Step 1: Begin
In this guide, we provide a simple, three-step path, to quickly get you up and running with Juniper Networks® Junos® Space Security Director (Security Director). You’ll learn how to install and deploy Security Director, and do some initial configuration to start managing the security devices on your network.
Meet Security Director
Security Director provides security policy management through a smart, centralized, Web-based interface. Using intuitive dashboards and reporting features, you gain insight into threats, compromised devices, risky applications, and more.
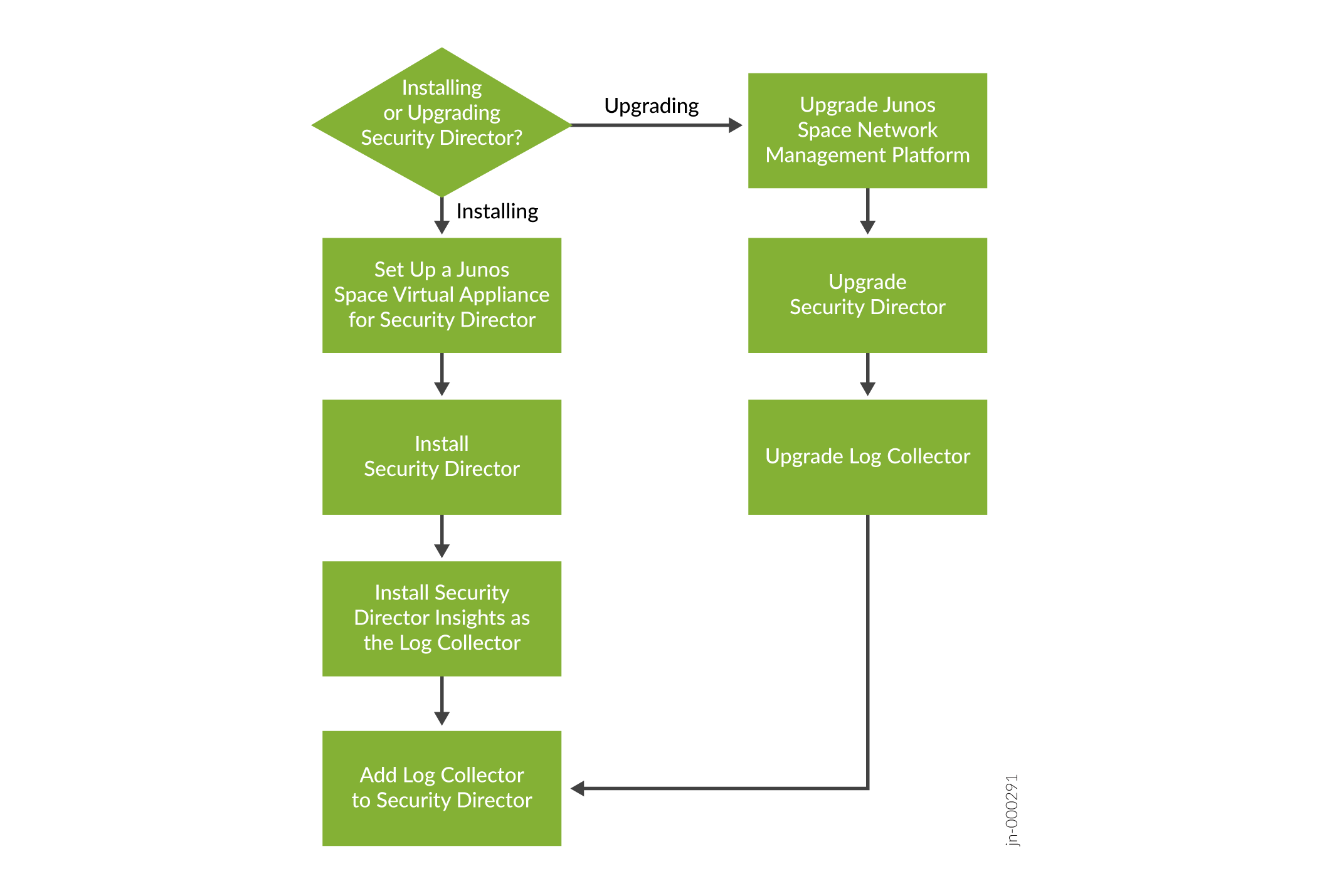
Install and Deploy Workflow
Here’s an overview of the process to install Security Director and deploy log collector.
