이 페이지에서
예: EVPN-VXLAN에 기반한 필터 기반 포워딩
요구 사항
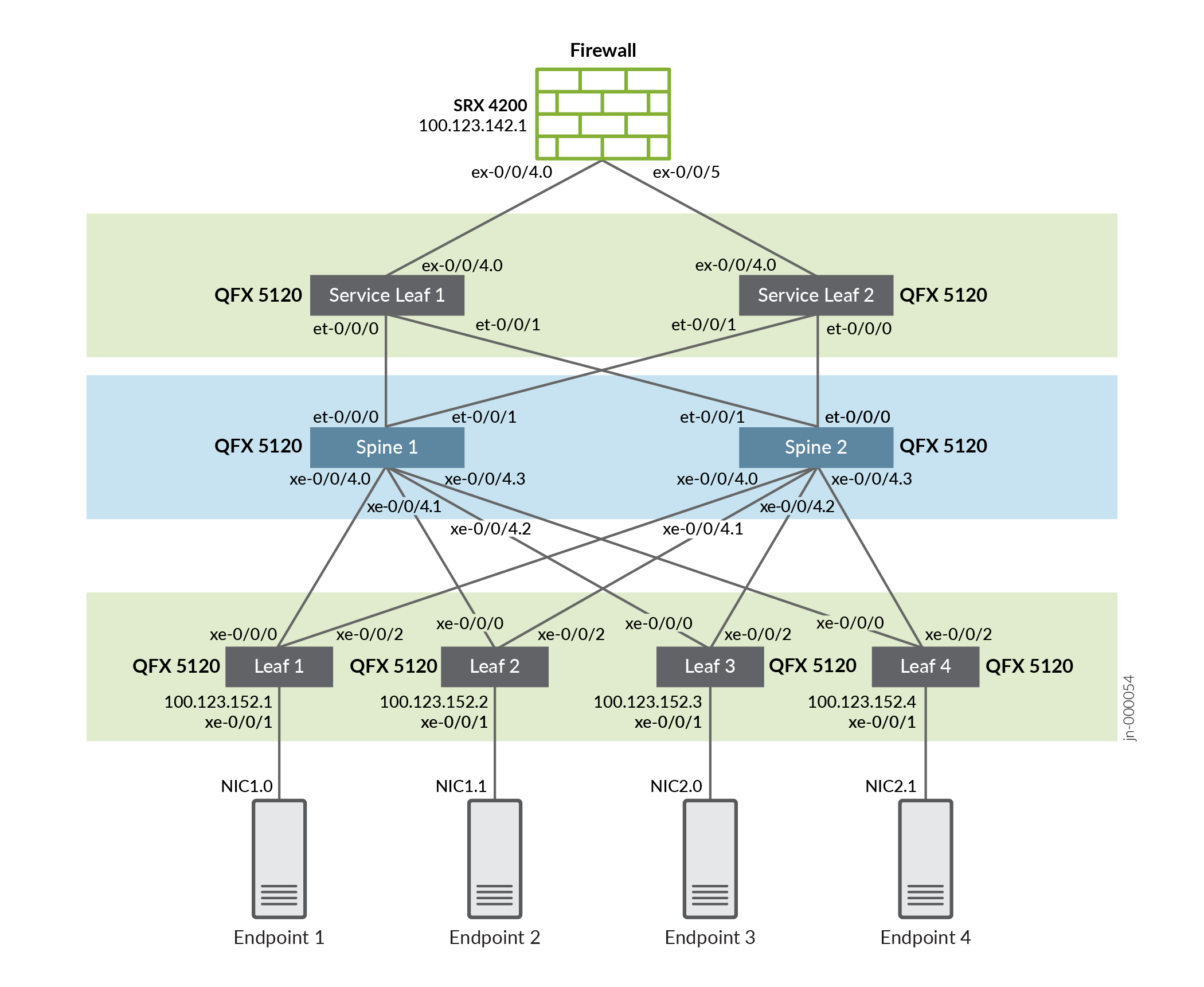
이 EVPN-VXLAN 패브릭은 에지 라우팅 브리징(ERB) 모델을 사용합니다. VLAN 간 라우팅은 리프 디바이스에서 발생합니다. 이 예는 ERB 패브릭이 제자리에 있다고 가정하므로 보안 검사를 위한 플로우를 선택하기 위해 FBF를 사용하는 데 초점을 맞출 수 있습니다. 예제 끝의 세부 구성은 특정 플로우를 검사하는 데 필요한 FBF 외에 작동하는 ERB 기준선에 필요한 구성을 보여줍니다. 예제 토폴로지는 아래에 표시됩니다.
ERB EVPN-VXLAN 패브릭에 대한 배경 정보 및 구성 세부 정보는 EVPN-VXLAN 아키텍처 및 기술을 참조하십시오.
토폴로지
이 NCE에서는 4개의 서버 리프 스위치, 2개의 언더레이 스파인 스위치, 2개의 서비스 리프 스위치 및 방화벽으로 구성된 EVPN-VXLAN 패브릭에 대해 설명합니다.
스파인 노드
- Junos 버전 20.2R2를 실행하는 QFX5120-32C 시리즈 스위치
서버 리프
- Junos 버전 20.3R1을 실행하는 QFX5120-48Y 시리즈 스위치
서비스 리프
- Junos 버전 20.2R2를 실행하는 QFX5120-32C 시리즈 스위치
방화벽
- Junos 버전 20.1R2를 실행하는 SRX 4200 서비스 게이트웨이
단계별 구성
다음 구성에서는 엔드포인트-1을 서버 리프-1에 연결합니다. 또한 새로운 라우팅 인스턴스를 생성하여 INSPECT_VRF Service Leaf-1 및 Service Leaf-2를 사용하여 type-5 경로를 내보내고 가져오도록 구성합니다. 필터 기반 포워딩을 사용하여 엔드포인트-1에서 엔드포인트-2로 트래픽을 INSPECT_VRF 리디렉션합니다.
서버 리프-1
-
Server Leaf-1에서 INSPECT_VRF 라우팅 인스턴스를 설정합니다.
set routing-instances INSPECT_VRF routing-options multipath set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes vni 9991 set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes export T5_INSPECT_EXPORT set routing-instances INSPECT_VRF description "VRF for Firewall-1" set routing-instances INSPECT_VRF instance-type vrf set routing-instances INSPECT_VRF interface lo0.991 set routing-instances INSPECT_VRF route-distinguisher 10.80.224.140:9991 set routing-instances INSPECT_VRF vrf-target target:64730:991 set routing-instances INSPECT_VRF vrf-table-label set interfaces lo0 unit 991 family inet address 192.168.91.1/32
-
엔드포인트-1에 대한 정적 경로를 추가하여 Tenant1_VRF.
set routing-instances INSPECT_VRF routing-options static route 10.1.110.11/32 next-table Tenant1_VRF.inet.0
-
Inspect_VRF 방화벽이 트래픽을 수신할 수 있도록 엔드포인트-1에 대한 유형 5 정적 호스트 경로를 보급해야 합니다. 또한 방화벽은 Leaf 1의 기본 경로를 보급해야 합니다.
set policy-options policy-statement T5_INSPECT_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_INSPECT_EXPORT term fm_direct then accept set policy-options policy-statement T5_INSPECT_EXPORT term fm_static from protocol static set policy-options policy-statement T5_INSPECT_EXPORT term fm_static then accept
-
이제 Leaf-1에 대한 방화벽 필터를 설정해야 합니다. 필터는 엔드포인트-1에서 엔드포인트-2로 트래픽을 일치시키고 이러한 패킷을 INSPECT_VRF 리디렉션합니다. 다른 모든 트래픽은 Tenant1_VRF 평소와 같이 라우팅됩니다.
set firewall family inet filter SecureTraffic term EP1_to_EP2 from source-address 10.1.110.11/32 set firewall family inet filter SecureTraffic term EP1_to_EP2 from destination-address 10.1.111.21/32 set firewall family inet filter SecureTraffic term EP1_to_EP2 then count EP1_to_EP2 set firewall family inet filter SecureTraffic term EP1_to_EP2 then routing-instance INSPECT_VRF set firewall family inet filter SecureTraffic term Allow_All then count Normal_Count set firewall family inet filter SecureTraffic term Allow_All then accept
-
Leaf-1에서는 IRB.110을 통과할 때 방화벽 필터를 VLAN 110 트래픽에 적용해야 합니다(이 인터페이스는 엔드포인트-1에 연결된 인터페이스임).
set interfaces irb unit 110 virtual-gateway-accept-data set interfaces irb unit 110 family inet filter input SecureTraffic set interfaces irb unit 110 family inet address 10.1.110.100/24 virtual-gateway-address 10.1.110.1 set interfaces irb unit 110 virtual-gateway-v4-mac e4:5d:37:11:10:01
서버 리프-2
다음으로 Service Leaf-1과 Service Leaf-2를 모두 사용하여 type-5 경로를 내보내고 가져오기 위해 Server Leaf-2에서 SECURE_VRF 라우팅 인스턴스를 생성해야 합니다. 이전과 마찬가지로 필터 기반 포워딩을 사용하여 엔드포인트-2에서 엔드포인트-1로 트래픽을 SECURE_VRF 리디렉션합니다.
-
Server Leaf-2에서 SECURE_VRF 라우팅 인스턴스를 설정합니다.
set routing-instances SECURE_VRF routing-options multipath set routing-instances SECURE_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances SECURE_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances SECURE_VRF protocols evpn ip-prefix-routes vni 9992 set routing-instances SECURE_VRF protocols evpn ip-prefix-routes export T5_SECURE_EXPORT set routing-instances SECURE_VRF description "VRF for SECURED FIREWALL TRAFFIC" set routing-instances SECURE_VRF instance-type vrf set routing-instances SECURE_VRF interface lo0.992 set routing-instances SECURE_VRF route-distinguisher 10.80.224.141:9992 set routing-instances SECURE_VRF vrf-target target:64730:992 set routing-instances SECURE_VRF vrf-table-label set interfaces lo0 unit 992 family inet address 192.168.92.2/32
-
Tenant1_VRF 포인트로 하는 엔드포인트-2에 대한 정적 경로를 구성합니다.
set routing-instances SECURE_VRF routing-options static route 10.1.111.21/32 next-table Tenant1_VRF.inet.0
-
SECURE_VRF 방화벽이 트래픽을 수신할 수 있도록 엔드포인트-2에 대한 유형 5 정적 호스트 경로를 보급해야 합니다. 또한 방화벽은 Leaf 2의 기본 경로를 보급해야 합니다.
