EN ESTA PÁGINA
Ejemplo: mejorar la seguridad mediante la configuración de OCSP para el estado de revocación de certificados
En este ejemplo se muestra cómo mejorar la seguridad mediante la configuración de dos pares mediante el Protocolo de estado de certificado en línea (OCSP) para comprobar el estado de revocación de los certificados usados en las negociaciones de fase 1 para el túnel VPN IPsec.
Requisitos
En cada dispositivo:
Obtener e inscribir un certificado local. Esto se puede hacer manualmente o mediante el Protocolo simple de inscripción de certificados (SCEP).
Opcionalmente, habilite la renovación automática del certificado local.
Configure políticas de seguridad para permitir el tráfico hacia y desde el dispositivo del mismo nivel.
Visión general
En ambos pares, se configura una raíz de perfil de entidad de certificación (CA) con las siguientes opciones:
El nombre de CA es Raíz.
La URL de inscripción es http://10.1.1.1:8080/scep/Root/. Esta es la URL a la que se envían las solicitudes SCEP a la CA.
La dirección URL del servidor OCSP es http://10.157.88.56:8210/Root/.
OCSP se usa primero para comprobar el estado de revocación del certificado. Si no hay respuesta del servidor OCSP, se utiliza la lista de revocación de certificados (CRL) para comprobar el estado. La URL de CRL es http://10.1.1.1:8080/crl-as-der/currentcrl-45.crlid=45.
El certificado de CA recibido en una respuesta OCSP no se comprueba para la revocación del certificado. Los certificados recibidos en una respuesta OCSP generalmente tienen una vida útil más corta y no se requiere una verificación de revocación.
En la tabla 1 se muestran las opciones de fase 1 utilizadas en este ejemplo.
Opción |
Par A |
Par B |
|---|---|---|
Propuesta de IKE |
ike_policy_ms_2_2_0 |
ike_proposal_ms_2_0_0 |
Método de autenticación |
Firmas RSA |
Firmas RSA |
Grupo DH |
grupo2 |
grupo2 |
Algoritmo de autenticación |
SHA 1 |
SHA 1 |
Algoritmo de cifrado |
3des-cbc |
3des-cbc |
Segundos de por vida |
3000 |
3000 |
Política de IKE |
ike_policy_ms_2_2_0 |
ike_policy_ms_2_0_0 |
Modo |
Principal |
Principal |
Propuesta |
ike_proposal_ms_2_2_0 |
ike_proposal_ms_2_0_0 |
Certificado |
local7_neg |
local7_moji |
Política |
ike_policy |
ike_policy |
Dirección de puerta de enlace |
10.0.1.2 |
192.0.2.0 |
Identidad remota |
company.net de FQDN |
company.net de FQDN |
Identidad local |
company.net de FQDN |
company.net de FQDN |
Interfaz externa |
GE-1/3/0 |
GE-1/3/0 |
Versión |
1 |
1 |
En la Tabla 2 se muestran las opciones de fase 2 utilizadas en este ejemplo.
Opción |
Par A |
Par B |
|---|---|---|
Propuesta IPsec |
ipsec_proposal_ms_2_2_0 |
ipsec_proposal_ms_2_0_0 |
Protocolo |
Esp |
Esp |
Algoritmo de autenticación |
HMAC-SHA1-96 |
HMAC-SHA1-96 |
Algoritmo de cifrado |
3des-cbc |
3des-cbc |
Segundos de por vida |
2000 |
2000 |
Directiva IPsec |
ipsec_policy_ms_2_2_0 |
ipsec_policy_ms_2_0_0 |
Claves PFC |
grupo2 |
grupo2 |
Propuesta |
ipsec_proposal_ms_2_2_0 |
ipsec_proposal_ms_2_0_0 |
VPN |
test_vpn |
test_vpn |
Política |
ipsec_policy |
ipsec_policy |
Establecer túneles |
- |
Inmediatamente |
Topología
En la figura 1 se muestran los dispositivos del mismo nivel que se configuran en este ejemplo.
