通过 SRX 系列设备对 EVPN-VXLAN 进行隧道检测
总结 阅读本主题,了解如何设置安全设备以对 EVPN-VXLAN 执行隧道检测,从而提供嵌入式安全性。
概述
(以太网 VPN)EVPN-(虚拟可扩展 LAN)VXLAN 为企业提供了一个用于管理园区和数据中心网络的通用框架。
移动和物联网设备的使用量迅速增加,为网络增加了大量的端点。现代企业网络必须快速扩展,以便提供对设备的即时访问,并扩展这些端点的安全性和控制力。
为了提供端点灵活性,EVPN-VXLAN 将底层网络(物理拓扑)与叠加网络(虚拟拓扑)分离。通过使用叠加,您可以灵活地在园区和数据中心的端点之间提供第 2 层/第 3 层连接,同时保持一致的底层架构。
您可以在 EVPN-VXLAN 解决方案中使用 SRX 系列防火墙连接园区、数据中心、分支机构和公共云环境中的端点,同时提供嵌入式安全性。
从 Junos OS 21.1R1 版开始,SRX 系列防火墙还可以对 EVPN-VXLAN 隧道流量应用以下第 4 层/第 7 层安全服务:
应用程序识别
国内流离失所者
瞻博网络 ATP(以前称为 ATP 云)
内容安全
图 1 显示了基于 Edge 路由桥接 (ERB) 的 EVPN-VXLAN 交换矩阵的典型部署方案,其中 SRX 系列防火墙充当增强型边界叶 (EBL) 角色。EBL 增强了边界叶的传统作用,能够对 VXLAN 隧道中的流量执行检查。
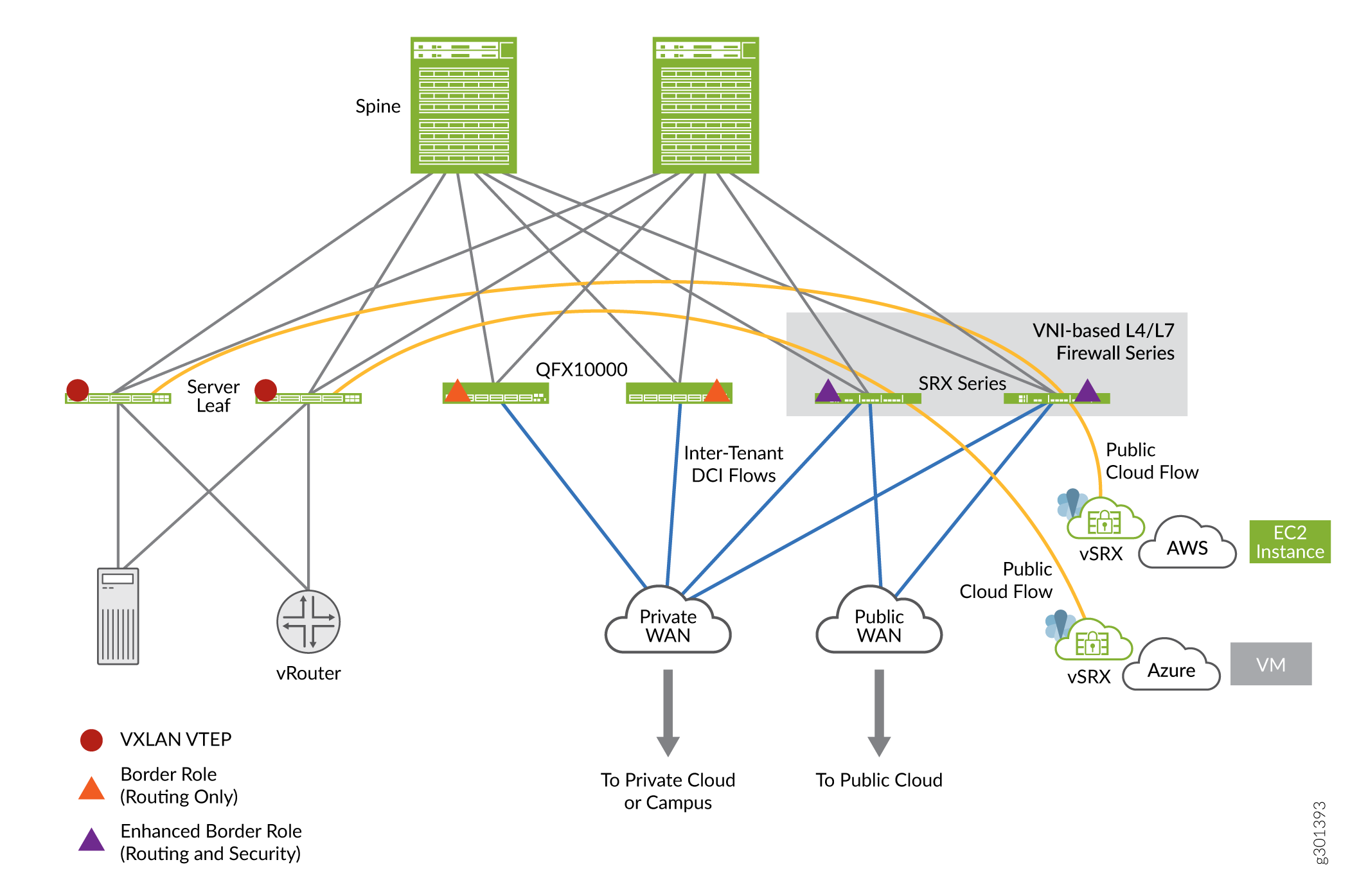 EVPN-VXLAN 架构
EVPN-VXLAN 架构
在图中,源自叶 1 设备的 VXLAN 流量遍历用作 EBL 的 SRX 系列防火墙。在此用例中,SRX 系列防火墙放置在边界,即园区或数据中心的入口和出口点,以便对通过防火墙的 VXLAN 封装数据包进行状态检测。
在架构图中,您可以注意到 SRX 系列防火墙位于两个 VTEP 设备(对网络流量执行 VXLAN 封装和解封装的设备)之间。当您使用适当的安全策略启用隧道检测功能时,SRX 系列防火墙会执行状态检测。
好处
在 EVPN VXLAN 中添加 SRX 系列防火墙可提供:
- 借助 EVPN-VXLAN 叠加网络中的企业级防火墙功能提高安全性。
- 通过第 4 层/第 7 层安全服务针对 VXLAN 封装流量进行增强的隧道检测。
示例 - 为 EVPN-VXLAN 隧道检测配置安全策略
使用此示例配置安全策略,以便对 SRX 系列防火墙上的 EVPN EVPN-VXLAN 隧道流量进行检查。
要求
此示例使用以下硬件和软件组件:
- SRX 系列防火墙或 vSRX 虚拟防火墙
- Junos OS 20.4R1 版
此示例假定您已经有一个基于 EVPN-VXLAN 的网络,并希望在 SRX 系列防火墙上启用隧道检测。
开始之前
- 确保 SRX 系列防火墙上具有有效的应用程序标识功能许可证,并且在设备上安装了应用程序签名包。
- 确保您了解 EVPN 和 VXLAN 的工作原理。请参阅 EVPN-VXLAN 园区架构 ,详细了解 EVPN-VXLAN
此示例假定您已经有一个基于 EVPN-VXLAN 的网络交换矩阵,并希望在 SRX 系列防火墙上启用隧道检测。您可以在 完整设备配置中查看此示例中使用的叶设备和主干设备的示例配置。
概述
在此示例中,我们将重点配置 SRX 系列防火墙,该防火墙是工作 EVPN-VXLAN 网络的一部分,该网络由两个每个站点和一个 IP 交换矩阵的 DC 位置组成。SRX 系列防火墙位于两个数据中心之间的数据中心互连 (DCI) 角色中。在此配置中,当您启用隧道检测时,SRX 系列防火墙会对在 DC 之间流动的 VXLAN 封装流量执行状态检测。
在本例中,我们使用 图 2 所示的拓扑结构。
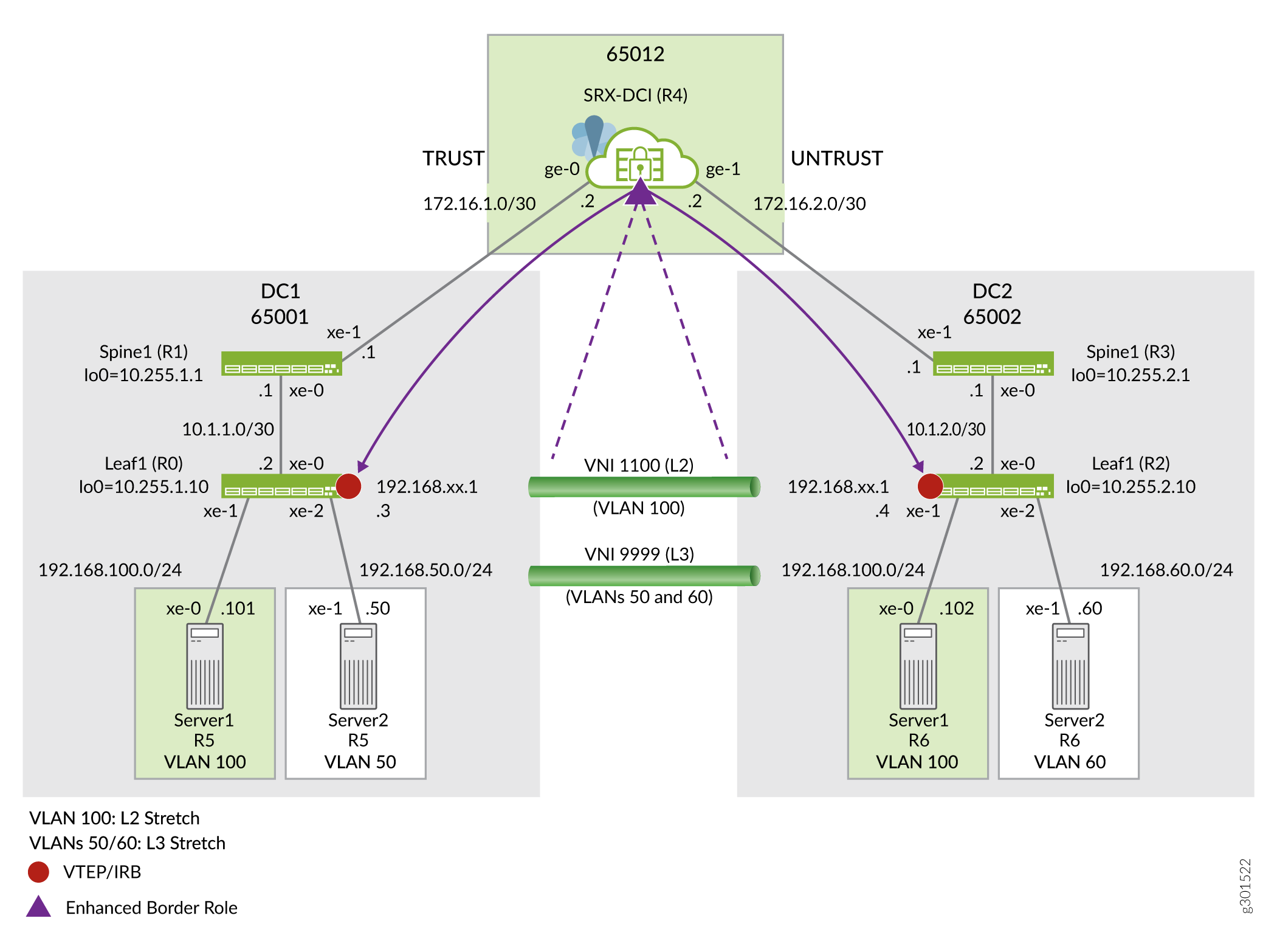 的拓扑
的拓扑
如拓扑所示,SRX 系列防火墙正在检查来自 DC-1 和 DC-2 数据中心叶子上的 VXLAN 隧道端点 (VTEP) 的中转 VLAN 封装流量。任何充当第 2 层或第 3 层 VXLAN 网关的瞻博网络设备(包括物理和虚拟设备)都可以作为 VTEP 设备来执行封装和解封装。
从服务器 1 收到第 2 层或第 3 层数据包后,叶 1 VTEP 添加相应的 VXLAN 报头,然后使用 IPv4 外部报头封装数据包,以便于通过 IPv4 底层网络建立数据包隧道。然后,叶 2 上的远程 VTEP 对流量进行解封装,并将原始数据包转发至目标主机。借助 Junos 软件 20.4 版,SRX 系列防火墙能够对通过它的 VXLAN 封装叠加网络流量执行隧道检测。
在此示例中,您将创建一个安全策略来启用对封装在 VXLAN 隧道中的流量的检查。在本例中,我们使用 表 1 中所述的参数。
| 参数 | 说明 | 参数名称 |
|---|---|---|
| 安全策略 | 用于创建由 VXLAN 叠加网络流量触发的流会话的策略。此策略引用外部 IP 源和目标地址。即源和目标 VTEP 的 IP 地址。在此示例中,这是叶的环路地址。 | 小一 |
| 策略集 | 内部流量检查策略。此策略对匹配的 VXLAN 隧道流量的内容进行操作。 | PSET-1 |
| 隧道检测配置文件 | 指定 VXLAN 隧道上的安全检查参数。 | TP-1 |
| VXLAN 网络标识符 (VNI) 列表或范围的名称 | 用于唯一标识 VXLAN 隧道 ID 的列表或范围。 | VLAN-100 |
| VXLAN 隧道标识符名称。 | 用于在隧道检测配置文件中以符号方式命名 VXLAN 隧道。 | VNI-1100 |
在 SRX 系列防火墙上配置隧道检测安全策略时,当数据包与安全策略匹配时,它会解封装数据包以访问内部标头。接下来,它会应用隧道检查配置文件来确定是否允许内部流量。安全设备使用内部数据包内容和应用的隧道检测配置文件参数执行策略查找,然后对内部会话执行状态检测。
配置
在此示例中,您将在 SRX 系列防火墙上配置以下功能:
- 定义信任和不信任区域以允许所有主机流量。这支持到主干设备的 BGP 会话,并允许来自任一区域 (DC) 的 SSH 等。
- 在 VNI 1100(针对 VLAN 100 延伸的第 2 层)中检查 192.168.100.0/24 子网中所有主机从 DC1 流向 DC2 的流量。策略应允许 ping,但拒绝所有其他流量。
- 允许从 DC2 到 DC1 的所有返回流量,而不进行隧道检查。
- 允许所有其他底层和叠加网络流量,而无需从 DC1 到 DC2 进行 VXLAN 隧道检查。
使用以下步骤在 VXLAN-EVPN 环境中对安全设备启用隧道检测:
为此示例中使用的所有设备提供了 完整的功能配置, 以帮助读者测试此示例。
此示例重点介绍启用和验证 VXLAN 隧道检测功能所需的配置步骤。假定 SRX 系列防火墙配置了接口寻址、BGP 对等和策略,以支持其 DCI 角色。
CLI 快速配置
要在 SRX 系列防火墙上快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改任何必要的详细信息以匹配您的网络配置,然后将命令复制并粘贴到 [edit] 层次结构级别的 CLI 中。
SRX 系列设备上的配置
set system host-name r4-dci-ebr set security address-book global address vtep-untrust 10.255.2.0/24 set security address-book global address vtep-trust 10.255.1.0/24 set security address-book global address vlan100 192.168.100.0/24 set security policies from-zone trust to-zone untrust policy P1 match source-address vtep-trust set security policies from-zone trust to-zone untrust policy P1 match destination-address vtep-untrust set security policies from-zone trust to-zone untrust policy P1 match application junos-vxlan set security policies from-zone trust to-zone untrust policy P1 then permit tunnel-inspection TP-1 set security policies from-zone untrust to-zone trust policy accept-all-dc2 match source-address any set security policies from-zone untrust to-zone trust policy accept-all-dc2 match destination-address any set security policies from-zone untrust to-zone trust policy accept-all-dc2 match application any set security policies from-zone untrust to-zone trust policy accept-all-dc2 then permit set security policies policy-set PSET-1 policy PSET-1-P1 match source-address vlan100 set security policies policy-set PSET-1 policy PSET-1-P1 match destination-address vlan100 set security policies policy-set PSET-1 policy PSET-1-P1 match