Configurar multiconexión de EVPN de estructura de campus
Siga estos pasos para combinar las capas de núcleo y distribución en un solo conmutador mediante la configuración de la multiconexión de EVPN.
La solución multiconexión de EVPN de estructuras de campus de Juniper Networks admite una arquitectura de núcleo colapsado. Esta arquitectura fusiona las capas de núcleo y distribución en un solo conmutador. La fusión de estas capas en un solo conmutador convierte la red jerárquica tradicional de tres niveles en una red de dos niveles. Esta arquitectura también elimina la necesidad de STP en las redes de campus al proporcionar capacidades de multihoming desde la capa de acceso hasta la capa central.
-
El tipo de topología EVPN Multihoming solo está disponible para la estructura de campus específica del sitio. No se puede compilar a nivel de organización.
-
En las topologías creadas en la nube de Mist después de las actualizaciones de mayo de 2025, Mist detecta e informa automáticamente cualquier bucle de EVPN y direcciones MAC duplicadas. Estos problemas se muestran en la página Información del conmutador.
-
Detección de bucles EVPN: la detección ligera de bucles PE-CE de EVPN-VXLAN ayuda a detectar y romper bucles Ethernet LAN en puertos descendentes leaf-to-server o de acceso. Esta función puede detectar bucles causados por problemas como componentes de estructura mal cableados o conmutadores de terceros conectados incorrectamente a la estructura. Para que esta función funcione, el conmutador debe ejecutar Junos OS versión 24.4R1 o posterior. Para obtener más información, consulte Detección ligera de bucles de hoja a servidor EVPN-VXLAN.
-
Detección de direcciones MAC duplicadas: identifica y mitiga problemas derivados del movimiento de direcciones MAC (movilidad MAC) entre diferentes interfaces o dispositivos en entornos EVPN. Aunque se espera cierta movilidad de MAC (por ejemplo, cuando un dispositivo realmente se mueve), los cambios rápidos pueden indicar problemas como bucles de red o configuraciones incorrectas. Para obtener más información, consulte Configuración de la detección de bucles para direcciones MAC duplicadas.
-
Para obtener un ejemplo de configuración detallado, consulte Flujo de trabajo de multiconexión de EVPN de estructura de campus.
Prácticas recomendadas de configuración de estructuras de campus
- Configure VLAN a nivel de plantilla de conmutador e impórtelas mientras se configura la estructura de campus. La plantilla debe ser la única fuente de información para todas las VLAN y perfiles de puerto, a menos que se requiera específicamente a nivel de conmutador o sitio.
- En la capa de acceso, evite usar perfiles de puerto troncal que permitan todas las VLAN, a menos que se requiera explícitamente.
- Cree la configuración de red VRF y VRF a través de la estructura del campus, no mediante plantillas de conmutador.
- Cree asignaciones de puertos por rol y sobrescriba la configuración en un dispositivo individual según sea necesario.
- Administre la configuración del relé DHCP a través del flujo de trabajo de la estructura del campus, excepto para los dispositivos de bloque de servicio.
Para configurar la multiconexión de EVPN de estructura de campus:
- En el menú de navegación izquierdo, seleccione Organización > estructura de campus.
- En la lista desplegable del sitio situada junto al encabezado de la página, seleccione el sitio en el que desea crear la estructura del campus.
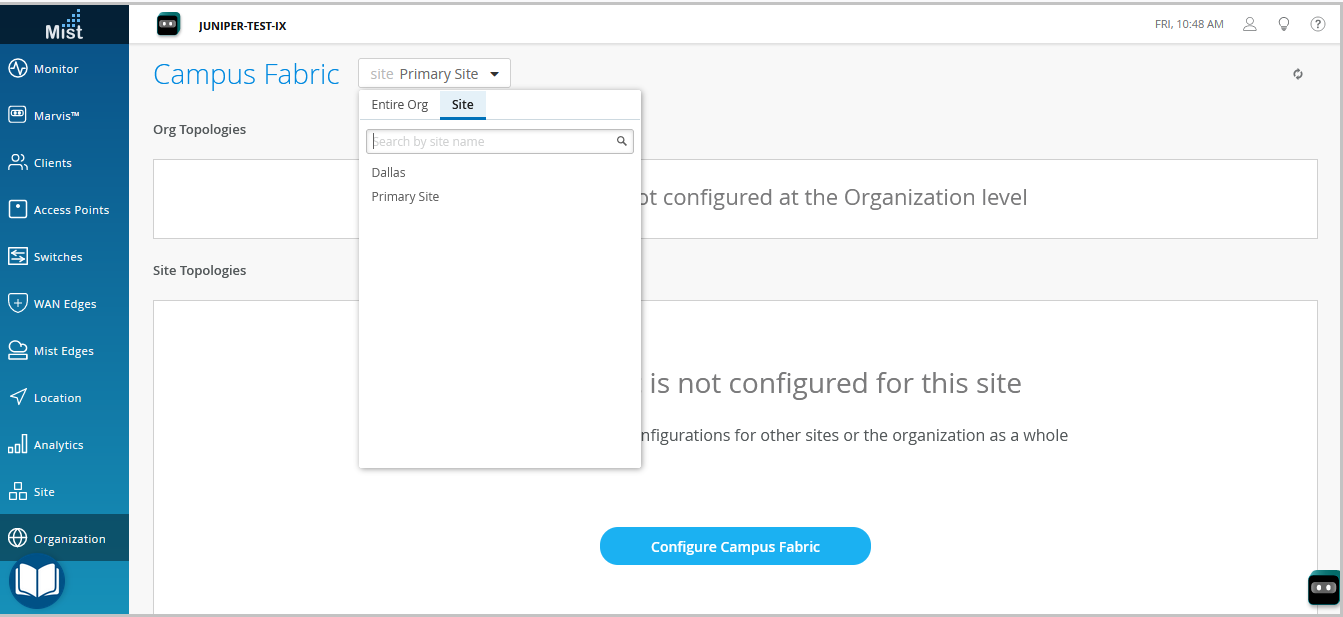
- Haga clic en la opción que le parezca. Clic:
-
el botón Configurar estructura de campus (que se muestra si el sitio no tiene asociada una configuración de estructura de campus).
