Configure o multihoming EVPN de malha de campus
Siga essas etapas para mesclar as camadas de núcleo e distribuição em um único switch, configurando o multihoming EVPN.
A solução multihoming EVPN de malha de campus da Juniper Networks oferece suporte a uma arquitetura de núcleo colapsada. Essa arquitetura mescla as camadas de núcleo e distribuição em um único switch. A fusão dessas camadas em um único switch transforma a rede hierárquica tradicional de três níveis em uma rede de duas camadas. Essa arquitetura também elimina a necessidade de STP em todas as redes de campus, fornecendo recursos multihoming da camada de acesso até a camada de núcleo.
-
O tipo de topologia EVPN Multihoming está disponível apenas para a malha de campus específica do site. Você não pode construí-la no nível da organização.
-
Em topologias que são incorporadas na Mist Cloud após as atualizações de maio de 2025, a Mist detecta e relata automaticamente quaisquer loops EVPN e endereços MAC duplicados. Esses problemas são exibidos na página insights do switch.
-
Detecção de loop EVPN — A detecção leve de loop PE-CE EVPN-VXLAN ajuda na detecção e quebra de loops LAN Ethernet em portas downstream leaf-to-server ou de acesso. Esse recurso pode detectar loops causados por problemas como componentes de malha mal conectados ou switches de terceiros conectados incorretamente à malha. Para que esse recurso funcione, o switch deve executar o Junos OS versão 24.4R1 ou posterior. Para obter mais informações, consulte o EVPN-VXLAN Lightweight Leaf para a detecção de loop de servidor.
-
Detecção de endereço MAC duplicada — identifica e mitiga problemas decorrentes da movimentação de endereço MAC (mobilidade MAC) entre diferentes interfaces ou dispositivos em ambientes EVPN. Embora alguma mobilidade MAC seja esperada (por exemplo, quando um dispositivo realmente se move), mudanças rápidas podem indicar problemas como loops de rede ou configurações incorretas. Para obter mais informações, consulte Configurando a detecção de loops para endereços MAC duplicados.
-
Para obter um exemplo de configuração detalhado, veja o fluxo de trabalho multihoming EVPN de malha de campus.
Melhores práticas de configuração de malha de campus
- Configure as VLANs no nível do modelo do switch e importe-as enquanto configura a malha do campus. O modelo deve ser a fonte única de verdade para todas as VLANs e perfis de porta, a menos que seja exigido especificamente no nível do switch ou do site.
- Na camada de acesso, evite usar perfis de porta de tronco que permitam todas as VLANs, a menos que seja explicitamente necessário.
- Crie configurações de rede VRF e VRF através da malha do campus, não através de modelos de switch.
- Crie atribuições de porta por função e sobreescreva a configuração em dispositivos individuais conforme necessário.
- Gerencie a configuração de retransmissão DE DHCP por meio do fluxo de trabalho da malha de campus, com exceção dos dispositivos de blocos de serviço.
Para configurar o multihoming EVPN de malha de campus:
- No menu de navegação à esquerda, selecione Organização > Malha de Campus.
- Na lista de quedas do site ao lado do título da página, selecione o site onde você deseja construir a malha do campus.