application junos-icmp-all set security policies policy-set PSET-1 policy PSET-1-P1 then permit set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces ge-0/0/0.0 set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols all set security zones security-zone untrust interfaces ge-0/0/1.0 set security tunnel-inspection inspection-profile TP-1 vxlan VNI-1100 policy-set PSET-1 set security tunnel-inspection inspection-profile TP-1 vxlan VNI-1100 vni VLAN-100 set security tunnel-inspection vni VLAN-100 vni-id 1100 set interfaces ge-0/0/0 description "Link to DC1 Spine 1" set interfaces ge-0/0/0 mtu 9000 set interfaces ge-0/0/0 unit 0 family inet address 172.16.1.2/30 set interfaces ge-0/0/1 description "Link to DC2 Spine 1" set interfaces ge-0/0/1 mtu 9000 set interfaces ge-0/0/1 unit 0 family inet address 172.16.2.2/30
分步过程
- 配置安全区域、接口和地址簿。
[edit] user@@r4-dci-ebr# set security zones security-zone trust user@@r4-dci-ebr# set security zones security-zone untrust user@@r4-dci-ebr# set interfaces ge-0/0/0 description "Link to DC1 Spine 1" user@@r4-dci-ebr# set interfaces ge-0/0/0 mtu 9000 user@@r4-dci-ebr# set interfaces ge-0/0/0 unit 0 family inet address 172.16.1.2/30 user@@r4-dci-ebr# set interfaces ge-0/0/1 description "Link to DC2 Spine 1" user@@r4-dci-ebr# set interfaces ge-0/0/1 mtu 9000 user@@r4-dci-ebr# set interfaces ge-0/0/1 unit 0 family inet address 172.16.2.2/30 user@@r4-dci-ebr# set security zones security-zone trust host-inbound-traffic system-services all user@@r4-dci-ebr# set security zones security-zone trust host-inbound-traffic protocols all user@@r4-dci-ebr# set security zones security-zone trust interfaces ge-0/0/0.0 user@@r4-dci-ebr# set security zones security-zone untrust host-inbound-traffic system-services all user@@r4-dci-ebr# set security zones security-zone untrust host-inbound-traffic protocols all user@@r4-dci-ebr# set security zones security-zone untrust interfaces ge-0/0/1.0 user@@r4-dci-ebr# set security address-book global address vtep-untrust 10.255.2.0/24 user@@r4-dci-ebr# set security address-book global address vtep-trust 10.255.1.0/24 user@@r4-dci-ebr# set security address-book global address vlan100 192.168.100.0/24
定义隧道检测配置文件。您可以指定应检查的 VNI 的范围或列表。
[edit] user@@r4-dci-ebr# set security tunnel-inspection vni VLAN-100 vni-id 1100 user@@r4-dci-ebr# set security tunnel-inspection inspection-profile TP-1 vxlan VNI-1100 vni VLAN-100 user@@r4-dci-ebr# set security tunnel-inspection inspection-profile TP-1 vxlan VNI-1100 policy-set PSET-1
在此示例中,只需要一个 VNI,因此
隧道检测配置文件链接到 VNI 列表/范围以及应应用于具有匹配 VNI 的 VXLAN 隧道的相关策略。vni-id使用关键字而不是vni-range选项。- 创建要在外部会话上匹配的安全策略。
[edit] user@@r4-dci-ebr# set security policies from-zone trust to-zone untrust policy P1 match source-address vtep-trust user@@r4-dci-ebr# set security policies from-zone trust to-zone untrust policy P1 match destination-address vtep-untrust user@@r4-dci-ebr# set security policies from-zone trust to-zone untrust policy P1 match application junos-vxlan user@@r4-dci-ebr# set security policies from-zone trust to-zone untrust policy P1 then permit tunnel-inspection TP-1
TP-1您在上一步中定义的隧道检测配置文件。在此示例中,目标是检查源自 DC1 并在 DC2 终止的 VXLAN 隧道。因此,不需要在返回流量上匹配第二个策略(DC2 叶 1 为源 VTEP)。 为内部会话创建策略集。
[edit] user@@r4-dci-ebr# set security policies policy-set PSET-1 policy PSET-1-P1 match source-address vlan100 user@@r4-dci-ebr# set security policies policy-set PSET-1 policy PSET-1-P1 match destination-address vlan100 user@@r4-dci-ebr# set security policies policy-set PSET-1 policy PSET-1-P1 match application junos-icmp-all user@@r4-dci-ebr# set security policies policy-set PSET-1 policy PSET-1-P1 then permit
此策略针对匹配的 VXLAN 流量的有效负载执行安全检查。在此示例中,这是从 DC1 中 VLAN 100 上的服务器 1 发送到 DC2 中的服务器 1 的流量。通过指定
junos-icmp-all匹配条件,您可以确保 ping 请求和回复都可以从服务器 1 离子 DC1 传递到 DC2 中的服务器 1。如果指定junos-icmp-ping,则仅允许源自 DC1 的 ping。回想一下,在此示例中,只允许 ping 来帮助促进对结果功能的测试。您可以匹配
application any以允许所有流量,或更改匹配标准以满足您的特定安全需求。定义接受数据中心之间的所有其他流量所需的策略,而无需进行任何隧道检测。