-
el botón Crear estructura de campus (que se muestra si el sitio ya tiene al menos una configuración de estructura de campus asociada).
Se muestra la ficha Topología . -
- Seleccione el tipo de topología EVPN Multihoming.
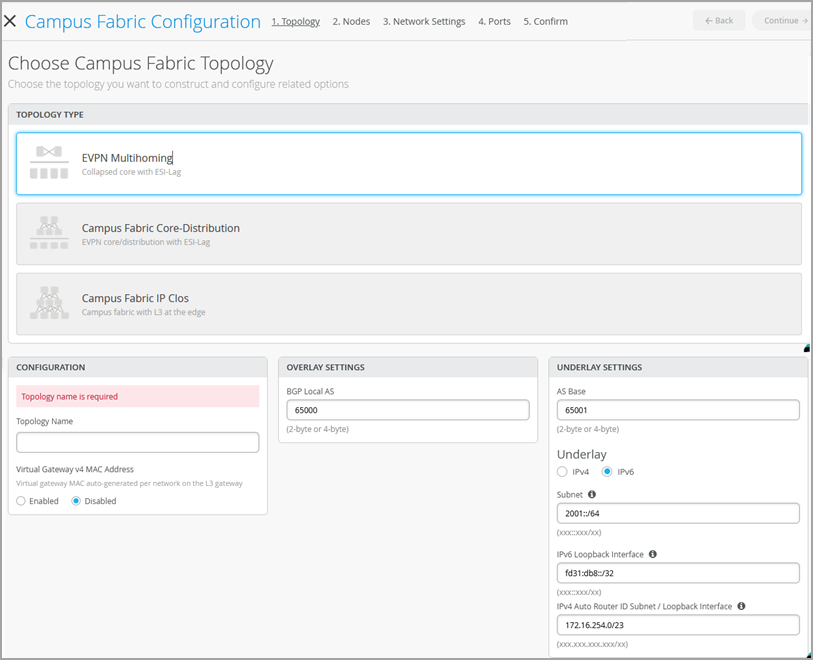
- Configure las opciones restantes en la ficha Topología, como se describe a continuación:
Nota:
Le recomendamos que use la configuración predeterminada en esta pantalla, a menos que entre en conflicto con alguna red conectada a la estructura del campus. Los vínculos punto a punto entre cada capa utilizan el direccionamiento /31 para conservar las direcciones.
- En la sección CONFIGURACIÓN, configure lo siguiente:
-
Nombre de topología: escriba un nombre para la topología.
-
Dirección MAC de la puerta de enlace virtual v4: habilite esta opción para admitir los redireccionamientos del portal de invitados en la WLAN. , Mist proporcionará una dirección MAC única para cada puerta de enlace virtual de capa 3 (L3) (por red). Desactivado de forma predeterminada.
-
- (Si decide no usar la configuración predeterminada) En la sección CONFIGURACIÓN DE SUPERPOSICIÓN, escriba lo siguiente:
-
AS local de BGP: representa el punto de partida de los números de AS de BGP privados que Mist asigna automáticamente a cada dispositivo. Puede usar cualquier intervalo de números de AS BGP privado que se adapte a su implementación. Mist aprovisiona la política de enrutamiento para que solo se intercambien las direcciones IP de circuito cerrado en la capa subyacente de la estructura.
-
- (Si decide no usar la configuración predeterminada) En la sección CONFIGURACIÓN DE SUBYACENTE, configure lo siguiente:
-
Base AS: el número base del AS. El valor predeterminado es 65001.
-
Base subyacente: seleccione una versión de protocolo de Internet para la capa subyacente. Las opciones son IPv4 e IPv6.
-
Subred: el rango de direcciones IP que Mist utiliza para los vínculos punto a punto entre dispositivos. Puede usar un rango que se adapte a su implementación. Mist divide esta subred en direcciones de subred /31 por vínculo. Puede modificar este número para adaptarlo a la escala de implementación específica. Por ejemplo, una red /24 proporcionaría hasta 128 subredes /31 punto a punto.
-
Interfaz de circuito cerrado IPv6: especifique una subred de interfaz de circuito cerrado IPv6, que se utiliza para configurar automáticamente la interfaz de circuito cerrado IPv6 en cada dispositivo de la estructura.
-
ID de enrutador automático Interfaz de subred/circuito cerrado: Mist utiliza esta subred para asignar automáticamente un ID de enrutador a cada dispositivo de la estructura (incluidos los dispositivos de acceso, independientemente de si están configurados con EVPN o no). Los ID de enrutador son interfaces de circuito cerrado (lo0.0) que se utilizan para superponer emparejamiento entre dispositivos. Para topologías nuevas, este campo rellena automáticamente un valor de subred predeterminado (172.16.254.0/23), que puede modificar. Cuando se edita una topología existente, este campo no rellena ningún valor predeterminado. El ID de enrutador se utiliza como identificador cuando se implementan protocolos de enrutamiento como BGP. Después de agregar el conmutador a la capa de núcleo contraído, haga clic en el icono del conmutador para ver el ID de enrutador asociado.
Puede sobrescribir el ID de enrutador asignado automáticamente configurando manualmente una interfaz de circuito cerrado en el campo ID de enrutador del mosaico Enrutamiento de la página de configuración del conmutador (Conmutadores > nombre del conmutador). Sin embargo, si modifica la configuración de la estructura del campus posteriormente, Mist vuelve a realizar la asignación automática del ID del enrutador y reemplaza la interfaz de circuito cerrado configurada manualmente.