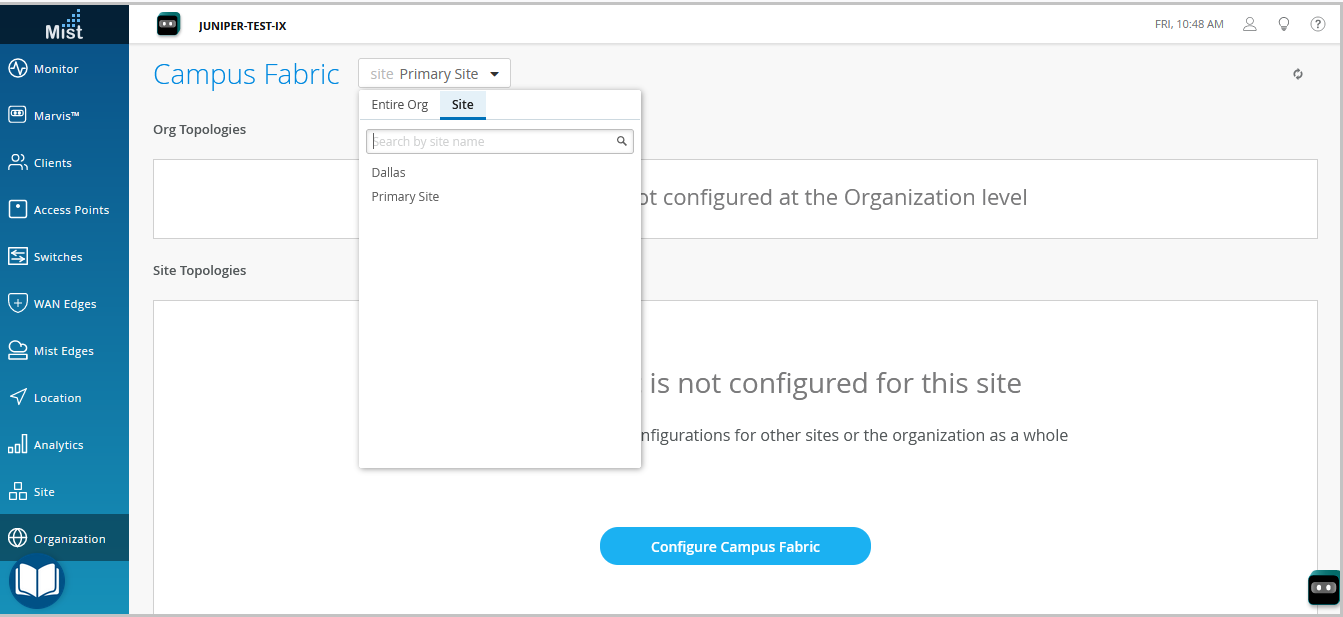
- Clique em qualquer opção que for relevante. Clique:
-
configurar o botão malha de campus (exibido se o site não tiver uma configuração de malha de campus associada a ele).
-
o botão Criar malha de campus (exibido se o site já tiver pelo menos uma configuração de malha de campus associada a ele).
A guia topologia é exibida. -
- Selecione o tipo de topologia EVPN Multihoming.
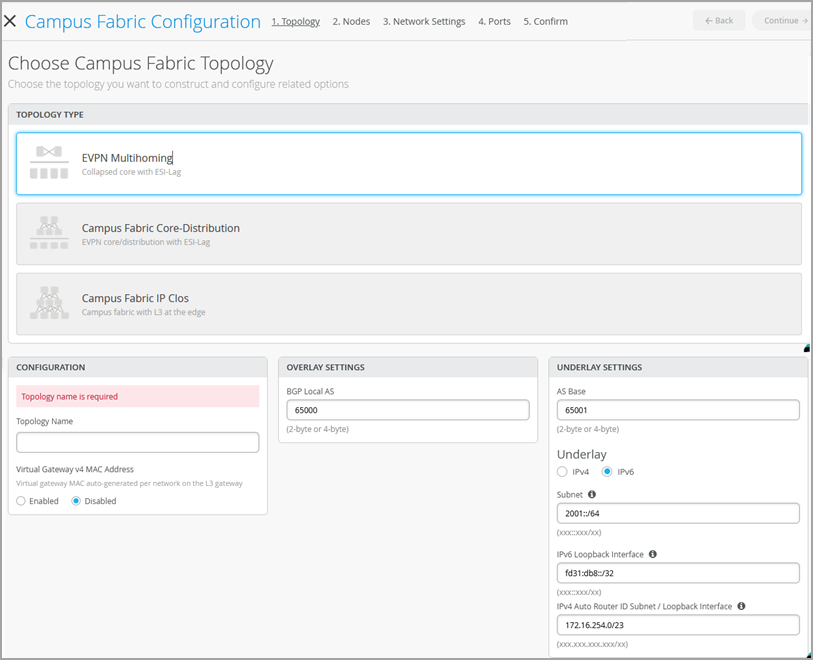
- Configure as configurações restantes na guia Topologia, conforme descrito abaixo:
Nota:
Recomendamos que você use as configurações padrão nesta tela a menos que entrem em conflito com quaisquer redes ligadas à malha do campus. Os links ponto a ponto entre cada camada utilizam endereçamento de /31 para conservar endereços.