[edit] user@@r4-dci-ebr# set security policies from-zone trust to-zone untrust policy accept-rest match source-address any user@@r4-dci-ebr# set security policies from-zone trust to-zone untrust policy accept-rest match destination-address any user@@r4-dci-ebr# set security policies from-zone trust to-zone untrust policy accept-rest match application any user@@r4-dci-ebr# set security policies from-zone trust to-zone untrust policy accept-rest then permit user@@r4-dci-ebr# set security policies from-zone untrust to-zone trust policy accept-all-dc2 match source-address any user@@r4-dci-ebr# set security policies from-zone untrust to-zone trust policy accept-all-dc2 match destination-address any user@@r4-dci-ebr# set security policies from-zone untrust to-zone trust policy accept-all-dc2 match application any user@@r4-dci-ebr# set security policies from-zone untrust to-zone trust policy accept-all-dc2 then permit
结果
在配置模式下,输入 show security 命令确认您的配置。如果输出未显示预期的配置,请重复此示例中的配置说明以进行更正。
[edit]
user@host# show security
address-book {
global {
address vtep-untrust 10.255.2.0/24;
address vtep-trust 10.255.1.0/24;
address vlan100 192.168.100.0/24;
}
}
policies {
from-zone trust to-zone untrust {
policy P1 {
match {
source-address vtep-trust;
destination-address vtep-untrust;
application junos-vxlan;
}
then {
permit {
tunnel-inspection {
TP-1;
}
}
}
}
policy accept-rest {
match {
source-address any;
destination-address any;
application any;
}
then {
permit;
}
}
}
from-zone untrust to-zone trust {
policy accept-all-dc2 {
match {
source-address any;
destination-address any;
application any;
}
then {
permit;
}
}
}
policy-set PSET-1 {
policy PSET-1-P1 {
match {
source-address vlan100;
destination-address vlan100;
application junos-icmp-all;
}
then {
permit;
}
}
}
}
zones {
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
ge-0/0/0.0;
}
}
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
ge-0/0/1.0;
}
}
}
tunnel-inspection {
inspection-profile TP-1 {
vxlan VNI-1100 {
policy-set PSET-1;
vni VLAN-100;
}
}
vni VLAN-100 {
vni-id 1100;
}
}
如果在设备上完成功能配置,请从配置模式输入 commit 。
验证
此时,您应该在 DC1 中的服务器 1 和 DC2 中的服务器 1 之间生成 ping 流量。ping 应该成功。在完成验证任务时,允许此测试流量在后台运行。
r5-dc1_server1> ping 192.168.100.102 PING 192.168.100.102 (192.168.100.102): 56 data bytes 64 bytes from 192.168.100.102: icmp_seq=0 ttl=64 time=565.451 ms 64 bytes from 192.168.100.102: icmp_seq=1 ttl=64 time=541.035 ms 64 bytes from 192.168.100.102: icmp_seq=2 ttl=64 time=651.420 ms 64 bytes from 192.168.100.102: icmp_seq=3 ttl=64 time=303.533 ms . . .
验证内部策略详细信息
Purpose
验证应用于内部会话的策略的详细信息。
Action
在操作模式下,输入 show security policies policy-set PSET-1 命令。
From zone: PSET-1, To zone: PSET-1
Policy: PSET-1-P1, State: enabled, Index: 7, Scope Policy: 0, Sequence number: 1, Log Profile ID: 0
From zones: any
To zones: any
Source vrf group: any
Destination vrf group: any
Source addresses: vlan100
Destination addresses: vlan100
Applications: junos-icmp-all
Source identity feeds: any
Destination identity feeds: any
Action: permit
检查隧道检测流量
Purpose
显示隧道检测流量详细信息。
Action
在操作模式下,输入 show security flow tunnel-inspection statistics 命令。
Flow Tunnel-inspection statistics:
Tunnel-inspection type VXLAN:
overlay session active: 4
overlay session create: 289
overlay session close: 285
underlay session active: 3
underlay session create: 31
underlay session close: 28
input packets: 607
input bytes: 171835
output packets: 418
output bytes: 75627
bypass packets: 0
bypass bytes: 0
检查隧道检测配置文件和 VNI
Purpose
显示隧道检测配置文件和 VNI 详细信息。
Action
在操作模式下,输入 show security tunnel-inspection profiles 命令。
Logical system: root-logical-system
Profile count: 1
Profile: TP-1
Type: VXLAN
Vxlan count: 1
Vxlan name: VXT-1
VNI count: 1
VNI:VNI-1
Policy set: PSET-1
Inspection level: 1
在操作模式下,输入 show security tunnel-inspection vnis 命令。
Logical system: root-logical-system
VNI count: 2
VNI name: VLAN-100
VNI id count: 1
[1100 - 1100]
VNI name: VNI-1
VNI id count: 1
[1100 - 1100]
检查安全流
Purpose
在 SRX 上显示 VXLAN 安全流信息,以确认 VXLAN 隧道检测正常工作。
Action
在操作模式下,输入 show security flow session vxlan-vni 1100 命令。
Session ID: 3811, Policy name: PSET-1-P1/7, State: Stand-alone, Timeout: 2, Valid In: 192.168.100.101/47883 --> 192.168.100.102/82;icmp, Conn Tag: 0xfcd, If: ge-0/0/0.0, Pkts: 1, Bytes: 84, Type: VXLAN, VNI: 1100, Tunnel Session ID: 2193 Out: 192.168.100.102/82 --> 192.168.100.101/47883;icmp, Conn Tag: 0xfcd, If: ge-0/0/1.0, Pkts: 0, Bytes: 0, Type: VXLAN, VNI: 0, Tunnel Session ID: 0 Session ID: 3812, Policy name: PSET-1-P1/7, State: Stand-alone, Timeout: 2, Valid In: 192.168.100.101/47883 --> 192.168.100.102/83;icmp, Conn Tag: 0xfcd, If: ge-0/0/0.0, Pkts: 1, Bytes: 84, Type: VXLAN, VNI: 1100, Tunnel Session ID: 2193 Out: 192.168.100.102/83 --> 192.168.100.101/47883;icmp, Conn Tag: 0xfcd, If: ge-0/0/1.0, Pkts: 0, Bytes: 0, Type: VXLAN, VNI: 0, Tunnel Session ID: 0 . . .