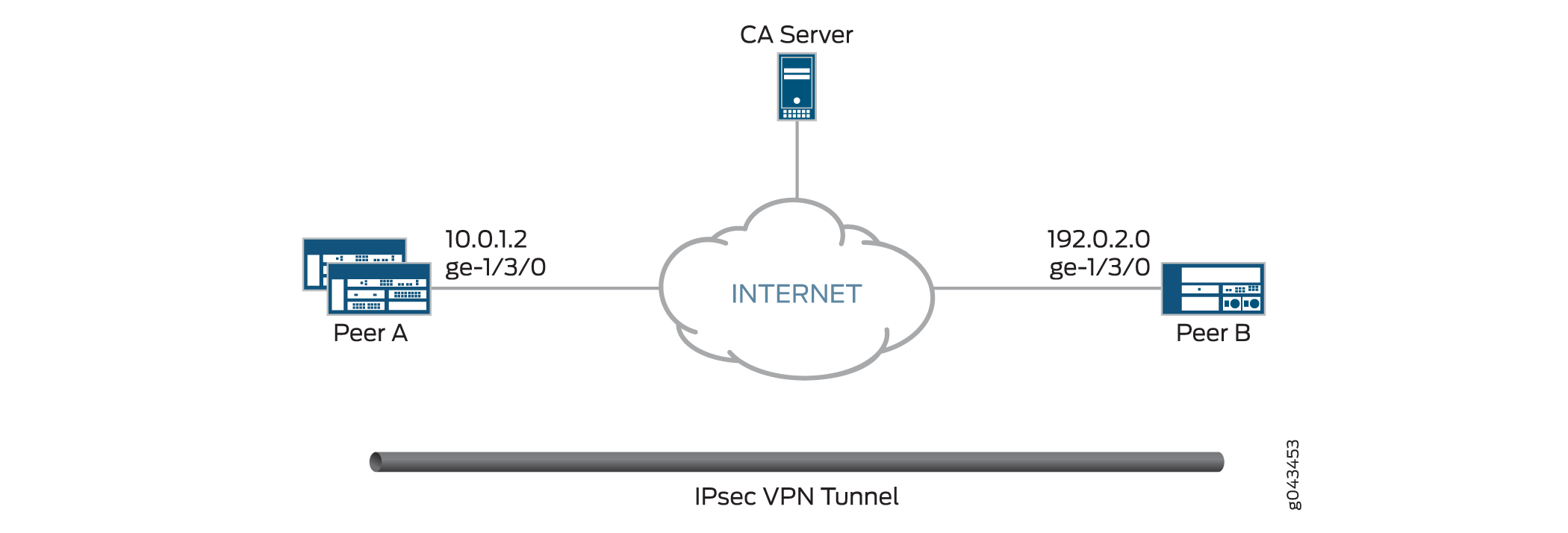 de configuración de OCSP
de configuración de OCSP
Configuración
Configuración del par A
Configuración rápida de CLI
Para configurar rápidamente la VPN par A para que use OCSP, copie los siguientes comandos, péguelos en un archivo de texto, elimine los saltos de línea, cambie los detalles necesarios para que coincidan con su configuración de red, copie y pegue los comandos en la CLI en el nivel de jerarquía [edit] y, a continuación, ingrese commit desde el modo de configuración.
set interfaces ge-1/3/0 unit 0 family inet address 10.0.1.2 set interfaces ms-2/2/0 unit 0 family inet set interfaces ms-2/2/0 unit 1 family inet set interfaces ms-2/2/0 unit 1 family inet6 set interfaces ms-2/2/0 unit 1 service-domain inside set interfaces ms-2/2/0 unit 2 family inet set interfaces ms-2/2/0 unit 2 family inet6 set interfaces ms-2/2/0 unit 2 service-domain outside set security pki ca-profile Root ca-identity Root set security pki ca-profile Root enrollment url http://10.1.1.1:8080/scep/Root/ set security pki ca-profile Root revocation-check ocsp url http://10.157.88.56:8210/Root/ set security pki ca-profile Root revocation-check use-ocsp set security pki ca-profile Root revocation-check ocsp disable-responder-revocation-check set security pki ca-profile Root revocation-check ocsp connection-failure fallback-crl set services ipsec-vpn ike proposal ike_prop authentication-method rsa-signatures set services service-set ips_ss1 next-hop-service inside-service-interface ms-2/2/0.1 set services service-set ips_ss1 next-hop-service outside-service-interface ms-2/2/0.2 set services service-set ips_ss1 ipsec-vpn-options local-gateway 10.0.1.2 set services service-set ips_ss1 ipsec-vpn-rules vpn_rule_ms_2_2_01 set services ipsec-vpn rule vpn_rule_ms_2_2_01 term term11 from source-address 203.0.113.0/24 set services ipsec-vpn rule vpn_rule_ms_2_2_01 term term11 from destination-address 198.51.100.0/24 set services ipsec-vpn rule vpn_rule_ms_2_2_01 term term11 then remote-gateway 192.0.2.0 set services ipsec-vpn rule vpn_rule_ms_2_2_01 term term11 then dynamic ike-policy ike_policy_ms_2_2_0 set services ipsec-vpn rule vpn_rule_ms_2_2_01 term term11 then dynamic ipsec-policy ipsec_policy_ms_2_2_0 set services ipsec-vpn rule vpn_rule_ms_2_2_01 match-direction input set services ipsec-vpn ipsec proposal ipsec_proposal_ms_2_2_0 protocol esp set services ipsec-vpn ipsec proposal ipsec_proposal_ms_2_2_0 authentication-algorithm hmac-sha1-96 set services ipsec-vpn ipsec proposal ipsec_proposal_ms_2_2_0 encryption-algorithm 3des-cbc set services ipsec-vpn ipsec proposal ipsec_proposal_ms_2_2_0 lifetime-seconds 2000 set services ipsec-vpn ipsec policy ipsec_policy_ms_2_2_0 proposals ipsec_proposal_ms_2_2_0 set services ipsec-vpn ike proposal ike_proposal_ms_2_2_0 authentication-method rsa-signatures set services ipsec-vpn ike