- Na seção CONFIGURAÇÃO, configure o seguinte:
-
Nome da topologia — insira um nome para topologia.
-
Endereço MAC do gateway virtual v4 — habilite essa opção de oferecer suporte a redirecionamentos do Portal de Convidados na WLAN. , a Mist fornecerá um endereço MAC exclusivo para cada gateway virtual de Camada 3 (L3) (por rede). Desativado por padrão.
-
- (Se optar por não usar as configurações padrão) Na seção CONFIGURAÇÕES DE OVERLAY, digite o seguinte:
-
BGP Local AS — Representa o ponto de partida dos números BGP AS privados que a Mist aloca para cada dispositivo automaticamente. Você pode usar qualquer faixa de número BGP AS privada que se adapte à sua implantação. A Mist provisiona a política de roteamento para que apenas os endereços IP de loopback sejam trocados na subcamada da malha.
-
- (Se optar por não usar as configurações padrão) Na seção CONFIGURAÇÕES UNDERLAY, configure o seguinte:
-
AS Base — O número base de AS. O padrão é 65001.
-
Underlay — Selecione uma versão de protocolo de internet para a underlay. As opções são IPv4 e IPv6.
-
Sub-rede — A gama de endereços IP que a Mist usa para links ponto a ponto entre dispositivos. Você pode usar um intervalo que se adapte à sua implantação. A Mist quebra essa sub-rede em endereçamento de sub-rede /31 por link. Você pode modificar esse número para se adequar à escala de implantação específica. Por exemplo, uma rede /24 forneceria até 128 sub-redes ponto a ponto/31.
-
Interface de loopback IPv6 — Especifique uma sub-rede de interface de loopback IPv6, usada para automatizar a interface de loopback IPv6 em cada dispositivo na malha.
-
Interface de sub-rede/loopback do roteador automático — a Mist usa essa sub-rede para atribuir automaticamente um ID do roteador a cada dispositivo na malha (incluindo dispositivos de acesso, independentemente de estarem configurados com EVPN ou não). Os IDs do roteador são interfaces de loopback (lo0.0) usadas para peering overlay entre dispositivos. Para novas topologias, este campo preenche automaticamente um valor padrão de sub-rede (172.16.254.0/23), que você pode modificar. Quando você edita uma topologia existente, este campo não preenche nenhum valor padrão. A ID do roteador é usada como um identificador ao implantar protocolos de roteamento, como o BGP. Depois de adicionar o switch à camada de núcleo colapsada, clique no ícone do switch para ver a ID do roteador associado.
Você pode substituir o ID do roteador atribuído automaticamente configurando manualmente uma interface de loopback no campo de ID do roteador no azulejo de roteamento na página de configuração do switch (Switches > Nome do switch). No entanto, se você modificar a configuração da malha de campus depois, a Mist realizará a atribuição automática do ID do roteador novamente, substituindo a interface de loopback configurada manualmente.
-
- Na seção CONFIGURAÇÃO, configure o seguinte:
- Clique em Continuar a acessar a guia Nós, onde você pode selecionar dispositivos que fazem parte da implantação da malha do campus.