确认 SSH 已被阻止
Purpose
尝试在 DC1 中的服务器 1 和 DC2 中的服务器 2 之间建立 SSH 会话。根据仅允许 ping 流量的策略,应在 SRX 上阻止此会话。
Action
在操作模式下,输入 show security flow session vxlan-vni 1100 命令。
r5-dc1_server1> ssh 192.168.100.102 ssh: connect to host 192.168.100.102 port 22: Operation timed out r5_dc1_server1>
用于区域级检测、IDP、内容安全和用于隧道检测的高级反恶意软件的配置
如果要配置区域级检测,并将第 7 层服务(如 IDP、瞻博网络 ATP、内容安全和高级反恶意软件)应用于隧道流量,请使用此步骤。从 Junos OS 21.1R1 版开始支持此功能。
此示例使用以下硬件和软件组件:
- SRX 系列防火墙或 vSRX 虚拟防火墙
- Junos OS 21.1R1 版
我们对外部会话使用的地址簿、安全区域、接口、隧道检测配置文件和安全策略配置与在配置中创建的配置相同
此步骤假定您已向瞻博网络 ATP 注册 SRX 系列防火墙。有关如何注册 SRX 系列防火墙的详细信息,请参阅 使用瞻博网络高级威胁防御云注册 SRX 系列设备。
在此配置中,您将为内部会话创建策略集,并将 IDP、内容安全、高级反恶意软件应用于隧道流量。
CLI 快速配置
要在 SRX 系列防火墙上快速配置此示例,请复制以下命令,将其粘贴到文本文件中,删除所有换行符,更改任何必要的详细信息以匹配您的网络配置,然后将命令复制并粘贴到 [edit] 层次结构级别的 CLI 中。
SRX 系列设备上的配置
set system host-name r4-dci-ebr set security address-book global address vtep-untrust 10.255.2.0/24 set security address-book global address vtep-trust 10.255.1.0/24 set security address-book global address vlan100 192.168.100.0/24 set security policies from-zone trust to-zone untrust policy P1 match source-address vtep-trust set security policies from-zone trust to-zone untrust policy P1 match destination-address vtep-untrust set security policies from-zone trust to-zone untrust policy P1 match application junos-vxlan set security policies from-zone trust to-zone untrust policy P1 then permit tunnel-inspection TP-1 set security policies from-zone untrust to-zone trust policy accept-all-dc2 match source-address any set security policies from-zone untrust to-zone trust policy accept-all-dc2 match destination-address any set security policies from-zone untrust to-zone trust policy accept-all-dc2 match application any set security policies from-zone untrust to-zone trust policy accept-all-dc2 then permit set security policies policy-set PSET-1 policy PSET-1-P1 match source-address vlan100 set security policies policy-set PSET-1 policy PSET-1-P1 match destination-address vlan100 set security policies policy-set PSET-1 policy PSET-1-P1 match application junos-icmp-all set security policies policy-set PSET-1 policy PSET-1-P1 match dynamic-application any set security policies policy-set PSET-1 policy PSET-1-P1 match url-category any set security policies policy-set PSET-1 policy PSET-1-P1 match from-zone trust set security policies policy-set PSET-1 policy PSET-1-P1 match to-zone untrust set security policies policy-set PSET-1 policy PSET-1-P1 then permit set security policies policy-set PSET-1 policy PSET-1-P1 then permit set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces ge-0/0/0.0 set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols all set security zones security-zone untrust interfaces ge-0/0/1.0 set security tunnel-inspection inspection-profile TP-1 vxlan VNI-1100 policy-set PSET-1 set security tunnel-inspection inspection-profile TP-1 vxlan VNI-1100 vni VLAN-100 set security tunnel-inspection vni VLAN-100 vni-id 1100 set interfaces ge-0/0/0 description "Link to DC1 Spine 1" set interfaces ge-0/0/0 mtu 9000 set interfaces ge-0/0/0 unit 0 family inet address 172.16.1.2/30 set interfaces ge-0/0/1 description "Link to DC2 Spine 1" set interfaces ge-0/0/1 mtu 9000 set interfaces ge-0/0/1 unit 0 family inet address 172.16.2.2/30
为隧道检测创建区域级检测
您可以为内部流量的 EVPN-VXLAN 隧道检测添加区域级策略控制。此策略针对匹配的 VXLAN 流量的有效负载执行安全检查。在以下步骤中,您将为流量指定从区域和到区域。
-
[edit] user@r4-dci-ebr# set security policies policy-set PSET-1 policy PSET-1-P1 match source-address vlan100 user@r4-dci-ebr# set security policies policy-set PSET-1 policy PSET-1-P1 match destination-address vlan100 user@r4-dci-ebr# set security policies policy-set PSET-1 policy PSET-1-P1 match application any user@r4-dci-ebr# set security policies policy-set PSET-1 policy PSET-1-P1 match dynamic-application any user@r4-dci-ebr# set security policies policy-set PSET-1 policy PSET-1-P1 match url-category any user@r4-dci-ebr# set security policies policy-set PSET-1 policy PSET-1-P1 match from-zone trust user@r4-dci-ebr# set security policies policy-set PSET-1 policy PSET-1-P1 match to-zone untrust user@r4-dci-ebr# set security policies policy-set PSET-1 policy PSET-1-P1 then permit
为隧道检测创建 IDP、内容安全和高级反恶意软件
您可以添加安全服务,如 IDP、高级 aniti 恶意软件、内容安全、SSL 代理,以便对内部流量进行 EVPN-VXLAN 隧道检测。此策略针对匹配的 VXLAN 流量的有效负载执行安全检查。
在以下步骤中,您将启用 IDP、内容安全、SSL 代理、安全智能、高级反恶意软件服务等服务,方法是在流量与策略规则匹配时在安全策略允许操作中指定这些服务。
-
[edit] user@r4-dci-ebr# set security policies policy-set PSET-1 policy PSET-1-P1 match source-address vlan100 user@r4-dci-ebr# set security policies policy-set PSET-1 policy PSET-1-P1 match destination-address vlan100 user@r4-dci-ebr# set security policies policy-set PSET-1 policy PSET-1-P1 match application any user@r4-dci-ebr# set security policies policy-set PSET-1 policy PSET-1-P1 then permit application-services ssl-proxy profile-name ssl-inspect-profile-1 user@r4-dci-ebr# set security policies policy-set PSET-1 policy PSET-1-P1 then permit application-services security-intelligence-policy secintel1 user@r4-dci-ebr# set security policies policy-set PSET-1 policy PSET-1-P1 then permit application-services advanced-anti-malware-policy P3 user@r4-dci-ebr# set security policies policy-set PSET-1 policy PSET-1-P1 then permit application-services idp-policy idp123 user@r4-dci-ebr# set security policies policy-set PSET-1 policy PSET-1-P1 then permit application-services utm-policy P1
以下步骤一目了然地显示了内容安全、IDP 和高级反恶意软件策略的配置片段。
配置高级反恶意软件策略。
[edit] user@r4-dci-ebr# set services advanced-anti-malware policy P3 http inspection-profile scripts user@r4-dci-ebr# set services advanced-anti-malware policy P3 http action block user@r4-dci-ebr# set services advanced-anti-malware policy P3 http notification log user@r4-dci-ebr# set services advanced-anti-malware policy P3 http client-notify message "AAMW Blocked!" user@r4-dci-ebr# set services advanced-anti-malware policy P3 verdict-threshold recommended user@r4-dci-ebr# set services advanced-anti-malware policy P3 fallback-options action permit user@r4-dci-ebr# set services advanced-anti-malware policy P3 fallback-options notification log
配置安全智能配置文件。
[edit] user@r4-dci-ebr# set services security-intelligence url https://cloudfeeds.argonqa.junipersecurity.net/api/manifest.xml user@r4-dci-ebr# set services security-intelligence authentication tls-profile aamw-ssl user@r4-dci-ebr# set services security-intelligence profile cc_profile category CC user@r4-dci-ebr# set services security-intelligence profile cc_profile rule cc_rule match threat-level 1 user@r4-dci-ebr# set services security-intelligence profile cc_profile rule cc_rule match threat-level 2 user@r4-dci-ebr# set services security-intelligence profile cc_profile rule cc_rule match threat-level 4 user@r4-dci-ebr# set services security-intelligence profile cc_profile rule cc_rule match threat-level 5 user@r4-dci-ebr# set services security-intelligence profile cc_profile rule cc_rule match threat-level 6 user@r4-dci-ebr# set services security-intelligence profile cc_profile rule cc_rule match threat-level 7 user@r4-dci-ebr# set services security-intelligence profile cc_profile rule cc_rule match threat-level 8 user@r4-dci-ebr# set services security-intelligence profile cc_profile rule cc_rule match threat-level 9 user@r4-dci-ebr# set services security-intelligence profile cc_profile rule cc_rule match threat-level 10 user@r4-dci-ebr# set services security-intelligence profile cc_profile rule cc_rule then action block close user@r4-dci-ebr# set services security-intelligence profile cc_profile rule cc_rule then log user@r4-dci-ebr# set services security-intelligence profile ih_profile category Infected-Hosts user@r4-dci-ebr# set services security-intelligence profile ih_profile rule ih_rule match threat-level 7 user@r4-dci-ebr# set services security-intelligence profile ih_profile rule ih_rule match threat-level 8 user@r4-dci-ebr# set services security-intelligence profile ih_profile rule ih_rule match threat-level 9 user@r4-dci-ebr# set services security-intelligence profile ih_profile rule ih_rule match threat-level 10 user@r4-dci-ebr# set services security-intelligence profile ih_profile rule ih_rule then action block close http message "Blocked!" user@r4-dci-ebr# set services security-intelligence profile ih_profile rule ih_rule then log user@r4-dci-ebr# set services security-intelligence policy secintel1 CC cc_profile user@r4-dci-ebr# set services security-intelligence policy secintel1 Infected-Hosts ih_profile