-
- En la sección CONFIGURACIÓN, configure lo siguiente:
- Haga clic en Continuar para ir a la pestaña Nodos, donde puede seleccionar dispositivos que formen parte de la implementación de estructura de campus.
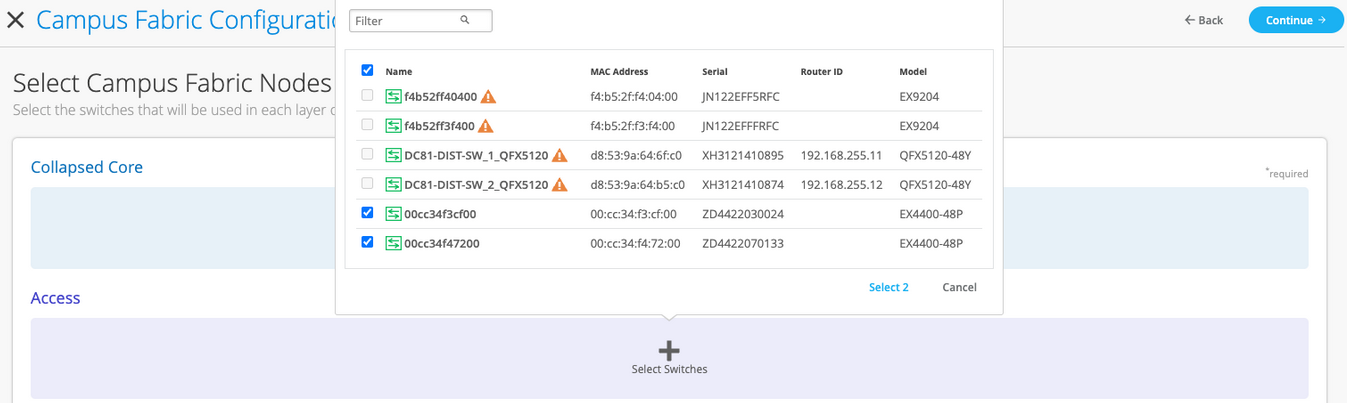
- Agregue conmutadores a la capa de núcleo colapsado y a la capa de acceso.
Le recomendamos que valide la presencia de cada dispositivo en el inventario de conmutadores antes de crear la estructura de campus.
Para agregar conmutadores:
- Haga clic en Seleccionar conmutadores.
- Elija los conmutadores que desea agregar a la estructura del campus.
- Haga clic en Seleccionar.
- Después de seleccionar los conmutadores, haga clic en Continuar para ir a la pestaña Configuración de red, donde puede configurar las redes.
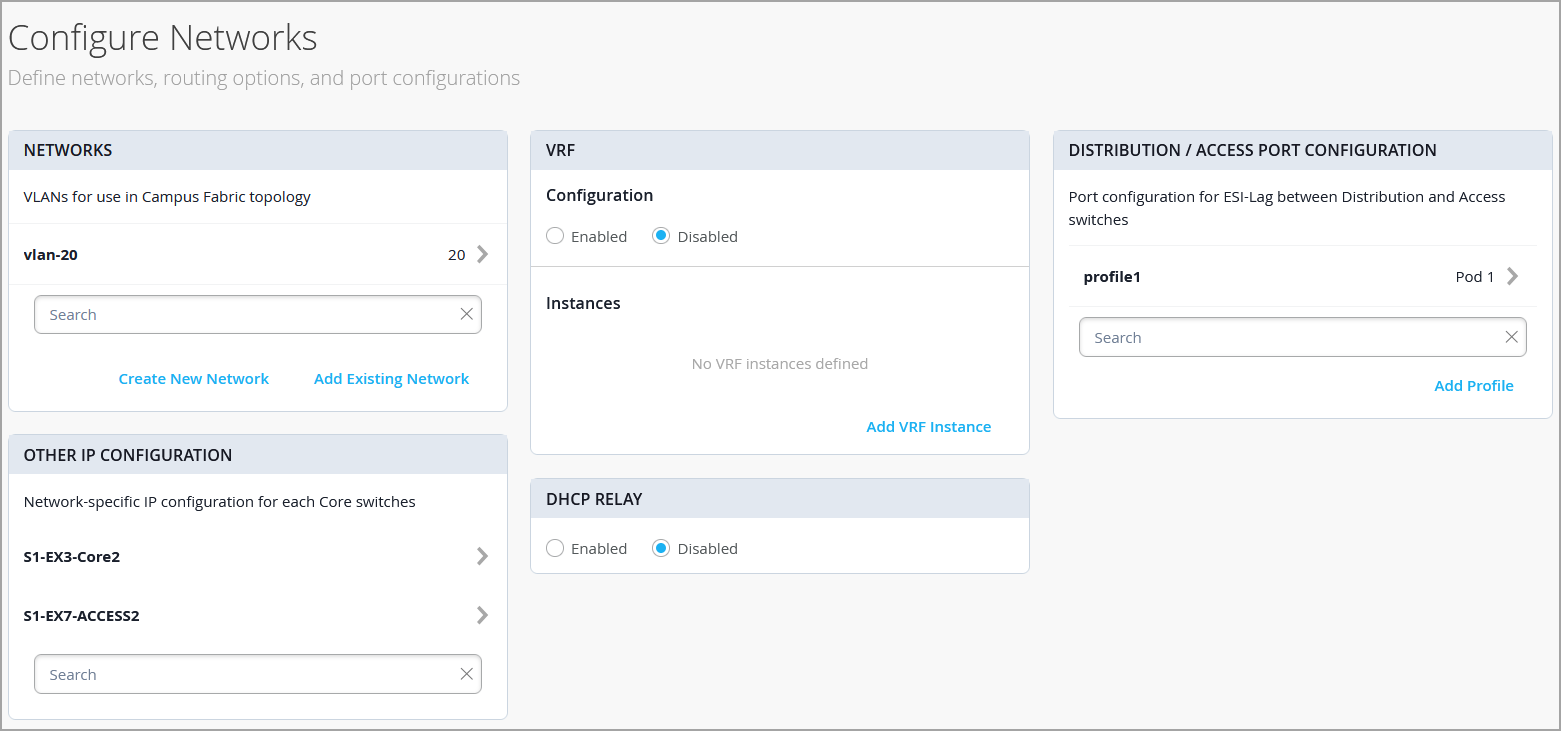
- Configure las opciones de red como se describe a continuación:
- En el mosaico REDES, agregue redes o VLAN a la configuración. Puede crear una nueva red o importarla desde la plantilla de conmutador definida en la página Plantillas de conmutador > organización.