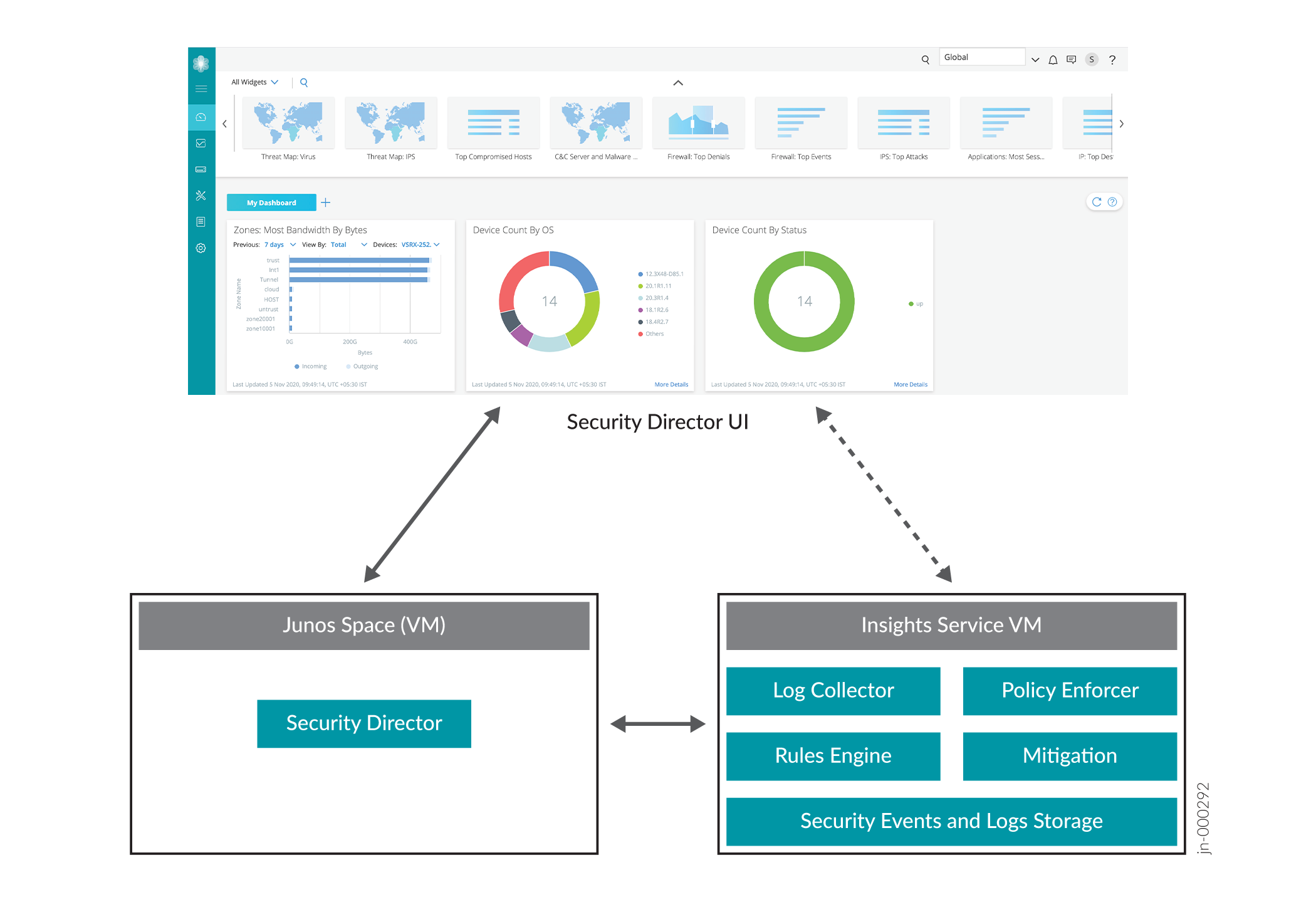
You'll need to use Security Director Insights as the log collector. Security Director Insights is a single virtual appliance (Service VM) that runs on the VMware vSphere infrastructure. The Security Director Insights GUI is integrated with the Security Director GUI, and the log collector and Policy Enforcer are integrated within the Security Director Insights VM. Here's an illustration of how Security Director Insights integrates with the Security Director ecosystem.
Before You Begin
Install and configure Junos Space Virtual Appliance. You’ll need to set up the virtual appliance to run as a Junos Space node. See the Junos Space Virtual Appliance Installation and Configuration Guide.
Starting in Junos Space Network Management Platform Release 22.1R1, you cannot install the Platform on the JA2500 Junos Space appliance.
Install Security Director
Installing Security Director is easy. First, verify the supported Junos Space Network Management Platform version by logging in to Network Management Platform > Administration > Application. Then, download the Security Director release image from the download site, upload it to the Junos Space Platform server, and install it. You can find all the details in Adding a Junos Space Application.
You can install Junos Space Security Director only on the supported Junos Space Network Management Platform version.