proposal ike_proposal_ms_2_2_0 dh-group group2 set services ipsec-vpn ike proposal ike_proposal_ms_2_2_0 lifetime-seconds 3000 set services ipsec-vpn ike policy ike_policy_ms_2_2_0 mode main set services ipsec-vpn ike policy ike_policy_ms_2_2_0 version 1 set services ipsec-vpn ike policy ike_policy_ms_2_2_0 proposals ike_proposal_ms_2_2_0 set services ipsec-vpn ike policy ike_policy_ms_2_2_0 local-id fqdn company.net set services ipsec-vpn ike policy ike_policy_ms_2_2_0 local-certificate local7_neg set services ipsec-vpn ike policy ike_policy_ms_2_2_0 remote-id fqdn company.net set services ipsec-vpn traceoptions level all set services ipsec-vpn traceoptions flag all set services ipsec-vpn establish-tunnels immediately
Procedimiento paso a paso
En el ejemplo siguiente es necesario navegar por varios niveles en la jerarquía de configuración. Para obtener instrucciones sobre cómo hacerlo, consulte Uso del editor de CLI en el modo de configuración de la Guía del usuario de CLI.
Para configurar la VPN del mismo nivel A para que use OCSP:
Configurar interfaces.
[edit interfaces] set interfaces ge-1/3/0 unit 0 family inet address 10.0.1.2 set interfaces ms-2/2/0 unit 0 family inet set interfaces ms-2/2/0 unit 1 family inet set interfaces ms-2/2/0 unit 1 family inet6 set interfaces ms-2/2/0 unit 1 service-domain inside set interfaces ms-2/2/0 unit 2 family inet set interfaces ms-2/2/0 unit 2 family inet6 set interfaces ms-2/2/0 unit 2 service-domain outside
Configure el perfil de CA.
[edit security pki ca-profile Root] set security pki ca-profile Root ca-identity Root set security pki ca-profile Root enrollment url http://10.1.1.1:8080/scep/Root/ set security pki ca-profile Root revocation-check ocsp url http://10.157.88.56:8210/Root/ set security pki ca-profile Root revocation-check use-ocsp set security pki ca-profile Root revocation-check ocsp disable-responder-revocation-check set security pki ca-profile Root revocation-check ocsp connection-failure fallback-crl
Configure las opciones de la fase 1.
[edit services ipsec-vpn ike proposal ike_proposal_ms_2_2_0] set services ipsec-vpn ike proposal ike_proposal_ms_2_2_0 authentication-method rsa-signatures set services ipsec-vpn ike proposal ike_proposal_ms_2_2_0 dh-group group2 set services ipsec-vpn ike proposal ike_proposal_ms_2_2_0 lifetime-seconds 3000 [edit services ipsec-vpn ike policy ike_policy_ms_2_2_0] set services ipsec-vpn ike policy ike_policy_ms_2_2_0 mode main set services ipsec-vpn ike policy ike_policy_ms_2_2_0 version 1 set services ipsec-vpn ike policy ike_policy_ms_2_2_0 proposals ike_proposal_ms_2_2_0 set services ipsec-vpn ike policy ike_policy_ms_2_2_0 local-id fqdn company.net set services ipsec-vpn ike policy ike_policy_ms_2_2_0 local-certificate local7_neg set services ipsec-vpn ike policy ike_policy_ms_2_2_0 remote-id fqdn company.net
Configure las opciones de la fase 2.