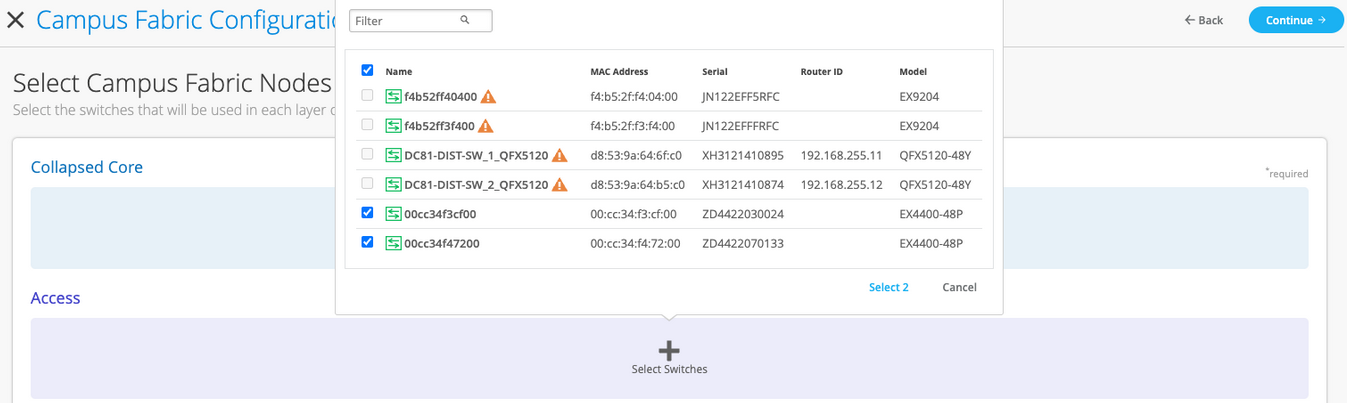
- Adicione switches à camada de núcleo colapsada e à camada de acesso.
Recomendamos que você valide a presença de cada dispositivo no inventário do switch antes de criar a malha do campus.
Para adicionar switches:
- Clique em Selecionar switches.
- Escolha os switches que você deseja adicionar à malha do campus.
- Clique em Selecionar.
- Depois de selecionar os switches, clique em Continuar a acessar a guia Configurações de rede, onde você pode configurar as redes.
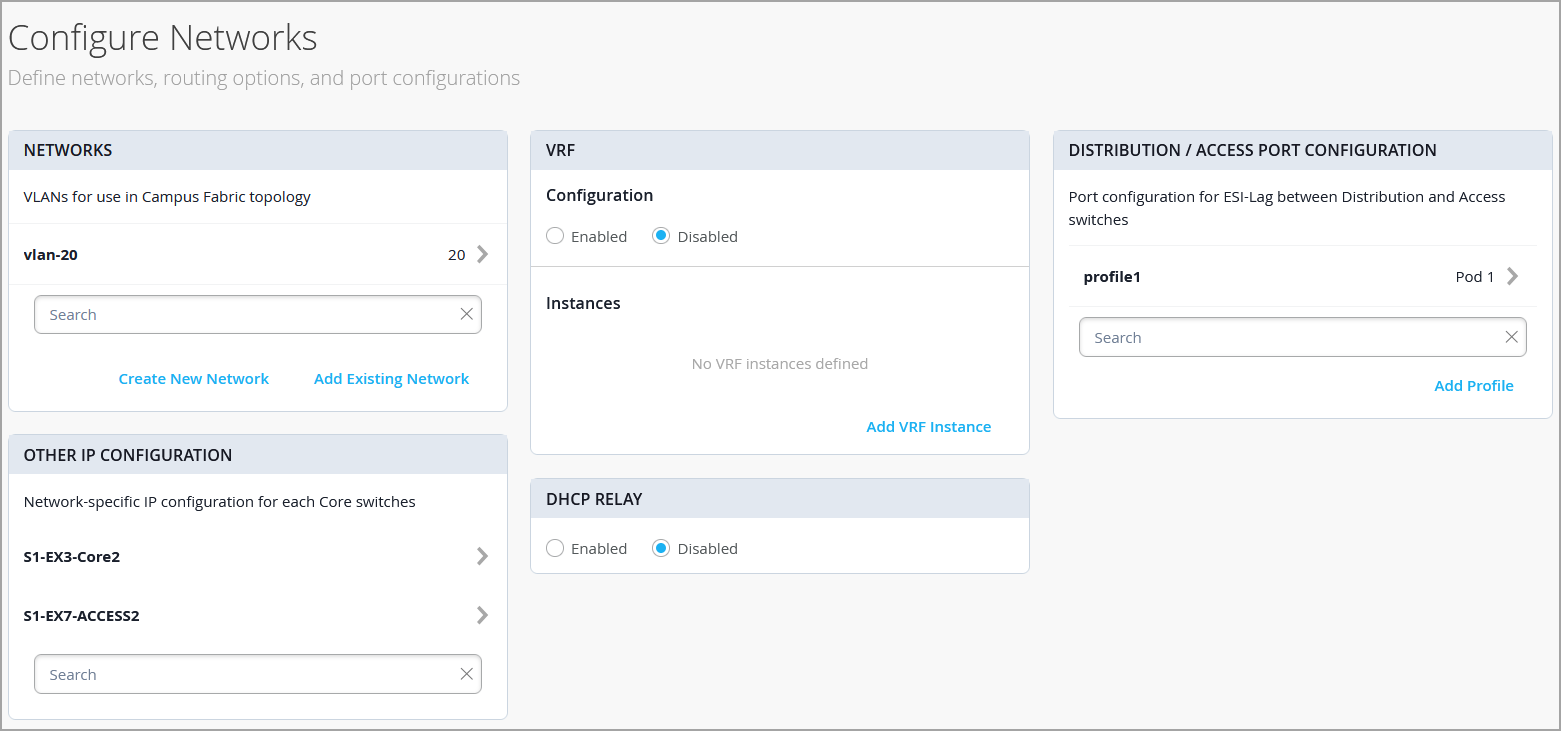
- Configure as configurações da rede, conforme descrito abaixo:
- No azulejo NETWORKS, adicione redes ou VLANs à configuração. Você pode criar uma nova rede ou importar a rede a partir do modelo de switch definido na página de modelos da Organização > switches.
Para adicionar uma nova VLAN, clique em Criar uma nova rede e configurar as VLANs. As configurações incluem um nome, ID VLAN e uma sub-rede. Você pode especificar endereços IPv4 ou IPv6 para a sub-rede.
Para importar VLANs do modelo:
-
Clique em Adicionar a rede existente.
-
Selecione um modelo de switch da lista de quedas do modelo para ver as VLANs disponíveis nesse modelo.
-
Selecione a VLAN necessária na lista exibida e clique na marca ✓.
As VLANs são mapeadas para identificadores de rede virtual (VNIs). Você pode mapear VLANs opcionalmente para instâncias de roteamento e encaminhamento virtual (VRF) para separar logicamente o tráfego.
-
- Analise as configurações na outra configuração de IP. Esta seção preenche as configurações automaticamente após você especificar as redes na seção NETWORKS.