Install Security Director Insights as the Log Collector
You'll need to use Security Director Insights as the log collector. You install Security Director Insights from an OVA file. Once installed, you can use the Security Director Insights VM as a log collector to view log data across multiple SRX Series Firewall. A single Security Director Insights VM provides up to 25K events per second (eps), making it easier for you to scale up with less virtual resources.
Here are the required specifications for deploying Security Director Insights VM for various eps rates:
|
EPS Rate |
CPU |
Memory |
|---|---|---|
|
5k |
4 |
16 |
|
10k |
8 |
16 |
|
15k |
8 |
24 |
|
25k |
16 |
32 |
In this guide, you learn how to deploy and configure Security Director Insights VM as the log collector. Based on your requirement, you can choose to deploy JSA as a log collector. For details, see the Security Director Installation and Upgrade Guide.
Deploy and Configure the Security Director Insights OVA File
Security Director Insights recommends VMware ESXi Server version 6.5 or later to support a VM with the following initial configuration:
-
12 CPUs
-
24 GB RAM
-
1.2 TB disk space
If you are not familiar with using VMware ESXi servers, see VMware Documentation and select the appropriate VMware vSphere version.
Here’s how to deploy and configure Security Director Insights using the OVA file:
-
Download the Security Director Insights VM OVA image from the Juniper Networks software download page.
CAUTION:Do not change the name of the Security Director Insights VM image file that you download from the Juniper Networks support site. If you change the name of the image file, the Security Director Insights VM creation may fail.
-
Launch the vSphere Client that is connected to the ESXi server where you want to deploy the Security Director Insights VM.
-
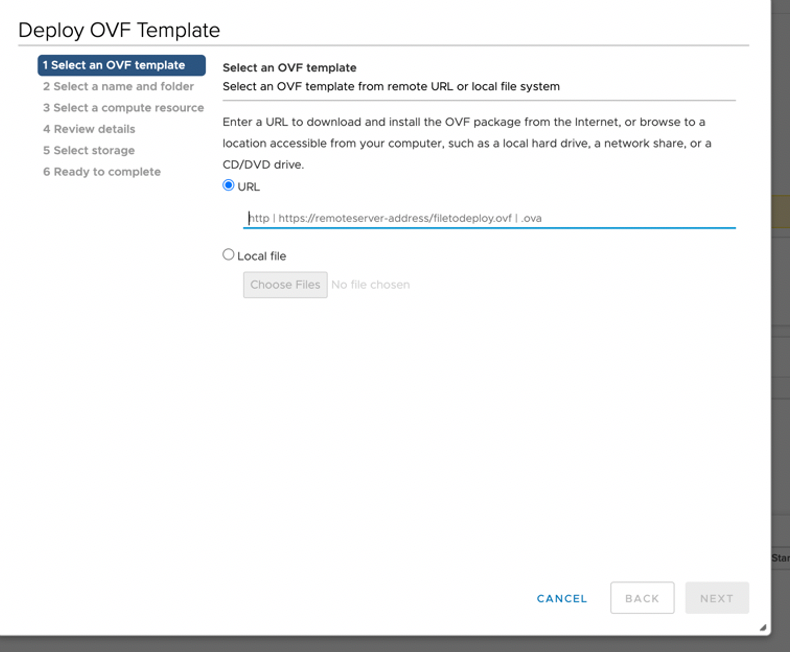
Select File > Deploy OVF Template to open the Deploy OVF Template page.
-
Select the URL option if you want to download the OVA image from the Internet or select Local file to browse the local drive and upload the OVA image.
-
Click Next.
The Select a name and folder page opens.
-
Enter the OVA file name and installation location for the VM, and click Next.
The Select a compute resource page opens.
-
Select the destination compute resource for the VM, and click Next.
The Review details page opens.
-
Verify the OVA details and click Next.
The License agreements page opens.
-
Accept the EULA and click Next.
The Select storage page opens.
-
Select the destination file storage for the VM configuration files and the disk format. (Thin Provision is for smaller disks and Thick Provision is for larger disks.)
Click Next. The Select networks page opens.
-
Select the network interfaces that the VM will use.
You can configure IP allocation for Static or DHCP addressing. We recommend using the Static IP Allocation Policy. Since the DHCP option is primarily used only for proof of concept, short-term deployments, we don't cover how to use that option here.