set policy-options policy-statement T5_SECURE_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_SECURE_EXPORT term fm_direct then accept set policy-options policy-statement T5_SECURE_EXPORT term fm_static from protocol static set policy-options policy-statement T5_SECURE_EXPORT term fm_static then accept
-
이전과 마찬가지로 Leaf-2에 대한 방화벽 필터를 설정해야 합니다. 이번에는 필터가 엔드포인트-2에서 엔드포인트-1로의 트래픽과 일치하고 이러한 패킷을 SECURE_VRF 리디렉션합니다. 다른 모든 트래픽은 Tenant1_VRF 평소와 같이 라우팅됩니다.
set firewall family inet filter SecureResponseTraffic term EP2_to_EP1 from source-address 10.1.111.21/32 set firewall family inet filter SecureResponseTraffic term EP2_to_EP1 from destination-address 10.1.110.11/32 set firewall family inet filter SecureResponseTraffic term EP2_to_EP1 then count EP2_to_EP1 set firewall family inet filter SecureResponseTraffic term EP2_to_EP1 then routing-instance SECURE_VRF set firewall family inet filter SecureResponseTraffic term Allow_All then accept
-
마지막으로 Leaf-2에서는 방화벽 필터가 IRB.111을 통과할 때 VLAN 111 트래픽에 적용해야 합니다(이것이 엔드포인트-2에 연결된 인터페이스임).
set interfaces irb unit 111 virtual-gateway-accept-data set interfaces irb unit 111 family inet filter input SecureResponseTraffic set interfaces irb unit 111 family inet address 10.1.111.101/24 virtual-gateway-address 10.1.111.1 set interfaces irb unit 111 virtual-gateway-v4-mac e4:5d:37:11:11:01
서비스 리프-1
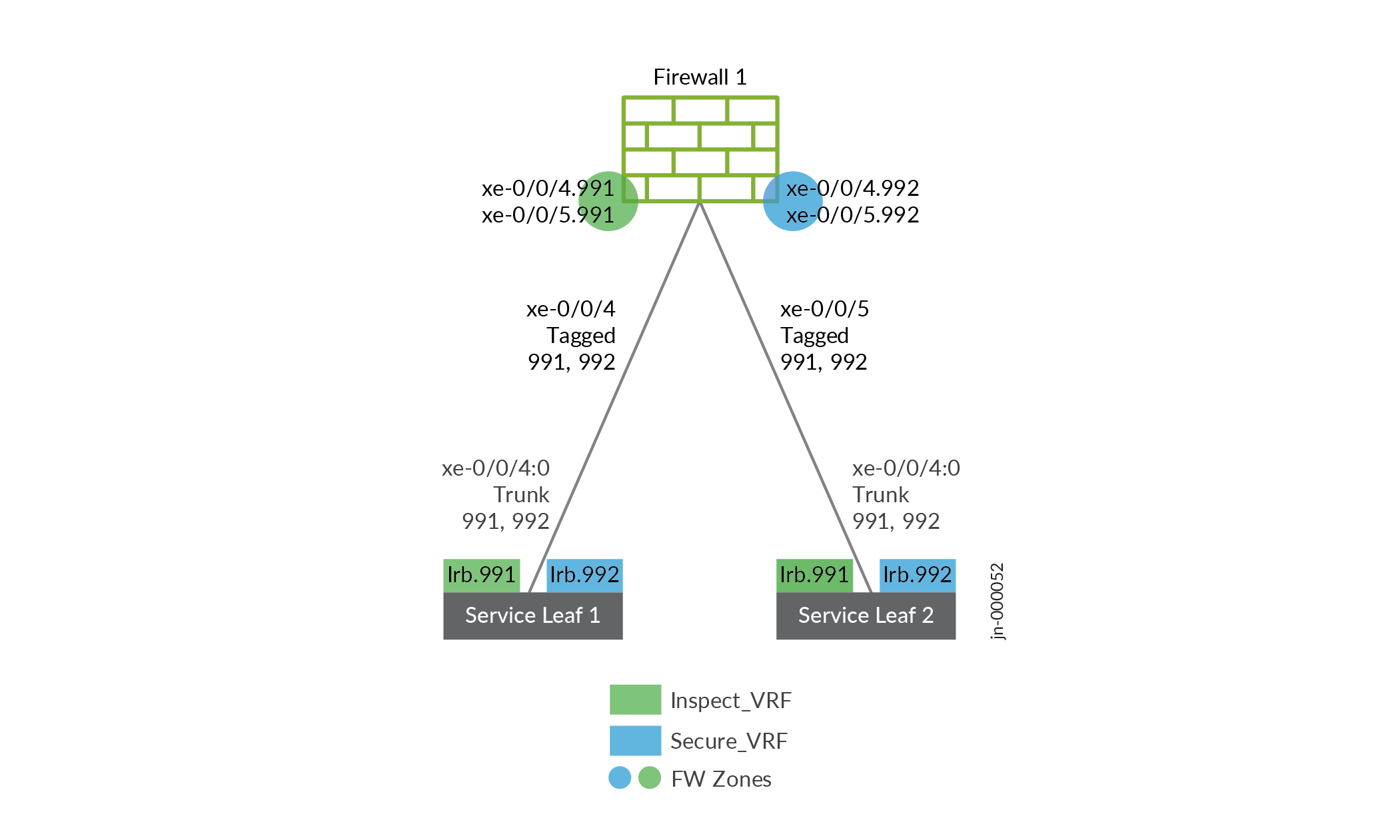
Service Leaf-1은 INSPECT_VRF 및 SECURE_VRF 라우팅 인스턴스를 모두 포함하며, 다음 그림과 같이 서비스 리프와 방화벽을 연결합니다. 인터페이스 IRB.991은 검사 VRF에 있고 인터페이스 IRB.992는 SECURE VRF에 있습니다.
서비스 리프는 두 라우팅 인스턴스 모두에서 기본 경로를 수신하는 방화벽과 EBGP 피어링을 설정합니다. Service Leaf-1은 Type-5를 사용하여 서버 리프에 기본 경로를 보급하고, 그로부터 엔드포인트-1 및 엔드포인트-2에 대한 특정 호스트 경로를 수신한 다음 EBGP를 사용하여 방화벽에 보급합니다.
-
서비스 리프에서 방화벽으로의 연결은 각각 IRB를 가진 VLAN 991 및 VLAN 992를 포함하는 트렁크 포트입니다. 인터페이스, 여기에 표시된 대로:
set interfaces xe-0/0/4:0 description "SRX Firewall 1: xe-0/0/4" set interfaces xe-0/0/4:0 mtu 9192 set interfaces xe-0/0/4:0 unit 0 family ethernet-switching interface-mode trunk set interfaces xe-0/0/4:0 unit 0 family ethernet-switching vlan members V991 set interfaces xe-0/0/4:0 unit 0 family ethernet-switching vlan members V992 set interfaces irb unit 991 family inet address 10.81.91.2/30 set interfaces irb unit 992 family inet address 10.81.92.2/30
-
Service Leaf-1에 라우팅 인스턴스를 설정해야 합니다.
set routing-instances INSPECT_VRF description "VRF for Firewall-1" set routing-instances INSPECT_VRF instance-type vrf set routing-instances INSPECT_VRF interface irb.991 set routing-instances INSPECT_VRF interface lo0.991 set routing-instances INSPECT_VRF route-distinguisher 10.80.224.138:9991 set routing-instances INSPECT_VRF vrf-target target:64730:991 set routing-instances INSPECT_VRF vrf-table-label set routing-instances INSPECT_VRF routing-options multipath set routing-instances INSPECT_VRF protocols bgp group Firewall-1 type external set routing-instances INSPECT_VRF protocols bgp group Firewall-1 export FW1_Export set routing-instances INSPECT_VRF protocols bgp group Firewall-1 local-as 64730 set routing-instances INSPECT_VRF protocols bgp group Firewall-1 neighbor 10.81.91.1 peer-as 64777 set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes vni 9991 set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes export T5_INSPECT_EXPORT set routing-instances SECURE_VRF description "VRF for SECURED FIREWALL TRAFFIC" set routing-instances SECURE_VRF instance-type vrf set routing-instances SECURE_VRF interface irb.992 set routing-instances SECURE_VRF interface lo0.992 set routing-instances SECURE_VRF route-distinguisher 10.80.224.138:9992 set routing-instances SECURE_VRF vrf-target target:64730:992 set routing-instances SECURE_VRF vrf-table-label set routing-instances SECURE_VRF routing-options multipath set routing-instances SECURE_VRF protocols bgp group Firewall-1 type external set routing-instances SECURE_VRF protocols bgp group Firewall-1 export FW1_Export set routing-instances SECURE_VRF protocols bgp group Firewall-1 local-as 64730 set routing-instances SECURE_VRF protocols bgp group Firewall-1 neighbor 10.81.92.1 peer-as 64777 set routing-instances SECURE_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances SECURE_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances SECURE_VRF protocols evpn ip-prefix-routes vni 9992 set routing-instances SECURE_VRF protocols evpn ip-prefix-routes export T5_SECURE_EXPORT set interfaces lo0 unit 991 family inet address 192.168.91.253/32 set interfaces lo0 unit 992 family inet address 192.168.92.253/32 set policy-options policy-statement T5_INSPECT_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_INSPECT_EXPORT term fm_direct then accept set policy-options policy-statement T5_INSPECT_EXPORT term Default_Route from route-filter 0.0.0.0/0 exact set policy-options policy-statement T5_INSPECT_EXPORT term Default_Route then accept set policy-options policy-statement T5_SECURE_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_SECURE_EXPORT term fm_direct then accept set policy-options policy-statement T5_SECURE_EXPORT term Default_Route from route-filter 0.0.0.0/0 exact set policy-options policy-statement T5_SECURE_EXPORT term Default_Route then accept set policy-options policy-statement FW1_Export from protocol evpn set policy-options policy-statement FW1_Export then accept
-
또한 Service Leaf-1에 정책 문을 설정해야 합니다.
set policy-options policy-statement T5_INSPECT_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_INSPECT_EXPORT term fm_direct then accept set policy-options policy-statement T5_INSPECT_EXPORT term Default_Route from route-filter 0.0.0.0/0 exact set policy-options policy-statement T5_INSPECT_EXPORT term Default_Route then accept set policy-options policy-statement T5_SECURE_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_SECURE_EXPORT term fm_direct then accept set policy-options policy-statement T5_SECURE_EXPORT term Default_Route from route-filter 0.0.0.0/0 exact set policy-options policy-statement T5_SECURE_EXPORT term Default_Route then accept set policy-options policy-statement FW1_Export from protocol evpn set policy-options policy-statement FW1_Export then accept
서비스 리프-2
Service Leaf-2의 구성은 서비스 리프-1 구성과 유사합니다.
