VMs, ESX/ESXi hosts, port groups and VDS. Apstra extensible telemetry collectors collect this information. The collector runs in an offbox agent and uses pyVmomi to connect to vCenter. On first connect, it downloads all of the necessary information and thereafter polls vCenter every 60 seconds for new updates. The collector updates the discovered data into the Apstra Graph Datastore allowing VM queries and alerts to be raised on physical/virtual network mismatch.
Supported Versions
Apstra Version 4.2.2 & 4.2.1
- vCenter Server/vSphere 7.0U1
Apstra Versions 4.2.0
VMware vSphere/vCenter integration is available for the following versions of VMware:
- vCenter Server/vSphere 7.0U1
- vCenter Server/vSphere 6.7
- vCenter Server/vSphere 6.5
The specific test and qualification for version 7.0 is three vCenter servers on three different routing zones: zone 1 supports 3000 VMs, zone 2 supports 1000 VMs, and zone 3 supports 1000 VMs. We support vCenter managed data center stretched clusters. vCenter segregation is based on workload, not location.
Limitations
vCenter integration does not support DVS port group with VLAN type Trunking.
Enable vCenter Integration
You only need Read permissions to enable vSphere Integration.
When you are ready to deploy, commit the changes from the Uncommitted tab.
VM Visibility
When Apstra software manages virtual infra, you can query VMs by name. From the blueprint, navigate to Active > Query > VMs and enter search criteria. VMs include the following details:
| Parameter | Description |
|---|---|
| Hosted On | The ESX host that the VM is on |
| VM IP |
The IP address as reported by vCenter after installation of VM tools. If the IP address is not available this field is empty. If the IP address is available, the VM IP address is displayed. |
| Leaf:Interface |
The leaf and the interface ESX host is connected to |
| Port Group Name:VLAN ID |
The VNIC’s portgroup and the VLAN ID associated with the portgroup |
| MAC Addresses |
MAC address of the VNIC |
| Virtual Infra Address |
IP address of the vCenter the VM is part of |
Validate Virtual Infra Integration
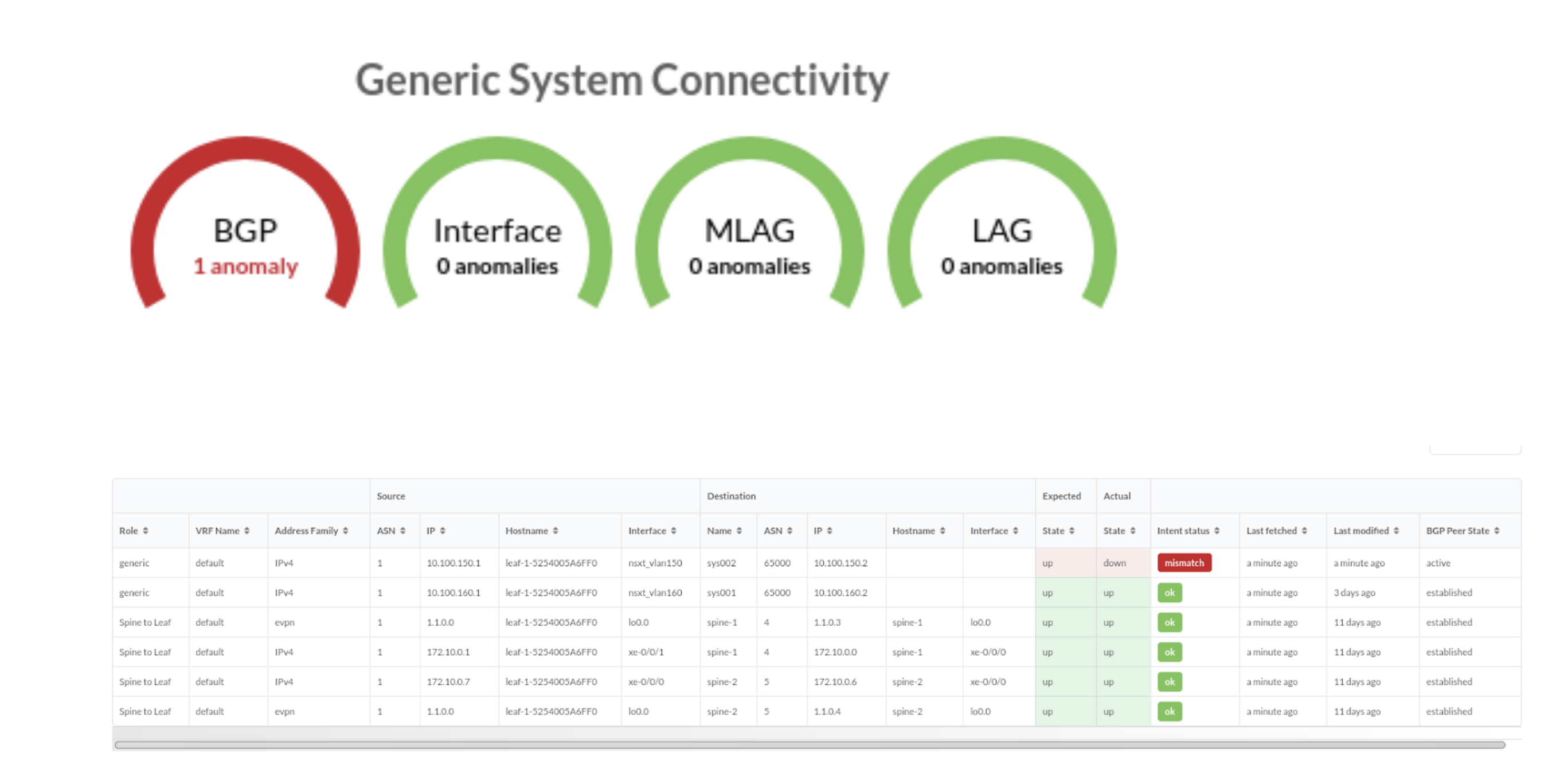
You can validate virtual infra with intent-based analytics. Apstra validates BGP
session towards NSX-T Edge. In case BGP neighborship in NSX-T Manager is deleted
then respective anomalies can be seen in Apstra dashboard.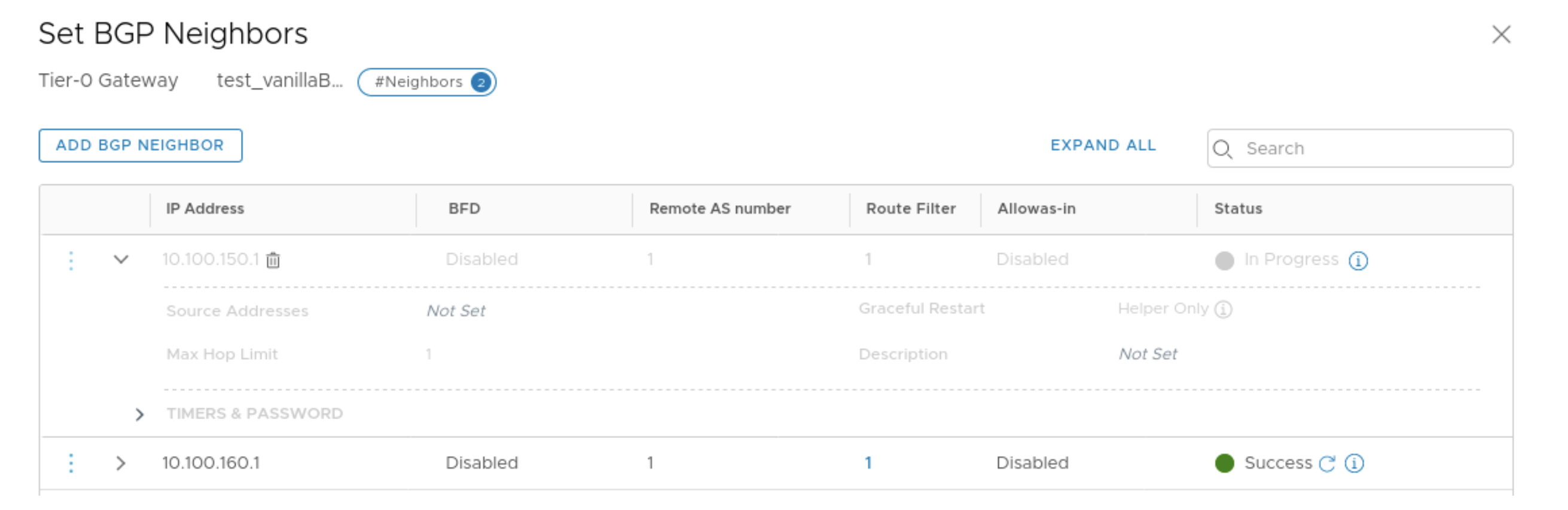
Two predefined analytics dashboards (as listed below) are available that instantiate predefined virtual infra probes.