- Opcionalmente, configure instâncias VRF. Recomendamos o uso de VRFs ao aplicar políticas de Tipo 5 (prefixo IP) em uma arquitetura de malha de campus baseada em segmentos. Por padrão, a Mist coloca todas as VLANs no VRF padrão. A opção VRF permite agrupar VLANs comuns na mesma VRF ou VRFs separadas, dependendo dos requisitos de isolamento de tráfego. Todas as VLANs dentro de cada VRF têm conectividade completa entre si e com outros recursos externos de rede. Um caso de uso comum é o isolamento do tráfego sem fio convidado da maioria dos domínios empresariais, exceto a conectividade à Internet. Por padrão, a malha de campus oferece isolamento completo entre VRFs, forçando as comunicações inter-VRF a atravessar um firewall. Se você precisar de comunicação entre VRF, você precisa incluir rotas extras para o VRF. A rota extra pode ser uma rota padrão que instrui a malha do campus a usar um roteador externo. Também pode ser um firewall para mais recursos de inspeção ou roteamento de segurança.
Para criar um VRF:
-
No azulejo VRF, clique em Adicionar instância VRF e especifique as configurações. As configurações incluem um nome para VRF e as redes a serem associadas ao VRF.
-
Para adicionar rotas extras, clique no link Adicionar rotas extras na página de nova instância VRF e especifique a rota. Você pode especificar endereços IPv4 ou IPv6.
-
- No azulejo DE CONFIGURAÇÃO DE PORTA DE ACESSO/NÚCLEO, preencha a configuração de porta para ESI-LAG entre o núcleo colapsado e os switches de acesso. As configurações incluem um nome e outros elementos de configuração de porta. Por padrão, essa configuração inclui as redes adicionadas no azulejo NETWORKS na mesma página. Se você quiser remover ou modificar as configurações, clique em Mostrar Avançado e configurar as configurações. Use as dicas na tela para configurar as configurações do perfil da porta.