-
여기에서 방화벽 인터커넥트 서비스 리프-2를 설정했습니다.
set interfaces xe-0/0/4:0 description "SRX Firewall-1: xe-0/0/5" set interfaces xe-0/0/4:0 mtu 9192 set interfaces xe-0/0/4:0 unit 0 family ethernet-switching interface-mode trunk set interfaces xe-0/0/4:0 unit 0 family ethernet-switching vlan members V991 set interfaces xe-0/0/4:0 unit 0 family ethernet-switching vlan members V992 set interfaces irb unit 991 family inet address 10.81.91.6/24 set interfaces irb unit 992 family inet address 10.81.92.6/24
-
여기에서 Service Leaf-2에 라우팅 인스턴스를 설정했습니다.
set routing-instances INSPECT_VRF description "VRF for Firewall-1" set routing-instances INSPECT_VRF instance-type vrf set routing-instances INSPECT_VRF interface irb.991 set routing-instances INSPECT_VRF interface lo0.991 set routing-instances INSPECT_VRF route-distinguisher 10.80.224.139:9991 set routing-instances INSPECT_VRF vrf-target target:64730:991 set routing-instances INSPECT_VRF vrf-table-label set routing-instances INSPECT_VRF routing-options multipath set routing-instances INSPECT_VRF protocols bgp group Firewall-1 type external set routing-instances INSPECT_VRF protocols bgp group Firewall-1 export FW1_Export set routing-instances INSPECT_VRF protocols bgp group Firewall-1 local-as 64730 set routing-instances INSPECT_VRF protocols bgp group Firewall-1 neighbor 10.81.91.5 peer-as 64777 set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes vni 9991 set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes export T5_INSPECT_EXPORT set routing-instances SECURE_VRF description "VRF for SECURED FIREWALL TRAFFIC" set routing-instances SECURE_VRF instance-type vrf set routing-instances SECURE_VRF interface irb.992 set routing-instances SECURE_VRF interface lo0.992 set routing-instances SECURE_VRF route-distinguisher 10.80.224.139:9992 set routing-instances SECURE_VRF vrf-target target:64730:992 set routing-instances SECURE_VRF vrf-table-label set routing-instances SECURE_VRF routing-options multipath set routing-instances SECURE_VRF protocols bgp group Firewall-1 type external set routing-instances SECURE_VRF protocols bgp group Firewall-1 export FW1_Export set routing-instances SECURE_VRF protocols bgp group Firewall-1 local-as 64730 set routing-instances SECURE_VRF protocols bgp group Firewall-1 neighbor 10.81.92.5 peer-as 64777 set routing-instances SECURE_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances SECURE_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances SECURE_VRF protocols evpn ip-prefix-routes vni 9992 set routing-instances SECURE_VRF protocols evpn ip-prefix-routes export T5_SECURE_EXPORT set interfaces lo0 unit 991 family inet address 192.168.91.254/32 set interfaces lo0 unit 992 family inet address 192.168.92.254/32
-
마지막으로 Service Leaf-2에 정책 문을 설정했습니다.
set policy-options policy-statement T5_INSPECT_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_INSPECT_EXPORT term fm_direct then accept set policy-options policy-statement T5_INSPECT_EXPORT term Default_Route from route-filter 0.0.0.0/0 exact set policy-options policy-statement T5_INSPECT_EXPORT term Default_Route then accept set policy-options policy-statement T5_SECURE_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_SECURE_EXPORT term fm_direct then accept set policy-options policy-statement T5_SECURE_EXPORT term Default_Route from route-filter 0.0.0.0/0 exact set policy-options policy-statement T5_SECURE_EXPORT term Default_Route then accept set policy-options policy-statement FW1_Export from protocol evpn set policy-options policy-statement FW1_Export then accept
방화벽
방화벽 인터페이스는 VLAN 태그 처리된 인터페이스로 구성됩니다. 그림 2와 같이 각 서비스 리프에 두 개의 EBGP 세션을 설정합니다.
-
여기에서는 이미지에 표시된 방화벽-1 서비스 리프 상호 연결과 BGP 피어링 및 경로 내보내기 기능을 설정했습니다.
set interfaces xe-0/0/4 vlan-tagging set interfaces xe-0/0/4 unit 991 vlan-id 991 set interfaces xe-0/0/4 unit 991 family inet address 10.81.91.1/30 set interfaces xe-0/0/4 unit 992 vlan-id 992 set interfaces xe-0/0/4 unit 992 family inet address 10.81.92.1/30 set interfaces xe-0/0/5 vlan-tagging set interfaces xe-0/0/5 unit 991 vlan-id 991 set interfaces xe-0/0/5 unit 991 family inet address 10.81.91.5/30 set interfaces xe-0/0/5 unit 992 vlan-id 992 set interfaces xe-0/0/5 unit 992 family inet address 10.81.92.5/30 set protocols bgp group ServiceLeaf type external set protocols bgp group ServiceLeaf export Export-Default-Route set protocols bgp group ServiceLeaf local-as 64777 set protocols bgp group ServiceLeaf neighbor 10.81.91.2 peer-as 64730 set protocols bgp group ServiceLeaf neighbor 10.81.92.2 peer-as 64730 set protocols bgp group ServiceLeaf neighbor 10.81.91.6 peer-as 64730 set protocols bgp group ServiceLeaf neighbor 10.81.92.6 peer-as 64730 set policy-options policy-statement Export-Default-Route term 10 from route-filter 0.0.0.0/0 exact set policy-options policy-statement Export-Default-Route term 10 then accept set policy-options policy-statement Export-Default-Route term 100 then reject
-
이제 방화벽-1에 대한 영역과 정책 구성을 설정해야 합니다. 논리 인터페이스 991을 트래버스하는 트래픽을 INSPECT_Zone, 논리적 인터페이스 992를 트래버스하는 트래픽을 SECURE_Zone.
set security zones security-zone INSPECT_Zone address-book address EP1 10.1.110.11/32 set security zones security-zone INSPECT_Zone host-inbound-traffic system-services all set security zones security-zone INSPECT_Zone host-inbound-traffic protocols all set security zones security-zone INSPECT_Zone interfaces xe-0/0/4.991 set security zones security-zone INSPECT_Zone interfaces xe-0/0/5.991 set security zones security-zone SECURE_Zone address-book address EP2 10.1.111.21/32 set security zones security-zone SECURE_Zone host-inbound-traffic system-services all set security zones security-zone SECURE_Zone host-inbound-traffic protocols all set security zones security-zone SECURE_Zone interfaces xe-0/0/4.992 set security zones security-zone SECURE_Zone interfaces xe-0/0/5.992
-
엔드포인트-1에서 엔드포인트-2로의 통신을 특정 프로토콜로만 제한하기 위해(서버에서 추적 경로를 지원하기 위해 Ping, HTTPS, SSH 및 UDP) INSPECT_Zone 및 SECURE_Zone 간의 트래픽에 대한 보안 정책을 만듭니다.
set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Allow_EP1_to_EP2 match source-address 10.1.110.11 set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Allow_EP1_to_EP2 match destination-address 10.1.111.21 set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Allow_EP1_to_EP2 match application junos-https set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Allow_EP1_to_EP2 match application junos-ssh set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Allow_EP1_to_EP2 match application junos-ping set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Allow_EP1_to_EP2 match application junos-udp-any set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Allow_EP1_to_EP2 then permit set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Block_All match source-address any set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Block_All match destination-address any set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Block_All match application any set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Block_All then deny
-
보안 영역에서 검사 영역까지 모든 트래픽을 수용하는 정책을 정의합니다.
set security policies from-zone SECURE_Zone to-zone INSPECT_Zone policy Allow_All match source-address any set security policies from-zone SECURE_Zone to-zone INSPECT_Zone policy Allow_All match destination-address any set security policies from-zone SECURE_Zone to-zone INSPECT_Zone policy Allow_All match application any set security policies from-zone SECURE_Zone to-zone INSPECT_Zone policy Allow_All then permit
확인
이 섹션의 명령과 출력은 FBF가 EP1과 EP2 사이의 트래픽에 대해 올바르게 작동하는지 확인합니다.
- EP1과 EP2 사이에 핑을 생성합니다. 핑이 흐르는 동안 먼저 삭제한 다음 리프 1과 리프 2에 방화벽 카운터를 표시합니다.
{master:0} jcluser@Leaf1>clear firewall all {master:0} root@Leaf1> show firewall Filter: SecureTraffic Counters: Name Bytes Packets EP1_to_EP2 1484 14 . . . {master:0} root@Leaf1> show firewall Filter: SecureTraffic Counters: Name Bytes Packets EP1_to_EP2 2332 22Leaf 1의 출력은 BMS 핑 트래픽이 SecureTraffic 필터에 충돌하고 있음을 확인하고 트래픽을 INSPECT_VRF 리디렉션하는 방화벽 용어입니다. Replies를 SECURE_VRF 조정하는 SecureResponseTraffic 필터의 Leaf2에서도 유사한 결과가 언급됩니다.
- SRX 디바이스에 보안 플로우 정보를 표시합니다.
jcluser@firewall>clear firewall all root@firewall> show security flow session | match icmp In: 10.1.110.11/5554 --> 10.1.111.21/31;icmp, Conn Tag: 0x0, If: xe-0/0/5.991, Pkts: 1, Bytes: 84, Out: 10.1.111.21/31 --> 10.1.110.11/5554;icmp, Conn Tag: 0x0, If: xe-0/0/4.992, Pkts: 0, Bytes: 0, In: 10.1.110.11/5554 --> 10.1.111.21/32;icmp, Conn Tag: 0x0, If: xe-0/0/5.991, Pkts: 1, Bytes: 84, Out: 10.1.111.21/32 --> 10.1.110.11/5554;icmp, Conn Tag: 0x0, If: xe-0/0/4.992, Pkts: 0, Bytes: 0, In: 10.1.110.11/5554 --> 10.1.111.21/33;icmp, Conn Tag: 0x0, If: xe-0/0/5.991, Pkts: 1, Bytes: 84,출력은 BMS 핑 트래픽이 방화벽에 의해 검사되고 있음을 확인합니다. 이는 FBF가 EP1에서 EP2로 전송되는 트래픽을 리프에서 서비스 리프로, 거기서 방화벽 디바이스 전송하고 있음을 확인합니다.
- EP1과 EP2 사이의 경로를 추적합니다. 방화벽 디바이스 통해 언더레이 포워딩 홉을 볼 수 있습니다.
결과는 그림 3에 표시됩니다.