Para agregar una nueva VLAN, haga clic en Crear nueva red y configure las VLAN. La configuración incluye un nombre, un ID de VLAN y una subred. Puede especificar direcciones IPv4 o IPv6 para la subred.
Para importar VLAN desde la plantilla:
-
Haga clic en Agregar red existente.
-
Seleccione una plantilla de conmutador en la lista desplegable Plantilla para ver las VLAN disponibles en esa plantilla.
-
Seleccione la VLAN necesaria de la lista mostrada y haga clic en la marca ✓.
Las VLAN se asignan a identificadores de red virtual (VNI). Opcionalmente, puede asignar VLAN a instancias de enrutamiento y reenvío virtual (VRF) para separar lógicamente el tráfico.
-
- Revise la configuración en el mosaico OTRA CONFIGURACIÓN IP. Esta sección rellena la configuración automáticamente después de especificar las redes en la sección REDES.
- Opcionalmente, configure instancias de VRF. Recomendamos usar VRF cuando se apliquen políticas de tipo 5 (prefijo IP) en una arquitectura de estructura de campus basada en segmentos. De forma predeterminada, Mist coloca todas las VLAN en el VRF predeterminado. La opción VRF le permite agrupar VLAN comunes en el mismo VRF o VRF separados según los requisitos de aislamiento de tráfico. Todas las VLAN de cada VRF tienen conectividad total entre sí y con otros recursos de red externos. Un caso de uso común es el aislamiento del tráfico inalámbrico de invitados de la mayoría de los dominios empresariales, excepto la conectividad a Internet. De forma predeterminada, la estructura de campus proporciona un aislamiento completo entre VRF, lo que obliga a las comunicaciones entre VRF a atravesar un firewall. Si necesita comunicación entre VRF, debe incluir rutas adicionales al VRF. La ruta adicional podría ser una ruta predeterminada que indique a la estructura del campus que use un enrutador externo. También podría ser un firewall para una mayor inspección de seguridad o capacidades de enrutamiento.
Para crear un VRF:
-
En el icono VRF, haga clic en Agregar instancia VRF y especifique la configuración. La configuración incluye un nombre para el VRF y las redes que se asociarán con el VRF.
-
Para agregar rutas adicionales, haga clic en el vínculo Agregar rutas adicionales en la página Nueva instancia de VRF y especifique la ruta. Puede especificar direcciones IPv4 o IPv6.
-
- En el mosaico CONFIGURACIÓN NÚCLEO/PUERTO DE ACCESO, complete la configuración de puerto para ESI-LAG entre el núcleo colapsado y los conmutadores de acceso. La configuración incluye un nombre y otros elementos de configuración de puerto. De forma predeterminada, esta configuración incluye las redes agregadas en el icono REDES en la misma página. Si desea eliminar o modificar la configuración, haga clic en Mostrar opciones avanzadas y configure las opciones. Utilice las sugerencias que aparecen en pantalla para configurar los ajustes del perfil de puerto.
- En el mosaico Retransmisión DHCP, configure las opciones de la retransmisión DHCP. Tiene las siguientes opciones:
-
Habilitado: configura la retransmisión DHCP en todos los dispositivos habilitados para IRB en la estructura del campus. Esta opción le permite habilitar la retransmisión DHCP en las redes seleccionadas. La red se rellenará dentro del mosaico Retransmisión DHCP siempre que aparezca en la pestaña Redes de la misma página.
-
Deshabilitado: deshabilite la retransmisión DHCP en los dispositivos en la estructura del campus. Cuando selecciona esta opción, la retransmisión DHCP se deshabilita en todos los dispositivos habilitados para IRB. Debe seleccionar cuidadosamente esta opción, ya que esto eliminará la retransmisión DHCP definida localmente en la página Detalles del conmutador.
-
Ninguno: esta opción se selecciona automáticamente cuando la topología de la estructura de campus tiene una mezcla de dispositivos en términos de la configuración del relé DHCP; es decir, algunos dispositivos tienen habilitado el relé DHCP, otros lo tienen deshabilitado y otros no lo tienen definido. Esta opción estará visible para todas las topologías de estructura de campus que tengan relé DHCP definido localmente en conmutadores individuales.
Si desea quitar todas las redes de retransmisión DHCP definidas localmente, seleccione Habilitada y, a continuación, elija Quitar todas las redes DHCP de nivel de dispositivo existentes. Puede simplificar la implementación de DHCP Relay centralizando cualquier cambio de configuración desde el flujo de trabajo de la estructura del campus.
Si habilita la retransmisión DHCP en una configuración de estructura de campus, se habilitará en todos los dispositivos definidos por IRB en la estructura y se deshabilitará en el resto de los dispositivos. Por ejemplo, en las topologías de multiconexión de EVPN, la retransmisión DHCP está habilitada en dispositivos de núcleo colapsado y deshabilitada en el resto.
-
- En el mosaico REDES, agregue redes o VLAN a la configuración. Puede crear una nueva red o importarla desde la plantilla de conmutador definida en la página Plantillas de conmutador > organización.
- Haga clic en Continuar para ir a la pestaña Puertos, donde puede configurar los puertos y crear una conexión entre los conmutadores de núcleo, distribución y capa de acceso.