配置 IDP 策略。
[edit] user@r4-dci-ebr# set security idp idp-policy idp123 rulebase-ips rule rule1 match application junos-icmp-all user@r4-dci-ebr# set security idp idp-policy idp123 rulebase-ips rule rule1 then action no-action
配置内容安全策略。
[edit] user@r4-dci-ebr# set security utm default-configuration anti-virus type sophos-engine user@r4-dci-ebr## set security utm utm-policy P1 anti-virus http-profile junos-sophos-av-defaults
配置 SSL 配置文件。
[edit] user@r4-dci-ebr# set services ssl initiation profile aamw-ssl user@r4-dci-ebr# set services ssl proxy profile ssl-inspect-profile-1 root-ca VJSA
结果
在配置模式下,输入 show security 命令确认您的配置。如果输出未显示预期的配置,请重复此示例中的配置说明以进行更正。
[edit]
user@host# show security
address-book {
global {
address vtep-untrust 10.255.2.0/24;
address vtep-trust 10.255.1.0/24;
address vlan100 192.168.100.0/24;
}
}
policies {
from-zone trust to-zone untrust {
policy P1 {
match {
source-address vtep-trust;
destination-address vtep-untrust;
application junos-vxlan;
}
then {
permit {
tunnel-inspection {
TP-1;
}
}
}
}
policy accept-rest {
match {
source-address any;
destination-address any;
application any;
}
then {
permit;
}
}
}
from-zone untrust to-zone trust {
policy accept-all-dc2 {
match {
source-address any;
destination-address any;
application any;
}
then {
permit;
}
}
}
policy-set PSET-1 {
policy PSET-1-P1 {
match {
source-address vlan100;
destination-address vlan100;
application junos-icmp-all;
dynamic-application any;
url-category any;
from-zone trust;
to-zone untrust;
}
then {
permit {
application-services {
idp-policy idp123;
ssl-proxy {
profile-name ssl-inspect-profile-1;
}
utm-policy P1;
security-intelligence-policy secintel1;
advanced-anti-malware-policy P3;
}
}
}
}
}
}
}
zones {
security-zone trust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
ge-0/0/0.0;
}
}
security-zone untrust {
host-inbound-traffic {
system-services {
all;
}
protocols {
all;
}
}
interfaces {
ge-0/0/1.0;
}
}
}
tunnel-inspection {
inspection-profile TP-1 {
vxlan VNI-1100 {
policy-set PSET-1;
vni VLAN-100;
}
}
vni VLAN-100 {
vni-id 1100;
}
}
[edit]
user@host# show services
application-identification;
ssl {
initiation {
profile aamw-ssl;
}
proxy {
profile ssl-inspect-profile-1 {
root-ca VJSA;
}
}
}
advanced-anti-malware {
policy P3 {
http {
inspection-profile scripts;
action block;
client-notify {
message "AAMW Blocked!";
}
notification {
log;
}
}
verdict-threshold recommended;
fallback-options {
action permit;
notification {
log;
}
}
}
}
security-intelligence {
url https://cloudfeeds.argonqa.junipersecurity.net/api/manifest.xml;
authentication {
tls-profile aamw-ssl;
}
profile cc_profile {
category CC;
rule cc_rule {
match {
threat-level [ 1 2 4 5 6 7 8 9 10 ];
}
then {
action {
block {
close;
}
}
log;
}
}
}
profile ih_profile {
category Infected-Hosts;
rule ih_rule {
match {
threat-level [ 7 8 9 10 ];
}
then {
action {
block {
close {
http {
message "Blocked!";
}
}
}
}
log;
}
}
}
policy secintel1 {
CC {
cc_profile;
}
Infected-Hosts {
ih_profile;
}
}
}
如果在设备上完成功能配置,请从配置模式输入 commit 。
完整的设备配置
请参阅这些配置以更好地理解或重新创建此示例的上下文。其中包括构成 DC 交换矩阵的 QFX 系列交换机的完整基于 ERB 的 EVPN-VXLAN 配置,以及基本和高级 VXLAN 隧道检测示例的 SRX 系列防火墙的结束状态。
提供的配置不显示用户登录、系统日志记录或管理相关配置,因为这些配置因位置而异,与 VXLAN 隧道检测功能无关。
有关配置 EVPN-VXLAN 的更多详细信息和示例,请参阅 使用 ERB 为园区网络配置 EVPN-VXLAN 交换矩阵中的网络配置示例。
叶 1 设备上的配置
set system host-name r0_dc1_leaf1 set interfaces xe-0/0/0 mtu 9000 set interfaces xe-0/0/0 unit 0 family inet address 10.1.1.2/30 set interfaces xe-0/0/1 unit 0 family ethernet-switching vlan members v100 set interfaces xe-0/0/2 unit 0 family ethernet-switching vlan members v50 set interfaces irb unit 50 virtual-gateway-accept-data set interfaces irb unit 50 family inet address 192.168.50.3/24 preferred set interfaces irb unit 50 family inet address 192.168.50.3/24 virtual-gateway-address 192.168.50.1 set interfaces irb unit 100 virtual-gateway-accept-data set interfaces irb unit 100 family inet address 192.168.100.3/24 preferred set interfaces irb unit 100 family inet address 192.168.100.3/24 virtual-gateway-address 192.168.100.1 set interfaces lo0 unit 0 family inet address 10.255.1.10/32 set interfaces lo0 unit 1 family inet address 10.255.10.10/32 set forwarding-options vxlan-routing next-hop 32768 set forwarding-options vxlan-routing overlay-ecmp set policy-options policy-statement ECMP-POLICY then load-balance per-packet set policy-options policy-statement FROM_Lo0 term 10 from interface lo0.0 set policy-options policy-statement FROM_Lo0 term 10 then accept set policy-options policy-statement FROM_Lo0 term 20 then reject set policy-options policy-statement OVERLAY_IMPORT term 5 from community comm_pod1 set policy-options policy-statement OVERLAY_IMPORT term 5 then accept set policy-options policy-statement OVERLAY_IMPORT term 10 from community comm_pod2 set policy-options policy-statement OVERLAY_IMPORT term 10 then accept set policy-options policy-statement OVERLAY_IMPORT term 20 from community shared_100_fm_pod2 set policy-options policy-statement OVERLAY_IMPORT term 20 from community shared_100_fm_pod1 set policy-options policy-statement OVERLAY_IMPORT term 20 then accept set policy-options policy-statement T5_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_EXPORT term fm_direct then accept set policy-options policy-statement T5_EXPORT term fm_static from protocol static set policy-options policy-statement T5_EXPORT term fm_static then accept set policy-options policy-statement T5_EXPORT term fm_v4_host from protocol evpn set policy-options policy-statement T5_EXPORT term fm_v4_host from route-filter 0.0.0.0/0 prefix-length-range /32-/32 set policy-options policy-statement T5_EXPORT term fm_v4_host then accept set policy-options policy-statement VRF1_T5_RT_EXPORT term t1 then community add target_t5_pod1 set policy-options policy-statement VRF1_T5_RT_EXPORT term t1 then accept set policy-options policy-statement VRF1_T5_RT_IMPORT term t1 from community target_t5_pod1 set policy-options policy-statement VRF1_T5_RT_IMPORT term t1 then accept set policy-options policy-statement VRF1_T5_RT_IMPORT term t2 from community target_t5_pod2 set policy-options policy-statement VRF1_T5_RT_IMPORT term t2 then accept set policy-options community comm_pod1 members target:65001:1 set policy-options community comm_pod2 members target:65002:2 set policy-options community shared_100_fm_pod1 members target:65001:100 set policy-options community shared_100_fm_pod2 members target:65002:100 set policy-options community target_t5_pod1 members target:65001:9999 set policy-options community target_t5_pod2 members target:65002:9999 set routing-instances TENANT_1_VRF routing-options multipath set routing-instances TENANT_1_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances TENANT_1_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances TENANT_1_VRF protocols evpn ip-prefix-routes vni 9999 set routing-instances TENANT_1_VRF protocols evpn ip-prefix-routes export T5_EXPORT set routing-instances TENANT_1_VRF instance-type vrf set routing-instances TENANT_1_VRF interface irb.50 set routing-instances TENANT_1_VRF interface irb.100 set routing-instances TENANT_1_VRF interface lo0.1 set routing-instances TENANT_1_VRF route-distinguisher 10.255.1.10:9999 set routing-instances TENANT_1_VRF vrf-import VRF1_T5_RT_IMPORT set routing-instances TENANT_1_VRF vrf-export VRF1_T5_RT_EXPORT set routing-instances TENANT_1_VRF vrf-table-label set routing-options router-id 10.255.1.10 set routing-options autonomous-system 65001 set routing-options forwarding-table export ECMP-POLICY set routing-options forwarding-table ecmp-fast-reroute set routing-options forwarding-table chained-composite-next-hop ingress evpn set protocols bgp group EVPN_FABRIC type internal set protocols bgp group EVPN_FABRIC local-address 10.255.1.10 set protocols bgp group EVPN_FABRIC family evpn signaling set protocols bgp group EVPN_FABRIC multipath set protocols bgp group EVPN_FABRIC