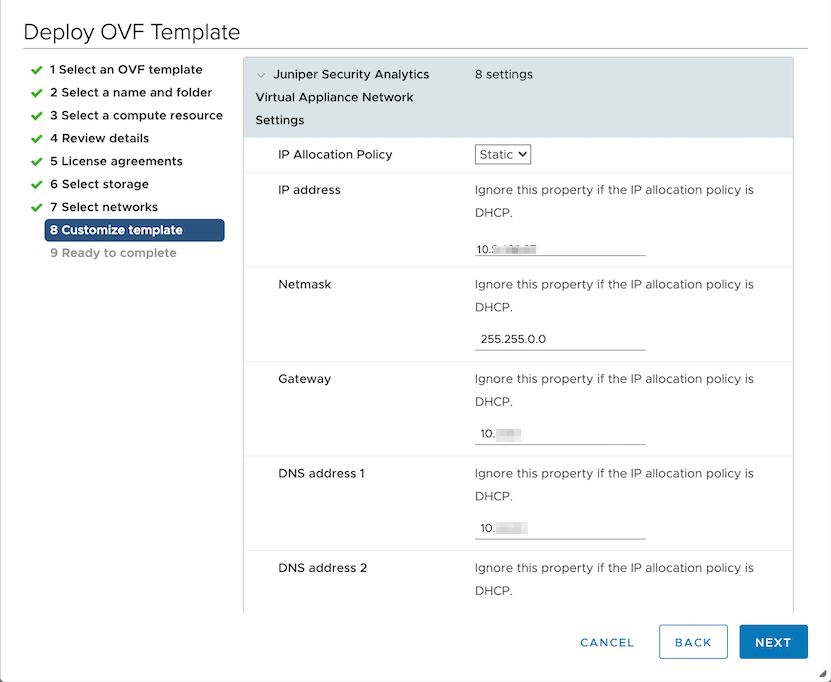
Click Next. The Customize template page opens.
-
For Static IP Allocation, configure the following parameters for the virtual machine:
-
IP Allocation Policy—Select Static
-
IP address—Enter the Security Director Insights VM IP address
-
Netmask—Enter the netmask
-
Gateway—Enter the gateway address
-
DNS Address 1—Enter the primary DNS address
-
DNS Address 2—Enter the secondary DNS address
Click Next. The Ready to complete page opens:
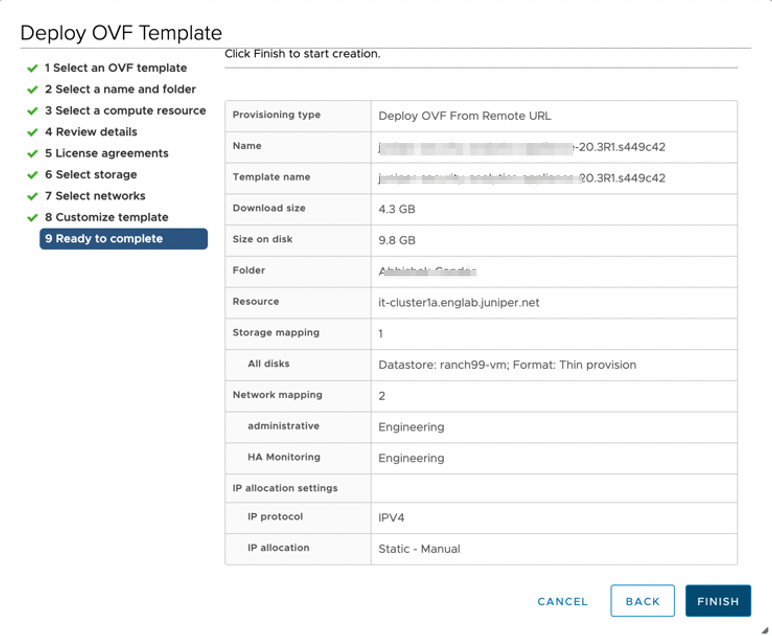
-
-
Review the details and click Finish to begin the OVA installation.
-
After the OVA is installed successfully, power on the VM and wait for the boot up to complete.
-
Once the VM powers on, in the CLI terminal, log in as administrator with the default username as “admin” and password as “abc123”.
After you log in, you’ll be prompted to change the default admin password. Enter a new password to change the default password.
Congratulations! The Security Director Insights deployment is now complete.
-
You will be prompted with Yes/No. Enter No to configure the OVA as LC + SDI on-prem.
Do More with Policy Enforcer
You can install Policy Enforcer to configure Juniper Connected Security. Policy Enforcer integrates with Juniper Networks® Advanced Threat Prevention Cloud (Juniper ATP Cloud) to provide centralized threat management and monitoring to your Juniper Connected Security network. You can use Policy Enforcer to combine threat intelligence from different solutions and act on that intelligence from one management point.
Starting in Security Director Release 24.1R1, standalone Policy Enforcer is not supported. You must use Security Director Insights as the Policy Enforcer.
For details on Security Director Insights as the integrated Policy Enforcer, see Configure Security Director Insights as Integrated Policy Enforcer.