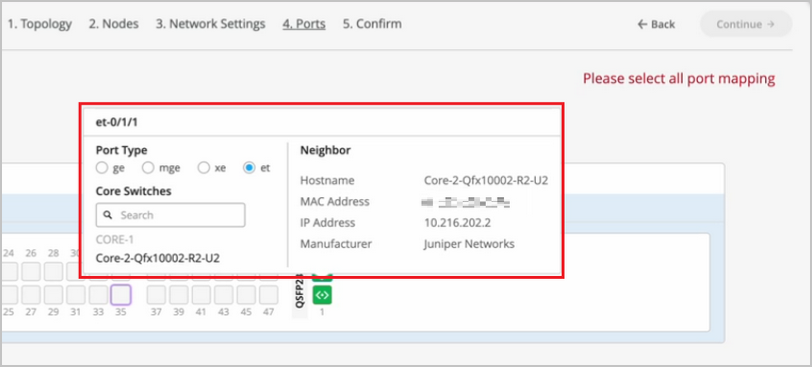
- Configure los puertos del conmutador en la capa de núcleo contraído de la siguiente manera:
- Seleccione un conmutador en la sección Núcleo colapsado para abrir el panel Puerto del conmutador.
- En el panel de puertos del conmutador, seleccione el puerto que desee configurar.
- Especifique un tipo de puerto (por ejemplo,
geoxe). - Escoger:
-
Enlace a núcleo colapsado para conectar el puerto a un conmutador central.
En la capa de núcleo contraído, puede conectar cada conmutador a todos los demás conmutadores para formar una topología de malla completa. Una topología de malla completa proporciona una estructura de campus de EVPN Multihoming con mayor resiliencia, lo que garantiza una funcionalidad de red continua incluso si falla un dispositivo.
-
Enlace al acceso para conectar el puerto a un conmutador de acceso.
-
- Seleccione el conmutador principal o de acceso (según la selección del paso anterior) en el que debe terminar el vínculo. Debe configurar todos los puertos que deben formar parte de la estructura del campus.
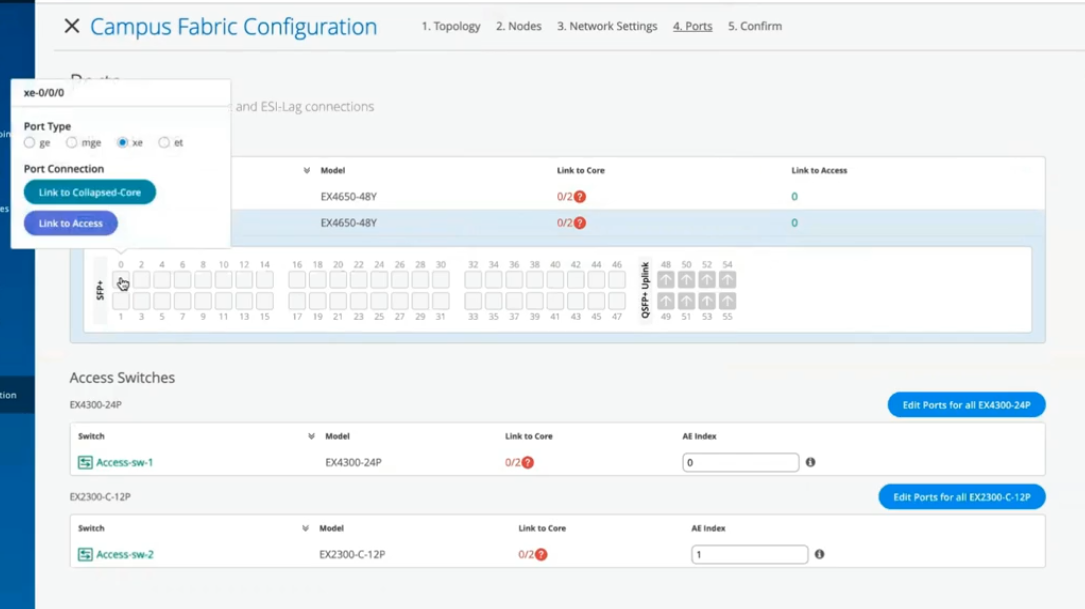 Para configurar los puertos del conmutador en la capa de acceso:
Para configurar los puertos del conmutador en la capa de acceso:- Seleccione un conmutador en la sección Acceso para abrir el panel Puerto del conmutador.
- En el panel de puertos del conmutador, seleccione el puerto que desee configurar.
- Especifique un tipo de puerto (por ejemplo,
geoxe).En caso de que la capa de acceso utilice un chasis virtual (VC), puede configurar los puertos en las fichas Principal y Copia de seguridad.
Para los conmutadores de acceso, seleccione sólo las interfaces que deben utilizarse para interconectar con el conmutador de distribución. El sistema agrupa todas las interfaces en un único paquete Ethernet mediante la opción de índice AE. Puede especificar un valor de índice AE para los dispositivos de acceso.
Si desea ver la información de configuración y estado de un puerto específico, coloque el cursor sobre el cuadro numerado que representa ese puerto en la interfaz de usuario del panel de puertos.
- Haga clic en Continuar para ir a la pestaña Confirmación.
- Haga clic en el icono de cada conmutador para ver y verificar la configuración.
- Después de verificar la configuración, haga clic en Aplicar cambios > Confirmar.
Este paso guarda la configuración de la estructura del campus en la nube de Mist y la aplica a los conmutadores. Si los conmutadores están sin conexión, se les aplicará la configuración la próxima vez que estén en línea. Un conmutador puede tardar hasta 10 minutos en completar la configuración.
- Haga clic en Cerrar configuración de estructura de campus.