참고: EP1의 트래픽은 VXLAN으로 캡슐화되어 리프 1에서 서비스 리프로 전송됩니다. 서비스 리프는 트래픽과 경로를 방화벽 디바이스 네이티브 IP로 디캡슐화하여 추적 경로의 출력에 언더레이 홉이 노출되도록 합니다.그림 3: FBF를 통한 EP1 ~EP2 추적 경로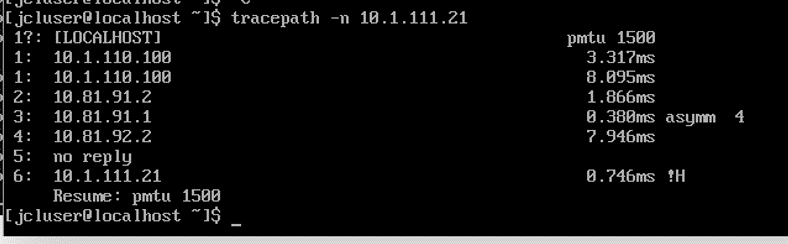
EP1(BMS 1)의 추적 경로 출력은 방화벽을 통해 트래픽을 조정하는 데 사용되는 추가 패브릭 포워딩 홉을 보여줍니다. 출력에서 홉 1과 6은 각각 리프 1과 리프 2의 IRB 인터페이스를 나타냅니다. 계약 중인 10.81.91.2 홉은 서비스 리프 1의 INSPECT_VRF 보관된 irb.991 인터페이스를 나타냅니다. 이러한 결과는 EP1 ~EP2 트래픽이 방화벽을 통해 올바르게 전달된다는 추가적인 확인을 추가합니다.
- 리프 1과 리프 2 모두에서 IRB 인터페이스에 적용된 방화벽 필터를 비활성화합니다. 변경 사항을 커밋해야 합니다.
{master:0}[edit] root@Leaf1# deactivate interfaces irb unit 110 family inet filter input{master:0}[edit] root@Leaf2# deactivate interfaces irb unit 111 family inet filter inputEP1과 EP2 사이의 추적 경로를 반복합니다. 결과는 그림 4에 표시됩니다.
그림 4: FBF가 없는 EP1에서 EP2 추적 경로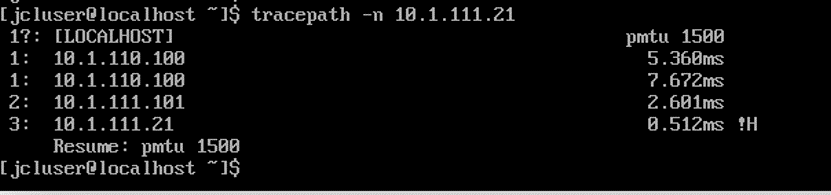
추적 경로 출력은 필터가 비활성화된 경우 EP1에서 EP2 트래픽 플로우가 리프 디바이스의 IRB 인터페이스 간에 직접 흐른다는 것을 보여줍니다. FBF로 서비스 리프를 제거하고 방화벽 디바이스 더 이상 이러한 엔드포인트 간 포워딩 경로에 없습니다.
전체 디바이스 구성
이 섹션은 이 예에서 사용되는 모든 디바이스에 대한 전체 구성을 제공합니다. 사용자 로그인, 시스템 서비스, 로깅 및 관리 인터페이스에 대한 사이트별 구성은 생략됩니다.
Spine-1 구성
set system host-name Spine1 set chassis fpc 0 pic 0 port 4 channel-speed 10g set interfaces et-0/0/0 mtu 9200 set interfaces et-0/0/0 unit 0 family inet address 10.80.224.30/31 set interfaces et-0/0/1 mtu 9200 set interfaces et-0/0/1 unit 0 family inet address 10.80.224.0/31 set interfaces xe-0/0/4:0 mtu 9200 set interfaces xe-0/0/4:0 unit 0 family inet address 10.80.224.2/31 set interfaces et-0/0/4:1 unit 0 family ethernet-switching vlan members default set interfaces et-0/0/4:1 unit 0 family ethernet-switching storm-control default set interfaces xe-0/0/4:1 mtu 9200 set interfaces xe-0/0/4:1 unit 0 family inet address 10.80.224.4/31 set interfaces et-0/0/4:2 unit 0 family ethernet-switching vlan members default set interfaces et-0/0/4:2 unit 0 family ethernet-switching storm-control default set interfaces xe-0/0/4:2 mtu 9200 set interfaces xe-0/0/4:2 unit 0 family inet address 10.80.224.6/31 set interfaces et-0/0/4:3 unit 0 family ethernet-switching vlan members default set interfaces et-0/0/4:3 unit 0 family ethernet-switching storm-control default set interfaces xe-0/0/4:3 mtu 9200 set interfaces xe-0/0/4:3 unit 0 family inet address 10.80.224.8/31 set interfaces lo0 unit 0 family inet address 10.80.224.149/32 set forwarding-options storm-control-profiles default all set policy-options policy-statement ECMP-POLICY then load-balance per-packet set policy-options policy-statement FROM_Lo0 term 10 from interface lo0.0 set policy-options policy-statement FROM_Lo0 term 10 then accept set policy-options policy-statement FROM_Lo0 term 20 then reject set policy-options policy-statement FROM_UNDERLAY_BGP term 10 from protocol bgp set policy-options policy-statement FROM_UNDERLAY_BGP term 10 then accept set policy-options policy-statement UNDERLAY-EXPORT term LOOPBACK from route-filter 10.80.224.128/25 orlonger set policy-options policy-statement UNDERLAY-EXPORT term LOOPBACK from route-filter 10.0.0.0/24 orlonger set policy-options policy-statement UNDERLAY-EXPORT term LOOPBACK then accept set policy-options policy-statement UNDERLAY-EXPORT term DEFAULT then reject set policy-options policy-statement UNDERLAY-IMPORT term LOOPBACK from route-filter 10.80.224.128/25 orlonger set policy-options policy-statement UNDERLAY-IMPORT term LOOPBACK from route-filter 10.0.0.0/24 orlonger set policy-options policy-statement UNDERLAY-IMPORT term LOOPBACK then accept set policy-options policy-statement UNDERLAY-IMPORT term DEFAULT then reject set routing-options forwarding-table export ECMP-POLICY set routing-options forwarding-table ecmp-fast-reroute set protocols bgp group EVPN_FABRIC type internal set protocols bgp group EVPN_FABRIC description "manage connection from leaves" set protocols bgp group EVPN_FABRIC local-address 10.80.224.149 set protocols bgp group EVPN_FABRIC family evpn signaling set protocols bgp group EVPN_FABRIC cluster 10.80.224.149 set protocols bgp group EVPN_FABRIC local-as 64730 set protocols bgp group EVPN_FABRIC multipath set protocols bgp group EVPN_FABRIC neighbor 10.80.224.139 set protocols bgp group EVPN_FABRIC neighbor 10.80.224.140 set protocols bgp group EVPN_FABRIC neighbor 10.80.224.141 set protocols bgp group EVPN_FABRIC neighbor 10.80.224.142 set protocols bgp group EVPN_FABRIC neighbor 10.80.224.143 set protocols bgp group EVPN_FABRIC neighbor 10.80.224.138 set protocols bgp group EVPN_FABRIC vpn-apply-export set protocols bgp group UNDERLAY type external set protocols bgp group UNDERLAY description "Connection to EBGP UNDERLAY" set protocols bgp group UNDERLAY import UNDERLAY-IMPORT set protocols bgp group UNDERLAY family inet unicast set protocols bgp group UNDERLAY export UNDERLAY-EXPORT set protocols bgp group UNDERLAY local-as 10021 set protocols bgp group UNDERLAY multipath multiple-as set protocols bgp group UNDERLAY bfd-liveness-detection minimum-interval 350 set protocols bgp group UNDERLAY bfd-liveness-detection multiplier 3 set protocols bgp group UNDERLAY neighbor 10.80.224.9 peer-as 65015 set protocols bgp group UNDERLAY neighbor 10.80.224.7 peer-as 65014 set protocols bgp group UNDERLAY neighbor 10.80.224.3 peer-as 65012 set protocols bgp group UNDERLAY neighbor 10.80.224.5 peer-as 65013 set protocols bgp group UNDERLAY neighbor 10.80.224.1 peer-as 65011 set protocols bgp group UNDERLAY neighbor 10.80.224.31 peer-as 65009 set protocols bgp hold-time 10 set protocols bgp log-updown set protocols lldp interface all set protocols igmp-snooping vlan default set vlans default vlan-id 1
Spine-2 구성
set system host-name Spine2 set chassis fpc 0 pic 0 port 4 channel-speed 10g set interfaces et-0/0/0 mtu 9200 set interfaces et-0/0/0 unit 0 family inet address 10.80.224.10/31 set interfaces et-0/0/1 mtu 9200 set interfaces et-0/0/1 unit 0 family inet address 10.80.224.32/31 set interfaces xe-0/0/4:0 mtu 9200 set interfaces xe-0/0/4:0 unit 0 family inet address 10.80.224.12/31 set interfaces xe-0/0/4:1 mtu 9200 set interfaces xe-0/0/4:1 unit 0 family inet address 10.80.224.14/31 set interfaces xe-0/0/4:2 unit 0 family inet address 10.80.224.16/31 set interfaces et-0/0/4:3 unit 0 family inet dhcp vendor-id Juniper-qfx5120-32c set interfaces xe-0/0/4:3 mtu 9200 set interfaces xe-0/0/4:3 unit 0 family inet address 10.80.224.18/31 set interfaces lo0 unit 0 family inet address 10.80.224.150/32 set forwarding-options storm-control-profiles default all set policy-options policy-statement ECMP-POLICY then load-balance per-packet set policy-options policy-statement FROM_Lo0 term 10 from interface lo0.0 set policy-options policy-statement FROM_Lo0 term 10 then accept set policy-options policy-statement FROM_Lo0 term 20 then reject set policy-options policy-statement FROM_UNDERLAY_BGP term 10 from protocol bgp set policy-options policy-statement FROM_UNDERLAY_BGP term 10 then accept set policy-options policy-statement UNDERLAY-EXPORT term LOOPBACK from route-filter 10.80.224.128/25 orlonger set policy-options policy-statement UNDERLAY-EXPORT term LOOPBACK then accept set policy-options policy-statement UNDERLAY-EXPORT term DEFAULT then reject set policy-options policy-statement UNDERLAY-IMPORT term LOOPBACK from route-filter 10.80.224.128/25 orlonger set policy-options policy-statement UNDERLAY-IMPORT term LOOPBACK then accept set policy-options policy-statement UNDERLAY-IMPORT term DEFAULT then reject set routing-options forwarding-table export ECMP-POLICY set routing-options forwarding-table ecmp-fast-reroute set protocols bgp group EVPN_FABRIC type internal set protocols bgp group EVPN_FABRIC description "manage connection from leaves" set protocols bgp group EVPN_FABRIC local-address 10.80.224.150 set protocols bgp group EVPN_FABRIC family evpn signaling set protocols bgp group EVPN_FABRIC cluster 10.80.224.150 set protocols bgp group EVPN_FABRIC local-as 64730 set protocols bgp group EVPN_FABRIC multipath set protocols bgp group EVPN_FABRIC neighbor 10.80.224.139 set protocols bgp group EVPN_FABRIC neighbor 10.80.224.140 set protocols bgp group EVPN_FABRIC neighbor 10.80.224.141 set protocols bgp group EVPN_FABRIC neighbor 10.80.224.142 set protocols bgp group EVPN_FABRIC neighbor 10.80.224.143 set protocols bgp group EVPN_FABRIC neighbor 10.80.224.138 set protocols bgp group EVPN_FABRIC vpn-apply-export set protocols bgp group UNDERLAY type external set protocols bgp group UNDERLAY description "Connection to EBGP UNDERLAY" set protocols bgp group UNDERLAY import UNDERLAY-IMPORT set protocols bgp group UNDERLAY family inet unicast set protocols bgp group UNDERLAY export UNDERLAY-EXPORT set protocols bgp group UNDERLAY local-as 10022 set protocols bgp group UNDERLAY multipath multiple-as set protocols bgp group UNDERLAY bfd-liveness-detection minimum-interval 350 set protocols bgp group UNDERLAY bfd-liveness-detection multiplier 3 set protocols bgp group UNDERLAY neighbor 10.80.224.13 peer-as 65012 set protocols bgp group UNDERLAY neighbor 10.80.224.19 peer-as 65015 set protocols bgp group UNDERLAY neighbor 10.80.224.11 peer-as 65011 set protocols bgp group UNDERLAY neighbor 10.80.224.17 peer-as 65014 set protocols bgp group UNDERLAY neighbor 10.80.224.15 peer-as 65013 set protocols bgp group UNDERLAY neighbor 10.80.224.33 peer-as 65009 set protocols bgp hold-time 10 set protocols bgp log-updown set protocols lldp port-id-subtype interface-name set protocols lldp interface all set protocols lldp-med interface all set protocols igmp-snooping vlan default
서버 리프-1 구성