bfd-liveness-detection minimum-interval 1000 set protocols bgp group EVPN_FABRIC bfd-liveness-detection multiplier 3 set protocols bgp group EVPN_FABRIC neighbor 10.255.1.1 set protocols bgp group UNDERLAY type external set protocols bgp group UNDERLAY family inet unicast set protocols bgp group UNDERLAY export FROM_Lo0 set protocols bgp group UNDERLAY local-as 65510 set protocols bgp group UNDERLAY multipath multiple-as set protocols bgp group UNDERLAY bfd-liveness-detection minimum-interval 350 set protocols bgp group UNDERLAY bfd-liveness-detection multiplier 3 set protocols bgp group UNDERLAY neighbor 10.1.1.1 peer-as 65511 set protocols evpn encapsulation vxlan set protocols evpn default-gateway no-gateway-community set protocols evpn vni-options vni 150 vrf-target target:65001:150 set protocols evpn vni-options vni 1100 vrf-target target:65001:100 set protocols evpn extended-vni-list 1100 set protocols evpn extended-vni-list 150 set protocols lldp interface all set switch-options vtep-source-interface lo0.0 set switch-options route-distinguisher 10.255.1.10:1 set switch-options vrf-import OVERLAY_IMPORT set switch-options vrf-target target:65001:1 set vlans v100 vlan-id 100 set vlans v100 l3-interface irb.100 set vlans v100 vxlan vni 1100 set vlans v50 vlan-id 50 set vlans v50 l3-interface irb.50 set vlans v50 vxlan vni 150
主干 1 设备上的配置
set system host-name r1_dc1_spine11 set interfaces xe-0/0/0 mtu 9000 set interfaces xe-0/0/0 unit 0 family inet address 10.1.1.1/30 set interfaces xe-0/0/1 mtu 9000 set interfaces xe-0/0/1 unit 0 family inet address 172.16.1.1/30 set interfaces lo0 unit 0 family inet address 10.255.1.1/32 set policy-options policy-statement ECMP-POLICY then load-balance per-packet set policy-options policy-statement FROM_Lo0 term 10 from interface lo0.0 set policy-options policy-statement FROM_Lo0 term 10 then accept set policy-options policy-statement FROM_Lo0 term 20 then reject set policy-options policy-statement UNDERLAY-EXPORT term LOOPBACK from route-filter 10.255.0.0/16 orlonger set policy-options policy-statement UNDERLAY-EXPORT term LOOPBACK from route-filter 10.1.0.0/16 orlonger set policy-options policy-statement UNDERLAY-EXPORT term LOOPBACK then accept set policy-options policy-statement UNDERLAY-EXPORT term DEFAULT then reject set policy-options policy-statement UNDERLAY-IMPORT term LOOPBACK from route-filter 10.255.0.0/16 orlonger set policy-options policy-statement UNDERLAY-IMPORT term LOOPBACK from route-filter 10.1.0.0/16 orlonger set policy-options policy-statement UNDERLAY-IMPORT term LOOPBACK then accept set policy-options policy-statement UNDERLAY-IMPORT term DEFAULT then reject set routing-options autonomous-system 65001 set routing-options forwarding-table export ECMP-POLICY set routing-options forwarding-table ecmp-fast-reroute set protocols bgp group EVPN_FABRIC type internal set protocols bgp group EVPN_FABRIC local-address 10.255.1.1 set protocols bgp group EVPN_FABRIC family evpn signaling set protocols bgp group EVPN_FABRIC cluster 10.255.1.1 set protocols bgp group EVPN_FABRIC multipath set protocols bgp group EVPN_FABRIC bfd-liveness-detection minimum-interval 1000 set protocols bgp group EVPN_FABRIC bfd-liveness-detection multiplier 3 set protocols bgp group EVPN_FABRIC neighbor 10.255.1.10 set protocols bgp group EVPN_FABRIC vpn-apply-export set protocols bgp group UNDERLAY type external set protocols bgp group UNDERLAY import UNDERLAY-IMPORT set protocols bgp group UNDERLAY family inet unicast set protocols bgp group UNDERLAY export UNDERLAY-EXPORT set protocols bgp group UNDERLAY local-as 65511 set protocols bgp group UNDERLAY multipath multiple-as set protocols bgp group UNDERLAY bfd-liveness-detection minimum-interval 350 set protocols bgp group UNDERLAY bfd-liveness-detection multiplier 3 set protocols bgp group UNDERLAY neighbor 10.1.1.2 peer-as 65510 set protocols bgp group UNDERLAY neighbor 172.16.1.2 peer-as 65012 set protocols bgp group OVERLAY_INTERDC type external set protocols bgp group OVERLAY_INTERDC multihop no-nexthop-change set protocols bgp group OVERLAY_INTERDC local-address 10.255.1.1 set protocols bgp group OVERLAY_INTERDC family evpn signaling set protocols bgp group OVERLAY_INTERDC multipath multiple-as set protocols bgp group OVERLAY_INTERDC neighbor 10.255.2.1 peer-as 65002 set protocols lldp interface all
叶 2 设备上的配置
set system host-name r2_dc2_leaf1 set interfaces xe-0/0/0 mtu 9000 set interfaces xe-0/0/0 unit 0 family inet address 10.1.2.2/30 set interfaces xe-0/0/1 unit 0 family ethernet-switching vlan members v100 set interfaces xe-0/0/2 unit 0 family ethernet-switching vlan members v60 set interfaces irb unit 60 virtual-gateway-accept-data set interfaces irb unit 60 family inet address 192.168.60.3/24 preferred set interfaces irb unit 60 family inet address 192.168.60.3/24 virtual-gateway-address 192.168.60.1 set interfaces irb unit 100 virtual-gateway-accept-data set interfaces irb unit 100 family inet address 192.168.100.4/24 preferred set interfaces irb unit 100 family inet address 192.168.100.4/24 virtual-gateway-address 192.168.100.1 set interfaces lo0 unit 0 family inet address 10.255.2.10/32 set interfaces lo0 unit 1 family inet address 10.255.20.10/32 set forwarding-options vxlan-routing next-hop 32768 set forwarding-options vxlan-routing overlay-ecmp set policy-options policy-statement ECMP-POLICY then load-balance per-packet set policy-options policy-statement FROM_Lo0 term 10 from interface lo0.0 set policy-options policy-statement FROM_Lo0 term 10 then accept set policy-options policy-statement FROM_Lo0 term 20 then reject set policy-options policy-statement OVERLAY_IMPORT term 5 from community comm_pod1 set policy-options policy-statement OVERLAY_IMPORT term 5 then accept set policy-options policy-statement OVERLAY_IMPORT term 10 from community comm_pod2 set policy-options policy-statement OVERLAY_IMPORT term 10 then accept set policy-options policy-statement OVERLAY_IMPORT term 20 from community shared_100_fm_pod2 set policy-options policy-statement OVERLAY_IMPORT term 20 from community shared_100_fm_pod1 set policy-options policy-statement OVERLAY_IMPORT term 20 then accept set policy-options policy-statement T5_EXPORT term fm_direct from protocol direct set policy-options policy-statement T5_EXPORT term fm_direct then accept set policy-options policy-statement T5_EXPORT term fm_static from protocol static set policy-options policy-statement T5_EXPORT term fm_static then accept set policy-options policy-statement T5_EXPORT term fm_v4_host from protocol evpn set policy-options policy-statement T5_EXPORT term fm_v4_host from route-filter 0.0.0.0/0 prefix-length-range /32-/32 set policy-options policy-statement T5_EXPORT term fm_v4_host then accept set policy-options policy-statement VRF1_T5_RT_EXPORT term t1 then community add target_t5_pod1 set policy-options policy-statement VRF1_T5_RT_EXPORT term t1 then accept set policy-options policy-statement VRF1_T5_RT_IMPORT term t1 from community target_t5_pod1 set policy-options policy-statement VRF1_T5_RT_IMPORT term t1 then accept set policy-options policy-statement VRF1_T5_RT_IMPORT term t2 from community target_t5_pod2 set policy-options policy-statement VRF1_T5_RT_IMPORT term t2 then accept set policy-options community comm_pod1 members target:65001:1 set policy-options community comm_pod2 members target:65002:2 set policy-options community shared_100_fm_pod1 members target:65001:100 set policy-options community shared_100_fm_pod2 members target:65002:100 set policy-options community target_t5_pod1 members target:65001:9999 set policy-options community target_t5_pod2 members target:65002:9999 set routing-instances TENANT_1_VRF routing-options multipath set routing-instances TENANT_1_VRF protocols evpn ip-prefix-routes advertise direct-nexthop set routing-instances TENANT_1_VRF protocols evpn ip-prefix-routes encapsulation vxlan set routing-instances TENANT_1_VRF protocols evpn ip-prefix-routes vni 9999 set routing-instances TENANT_1_VRF protocols evpn ip-prefix-routes export T5_EXPORT set routing-instances TENANT_1_VRF instance-type vrf set routing-instances