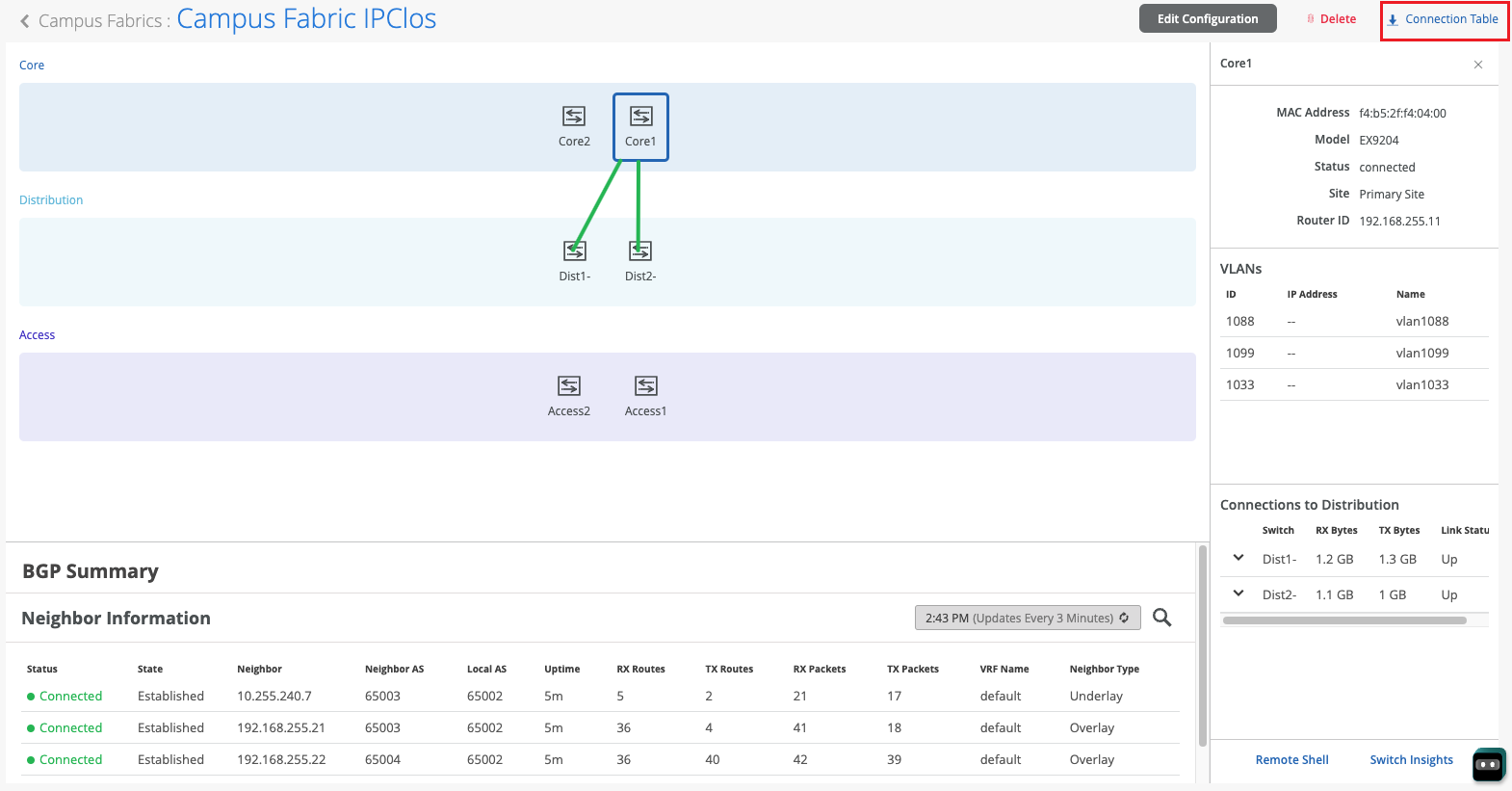
Después de que Mist compile la estructura del campus, o mientras crea la estructura, puede descargar la tabla de conexiones. La tabla de conexiones representa el diseño físico de la estructura del campus. Puede usar esta tabla para validar todas las interconexiones de conmutadores para los dispositivos que participan en la compilación de la estructura de campus físico. Haga clic en Tabla de conexiones para descargarla (formato .csv).
- Compruebe la configuración de la estructura del campus. Para comprobarlo, siga los pasos que se indican en la sección Verificación en Flujo de trabajo de multiconexión de EVPN de estructura de campus.
Hello and welcome to this edition of Wired Assurance. My name is Rohan Chada and today I'll be talking about building an EVPN week stand campus fabric in just four steps. Today we're going to talk about the deployment of EVPN multi homing topology. I'll walk you through the different steps that are required and I can promise you none of those require any CLI configuration.
Everything will be done through the UI and it'll be as simple as you can expect it to be. So let's just jump right into it and talk about EV Pin Multi Hamming. Before we jump into building the EV Pin Multi Hamming topology, let's understand the building blocks of it from a device perspective. Today as you can see, we're going to be using 2 core devices and two access devices.
The EVPN Multi Hamming topology can support up to 4 core devices, a minimum of two and a maximum of four and as many access devices as you'd like. But for this purposes of this video, we'll be using 2 core devices and two access devices. So to begin with, we click on organization and we under the wire tab we see Campus fabric. So as we click on Campus fabric, we can see that we are inside the site EVPN campus primary one and there is no campus fabric configured at this time.
And that's exactly where we'll begin. Click on configure campus fabric and we see that there are three topologies that are presented to us. EVPN multi homing which is collapse code with ESI lag, campus fabric Code distribution which is EVPN code distribution with ESI lag and canvas fabric IP cloth. What you see on the left side of each of these three names is a small diagram that basically depicts the topology that this this entails.
So you basically have above the line that you see the horizontal line in the diagram on each of these topologies. Above the line is where your your evpn vxlan construct exists. And what I mean by that is that's where those devices are, the devices that run Evpn vxlan configuration. Anything below the horizontal line are just pure access devices layer to they can be, they have to be non evpn VXLAN capable devices.