set system host-name Leaf1 set system root-authentication encrypted-password "$6$yMrAzWii$mH8/hzspVvEAWSta.W2sbI3Fkjh5DpY.QMJhvyXP1ZfFWZ4E0KLfzlPZISlUqElTGmzeKEuE9EDths9PviIwR/" set system login user jcluser uid 2000 set system login user jcluser class super-user set system login user jcluser authentication encrypted-password "$6$yz5sIC9j$Z3P7ygtxzWAdfjDFXUmz787lCqquxA0YbkseMs9W1ZxyDOIsXBwJer1ShHlrBp3obTitLJGYbrVk3IdIR5DfI." set system services ssh root-login allow set interfaces xe-0/0/0 mtu 9200 set interfaces xe-0/0/0 unit 0 family inet address 10.80.224.3/31 set interfaces xe-0/0/2 mtu 9200 set interfaces xe-0/0/2 unit 0 family inet address 10.80.224.13/31 set interfaces irb unit 110 virtual-gateway-accept-data set interfaces irb unit 110 family inet filter input SecureTraffic set interfaces irb unit 110 family inet address 10.1.110.100/24 virtual-gateway-address 10.1.110.1 set interfaces irb unit 110 virtual-gateway-v4-mac e4:5d:37:11:10:01 set interfaces irb unit 111 family inet address 10.1.111.1/24 set interfaces irb unit 111 virtual-gateway-v4-mac e4:5d:37:11:11:01 set interfaces irb unit 112 family inet address 10.1.112.1/24 set interfaces irb unit 112 virtual-gateway-v4-mac e4:5d:37:11:12:01 set interfaces lo0 unit 0 description "** dc-leaf1-lo0" set interfaces lo0 unit 0 family inet address 10.80.224.140/32 set interfaces lo0 unit 110 family inet address 192.168.110.1/32 set interfaces lo0 unit 110 family inet6 address 2001:db8::192:168:110:1/128 set interfaces lo0 unit 112 family inet address 192.168.112.1/32 set interfaces lo0 unit 112 family inet6 address 2001:db8::192:168:112:1/128 set interfaces lo0 unit 991 family inet address 192.168.91.1/32 set forwarding-options storm-control-profiles default all set forwarding-options vxlan-routing next-hop 32768 set forwarding-options vxlan-routing overlay-ecmp set policy-options policy-statement ECMP-POLICY then load-balance per-packet set policy-options policy-statement FROM_Lo0 term 10 from interface lo0.0 set policy-options policy-statement FROM_Lo0 term 10 then accept set policy-options policy-statement FROM_Lo0 term 20 then reject set policy-options policy-statement FROM_UNDERLAY_BGP term 10 from protocol bgp set policy-options policy-statement FROM_UNDERLAY_BGP term 10 then accept set policy-options policy-statement T5_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_EXPORT term fm_direct then accept set policy-options policy-statement T5_EXPORT term fm_static from protocol static set policy-options policy-statement T5_EXPORT term fm_static then accept set policy-options policy-statement T5_EXPORT term fm_v4_host from protocol evpn set policy-options policy-statement T5_EXPORT term fm_v4_host from route-filter 0.0.0.0/0 prefix-length-range /32-/32 set policy-options policy-statement T5_EXPORT term fm_v4_host then accept set policy-options policy-statement T5_EXPORT term fm_v6_host from route-filter 0::0/0 prefix-length-range /128-/128 set policy-options policy-statement T5_EXPORT term fm_v6_host then accept set policy-options policy-statement T5_INSPECT_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_INSPECT_EXPORT term fm_direct then accept set policy-options policy-statement T5_INSPECT_EXPORT term fm_static from protocol static set policy-options policy-statement T5_INSPECT_EXPORT term fm_static then accept set policy-options policy-statement T5_SECURE_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_SECURE_EXPORT term fm_direct then accept set policy-options policy-statement T5_SECURE_EXPORT term fm_static from protocol static set policy-options policy-statement T5_SECURE_EXPORT term fm_static then accept set firewall family inet filter SecureTraffic term EP1_to_EP2 from source-address 10.1.110.11/32 set firewall family inet filter SecureTraffic term EP1_to_EP2 from destination-address 10.1.111.21/32 set firewall family inet filter SecureTraffic term EP1_to_EP2 then count EP1_to_EP2 set firewall family inet filter SecureTraffic term EP1_to_EP2 then routing-instance INSPECT_VRF set firewall family inet filter SecureTraffic term Allow_All then accept set routing-instances INSPECT_VRF routing-options static route 10.1.110.11/32 next-table Tenant1_VRF.inet.0 set routing-instances INSPECT_VRF routing-options multipath set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes vni 9991 set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes export T5_INSPECT_EXPORT set routing-instances INSPECT_VRF description "VRF for Firewall1" set routing-instances INSPECT_VRF instance-type vrf set routing-instances INSPECT_VRF interface lo0.991 set routing-instances INSPECT_VRF route-distinguisher 10.80.224.140:9991 set routing-instances INSPECT_VRF vrf-target target:64730:991 set routing-instances INSPECT_VRF vrf-table-label set routing-instances Tenant1_VRF routing-options multipath set routing-instances Tenant1_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances Tenant1_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances Tenant1_VRF protocols evpn ip-prefix-routes vni 9110 set routing-instances Tenant1_VRF protocols evpn ip-prefix-routes export T5_EXPORT set routing-instances Tenant1_VRF description "VRF for tenant Tenant_1" set routing-instances Tenant1_VRF instance-type vrf set routing-instances Tenant1_VRF forwarding-options dhcp-relay dhcpv6 overrides relay-source lo0.110 set routing-instances Tenant1_VRF forwarding-options dhcp-relay dhcpv6 forward-only set routing-instances Tenant1_VRF forwarding-options dhcp-relay dhcpv6 forward-only-replies set routing-instances Tenant1_VRF forwarding-options dhcp-relay dhcpv6 group all interface irb.110 set routing-instances Tenant1_VRF forwarding-options dhcp-relay dhcpv6 server-group dhcp-servers-v6 2001:db8::10:1:140:188 set routing-instances Tenant1_VRF forwarding-options dhcp-relay dhcpv6 active-server-group dhcp-servers-v6 set routing-instances Tenant1_VRF forwarding-options dhcp-relay relay-option-82 set routing-instances Tenant1_VRF interface irb.110 set routing-instances Tenant1_VRF interface irb.111 set routing-instances Tenant1_VRF interface lo0.110 set routing-instances Tenant1_VRF route-distinguisher 10.80.224.140:9110 set routing-instances Tenant1_VRF vrf-target target:64730:110 set routing-instances Tenant1_VRF vrf-table-label set routing-instances Tenant2_VRF routing-options multipath set routing-instances Tenant2_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances Tenant2_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances Tenant2_VRF protocols evpn ip-prefix-routes vni 9112 set routing-instances Tenant2_VRF protocols evpn ip-prefix-routes export T5_EXPORT set routing-instances Tenant2_VRF description "VRF for tenant Tenant_1" set routing-instances Tenant2_VRF instance-type vrf set routing-instances Tenant2_VRF interface irb.112 set routing-instances Tenant2_VRF interface lo0.112 set routing-instances Tenant2_VRF route-distinguisher 10.80.224.140:9112 set routing-instances Tenant2_VRF vrf-target target:64730:112 set routing-instances Tenant2_VRF vrf-table-label set routing-options router-id 10.80.224.140 set routing-options autonomous-system 64730 set routing-options forwarding-table export ECMP-POLICY set routing-options forwarding-table ecmp-fast-reroute set routing-options forwarding-table chained-composite-next-hop ingress evpn set protocols bgp group EVPN_FABRIC type internal set protocols bgp group EVPN_FABRIC description "Connection to EVPN Fabric RRs (tenants.bgp_reflector)" set protocols bgp group EVPN_FABRIC local-address 10.80.224.140 set protocols bgp group EVPN_FABRIC family evpn signaling set protocols bgp group EVPN_FABRIC local-as 64730 set protocols bgp group EVPN_FABRIC multipath set protocols bgp group EVPN_FABRIC neighbor 10.80.224.149 set protocols bgp group EVPN_FABRIC neighbor 10.80.224.150 set protocols bgp group UNDERLAY type external set protocols bgp group UNDERLAY description "Connection to EBGP UNDERLAY" set protocols bgp group UNDERLAY family inet unicast set protocols bgp group UNDERLAY export FROM_Lo0 set protocols bgp group UNDERLAY export FROM_UNDERLAY_BGP set protocols bgp group UNDERLAY local-as 65012 set protocols bgp group UNDERLAY multipath multiple-as set protocols bgp group UNDERLAY bfd-liveness-detection minimum-interval 350 set protocols bgp group UNDERLAY bfd-liveness-detection multiplier 3 set protocols bgp group UNDERLAY neighbor 10.80.224.12 peer-as 10022 set protocols bgp group UNDERLAY neighbor 10.80.224.2 peer-as 10021 set protocols bgp hold-time 10 set protocols bgp log-updown set protocols evpn encapsulation vxlan set protocols evpn extended-vni-list 110 set protocols evpn extended-vni-list 111 set protocols evpn extended-vni-list 112 set protocols l2-learning global-mac-table-aging-time 600 set protocols l2-learning global-mac-ip-table-aging-time 300 set protocols l2-learning decapsulate-accept-inner-vlan set protocols lldp interface all set protocols igmp-snooping vlan default set switch-options vtep-source-interface lo0.0 set switch-options route-distinguisher 10.80.224.140:1 set switch-options vrf-target target:64730:1 set switch-options vrf-target auto set vlans default vlan-id 1 set vlans v110 vlan-id 110 set vlans v110 l3-interface irb.110 set vlans v110 vxlan vni 110 set vlans v111 vlan-id 111 set vlans v111 l3-interface irb.111 set vlans v111 vxlan vni 111 set vlans v112 vlan-id 112 set vlans v112 l3-interface irb.112 set vlans v112 vxlan vni 112
서버 리프-2 구성:
set system host-name Leaf2 set interfaces xe-0/0/0 mtu 9200 set interfaces xe-0/0/0 unit 0 family inet address 10.80.224.5/31 set interfaces xe-0/0/1 unit 0 family ethernet-switching interface-mode trunk set interfaces xe-0/0/1 unit 0 family ethernet-switching vlan members v110 set interfaces xe-0/0/1 unit 0 family ethernet-switching vlan members v111 set interfaces et-0/0/2 unit 0 family inet dhcp vendor-id Juniper-qfx5120-48y-8c set interfaces ge-0/0/2 unit 0 family inet dhcp vendor-id Juniper-qfx5120-48y-8c set interfaces xe-0/0/2 mtu 9200 set interfaces xe-0/0/2 unit 0 family inet address 10.80.224.15/31 set interfaces irb unit 110 virtual-gateway-accept-data set interfaces irb unit 110 family inet address 10.1.110.101/24 virtual-gateway-address 10.1.110.1 set interfaces irb unit 110 virtual-gateway-v4-mac e4:5d:37:11:10:01 set interfaces irb unit 111 virtual-gateway-accept-data set interfaces irb unit 111 family inet filter input SecureResponseTraffic set interfaces irb unit 111 family inet address 10.1.111.101/24 virtual-gateway-address 10.1.111.1 set interfaces irb unit 111 virtual-gateway-v4-mac e4:5d:37:11:11:01 set interfaces irb unit 112 family inet address 10.1.112.101/24 virtual-gateway-address 10.1.112.1 set interfaces irb unit 112 virtual-gateway-v4-mac e4:5d:37:11:12:01 set interfaces lo0 unit 0 description "** dc-leaf2-lo0" set interfaces lo0 unit 0 family inet address 10.80.224.141/32 set interfaces lo0 unit 110 family inet address 192.168.110.2/32 set interfaces lo0 unit 110 family inet6 address 2001:db8::192:168:110:2/128 set interfaces lo0 unit 112 family inet address 192.168.112.2/32 set interfaces lo0 unit 112 family inet6 address 2001:db8::192:168:112:2/128 set interfaces lo0 unit 992 family inet address 192.168.92.2/32 set forwarding-options storm-control-profiles default all set forwarding-options vxlan-routing next-hop 32768 set forwarding-options vxlan-routing overlay-ecmp set policy-options policy-statement ECMP-POLICY then load-balance per-packet set policy-options policy-statement FROM_Lo0 term 10 from interface lo0.0 set policy-options policy-statement FROM_Lo0 term 10 then accept set policy-options policy-statement FROM_Lo0 term 20 then reject set policy-options policy-statement FROM_UNDERLAY_BGP term 10 from protocol bgp set policy-options policy-statement FROM_UNDERLAY_BGP term 10 then accept set policy-options policy-statement T5_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_EXPORT term fm_direct then accept set policy-options policy-statement T5_EXPORT term fm_static from protocol static set policy-options policy-statement T5_EXPORT term fm_static then accept set policy-options policy-statement T5_EXPORT term fm_v4_host from protocol evpn set policy-options policy-statement T5_EXPORT term fm_v4_host from route-filter 0.0.0.0/0 prefix-length-range /32-/32 set policy-options policy-statement T5_EXPORT term fm_v4_host then accept set policy-options policy-statement T5_EXPORT term fm_v6_host from route-filter 0::0/0 prefix-length-range /128-/128 set policy-options policy-statement T5_EXPORT term fm_v6_host then accept set policy-options policy-statement T5_INSPECT_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_INSPECT_EXPORT term fm_direct then accept set policy-options policy-statement T5_INSPECT_EXPORT term fm_static from protocol static set policy-options policy-statement T5_INSPECT_EXPORT term fm_static then accept set policy-options policy-statement T5_SECURE_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_SECURE_EXPORT term fm_direct then accept set policy-options policy-statement T5_SECURE_EXPORT term fm_static from protocol static set policy-options policy-statement T5_SECURE_EXPORT term fm_static then accept set firewall family inet filter SecureResponseTraffic term EP2_to_EP1 from source-address 10.1.111.21/32 set firewall family inet filter SecureResponseTraffic term EP2_to_EP1 from destination-address 10.1.110.11/32 set firewall family inet filter SecureResponseTraffic term EP2_to_EP1 then count EP2_to_EP1 set firewall family inet filter SecureResponseTraffic term EP2_to_EP1 then routing-instance SECURE_VRF set firewall family inet filter SecureResponseTraffic term Allow_All then accept set routing-instances INSPECT_VRF routing-options static route 10.1.111.21/32 next-table Tenant1_VRF.inet.0 set routing-instances INSPECT_VRF routing-options multipath set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes vni 9992 set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes export T5_SECURE_EXPORT set routing-instances INSPECT_VRF description "VRF for SECURED FIREWALL TRAFFIC" set routing-instances INSPECT_VRF instance-type vrf set routing-instances INSPECT_VRF interface lo0.992 set routing-instances INSPECT_VRF route-distinguisher 10.80.224.141:9992 set routing-instances INSPECT_VRF vrf-target target:64730:992 set routing-instances INSPECT_VRF vrf-table-label set routing-instances Tenant1_VRF routing-options multipath set routing-instances Tenant1_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances Tenant1_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances Tenant1_VRF protocols evpn ip-prefix-routes vni 9110 set routing-instances Tenant1_VRF protocols evpn ip-prefix-routes export T5_EXPORT set routing-instances Tenant1_VRF description "VRF for tenant Tenant_1" set routing-instances Tenant1_VRF instance-type vrf set routing-instances Tenant1_VRF interface irb.110 set routing-instances Tenant1_VRF interface irb.111 set routing-instances Tenant1_VRF interface lo0.110 set routing-instances Tenant1_VRF route-distinguisher 10.80.224.141:9110 set routing-instances Tenant1_VRF vrf-target target:64730:110 set routing-instances Tenant1_VRF vrf-table-label set routing-instances Tenant2_VRF routing-options multipath set routing-instances Tenant2_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances Tenant2_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances Tenant2_VRF protocols evpn ip-prefix-routes vni 9112 set routing-instances Tenant2_VRF protocols evpn ip-prefix-routes export T5_EXPORT set routing-instances Tenant2_VRF description "VRF for tenant Tenant_1" set routing-instances Tenant2_VRF instance-type vrf set routing-instances Tenant2_VRF interface irb.112 set routing-instances Tenant2_VRF interface lo0.112 set routing-instances Tenant2_VRF route-distinguisher 10.80.224.141:9112 set routing-instances Tenant2_VRF vrf-target target:64730:112 set routing-instances Tenant2_VRF vrf-table-label set routing-options static route 0.0.0.0/0 next-hop 100.123.0.1 set routing-options router-id 10.80.224.141 set routing-options autonomous-system 64730 set routing-options forwarding-table export ECMP-POLICY set routing-options forwarding-table ecmp-fast-reroute set routing-options forwarding-table chained-composite-next-hop ingress evpn set protocols bgp group EVPN_FABRIC type internal set protocols bgp group EVPN_FABRIC description "Connection to EVPN Fabric RRs (tenants.bgp_reflector)" set protocols bgp group EVPN_FABRIC local-address 10.80.224.141 set protocols bgp group EVPN_FABRIC family evpn signaling set protocols bgp group EVPN_FABRIC local-as 64730 set protocols bgp group EVPN_FABRIC multipath set protocols bgp group EVPN_FABRIC neighbor 10.80.224.149 set protocols bgp group EVPN_FABRIC neighbor 10.80.224.150 set protocols bgp group UNDERLAY type external set protocols bgp group UNDERLAY description "Connection to EBGP UNDERLAY" set protocols bgp group UNDERLAY family inet unicast set protocols bgp group UNDERLAY export FROM_Lo0 set protocols bgp group UNDERLAY export FROM_UNDERLAY_BGP set protocols bgp group UNDERLAY local-as 65013 set protocols bgp group UNDERLAY multipath multiple-as set protocols bgp group UNDERLAY bfd-liveness-detection minimum-interval 350 set protocols bgp group UNDERLAY bfd-liveness-detection multiplier 3 set protocols bgp group UNDERLAY neighbor 10.80.224.4 peer-as 10021 set protocols bgp group UNDERLAY neighbor 10.80.224.14 peer-as 10022 set protocols bgp hold-time 10 set protocols bgp log-updown set protocols evpn encapsulation vxlan set protocols evpn extended-vni-list 110 set protocols evpn extended-vni-list 111 set protocols evpn extended-vni-list 112 set protocols l2-learning global-mac-table-aging-time 600 set protocols l2-learning global-mac-ip-table-aging-time 300 set protocols l2-learning decapsulate-accept-inner-vlan set protocols lldp port-id-subtype interface-name set protocols lldp interface all set protocols igmp-snooping vlan default set switch-options vtep-source-interface lo0.0 set switch-options route-distinguisher 10.80.224.143:1 set switch-options vrf-target target:64730:1 set switch-options vrf-target auto set vlans v110 vlan-id 110 set vlans v110 l3-interface irb.110 set vlans v110 vxlan vni 110 set vlans v111 vlan-id 111 set vlans v111 l3-interface irb.111 set vlans v111 vxlan vni 111 set vlans v112 vlan-id 112 set vlans v112 l3-interface irb.112 set vlans v112 vxlan vni 112
서비스 리프-1 구성
set system host-name ServiceLeaf1 set chassis fpc 0 pic 0 port 4 channel-speed 10g set interfaces et-0/0/0 mtu 9200 set interfaces et-0/0/0 unit 0 family inet address 10.80.224.31/31 set interfaces et-0/0/1 mtu 9200 set interfaces et-0/0/1 unit 0 family inet address 10.80.224.33/31 set interfaces xe-0/0/4:0 description "SRX Firewall 1: xe-0/0/4" set interfaces xe-0/0/4:0 mtu 9192 set interfaces xe-0/0/4:0 unit 0 family ethernet-switching interface-mode trunk set interfaces xe-0/0/4:0 unit 0 family ethernet-switching vlan members V991 set interfaces xe-0/0/4:0 unit 0 family ethernet-switching vlan members V992 set interfaces et-0/0/4:1 unit 0 family inet dhcp vendor-id Juniper-qfx5120-32c set interfaces irb unit 991 family inet address 10.81.91.2/30 set interfaces irb unit 992 family inet address 10.81.92.2/30 set interfaces lo0 unit 0 family inet address 10.80.224.138/32 set interfaces lo0 unit 110 family inet address 192.168.110.253/32 set interfaces lo0 unit 110 family inet6 address 2001:db8::192:168:110:253/128 set interfaces lo0 unit 112 family inet address 192.168.112.253/32 set interfaces lo0 unit 112 family inet6 address 2001:db8::192:168:112:253/128 set interfaces lo0 unit 991 family inet address 192.168.91.253/32 set interfaces lo0 unit 992 family inet address 192.168.92.253/32 set forwarding-options storm-control-profiles default all set policy-options policy-statement ECMP-POLICY then load-balance per-packet set policy-options policy-statement FROM_Lo0 term 10 from interface lo0.0 set policy-options policy-statement FROM_Lo0 term 10 then accept set policy-options policy-statement FROM_Lo0 term 20 then reject set policy-options policy-statement FROM_UNDERLAY_BGP term 10 from protocol bgp set policy-options policy-statement FROM_UNDERLAY_BGP term 10 then accept set policy-options policy-statement FW1_Export from protocol evpn set policy-options policy-statement FW1_Export then accept set policy-options policy-statement T5_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_EXPORT term fm_direct then accept set policy-options policy-statement T5_EXPORT term fm_static from protocol static set policy-options policy-statement