[edit services ipsec-vpn ipsec proposal ipsec_proposal_ms_2_2_0] set services ipsec-vpn ipsec proposal ipsec_proposal_ms_2_2_0 protocol esp set services ipsec-vpn ipsec proposal ipsec_proposal_ms_2_2_0 authentication-algorithm hmac-sha1-96 set services ipsec-vpn ipsec proposal ipsec_proposal_ms_2_2_0 encryption-algorithm 3des-cbc set services ipsec-vpn ipsec proposal ipsec_proposal_ms_2_2_0 lifetime-seconds 2000 [edit services ipsec-vpn ipsec policy ipsec_policy_ms_2_2_0] set services ipsec-vpn ipsec policy ipsec_policy_ms_2_2_0 proposals ipsec_proposal_ms_2_2_0 [edit services service-set ips_ss1] set services service-set ips_ss1 next-hop-service inside-service-interface ms-2/2/0.1 set services service-set ips_ss1 next-hop-service outside-service-interface ms-2/2/0.2 set services service-set ips_ss1 ipsec-vpn-options local-gateway 10.0.1.2 set services service-set ips_ss1 ipsec-vpn-rules vpn_rule_ms_2_2_01 [edit services ipsec-vpn rule vpn_rule_ms_2_2_01] set services ipsec-vpn rule vpn_rule_ms_2_2_01 term term11 from source-address 203.0.113.0/24 set services ipsec-vpn rule vpn_rule_ms_2_2_01 term term11 from destination-address 198.51.100.0/24 set services ipsec-vpn rule vpn_rule_ms_2_2_01 term term11 then remote-gateway 192.0.2.0 set services ipsec-vpn rule vpn_rule_ms_2_2_01 term term11 then dynamic ike-policy ike_policy_ms_2_2_0 set services ipsec-vpn rule vpn_rule_ms_2_2_01 term term11 then dynamic ipsec-policy ipsec_policy_ms_2_2_0 set services ipsec-vpn rule vpn_rule_ms_2_2_01 match-direction input
Resultados
Desde el modo de configuración, escriba los comandos , , show security pki ca-profile Rootshow services ipsec-vpn ikey show services ipsec-vpn ipsec para confirmar la show interfacesconfiguración. Si el resultado no muestra la configuración deseada, repita las instrucciones de configuración en este ejemplo para corregirla.
[edit]
user@host# show interfaces
ge-1/3/0 {
unit 0 {
family inet {
address 10.0.1.2/24;
}
}
}
ms-2/2/0 {
unit 0 {
family inet;
}
unit 1 {
family inet;
family inet6;
service-domain inside;
}
unit 2 {
family inet;
family inet6;
service-domain inside;
}
}
[edit]
user@host# show security pki ca-profile Root
ca-identity Root;
enrollment {
url http://10.1.1.1:8080/scep/Root/;
}
revocation-check {
ocsp {
url http://10.157.88.56:8210/Root/;
disable-responder-revocation-check;
connection-failure fallback-crl;
}
use-ocsp;
}
[edit]
user@host# show services ipsec-vpn ike
proposal ike_proposal_ms_2_2_0 {
authentication-method rsa-signatures;
dh-group group2;
lifetime-seconds 3000;
}
policy ike_policy_ms_2_2_0 {
mode main;
version 1;
proposals ike_proposal_ms_2_2_0;
local-id fqdn company.net;
local-certificate local7_neg;
remote-id fqdn company.net;
}
[edit]
user@host# show services ipsec-vpn ipsec
proposal ipsec_proposal_ms_2_2_0 {
protocol esp;
authentication-algorithm hmac-sha1-96;
encryption-algorithm 3des-cbc;
lifetime-seconds 2000;
}
policy ipsec_policy_ms_2_2_0 {
proposals ipsec_proposal_ms_2_2_0;
}
Si ha terminado de configurar el dispositivo, ingrese commit desde el modo de configuración.
Configuración del par B
Configuración rápida de CLI
Para configurar rápidamente la VPN par B para que use OCSP, copie los siguientes comandos, péguelos en un archivo de texto, elimine los saltos de línea, cambie los detalles necesarios para que coincidan con su configuración de red, copie y pegue los comandos en la CLI en el nivel de jerarquía [edit] y, a continuación, ingrese commit desde el modo de configuración.
set interfaces ge-1/3/0 unit 0 family inet address 192.0.2.0/24 set interfaces ms-2/0/0 unit 0 family inet set interfaces ms-2/0/0 unit 1 family inet set interfaces ms-2/0/0 unit 1 family inet6 set interfaces ms-2/0/0 unit 1 service-domain inside set interfaces ms-2/0/0 unit 2 family inet set interfaces ms-2/0/0 unit 2 family inet6 set interfaces ms-2/0/0 unit 2 service-domain outside set security pki ca-profile Root ca-identity Root set security pki ca-profile Root enrollment url http://10.1.1.1:8080/scep/Root/ set security pki ca-profile Root revocation-check ocsp url http://10.157.88.56:8210/Root/ set security pki ca-profile Root revocation-check use-ocsp set security pki ca-profile Root revocation-check ocsp disable-responder-revocation-check set security pki ca-profile Root revocation-check ocsp