So once you've selected the EVPN multi homing we see that it's a collapsed core and what that means is that two or three layers of EVPN configuration is collapsed into just one layer. So we'll jump right in there by giving it a topology name. We're going to go ahead and call it evpn image. There are two settings that you have to provide on the initial page and that's for the overlay and the underlay settings.
For overlay we use ibgp today and for underlay we use ebgp. The default values will be presented to you, there is no reason to change it if there isn't a purpose behind it. And 65,000 is the local AS and 65,001 is the AS base to begin with for the underlay ebgp. And then we'll increment sequentially on a device spaces starting with 65001.
The loopback prefix as you can see is the the prefix that's used to assign to all the interfaces, all the loopback interfaces on all the devices. These interfaces are used to peer with every other VTAP in the campus fabric. And then last is the subnet, which is again a default value provided that can be changed by the user. This subnet is used to connect the underlying physical interfaces between the campus fabric.
Let's jump right into the next step and click on Continue. At this step we'll be selecting the Campus fabric nodes. In this Campus fabric configuration we'll be selecting 2 Campus course and I'll select Code one and Code 3 for this demo. And as you can see in this nice drop down, you have all the information provided to you and that includes the model as well as the Mac address so you don't have to go back and forth between different pages of the UI.
Every information is provided right here. For the access devices, I'll be picking switch one and switch two. My core devices are EX 465048 wise that are EVPN capable. My access devices are EX 2300 and 4300 that do not understand EVPN.
Hence I am putting these in an access layer. The platform support on a topology basis is on the on the website and we've listed every platform that's supported on a per layer basis. So once you've selected this topology, we know that there are two core devices, 2 access devices. I can click on these core devices and I can see that the basic information about core one I see there is a router ID assigned.
This router ID is assigned as needed for the loop back interface. As I mentioned earlier, that's used for peering between the two core devices. In case of a collapsed core, the two core devices will act as the as the two vtips that basically they will be forming A VXLAN tunnel between each other. The access, which is on the other hand do not necessarily need a router ID, but we've provided them for consistency's sake.
They do not need it, but let's go ahead with that. Step three is basically configuring networks. So networks are basically of Vlans. So we'll go ahead and start creating some new networks here.
I'm going to be assigning some generic names here and I'll call it image vlan 10 and S and vlan ID 10 and I'll give it the subnet 190 to one 6810.0 slash 24 and I'll give it a virtual gateway for 190 to 168 dot 10.1. Now providing this subnet is. This is the only I would say.
This is the second step wherein you'll be providing us a subnet. The IP addressing for the IRB slash SVI interfaces or any IP addressing in the underlying physical interfaces in our fabric is taken care by missed Wire Assurance Campus Fabric. As a user and administrator, you don't have to worry about it. So once you've provided us a subnet, we'll take care of it.
So this virtual gateway will essentially be used for as a common address between the two core devices. So any underlying device, for example an access switch or any any device connected to the access switch will have its gateway as 190 to 168 or 10.1 which will be advertised via avpn and that's why we come in here and manually define it. So as you can see, I created a VLAN, VLAN 10 and voila, we see two IP addresses that have already been chosen to be assigned for the corresponding IRB slash SVI interfaces that will be assigned to code one and code 3 for VLAN 10.
Let's go ahead and create another one and we'll call it image VLAN 20. But in this case I'm not going to assign a subnet or virtual git net because I want to route for this particular VLAN. I want to route on the the the firewall of the campus fabric. So my the two core devices that I have will be connected dual home to a firewall and I want the routing to happen for this particular VLAN on the firewall.
So I'm going to skip this and this is basically a bridged overlay design wherein we'll assign the VNI to the corresponding VLAN 20, but we will not be configuring A subnet or a gateway on the 2 core devices. This is one way of creating a VLAN. The other way of adding a VLAN to the campus fabric is if you have existing network on the sites already. So we'll click on existing network and what we see is that there is a common VLAN that we already created earlier before we started this demo on an entire site.
So using the site configuration here, I created a VLAN called site wide VLAN with a VLAN ID of 100 and that's it. And what that did was all the devices in that site inherited the site wide VLAN. So I'm going to take site wide VLAN and I'm going to add that. So now I'm told that there is a virtual gateway that is required.
OK, there is a virtual gateway required. So we'll go ahead and add the virtual gateway. The subnet basically was inherited from the the site configuration where I had created VLAN printer. So I'm being told that the provided gateway is already used.
OK, so here we have 3 Vlans and as we already see that for two of them the static IP addresses have already been defined. For VLAN 10 there are two IP addresses, code one and code 3. Similarly for site VLAN 100, we have two IP addresses, one each for core one and core 3. And as we already know VLAN 20 is a doesn't have a virtual gateway on the collapse core, so we do not have a gateway for that.
Now let's jump into VRF and understand this is virtual routing and forwarding wherein you can create separate routing instances. You can basically increase the security in your network by segregating the Vlans in different routing instances. A different routing instance basically means that there is a different routing table on a per VLAN basis or however many Vlans you would like in that particular VRF. So we'll go and assign this name vrf one and then we'll we'll add image vlan 10 to vrf one if if there is a need.
I can always add extra routes within the VRF as well and that is an option. You go ahead and another VRF called VRF 2 and I'll use site by vlan for this particular VRF 2. The last step on this page is to basically configure the core access port configuration. This is the port configuration towards the access switches from the collapse code as it if you read the description it says this is the ESL configuration.
So let's just assign it a name and let's call it Yesi LAG, any name of the book, but Yesi Haffen LAG is what I've assigned. We presume that all the Vlans and networks that you've defined here are going to be a part of the ESI LAG configuration, and so we automatically add them to the trunk networks. You can come in here and manually change any settings that you would like. If you would like a smaller MTU or if you would like to manipulate the MTU size here to your environment needs, you can do that.
You can enable storm control. You can also enable Poe if that's a requirement, change the speed, duplex, add native VLAN. All of that is an option that we've provided. This is the last and final step and what we see here is there are different port panels.