TENANT_1_VRF interface irb.60 set routing-instances TENANT_1_VRF interface irb.100 set routing-instances TENANT_1_VRF interface lo0.1 set routing-instances TENANT_1_VRF route-distinguisher 10.255.1.2:9999 set routing-instances TENANT_1_VRF vrf-import VRF1_T5_RT_IMPORT set routing-instances TENANT_1_VRF vrf-export VRF1_T5_RT_EXPORT set routing-instances TENANT_1_VRF vrf-table-label set routing-options router-id 10.255.2.10 set routing-options autonomous-system 65002 set routing-options forwarding-table export ECMP-POLICY set routing-options forwarding-table ecmp-fast-reroute set routing-options forwarding-table chained-composite-next-hop ingress evpn set protocols bgp group EVPN_FABRIC type internal set protocols bgp group EVPN_FABRIC local-address 10.255.2.10 set protocols bgp group EVPN_FABRIC family evpn signaling set protocols bgp group EVPN_FABRIC multipath set protocols bgp group EVPN_FABRIC bfd-liveness-detection minimum-interval 1000 set protocols bgp group EVPN_FABRIC bfd-liveness-detection multiplier 3 set protocols bgp group EVPN_FABRIC neighbor 10.255.2.1 set protocols bgp group UNDERLAY type external set protocols bgp group UNDERLAY family inet unicast set protocols bgp group UNDERLAY export FROM_Lo0 set protocols bgp group UNDERLAY local-as 65522 set protocols bgp group UNDERLAY multipath multiple-as set protocols bgp group UNDERLAY bfd-liveness-detection minimum-interval 350 set protocols bgp group UNDERLAY bfd-liveness-detection multiplier 3 set protocols bgp group UNDERLAY neighbor 10.1.2.1 peer-as 65523 set protocols evpn encapsulation vxlan set protocols evpn default-gateway no-gateway-community set protocols evpn vni-options vni 160 vrf-target target:65002:160 set protocols evpn vni-options vni 1100 vrf-target target:65002:100 set protocols evpn extended-vni-list 1100 set protocols evpn extended-vni-list 160 set protocols lldp interface all set switch-options vtep-source-interface lo0.0 set switch-options route-distinguisher 10.255.2.10:1 set switch-options vrf-import OVERLAY_IMPORT set switch-options vrf-target target:65002:1 set vlans v100 vlan-id 100 set vlans v100 l3-interface irb.100 set vlans v100 vxlan vni 1100 set vlans v60 vlan-id 60 set vlans v60 l3-interface irb.60 set vlans v60 vxlan vni 160
主干 2 设备上的配置
set system host-name r3_dc2_spine1 set interfaces xe-0/0/0 mtu 9000 set interfaces xe-0/0/0 unit 0 family inet address 10.1.2.1/30 set interfaces xe-0/0/1 mtu 9000 set interfaces xe-0/0/1 unit 0 family inet address 172.16.2.1/30 set interfaces lo0 unit 0 family inet address 10.255.2.1/32 set policy-options policy-statement ECMP-POLICY then load-balance per-packet set policy-options policy-statement FROM_Lo0 term 10 from interface lo0.0 set policy-options policy-statement FROM_Lo0 term 10 then accept set policy-options policy-statement FROM_Lo0 term 20 then reject set policy-options policy-statement UNDERLAY-EXPORT term LOOPBACK from route-filter 10.255.0.0/16 orlonger set policy-options policy-statement UNDERLAY-EXPORT term LOOPBACK from route-filter 10.1.0.0/16 orlonger set policy-options policy-statement UNDERLAY-EXPORT term LOOPBACK then accept set policy-options policy-statement UNDERLAY-EXPORT term DEFAULT then reject set policy-options policy-statement UNDERLAY-IMPORT term LOOPBACK from route-filter 10.255.0.0/16 orlonger set policy-options policy-statement UNDERLAY-IMPORT term LOOPBACK from route-filter 10.1.0.0/16 orlonger set policy-options policy-statement UNDERLAY-IMPORT term LOOPBACK then accept set policy-options policy-statement UNDERLAY-IMPORT term DEFAULT then reject set routing-options autonomous-system 65002 set routing-options forwarding-table export ECMP-POLICY set routing-options forwarding-table ecmp-fast-reroute set protocols bgp group EVPN_FABRIC type internal set protocols bgp group EVPN_FABRIC local-address 10.255.2.1 set protocols bgp group EVPN_FABRIC family evpn signaling set protocols bgp group EVPN_FABRIC cluster 10.255.2.1 set protocols bgp group EVPN_FABRIC multipath set protocols bgp group EVPN_FABRIC bfd-liveness-detection minimum-interval 1000 set protocols bgp group EVPN_FABRIC bfd-liveness-detection multiplier 3 set protocols bgp group EVPN_FABRIC neighbor 10.255.2.10 set protocols bgp group EVPN_FABRIC vpn-apply-export set protocols bgp group UNDERLAY type external set protocols bgp group UNDERLAY import UNDERLAY-IMPORT set protocols bgp group UNDERLAY family inet unicast set protocols bgp group UNDERLAY export UNDERLAY-EXPORT set protocols bgp group UNDERLAY local-as 65523 set protocols bgp group UNDERLAY multipath multiple-as set protocols bgp group UNDERLAY bfd-liveness-detection minimum-interval 350 set protocols bgp group UNDERLAY bfd-liveness-detection multiplier 3 set protocols bgp group UNDERLAY neighbor 10.1.2.2 peer-as 65522 set protocols bgp group UNDERLAY neighbor 172.16.2.2 peer-as 65012 set protocols bgp group OVERLAY_INTERDC type external set protocols bgp group OVERLAY_INTERDC multihop no-nexthop-change set protocols bgp group OVERLAY_INTERDC local-address 10.255.2.1 set protocols bgp group OVERLAY_INTERDC family evpn signaling set protocols bgp group OVERLAY_INTERDC multipath multiple-as set protocols bgp group OVERLAY_INTERDC neighbor 10.255.1.1 peer-as 65001 set protocols lldp interface all
SRX 系列设备上的基本隧道检测配置
set system host-name r4-dci-ebr set security address-book global address vtep-untrust 10.255.2.0/24 set security address-book global address vtep-trust 10.255.1.0/24 set security address-book global address vlan100 192.168.100.0/24 set security policies from-zone trust to-zone untrust policy P1 match source-address vtep-trust set security policies from-zone trust to-zone untrust policy P1 match destination-address vtep-untrust set security policies from-zone trust to-zone untrust policy P1 match application junos-vxlan set security policies from-zone trust to-zone untrust policy P1 then permit tunnel-inspection TP-1 set security policies from-zone trust to-zone untrust policy accept-rest match source-address any set security policies from-zone trust to-zone untrust policy accept-rest match destination-address any set security policies from-zone trust to-zone untrust policy accept-rest match application any set security policies from-zone trust to-zone untrust policy accept-rest then permit set security policies from-zone untrust to-zone trust policy accept-return match source-address any set security policies from-zone untrust to-zone trust policy accept-return match destination-address any set security policies from-zone untrust to-zone trust policy accept-return match application any set security policies from-zone untrust to-zone trust policy accept-return then permit set security policies policy-set PSET-1 policy PSET-1-P1 match source-address vlan100 set security policies policy-set PSET-1 policy PSET-1-P1 match destination-address vlan100 set security policies policy-set PSET-1 policy PSET-1-P1 match application junos-icmp-all set security policies policy-set PSET-1 policy PSET-1-P1 then permit set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces ge-0/0/0.0 set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols all set security zones security-zone untrust interfaces ge-0/0/1.0 set security tunnel-inspection inspection-profile TP-1 vxlan VNI-1100 policy-set PSET-1 set security tunnel-inspection inspection-profile TP-1 vxlan VNI-1100 vni VLAN-100 set security tunnel-inspection vni VLAN-100 vni-id 1100 set interfaces ge-0/0/0 description "Link to DC2 Spine 1" set interfaces ge-0/0/0 mtu 9000 set interfaces ge-0/0/0 unit 0 family inet address 172.16.1.2/30 set interfaces ge-0/0/1 mtu 9000 set interfaces ge-0/0/1 unit 0 family inet address 172.16.2.2/30 set policy-options policy-statement ECMP-POLICY then load-balance per-packet set policy-options policy-statement dci term 1 from protocol direct set policy-options policy-statement dci term 1 then accept set protocols bgp group UNDERLAY export dci set protocols bgp group UNDERLAY multipath multiple-as set protocols bgp group UNDERLAY bfd-liveness-detection minimum-interval 350 set protocols bgp group UNDERLAY bfd-liveness-detection multiplier 3 set protocols bgp group UNDERLAY neighbor 172.16.1.1 peer-as 65511 set protocols bgp group UNDERLAY neighbor 172.16.2.1 peer-as 65523 set routing-options autonomous-system 65012 set routing-options forwarding-table export ECMP-POLICY