connection-failure fallback-crl set services service-set ips_ss1 next-hop-service inside-service-interface ms-2/0/0.1 set services service-set ips_ss1 next-hop-service outside-service-interface ms-2/0/0.2 set services service-set ips_ss1 ipsec-vpn-options local-gateway 192.0.2.0 set services service-set ips_ss1 ipsec-vpn-rules vpn_rule_ms_2_0_01 set services ipsec-vpn rule vpn_rule_ms_2_0_01 term term11 from source-address 203.0.113.0/24 set services ipsec-vpn rule vpn_rule_ms_2_0_01 term term11 from destination-address 198.51.100.0/24 set services ipsec-vpn rule vpn_rule_ms_2_0_01 term term11 then remote-gateway 10.0.1.2 set services ipsec-vpn rule vpn_rule_ms_2_0_01 term term11 then dynamic ike-policy ike_policy_ms_2_0_0 set services ipsec-vpn rule vpn_rule_ms_2_0_01 term term11 then dynamic ipsec-policy ipsec_policy_ms_2_0_0 set services ipsec-vpn rule vpn_rule_ms_2_0_01 match-direction input set services ipsec-vpn ipsec proposal ipsec_proposal_ms_2_0_0 protocol esp set services ipsec-vpn ipsec proposal ipsec_proposal_ms_2_0_0 authentication-algorithm hmac-sha1-96 set services ipsec-vpn ipsec proposal ipsec_proposal_ms_2_0_0 encryption-algorithm 3des-cbc set services ipsec-vpn ipsec proposal ipsec_proposal_ms_2_0_0 lifetime-seconds 2000 set services ipsec-vpn ipsec policy ipsec_policy_ms_2_0_0 proposals ipsec_proposal_ms_2_0_0 set services ipsec-vpn ike proposal ike_proposal_ms_2_0_0 authentication-method rsa-signatures set services ipsec-vpn ike proposal ike_proposal_ms_2_0_0 dh-group group2 set services ipsec-vpn ike proposal ike_proposal_ms_2_0_0 lifetime-seconds 3000 set services ipsec-vpn ike policy ike_policy_ms_2_0_0 mode main set services ipsec-vpn ike policy ike_policy_ms_2_0_0 version 1 set services ipsec-vpn ike policy ike_policy_ms_2_0_0 proposals ike_proposal_ms_2_0_0 set services ipsec-vpn ike policy ike_policy_ms_2_0_0 local-id fqdn company.net set services ipsec-vpn ike policy ike_policy_ms_2_0_0 local-certificate local7_moji set services ipsec-vpn ike policy ike_policy_ms_2_0_0 remote-id fqdn company.net set services ipsec-vpn traceoptions level all set services ipsec-vpn traceoptions flag all
Procedimiento paso a paso
En el ejemplo siguiente es necesario navegar por varios niveles en la jerarquía de configuración. Para obtener instrucciones sobre cómo hacerlo, consulte Uso del editor de CLI en el modo de configuración de la Guía del usuario de CLI.
Para configurar la VPN del mismo nivel B para que use OCSP:
Configurar interfaces.
[edit interfaces] set interfaces ge-1/3/0 unit 0 family inet address 192.0.2.0/24 set interfaces ms-2/0/0 unit 0 family inet set interfaces ms-2/0/0 unit 1 family inet set interfaces ms-2/0/0 unit 1 family inet6 set interfaces ms-2/0/0 unit 1 service-domain inside set interfaces ms-2/0/0 unit 2 family inet set interfaces ms-2/0/0 unit 2 family inet6 set interfaces ms-2/0/0 unit 2 service-domain outside
Configure el perfil de CA.
[edit security pki ca-profile Root] set security pki ca-profile Root ca-identity Root set security pki ca-profile Root enrollment url http://10.1.1.1:8080/scep/Root/ set security pki ca-profile Root revocation-check ocsp url http://10.157.88.56:8210/Root/ set security pki ca-profile Root revocation-check use-ocsp set security pki ca-profile Root revocation-check ocsp disable-responder-revocation-check set security pki ca-profile Root revocation-check ocsp connection-failure fallback-crl
Configure las opciones de la fase 1.
[edit services ipsec-vpn ike proposal ike_proposal_ms_2_0_0] set services ipsec-vpn ike proposal ike_proposal_ms_2_0_0 authentication-method rsa-signatures set services ipsec-vpn ike proposal ike_proposal_ms_2_0_0 dh-group group2 set services ipsec-vpn ike proposal ike_proposal_ms_2_0_0 lifetime-seconds 3000 [edit services ipsec-vpn ike policy ike_policy_ms_2_0_0] set services ipsec-vpn ike policy ike_policy_ms_2_0_0 mode main set services ipsec-vpn ike policy ike_policy_ms_2_0_0 version 1 set services ipsec-vpn ike policy ike_policy_ms_2_0_0 proposals ike_proposal_ms_2_0_0 set services ipsec-vpn ike policy ike_policy_ms_2_0_0 local-id fqdn company.net set services ipsec-vpn ike policy ike_policy_ms_2_0_0 local-certificate local7_moji set services ipsec-vpn ike policy ike_policy_ms_2_0_0 remote-id fqdn company.net
Configure las opciones de la fase 2.