Virtual Infra Fabric Health Check Dashboard
- Hypervisor MTU Mismatch Probe
- Hypervisor MTU Threshold Check Probe
- Hypervisor & Fabric LAG Config Mismatch Probe
- Hypervisor & Fabric VLAN Config Mismatch Probe
- Hypervisor Missing LLDP Config Probe
- VMs without Fabric Configured VLANs Probe
Virtual Infra Redundancy Check Dashboard
See Also
Auto-Remediation Overview
Automatic remediation of virtual network anomalies is available without user intervention. This can reduce operational cost when network operators don't need to investigate each anomaly and check for details and intervene to mitigate anomalies. VxLAN auto-remediation is a policy configured while adding vCenter/NSX-T to a blueprint. Anomaly remediation is done in accordance with this policy.
A policy-based auto-remediation approach automatically notifies you if there is a mismatch between vSphere DPG (VMware Port Groups) and VN in a particular blueprint, or if there is a VLAN mismatch between virtual infra and the Apstra fabric, or if there is a mismatch in LAG configuration on hypervisors and the corresponding leaf ports. Apstra software provides automatic guided remediation of such anomalies.
Some of the constraints and validations that take place before the remediation happens are listed below:
- When remediation policy is set to VLAN, that is rack-local, routing zone can only be the default one.
- If VLAN ID for virtual network spanning multiple hypervisors is the same, a single layer 2 broadcast domain is assumed. For such scenarios, the VLAN remediation policy must be set to VXLAN as for missing VLAN anomalies it is checked on all the ToR leaf devices connected to different hypervisors having virtual network with the same VLAN ID. If this is mistakenly chosen as VLAN type, validation errors are generated.
- Errors are flagged for different types of remediation policies (For example, if one is VXLAN type and other is VLAN type) are found attached to different virtual infras (such as two different vCenter servers) having the same VLAN ID in anomalies.
- If two different virtual infra servers are mapped in a blueprint and they have the same VLAN IDs then it is checked as two separate virtual networks by VXLAN auto-remediation policy.
Enable Auto-Remediation
After enabling the VLAN remediation policy as inter-rack, Apstra software searches for matching local VLANs in all ToRs connecting any member host (hypervisor for example) participating in the virtual infra virtual network. If such a VN is found, it simply extends that VN to also be bound to the ToR in question with the same local VLAN. If it's not found, a new inter-rack VN is created in the specified routing zone.
Remediate Probe Anomalies
The Remediate Anomalies feature works in conjunction with the Virtual Network (Single) primitive in connectivity templates. It can't be used with the Virtual Network (Multiple) primitive.
Apstra policy-based remediation has the following features:
- VLAN mismatch anomalies create one virtual network for one vCenter Distributed Virtual Switch (vDS) port group that is attached to hypervisors connected to leaf ports of ToRs in Apstra fabric.
- You cannot delete a routing zone that is being referenced in remediation policy.
For an EVPN-enabled fabric, we recommend that you have VN type as inter-rack or VXLAN in a specific routing zone.
- From the blueprint, navigate to Analytics > Probes and click one of the instantiated predefined probe names.
- Click Remediate Anomalies on a given stage. The Apstra software automatically updates the staged blueprint by adding/removing/updating VN endpoints and VNs to resolve the anomalies.
- Review the staged configuration in terms of virtual network parameters, then commit the configuration. The Apstra software indicates if there are no detected changes. This could happen if you invoke remediation more than once.
- Review and commit the changes on the Uncommitted tab.
- Return to the predefined probe to view any remaining anomalies.
Disable Virtual Infra Integration
Virtual infra integrations are disabled by deleting them from the blueprint and external systems.