具有第 7 层安全服务的 SRX 系列设备上的隧道检测配置
set system host-name r4-dci-ebrset services application-identification set services ssl initiation profile aamw-ssl set services ssl proxy profile ssl-inspect-profile-1 root-ca VJSA set services advanced-anti-malware policy P3 http inspection-profile scripts set services advanced-anti-malware policy P3 http action block set services advanced-anti-malware policy P3 http client-notify message "AAMW Blocked!" set services advanced-anti-malware policy P3 http notification log set services advanced-anti-malware policy P3 verdict-threshold recommended set services advanced-anti-malware policy P3 fallback-options action permit set services advanced-anti-malware policy P3 fallback-options notification log set services security-intelligence url https://cloudfeeds.argonqa.junipersecurity.net/api/manifest.xml set services security-intelligence authentication tls-profile aamw-ssl set services security-intelligence profile cc_profile category CC set services security-intelligence profile cc_profile rule cc_rule match threat-level 1 set services security-intelligence profile cc_profile rule cc_rule match threat-level 2 set services security-intelligence profile cc_profile rule cc_rule match threat-level 4 set services security-intelligence profile cc_profile rule cc_rule match threat-level 5 set services security-intelligence profile cc_profile rule cc_rule match threat-level 6 set services security-intelligence profile cc_profile rule cc_rule match threat-level 7 set services security-intelligence profile cc_profile rule cc_rule match threat-level 8 set services security-intelligence profile cc_profile rule cc_rule match threat-level 9 set services security-intelligence profile cc_profile rule cc_rule match threat-level 10 set services security-intelligence profile cc_profile rule cc_rule then action block close set services security-intelligence profile cc_profile rule cc_rule then log set services security-intelligence profile ih_profile category Infected-Hosts set services security-intelligence profile ih_profile rule ih_rule match threat-level 7 set services security-intelligence profile ih_profile rule ih_rule match threat-level 8 set services security-intelligence profile ih_profile rule ih_rule match threat-level 9 set services security-intelligence profile ih_profile rule ih_rule match threat-level 10 set services security-intelligence profile ih_profile rule ih_rule then action block close http message "Blocked!" set services security-intelligence profile ih_profile rule ih_rule then log set services security-intelligence policy secintel1 CC cc_profile set services security-intelligence policy secintel1 Infected-Hosts ih_profile set security pki ca-profile aamw-ca ca-identity deviceCA set security pki ca-profile aamw-ca enrollment url http://ca.junipersecurity.net:8080/ejbca/publicweb/apply/scep/SRX/pkiclient.exe set security pki ca-profile aamw-ca revocation-check disable set security pki ca-profile aamw-ca revocation-check crl url http://va.junipersecurity.net/ca/deviceCA.crl set security pki ca-profile aamw-secintel-ca ca-identity JUNIPER set security pki ca-profile aamw-secintel-ca revocation-check crl url http://va.junipersecurity.net/ca/current.crl set security pki ca-profile aamw-cloud-ca ca-identity JUNIPER_CLOUD set security pki ca-profile aamw-cloud-ca revocation-check crl url http://va.junipersecurity.net/ca/cloudCA.crl set security idp idp-policy idp123 rulebase-ips rule rule1 match application junos-icmp-all set security idp idp-policy idp123 rulebase-ips rule rule1 then action no-action set security address-book global address vtep-untrust 10.255.2.0/24 set security address-book global address vtep-trust 10.255.1.0/24 set security address-book global address vlan100 192.168.100.0/24 set security utm default-configuration anti-virus type sophos-engine set security utm utm-policy P1 anti-virus http-profile junos-sophos-av-defaults set security policies from-zone trust to-zone untrust policy P1 match source-address vtep-trust set security policies from-zone trust to-zone untrust policy P1 match destination-address vtep-untrust set security policies from-zone trust to-zone untrust policy P1 match application junos-vxlan set security policies from-zone trust to-zone untrust policy P1 then permit tunnel-inspection TP-1 set security policies from-zone trust to-zone untrust policy accept-rest match source-address any set security policies from-zone trust to-zone untrust policy accept-rest match destination-address any set security policies from-zone trust to-zone untrust policy accept-rest match application any set security policies from-zone trust to-zone untrust policy accept-rest then permit set security policies from-zone untrust to-zone trust policy accept-return match source-address any set security policies from-zone untrust to-zone trust policy accept-return match destination-address any set security policies from-zone untrust to-zone trust policy accept-return match application any set security policies from-zone untrust to-zone trust policy accept-return then permit set security policies policy-set PSET-1 policy PSET-1-P1 match source-address vlan100 set security policies policy-set PSET-1 policy PSET-1-P1 match destination-address vlan100 set security policies policy-set PSET-1 policy PSET-1-P1 match application any set security policies policy-set PSET-1 policy PSET-1-P1 match dynamic-application any set security policies policy-set PSET-1 policy PSET-1-P1 match url-category any set security policies policy-set PSET-1 policy PSET-1-P1 match from-zone trust set security policies policy-set PSET-1 policy PSET-1-P1 match to-zone untrust set security policies policy-set PSET-1 policy PSET-1-P1 then permit application-services idp-policy idp123 set security policies policy-set PSET-1 policy PSET-1-P1 then permit application-services ssl-proxy profile-name ssl-inspect-profile-1 set security policies policy-set PSET-1 policy PSET-1-P1 then permit application-services utm-policy P1 set security policies policy-set PSET-1 policy PSET-1-P1 then permit application-services security-intelligence-policy secintel1 set security policies policy-set PSET-1 policy PSET-1-P1 then permit application-services advanced-anti-malware-policy P3 set security zones security-zone trust host-inbound-traffic system-services all set security zones security-zone trust host-inbound-traffic protocols all set security zones security-zone trust interfaces ge-0/0/0.0 set security zones security-zone untrust host-inbound-traffic system-services all set security zones security-zone untrust host-inbound-traffic protocols all set security zones security-zone untrust interfaces ge-0/0/1.0 set security tunnel-inspection inspection-profile TP-1 vxlan VNI-1100 policy-set PSET-1 set security tunnel-inspection inspection-profile TP-1 vxlan VNI-1100 vni VLAN-100 set security tunnel-inspection vni VLAN-100 vni-id 1100 set interfaces ge-0/0/0 description "Link to DC2 Spine 1" set interfaces ge-0/0/0 mtu 9000 set interfaces ge-0/0/0 unit 0 family inet address 172.16.1.2/30 set interfaces ge-0/0/1 mtu 9000 set interfaces ge-0/0/1 unit 0 family inet address 172.16.2.2/30 set policy-options policy-statement ECMP-POLICY then load-balance per-packet set policy-options policy-statement dci term 1 from protocol direct set policy-options policy-statement dci term 1 then accept set protocols bgp group UNDERLAY export dci set protocols bgp group UNDERLAY multipath multiple-as set protocols bgp group UNDERLAY bfd-liveness-detection minimum-interval 350 set protocols bgp group UNDERLAY bfd-liveness-detection multiplier 3 set protocols bgp group UNDERLAY neighbor 172.16.1.1 peer-as 65511 set protocols bgp group UNDERLAY neighbor 172.16.2.1 peer-as 65523 set routing-options autonomous-system 65012 set routing-options static route 0.0.0.0/0 next-hop 10.9.159.252 set routing-options forwarding-table export ECMP-POLICY