[edit services ipsec-vpn ipsec proposal ipsec_proposal_ms_2_0_0] set services ipsec-vpn ipsec proposal ipsec_proposal_ms_2_0_0 protocol esp set services ipsec-vpn ipsec proposal ipsec_proposal_ms_2_0_0 authentication-algorithm hmac-sha1-96 set services ipsec-vpn ipsec proposal ipsec_proposal_ms_2_0_0 encryption-algorithm 3des-cbc set services ipsec-vpn ipsec proposal ipsec_proposal_ms_2_0_0 lifetime-seconds 2000 [edit services ipsec-vpn ipsec policy ipsec_policy_ms_2_0_0] set services ipsec-vpn ipsec policy ipsec_policy_ms_2_0_0 proposals ipsec_proposal_ms_2_0_0 [edit services service-set ips_ss1] set services service-set ips_ss1 next-hop-service inside-service-interface ms-2/0/0.1 set services service-set ips_ss1 next-hop-service outside-service-interface ms-2/0/0.2 set services service-set ips_ss1 ipsec-vpn-options local-gateway 192.0.2.0 set services service-set ips_ss1 ipsec-vpn-rules vpn_rule_ms_2_0_01 [edit services ipsec-vpn rule vpn_rule_ms_2_0_01] set services ipsec-vpn rule vpn_rule_ms_2_0_01 term term11 from source-address 203.0.113.0/24 set services ipsec-vpn rule vpn_rule_ms_2_0_01 term term11 from destination-address 198.51.100.0/24 set services ipsec-vpn rule vpn_rule_ms_2_0_01 term term11 then remote-gateway 10.0.1.2 set services ipsec-vpn rule vpn_rule_ms_2_0_01 term term11 then dynamic ike-policy ike_policy_ms_2_0_0 set services ipsec-vpn rule vpn_rule_ms_2_0_01 term term11 then dynamic ipsec-policy ipsec_policy_ms_2_0_0 set services ipsec-vpn rule vpn_rule_ms_2_0_01 match-direction input
Resultados
Desde el modo de configuración, escriba los comandos , , show security pki ca-profile Rootshow services ipsec-vpn ikey show services ipsec-vpn ipsec para confirmar la show interfacesconfiguración. Si el resultado no muestra la configuración deseada, repita las instrucciones de configuración en este ejemplo para corregirla.
[edit]
user@host# show interfaces
ge-1/3/0 {
unit 0 {
family inet {
address 192.0.2.0/24;
}
}
}
ms-2/0/0 {
unit 0 {
family inet;
}
unit 1 {
family inet;
family inet6;
service-domain inside;
}
unit 2 {
family inet;
family inet6;
service-domain inside;
}
}
[edit]
user@host# show security pki ca-profile Root
ca-identity Root;
enrollment {
url http://10.1.1.1:8080/scep/Root/;
}
revocation-check {
ocsp {
url http://10.157.88.56:8210/Root/;
disable-responder-revocation-check;
connection-failure fallback-crl;
}
use-ocsp;
}
[edit]
user@host# show services ipsec-vpn ike
proposal ike_proposal_ms_2_0_0 {
authentication-method rsa-signatures;
dh-group group2;
lifetime-seconds 3000;
}
policy ike_policy_ms_2_0_0 {
mode main;
version 1;
proposals ike_proposal_ms_2_0_0;
local-id fqdn company.net;
local-certificate local7_moji;
remote-id fqdn company.net;
}
[edit]
user@host# show services ipsec-vpn ipsec
proposal ipsec_proposal_ms_2_0_0 {
protocol esp;
authentication-algorithm hmac-sha1-96;
encryption-algorithm 3des-cbc;
lifetime-seconds 2000;
}
policy ipsec_policy_ms_2_0_0 {
proposals ipsec_proposal_ms_2_0_0;
}
Si ha terminado de configurar el dispositivo, ingrese commit desde el modo de configuración.
Verificación
Confirme que la configuración funciona correctamente.
- Comprobación de certificados de CA
- Verificación de certificados locales
- Verificación del estado de la fase 1 de IKE
- Comprobación del estado de fase 2 de IPsec
Comprobación de certificados de CA
Propósito
Compruebe la validez de un certificado de CA en cada dispositivo del mismo nivel.
Acción
En el modo operativo, escriba el show security pki ca-certificate ca-profile Root comando o show security pki ca-certificate ca-profile Root detail .