T5_EXPORT term fm_static then accept set policy-options policy-statement T5_EXPORT term fm_v4_host from protocol evpn set policy-options policy-statement T5_EXPORT term fm_v4_host from route-filter 0.0.0.0/0 prefix-length-range /32-/32 set policy-options policy-statement T5_EXPORT term fm_v4_host then accept set policy-options policy-statement T5_EXPORT term fm_v6_host from protocol evpn set policy-options policy-statement T5_EXPORT term fm_v6_host from route-filter 0::0/0 prefix-length-range /128-/128 set policy-options policy-statement T5_EXPORT term fm_v6_host then accept set policy-options policy-statement T5_EXPORT term Default_Route from route-filter 0.0.0.0/0 exact set policy-options policy-statement T5_EXPORT term Default_Route then accept set policy-options policy-statement T5_EXPORT term Default_Route_v6 from route-filter ::/0 exact set policy-options policy-statement T5_EXPORT term Default_Route_v6 then accept set policy-options policy-statement T5_INSPECT_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_INSPECT_EXPORT term fm_direct then accept set policy-options policy-statement T5_INSPECT_EXPORT term Default_Route from route-filter 0.0.0.0/0 exact set policy-options policy-statement T5_INSPECT_EXPORT term Default_Route then accept set policy-options policy-statement T5_SECURE_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_SECURE_EXPORT term fm_direct then accept set policy-options policy-statement T5_SECURE_EXPORT term Default_Route from route-filter 0.0.0.0/0 exact set policy-options policy-statement T5_SECURE_EXPORT term Default_Route then accept set routing-instances INSPECT_VRF routing-options multipath set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes vni 9991 set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes export T5_INSPECT_EXPORT set routing-instances INSPECT_VRF protocols bgp group Firewall-1 type external set routing-instances INSPECT_VRF protocols bgp group Firewall-1 export FW1_Export set routing-instances INSPECT_VRF protocols bgp group Firewall-1 local-as 64730 set routing-instances INSPECT_VRF protocols bgp group Firewall-1 neighbor 10.81.91.1 peer-as 64777 set routing-instances INSPECT_VRF description "VRF for Firewall-1" set routing-instances INSPECT_VRF instance-type vrf set routing-instances INSPECT_VRF interface irb.991 set routing-instances INSPECT_VRF interface lo0.991 set routing-instances INSPECT_VRF route-distinguisher 10.80.224.138:9991 set routing-instances INSPECT_VRF vrf-target target:64730:991 set routing-instances INSPECT_VRF vrf-table-label set routing-instances SECURE_VRF routing-options multipath set routing-instances SECURE_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances SECURE_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances SECURE_VRF protocols evpn ip-prefix-routes vni 9992 set routing-instances SECURE_VRF protocols evpn ip-prefix-routes export T5_SECURE_EXPORT set routing-instances SECURE_VRF protocols bgp group Firewall-1 type external set routing-instances SECURE_VRF protocols bgp group Firewall-1 export FW1_Export set routing-instances SECURE_VRF protocols bgp group Firewall-1 local-as 64730 set routing-instances SECURE_VRF protocols bgp group Firewall-1 neighbor 10.81.92.1 peer-as 64777 set routing-instances SECURE_VRF description "VRF for SECURED FIREWALL TRAFFIC" set routing-instances SECURE_VRF instance-type vrf set routing-instances SECURE_VRF interface irb.992 set routing-instances SECURE_VRF interface lo0.992 set routing-instances SECURE_VRF route-distinguisher 10.80.224.138:9992 set routing-instances SECURE_VRF vrf-target target:64730:992 set routing-instances SECURE_VRF vrf-table-label set routing-instances Tenant1_VRF routing-options multipath set routing-instances Tenant1_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances Tenant1_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances Tenant1_VRF protocols evpn ip-prefix-routes vni 9110 set routing-instances Tenant1_VRF protocols evpn ip-prefix-routes export T5_EXPORT set routing-instances Tenant1_VRF instance-type vrf set routing-instances Tenant1_VRF interface xe-0/0/28:1.110 set routing-instances Tenant1_VRF interface lo0.110 set routing-instances Tenant1_VRF route-distinguisher 10.80.224.138:9110 set routing-instances Tenant1_VRF vrf-target target:64730:110 set routing-instances Tenant1_VRF vrf-table-label set routing-instances Tenant2_VRF routing-options multipath set routing-instances Tenant2_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances Tenant2_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances Tenant2_VRF protocols evpn ip-prefix-routes vni 9112 set routing-instances Tenant2_VRF protocols evpn ip-prefix-routes export T5_EXPORT set routing-instances Tenant2_VRF instance-type vrf set routing-instances Tenant2_VRF interface xe-0/0/28:0.112 set routing-instances Tenant2_VRF interface xe-0/0/28:1.112 set routing-instances Tenant2_VRF interface lo0.112 set routing-instances Tenant2_VRF route-distinguisher 10.80.224.138:9112 set routing-instances Tenant2_VRF vrf-target target:64730:112 set routing-instances Tenant2_VRF vrf-table-label set routing-options router-id 10.80.224.138 set routing-options autonomous-system 64730 set routing-options forwarding-table export ECMP-POLICY set routing-options forwarding-table ecmp-fast-reroute set routing-options forwarding-table chained-composite-next-hop ingress evpn set protocols bgp group EVPN_FABRIC type internal set protocols bgp group EVPN_FABRIC description "Connection to EVPN Fabric RRs (tenants.bgp_reflector)" set protocols bgp group EVPN_FABRIC local-address 10.80.224.138 set protocols bgp group EVPN_FABRIC family evpn signaling set protocols bgp group EVPN_FABRIC local-as 64730 set protocols bgp group EVPN_FABRIC multipath set protocols bgp group EVPN_FABRIC neighbor 10.80.224.149 set protocols bgp group EVPN_FABRIC neighbor 10.80.224.150 set protocols bgp group UNDERLAY type external set protocols bgp group UNDERLAY description "Connection to EBGP UNDERLAY" set protocols bgp group UNDERLAY family inet unicast set protocols bgp group UNDERLAY export FROM_Lo0 set protocols bgp group UNDERLAY export FROM_UNDERLAY_BGP set protocols bgp group UNDERLAY local-as 65009 set protocols bgp group UNDERLAY multipath multiple-as set protocols bgp group UNDERLAY bfd-liveness-detection minimum-interval 350 set protocols bgp group UNDERLAY bfd-liveness-detection multiplier 3 set protocols bgp group UNDERLAY neighbor 10.80.224.30 peer-as 10021 set protocols bgp group UNDERLAY neighbor 10.80.224.32 peer-as 10022 set protocols bgp hold-time 10 set protocols bgp log-updown set protocols l2-learning global-mac-table-aging-time 600 set protocols l2-learning global-mac-ip-table-aging-time 300 set protocols lldp port-id-subtype interface-name set protocols lldp interface all set protocols lldp-med interface all set protocols igmp-snooping vlan default set vlans V991 vlan-id 991 set vlans V991 l3-interface irb.991 set vlans V992 vlan-id 992 set vlans V992 l3-interface irb.992
서비스 리프-2 구성
set system host-name ServiceLeaf2 set chassis fpc 0 pic 0 port 4 channel-speed 10g set interfaces et-0/0/0 mtu 9200 set interfaces et-0/0/0 unit 0 family inet address 10.80.224.11/31 set interfaces et-0/0/1 mtu 9200 set interfaces et-0/0/1 unit 0 family inet address 10.80.224.1/31 set interfaces xe-0/0/4:0 description "SRX Firewall-1: xe-0/0/5" set interfaces xe-0/0/4:0 mtu 9192 set interfaces xe-0/0/4:0 unit 0 family ethernet-switching interface-mode trunk set interfaces xe-0/0/4:0 unit 0 family ethernet-switching vlan members V991 set interfaces xe-0/0/4:0 unit 0 family ethernet-switching vlan members V992 set interfaces irb unit 991 family inet address 10.81.91.6/24 set interfaces irb unit 992 family inet address 10.81.92.6/24 set interfaces lo0 unit 0 description "** qfx10k-svador" set interfaces lo0 unit 0 family inet address 10.80.224.139/32 set interfaces lo0 unit 110 family inet address 192.168.110.254/32 set interfaces lo0 unit 110 family inet6 address 2001:db8::192:168:110:254/128 set interfaces lo0 unit 112 family inet address 192.168.112.254/32 set interfaces lo0 unit 112 family inet6 address 2001:db8::192:168:112:254/128 set interfaces lo0 unit 991 family inet address 192.168.91.254/32 set interfaces lo0 unit 992 family inet address 192.168.92.254/32 set forwarding-options storm-control-profiles default all set policy-options policy-statement ECMP-POLICY then load-balance per-packet set policy-options policy-statement FROM_Lo0 term 10 from interface lo0.0 set policy-options policy-statement FROM_Lo0 term 10 then accept set policy-options policy-statement FROM_Lo0 term 20 then reject set policy-options policy-statement FROM_UNDERLAY_BGP term 10 from protocol bgp set policy-options policy-statement FROM_UNDERLAY_BGP term 10 then accept set policy-options policy-statement FW1_Export from protocol evpn set policy-options policy-statement FW1_Export then accept set policy-options policy-statement T5_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_EXPORT term fm_direct then accept set policy-options policy-statement T5_EXPORT term fm_static from protocol static set policy-options policy-statement T5_EXPORT term fm_static then accept set policy-options policy-statement T5_EXPORT term fm_v4_host from protocol evpn set policy-options policy-statement T5_EXPORT term fm_v4_host from route-filter 0.0.0.0/0 prefix-length-range /32-/32 set policy-options policy-statement T5_EXPORT term fm_v4_host then accept set policy-options policy-statement T5_EXPORT term fm_v6_host from protocol evpn set policy-options policy-statement T5_EXPORT term fm_v6_host from route-filter 0::0/0 prefix-length-range /128-/128 set policy-options policy-statement T5_EXPORT term fm_v6_host then accept set policy-options policy-statement T5_EXPORT term Default_Route from route-filter 0.0.0.0/0 exact set policy-options policy-statement T5_EXPORT term Default_Route then accept set policy-options policy-statement T5_EXPORT term Default_Route_v6 from route-filter ::/0 