These port panels are on a platform basis. For the purposes of this video, we are using EX4650 and two other platforms. So we'll show you the appropriate port panels as needed whenever any platform other than these are used. So let's jump right into it and let's let I'll go ahead and I'll configure these interfaces quickly.
So what I've done at this point is I've connected all the two collapsed core devices with the other two access devices. Basically the requirement is that there should be two interfaces connected to each other between the two core devices. Evpn multi Homing has that requirement for redundancy and then core one needs to connect to both access switch one and Access switch 2. Similarly code 3 needs to connect to both access switch one and access Switch 2.
So once those interfaces have been have been connected here you've told the missed UI that these are the interfaces. We can proceed and we can click on continue. This is the last step wherein you confirm that the topology changes that you want are there and if you click on code 1, we can see that on the right. We see a lot of information about everything that we've done so far.
We see the model, we see the router ID, we see the Vlans that we wanted in the campus fabric. Along with the Vlans we also see the IP addresses. I see that there are two IP addresses and three Vlans. One of them is and doesn't have an IP address and that is basically a bridge overlay design as I mentioned earlier.
We also see the connections by the way. I can see and I can verify here the connections connections to collapsed core or three and access switch one and access switch two at any point in this entire step. If you'd like to access the remote shell, we've provided you that option as well. So before you hit apply changes, if you'd like to log into your device you can do that here.
You can click on remote shell and pop up window will open for you and at this point you can you can look at your configuration. You can look at how your devices are connected. I see here that my devices are connected or one connects to two core 3 interfaces and core one has a connection to switch to and switch one as well. So a a little handy tool here where you can verify by logging into the device.
Let's click apply changes and confirm. At this time, what has happened is that the configuration that we decided to push to the devices is being pushed and is being committed to the junuper devices and right after that's committed, BGP Underlay as well as Overlay will be provisioned. Once BGP Underlay is provisioned, overlay and the VX LAN tunnels will come up, the VX LAN tunnel will be two way between collapsed Core one and collapsed Core 2. Let's just jump right into the switches while this configuration is happening.
We look at what's the scenario and the switches and the configuration that we pushed under the hood. Remember, everything that we did so far was based on UI. We did not touch the CLI. We did not make any CLI changes manually.
You did not have to define the EVPN configuration or the BGP configuration or the underlying physical connectivity. This is the value of Missed Wire Assurance Campus Fabric. Let's click on Utilities and click on Download JS Config. We see that configuration file has been downloaded.
This is a. This is a handy tool. What this does is it enables us to verify the configuration. All of us have been used to configuring things while the CLI and so it is very important that we verify that if you're doing this for the first time that everything that you want in the configuration should be there.
You could be a Greenfield environment or or a brownfield environment. You should be able to verify your configuration. So let's dive right into it. Let's look at this.
So as we can see, the first thing I see is I see some BGP configuration here. That's very important. We see the underlay BGP configuration here between the two core devices. There are two peers here on 2 interfaces.
We see the overlay configuration here since there's only one peer for core one and that is core three. There is only one neighbor. We see some EVPN configuration here, right? We also see the ESI LAG configuration here that was pushed by Campus Fabric.
None of that required us to push anything through CLI. We see 22 LAG interfaces AE0 and AE1AE0. It's towards switch one and AE three is towards switch two. We see the IRB configuration as we discussed earlier.
IRB 10 is the the first VLAN that we defined with a gateway and IRB 100 is the third one that was inherited from the site wide template. We also see the VRF configuration here. So as we can see, there's VRF one configuration that has one VLAN IRB .10. We also have type 5 routes as a part of it.
We also see VRF 2 configuration in this VRF 2 configuration, what we see is IRP 100. The second, I'm sorry, the third VLAN that we chose is also there. And then if you look at the configuration here, we see all three Vlans, even the VLAN, even the VLAN that we made bridged overlay is a part of the configuration has a VNI. So we can go ahead and we can assign the gateway for this particular VLAN on either the router of the campus fabric or the firewall based on your environment.
So now that we've looked at the configuration, let's look at how our EVPN campus fabric is doing and what do the EVPN insights tell us. So the EVPN insights, it's basically a pretty layer on top of the campus fabric that tells you about a few green and red links. And those green and red links are not not just the the interface status. They tell you some good information about your peering in the network.
So we looked at there are a few green links. We see that the status is up, but we see these triangles. And these triangles are not, they do not look great. So when I hover over this topology, I am being told that the selected port is not connected to the correct switchboard in the campus traffic topology.
What that basically means is that the the the back end of the campus fabric knows that the core one to core 3 port that I've selected is not the right port and instead it is something else. It is smart enough to understand that there was another port that should have been connected, but I have connected the wrong the wrong port and that is absolutely right. So I'm going to jump right into the campus fabric and change that quickly for you guys. So I'll click on edit configuration and go right to the last step and I'll change this zero to 1 and we'll hit continue and we'll apply changes and save them while the provisioning takes a while.
I'll be right back in a minute. So, so we're back. So as we can see our pretty green lines are back. What and what that means is that we've you corrected the interface that was not correct in the right way.
Campus Fabric was smart enough to let us know that the interfaces that were connected between code one and code three were not right. As you can see, I had 000 earlier and I switched that over to 001 and after doing that my BGP neighborship came back. And then here we can see if I click on any device the statistics between the two devices. We can also see, as I mentioned earlier, the Vlans and the IP addresses.
Thank you. This concludes our campus fabric demo today. I'll summarize all the things that we did today in this last 2025 minute session. So we built a campus fabric using the Mist UI.
None of those steps included anything to do on the CLI. We built a campus fabric in four steps wherein we as a step one, we selected the kind of topology that the user would want. As a second step, we chose the campus fabric nodes that will participate in the campus fabric. The third step was to provide us the networks that will be participating in the in the campus fabric.
And the last and final step was the connectivity of the devices itself. It's as simple as that.