user@host> show security pki ca-certificate ca-profile Root
Certificate identifier: Root
Issued to: Root, Issued by: C = US, O = Juniper, CN = Root
Validity:
Not before: 07- 3-2015 10:54 UTC
Not after: 07- 1-2020 10:54 UTC
Public key algorithm: rsaEncryption(2048 bits)
user@host> show security pki ca-certificate ca-profile Root detail
Certificate identifier: Root
Certificate version: 3
Serial number: 0000a17f
Issuer:
Organization: Juniper, Country: US, Common name: Root
Subject:
Organization: Juniper, Country: US, Common name: Root
Subject string:
C=US, O=Juniper, CN=Root
Validity:
Not before: 07- 3-2015 10:54 UTC
Not after: 07- 1-2020 10:54 UTC
Public key algorithm: rsaEncryption(2048 bits)
30:82:01:0a:02:82:01:01:00:c6:38:e9:03:69:5e:45:d8:a3:ea:3d
2e:e3:b8:3f:f0:5b:39:f0:b7:35:64:ed:60:a0:ba:89:28:63:29:e7
27:82:47:c4:f6:41:53:c8:97:d7:1e:3c:ca:f0:a0:b9:09:0e:3d:f8
76:5b:10:6f:b5:f8:ef:c5:e8:48:b9:fe:46:a3:c6:ba:b5:05:de:2d
91:ce:20:12:8f:55:3c:a6:a4:99:bb:91:cf:05:5c:89:d3:a7:dc:a4
d1:46:f2:dc:36:f3:f0:b5:fd:1d:18:f2:e6:33:d3:38:bb:44:8a:19
ad:e0:b1:1a:15:c3:56:07:f9:2d:f6:19:f7:cd:80:cf:61:de:58:b8
a3:f5:e0:d1:a3:3a:19:99:80:b0:63:03:1f:25:05:cc:b2:0c:cd:18
ef:37:37:46:91:20:04:bc:a3:4a:44:a9:85:3b:50:33:76:45:d9:ba
26:3a:3b:0d:ff:82:40:36:64:4e:ea:6a:d8:9b:06:ff:3f:e2:c4:a6
76:ee:8b:58:56:a6:09:d3:4e:08:b0:64:60:75:f3:e2:06:91:64:73
d2:78:e9:7a:cb:8c:57:0e:d1:9a:6d:3a:4a:9e:5b:d9:e4:a2:ef:31
5d:2b:2b:53:ab:a1:ad:45:49:fd:a5:e0:8b:4e:0b:71:52:ca:6b:fa
8b:0e:2c:7c:7b:02:03:01:00:01
Signature algorithm: sha1WithRSAEncryption
Distribution CRL:
http://10.1.1.1:8080/crl-as-der/currentcrl-45.crl?id=45
Authority Information Access OCSP:
http://10.1.1.1:8090/Root/
Use for key: CRL signing, Certificate signing, Key encipherment, Digital signature
Fingerprint:
ed:ce:ec:13:1a:d2:ab:0a:76:e5:26:6d:2c:29:5d:49:90:57:f9:41 (sha1)
af:87:07:69:f0:3e:f7:c6:b8:2c:f8:df:0b:ae:b0:28 (md5)
En este ejemplo, se utilizan direcciones IP en las direcciones URL de la configuración del perfil de CA. Si las direcciones IP no se usan con certificados emitidos por CA o certificados de CA, el DNS debe configurarse en la configuración del dispositivo. DNS debe poder resolver el host en la CRL de distribución y en la URL de CA en la configuración del perfil de CA. Además, debe tener acceso de red al mismo host para recibir comprobaciones de revocación.
Significado
El resultado muestra los detalles y la validez del certificado de CA en cada par de la siguiente manera:
C—País.O—Organización.CN—Nombre común.Not before—Fecha de inicio de validez.Not after—Fecha de finalización de la validez.
Verificación de certificados locales
Propósito
Compruebe la validez de un certificado local en cada dispositivo del mismo nivel.
Acción
Desde el modo operativo, ingrese el show security pki local-certificate certificate-id localcert1 detail comando.
user@host> show security pki local-certificate certificate-id local7_neg detail
Certificate identifier: local7_neg
Certificate version: 3
Serial number: 0007d964
Issuer:
Organization: juniper, Country: us, Common name: Subca2
Subject:
Organization: juniper, Organizational unit: marketing, State: california, Locality: sunnyvale, Common name: local, Domain component: juniper
Subject string:
DC=juniper, CN=local, OU=marketing, O=juniper, L=sunnyvale, ST=california, C=us
Alternate subject: "test@company.net", company.net, 10.0.0.2
Validity:
Not before: 04- 5-2016 03:30 UTC
Not after: 07- 1-2020 10:54 UTC
Public key algorithm: rsaEncryption(1024 bits)
30:81:89:02:81:81:00:b9:44:42:0e:26:5a:46:8e:a7:9c:b9:15:a5
f1:38:e4:59:59:9d:84:75:ee:7a:64:ca:0a:a7:68:3b:2b:0c:dc:a8
de:60:df:07:80:23:58:7d:56:dd:4f:50:de:a4:57:f1:a0:df:a9:7a
6c:3d:e0:6d:7a:cf:ef:af:95:1b:12:7a:c4:54:61:12:db:65:0c:f9
25:40:2d:01:71:21:8a:fc:fc:f6:9d:db:5a:63:ca:1a:92:2b:a3:98
f6:6b:e4:23:67:53:92:6a:5e:ad:ae:d7:82:ab:32:c1:60:6f:01:14
fd:46:bd:3f:b3:6b:fd:e6:41:de:6d:94:0d:6f:ad:02:03:01:00:01
Signature algorithm: sha256WithRSAEncryption
Distribution CRL:
http://10.1.1.1:8080/crl-as-der/currentcrl-1925.crl?id=1925
Authority Information Access OCSP:
http://10.204.128.120:8090/Subca2/
Fingerprint:
69:00:fe:e1:81:37:ab:54:27:81:ce:57:11:a1:f2:d8:00:e7:e6:c7 (sha1)
1e:27:93:a1:96:eb:28:0c:dc:f3:50:20:bb:eb:ed:57 (md5)
Auto-re-enrollment:
Status: Disabled
Next trigger time: Timer not started
Significado
El resultado muestra los detalles y la validez de un certificado local en cada par de la siguiente manera:
DC: componente de dominio.CN—Nombre común.OU—Unidad organizativa.O—Organización.L—LocalidadST—Estado.C—País.Not before—Fecha de inicio de validez.Not after—Fecha de finalización de la validez.