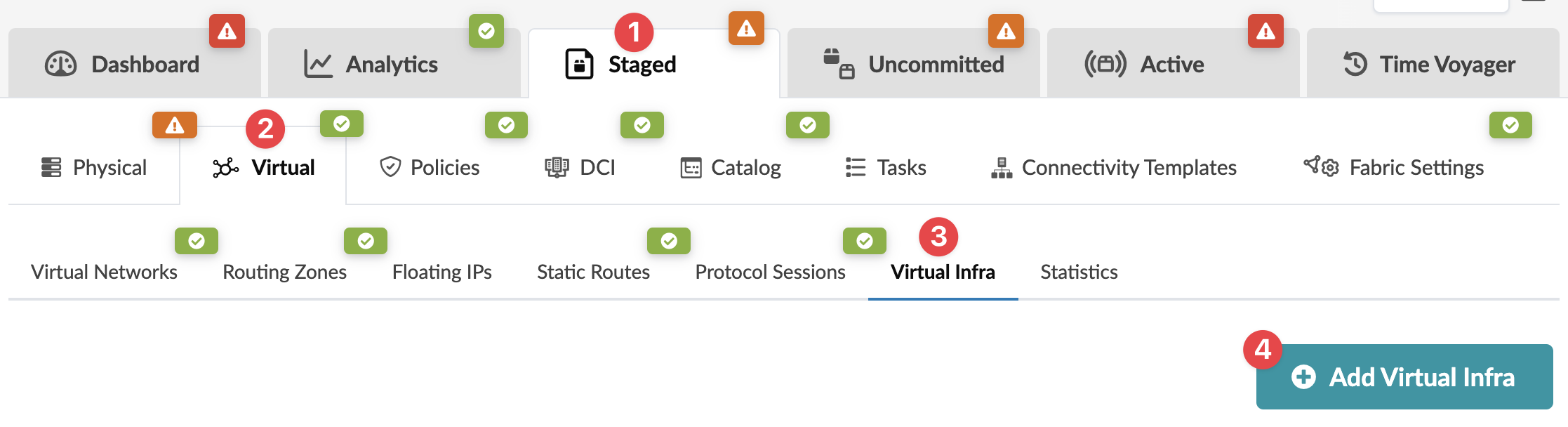
- From the blueprint, navigate to Staged > Virtual > Virtual Infra and click the Delete button for the virtual infra to disable.
- Click Uncommitted (top menu) and commit the deletion.
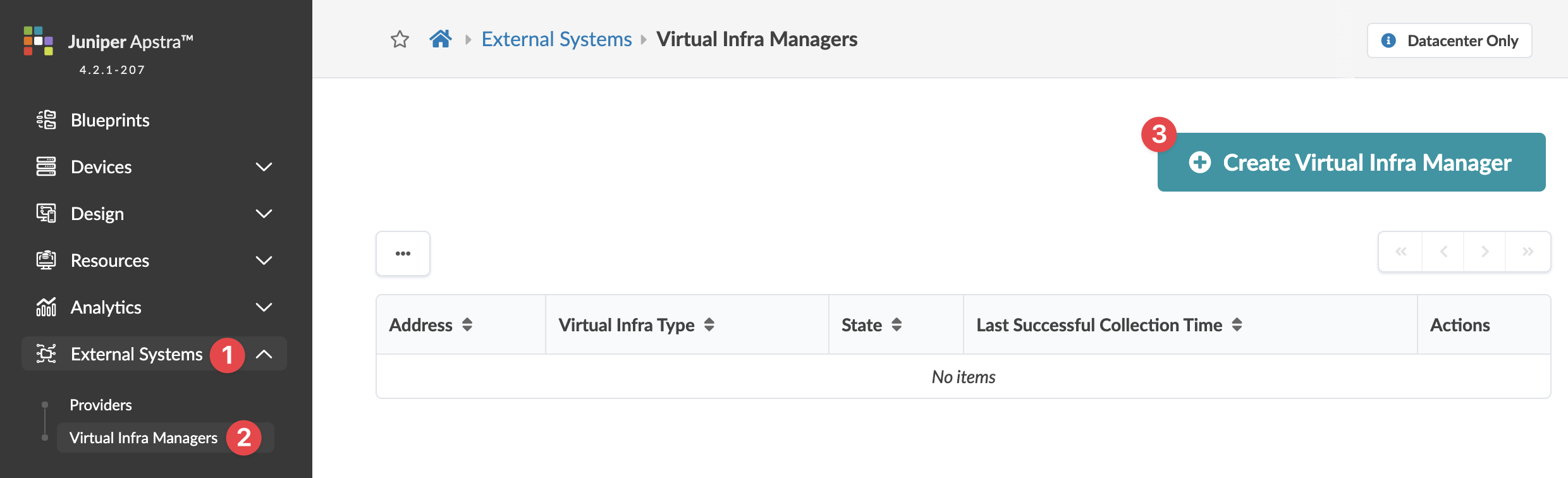
- From the left navigation menu, navigate to External Systems > Virtual Ingra Managers and click the Delete button for the virtual infra to disable.