exact set policy-options policy-statement T5_EXPORT term Default_Route_v6 then accept set policy-options policy-statement T5_INSPECT_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_INSPECT_EXPORT term fm_direct then accept set policy-options policy-statement T5_INSPECT_EXPORT term Default_Route from route-filter 0.0.0.0/0 exact set policy-options policy-statement T5_INSPECT_EXPORT term Default_Route then accept set policy-options policy-statement T5_SECURE_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_SECURE_EXPORT term fm_direct then accept set policy-options policy-statement T5_SECURE_EXPORT term Default_Route from route-filter 0.0.0.0/0 exact set policy-options policy-statement T5_SECURE_EXPORT term Default_Route then accept set routing-instances INSPECT_VRF routing-options multipath set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes vni 9991 set routing-instances INSPECT_VRF protocols evpn ip-prefix-routes export T5_INSPECT_EXPORT set routing-instances INSPECT_VRF protocols bgp group Firewall-1 type external set routing-instances INSPECT_VRF protocols bgp group Firewall-1 export FW1_Export set routing-instances INSPECT_VRF protocols bgp group Firewall-1 local-as 64730 set routing-instances INSPECT_VRF protocols bgp group Firewall-1 neighbor 10.81.91.5 peer-as 64777 set routing-instances INSPECT_VRF description "VRF for Firewall-1" set routing-instances INSPECT_VRF instance-type vrf set routing-instances INSPECT_VRF interface irb.991 set routing-instances INSPECT_VRF interface lo0.991 set routing-instances INSPECT_VRF route-distinguisher 10.80.224.139:9991 set routing-instances INSPECT_VRF vrf-target target:64730:991 set routing-instances INSPECT_VRF vrf-table-label set routing-instances SECURE_VRF routing-options multipath set routing-instances SECURE_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances SECURE_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances SECURE_VRF protocols evpn ip-prefix-routes vni 9992 set routing-instances SECURE_VRF protocols evpn ip-prefix-routes export T5_SECURE_EXPORT set routing-instances SECURE_VRF protocols bgp group Firewall-1 type external set routing-instances SECURE_VRF protocols bgp group Firewall-1 export FW1_Export set routing-instances SECURE_VRF protocols bgp group Firewall-1 local-as 64730 set routing-instances SECURE_VRF protocols bgp group Firewall-1 neighbor 10.81.92.5 peer-as 64777 set routing-instances SECURE_VRF description "VRF for SECURED FIREWALL TRAFFIC" set routing-instances SECURE_VRF instance-type vrf set routing-instances SECURE_VRF interface irb.992 set routing-instances SECURE_VRF interface lo0.992 set routing-instances SECURE_VRF route-distinguisher 10.80.224.139:9992 set routing-instances SECURE_VRF vrf-target target:64730:992 set routing-instances SECURE_VRF vrf-table-label set routing-instances Tenant1_VRF routing-options multipath set routing-instances Tenant1_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances Tenant1_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances Tenant1_VRF protocols evpn ip-prefix-routes vni 9110 set routing-instances Tenant1_VRF protocols evpn ip-prefix-routes export T5_EXPORT set routing-instances Tenant1_VRF instance-type vrf set routing-instances Tenant1_VRF interface xe-0/0/28:0.110 set routing-instances Tenant1_VRF interface xe-0/0/28:1.110 set routing-instances Tenant1_VRF interface xe-0/0/39:0.0 set routing-instances Tenant1_VRF interface lo0.110 set routing-instances Tenant1_VRF route-distinguisher 10.80.224.139:9110 set routing-instances Tenant1_VRF vrf-target target:64730:110 set routing-instances Tenant1_VRF vrf-table-label set routing-instances Tenant2_VRF routing-options multipath set routing-instances Tenant2_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances Tenant2_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances Tenant2_VRF protocols evpn ip-prefix-routes vni 9112 set routing-instances Tenant2_VRF protocols evpn ip-prefix-routes export T5_EXPORT set routing-instances Tenant2_VRF instance-type vrf set routing-instances Tenant2_VRF interface xe-0/0/28:0.112 set routing-instances Tenant2_VRF interface xe-0/0/28:1.112 set routing-instances Tenant2_VRF interface lo0.112 set routing-instances Tenant2_VRF route-distinguisher 10.80.224.139:9112 set routing-instances Tenant2_VRF vrf-target target:64730:112 set routing-instances Tenant2_VRF vrf-table-label set routing-options router-id 10.80.224.139 set routing-options autonomous-system 64730 set routing-options forwarding-table export ECMP-POLICY set routing-options forwarding-table ecmp-fast-reroute set routing-options forwarding-table chained-composite-next-hop ingress evpn set protocols bgp group EVPN_FABRIC type internal set protocols bgp group EVPN_FABRIC description "Connection to EVPN Fabric RRs (tenants.bgp_reflector)" set protocols bgp group EVPN_FABRIC local-address 10.80.224.139 set protocols bgp group EVPN_FABRIC family evpn signaling set protocols bgp group EVPN_FABRIC local-as 64730 set protocols bgp group EVPN_FABRIC multipath set protocols bgp group EVPN_FABRIC neighbor 10.80.224.149 set protocols bgp group EVPN_FABRIC neighbor 10.80.224.150 set protocols bgp group UNDERLAY type external set protocols bgp group UNDERLAY description "Connection to EBGP UNDERLAY" set protocols bgp group UNDERLAY family inet unicast set protocols bgp group UNDERLAY export FROM_Lo0 set protocols bgp group UNDERLAY export FROM_UNDERLAY_BGP set protocols bgp group UNDERLAY local-as 65011 set protocols bgp group UNDERLAY multipath multiple-as set protocols bgp group UNDERLAY bfd-liveness-detection minimum-interval 350 set protocols bgp group UNDERLAY bfd-liveness-detection multiplier 3 set protocols bgp group UNDERLAY neighbor 10.80.224.0 peer-as 10021 set protocols bgp group UNDERLAY neighbor 10.80.224.10 peer-as 10022 set protocols bgp hold-time 10 set protocols bgp log-updown set protocols l2-learning global-mac-table-aging-time 600 set protocols l2-learning global-mac-ip-table-aging-time 300 set protocols lldp port-id-subtype interface-name set protocols lldp interface all set protocols lldp-med interface all set protocols igmp-snooping vlan default set vlans V991 vlan-id 991 set vlans V991 l3-interface irb.991 set vlans V992 vlan-id 992 set vlans V992 l3-interface irb.992
방화벽 구성
set system host-name firewall set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Allow_EP1_to_EP2 match source-address 10.1.110.11 set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Allow_EP1_to_EP2 match destination-address 10.1.111.21 set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Allow_EP1_to_EP2 match application junos-https set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Allow_EP1_to_EP2 match application junos-ssh set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Allow_EP1_to_EP2 match application junos-ping set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Allow_EP1_to_EP2 match application junos-udp-any set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Allow_EP1_to_EP2 then permit set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Block_All match source-address any set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Block_All match destination-address any set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Block_All match application any set security policies from-zone INSPECT_Zone to-zone SECURE_Zone policy Block_All then deny set security policies from-zone SECURE_Zone to-zone INSPECT_Zone policy Allow_All match source-address any set security policies from-zone SECURE_Zone to-zone INSPECT_Zone policy Allow_All match destination-address any set security policies from-zone SECURE_Zone to-zone INSPECT_Zone policy Allow_All match application any set security policies from-zone SECURE_Zone to-zone INSPECT_Zone policy Allow_All then permit set security zones security-zone INSPECT_Zone address-book address 10.1.110.11 10.1.110.11/32 set security zones security-zone INSPECT_Zone address-book address EP1 10.1.110.11/32 set security zones security-zone INSPECT_Zone host-inbound-traffic system-services all set security zones security-zone INSPECT_Zone host-inbound-traffic protocols all set security zones security-zone INSPECT_Zone interfaces xe-0/0/4.991 set security zones security-zone INSPECT_Zone interfaces xe-0/0/5.991 set security zones security-zone SECURE_Zone address-book address 10.1.111.21 10.1.111.21/32 set security zones security-zone SECURE_Zone address-book address EP2 10.1.111.21/32 set security zones security-zone SECURE_Zone host-inbound-traffic system-services all set security zones security-zone SECURE_Zone host-inbound-traffic protocols all set security zones security-zone SECURE_Zone interfaces xe-0/0/4.992 set security zones security-zone SECURE_Zone interfaces xe-0/0/5.992 set interfaces xe-0/0/4 vlan-tagging set interfaces xe-0/0/4 unit 991 vlan-id 991 set interfaces xe-0/0/4 unit 991 family inet address 10.81.91.1/30 set interfaces xe-0/0/4 unit 992 vlan-id 992 set interfaces xe-0/0/4 unit 992 family inet address 10.81.92.1/30 set interfaces xe-0/0/5 vlan-tagging set interfaces xe-0/0/5 unit 991 vlan-id 991 set interfaces xe-0/0/5 unit 991 family inet address 10.81.91.5/30 set interfaces xe-0/0/5 unit 992 vlan-id 992 set interfaces xe-0/0/5 unit 992 family inet address 10.81.92.5/30 set policy-options policy-statement Export-Default-Route term 10 from route-filter 0.0.0.0/0 exact set policy-options policy-statement Export-Default-Route term 10 then accept set policy-options policy-statement Export-Default-Route term 100 then reject set protocols bgp group ServiceLeaf type external set protocols bgp group ServiceLeaf export Export-Default-Route set protocols bgp group ServiceLeaf local-as 64777 set protocols bgp group ServiceLeaf neighbor 10.81.91.2 peer-as 64730 set protocols bgp group ServiceLeaf neighbor 10.81.92.2 peer-as 64730 set protocols bgp group ServiceLeaf neighbor 10.81.91.6 peer-as 64730 set protocols bgp group ServiceLeaf neighbor 10.81.92.6 peer-as 64730