Verificación del estado de la fase 1 de IKE
Propósito
Verifique el estado de la fase 1 de IKE en cada dispositivo del mismo nivel.
Acción
Desde el modo operativo, ingrese el show services ipsec-vpn ike security-associations comando.
user@host> show services ipsec-vpn ike security-associations Remote Address State Initiator cookie Responder cookie Exchange type 192.0.2.0 Matured 63b3445edda507fb 2715ee5895ed244d Main
Desde el modo operativo, ingrese el show services ipsec-vpn ike security-associations detail comando.
user@host> show services ipsec-vpn ike security-associations detail IKE peer 192.0.2.0 Role: Initiator, State: Matured Initiator cookie: 63b3445edda507fb, Responder cookie: 2715ee5895ed244d Exchange type: Main, Authentication method: RSA-signatures Local: 10.0.1.2, Remote: 192.0.2.0 Lifetime: Expires in 788 seconds Algorithms: Authentication : hmac-sha1-96 Encryption : 3des-cbc Pseudo random function: hmac-sha1 Diffie-Hellman group : 2 Traffic statistics: Input bytes : 3100 Output bytes : 4196 Input packets: 7 Output packets: 9 Flags: IKE SA created IPSec security associations: 4 created, 4 deleted
Significado
El flags campo del resultado muestra que se ha creado una asociación de seguridad IKE.
Comprobación del estado de fase 2 de IPsec
Propósito
Compruebe el estado de fase 2 de IPsec en cada dispositivo del mismo nivel.
Acción
Desde el modo operativo, ingrese el show services ipsec-vpn ipsec security-associations comando.
user@host> show services ipsec-vpn ipsec security-associations
Service set: ips_ss1, IKE Routing-instance: default
Rule: vpn_rule_ms_2_2_01, Term: term11, Tunnel index: 1
Local gateway: 10.0.1.2, Remote gateway: 192.0.2.0
IPSec inside interface: ms-2/2/0.1, Tunnel MTU: 1500
UDP encapsulate: Disabled, UDP Destination port: 0
Direction SPI AUX-SPI Mode Type Protocol
inbound 2151932129 0 tunnel dynamic ESP
outbound 4169263669 0 tunnel dynamic ESP
Desde el modo operativo, ingrese el show services ipsec-vpn ipsec security-associations detail comando.
user@host> show services ipsec-vpn ipsec security-associations detail
Service set: ips_ss1, IKE Routing-instance: default
Rule: vpn_rule_ms_2_2_01, Term: term11, Tunnel index: 1
Local gateway: 10.0.1.2, Remote gateway: 192.0.2.0
IPSec inside interface: ms-2/2/0.1, Tunnel MTU: 1500
UDP encapsulate: Disabled, UDP Destination port: 0
Local identity: ipv4_subnet(any:0,[0..7]=80.0.0.0/16)
Remote identity: ipv4_subnet(any:0,[0..7]=30.0.0.0/16)
Direction: inbound, SPI: 3029124496, AUX-SPI: 0
Mode: tunnel, Type: dynamic, State: Installed
Protocol: ESP, Authentication: hmac-sha1-96, Encryption: 3des-cbc
Soft lifetime: Expires in 840 seconds
Hard lifetime: Expires in 1273 seconds
Anti-replay service: Enabled, Replay window size: 4096
Copy ToS: Disabled, ToS value: 0
Copy TTL: Disabled, TTL value: 64
Direction: outbound, SPI: 4046774180, AUX-SPI: 0
Mode: tunnel, Type: dynamic, State: Installed
Protocol: ESP, Authentication: hmac-sha1-96, Encryption: 3des-cbc
Soft lifetime: Expires in 840 seconds
Hard lifetime: Expires in 1273 seconds
Anti-replay service: Enabled, Replay window size: 4096
Copy ToS: Disabled, ToS value: 0
Copy TTL: Disabled, TTL value: 64
Significado
El resultado muestra los detalles de las asociaciones de seguridad ipsec.