- No azulejo de retransmissão DHCP, configure as configurações de retransmissão DHCP. Você tem as seguintes opções:
-
Habilitado — configura o retransmissão DHCP em todos os dispositivos habilitados para IRB na malha do campus. Essa opção permite que você habilite o DhCP Relay em redes que você selecionou. A rede será povoada dentro do azulejo de retransmissão DHCP, desde que esteja listada na guia Networks na mesma página.
-
Desativado — Desabilite o retransmissão de DHCP nos dispositivos da malha do campus. Ao selecionar essa opção, o retransmissão DHCP é desativado em todos os dispositivos habilitados para IRB. Você deve selecionar cuidadosamente essa opção, pois isso removerá o dhcp relay definido localmente na página detalhada do switch.
-
Nenhuma — essa opção é selecionada automaticamente quando a topologia da malha de campus tem uma mistura de dispositivos em termos da configuração de transmissão DHCP; ou seja, alguns dispositivos têm o retransmissão DHCP habilitado, alguns o desabilitam e outros não o têm definido. Essa opção será visível para todas as topologias de malha de campus que tenham o DHCP Relay definido localmente em switches individuais.
Se você quiser remover todas as redes de retransmissão DHCP definidas localmente, selecione Habilitado e escolha Remover todas as redes DHCP de nível de dispositivo existentes. Você pode simplificar a implantação do seu DHCP Relay centralizando qualquer mudança de configuração do fluxo de trabalho da malha do campus.
Se você habilitar o retransmissão DHCP em uma configuração de malha de campus, ele será habilitado em todos os dispositivos definidos por IRB na malha e desativado no resto dos dispositivos. Por exemplo, em topologias EVPN Multihoming, o retransmissão DHCP é habilitado em dispositivos de núcleo colapsados e desativado no restante.
-
- No azulejo NETWORKS, adicione redes ou VLANs à configuração. Você pode criar uma nova rede ou importar a rede a partir do modelo de switch definido na página de modelos da Organização > switches.
- Clique em Continuar a acessar a guia Portas, onde você pode configurar as portas e criar uma conexão entre o núcleo, a distribuição e os switches de camada de acesso.
- Configure as portas do switch na camada de núcleo colapsada da seguinte forma:
- Selecione um switch na seção Núcleo colapsado para abrir o painel da porta do switch.
- No painel de portas do switch, selecione uma porta que você deseja configurar.
- Especifique um tipo de porta (por exemplo,
geouxe). - Selecionar:
-
Link para o núcleo colapsado para conectar a porta a um switch de núcleo.
Na camada de núcleo colapsada, você pode conectar cada switch a todos os outros switches para formar uma topologia de malha completa. Uma topologia de malha completa oferece uma malha de campus multihoming EVPN com maior resiliência, o que garante uma funcionalidade de rede contínua mesmo se um dispositivo falhar.
-
Link para acesso para conectar a porta a um switch de acesso.
-
- Selecione o núcleo ou o switch de acesso (com base na seleção na etapa anterior) em que o link deve terminar. Você precisa configurar todas as portas que precisam fazer parte da malha do campus.
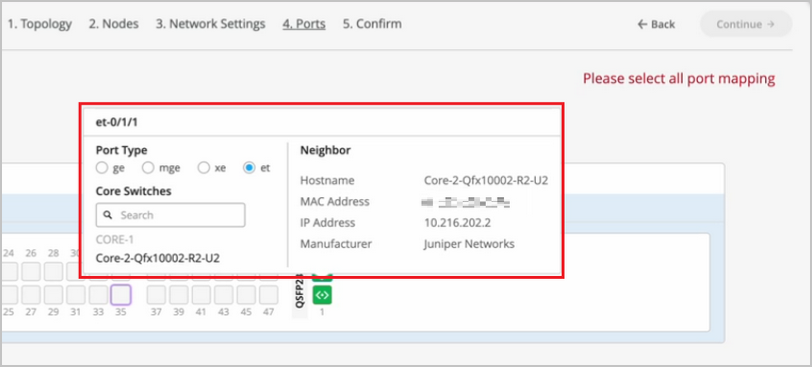
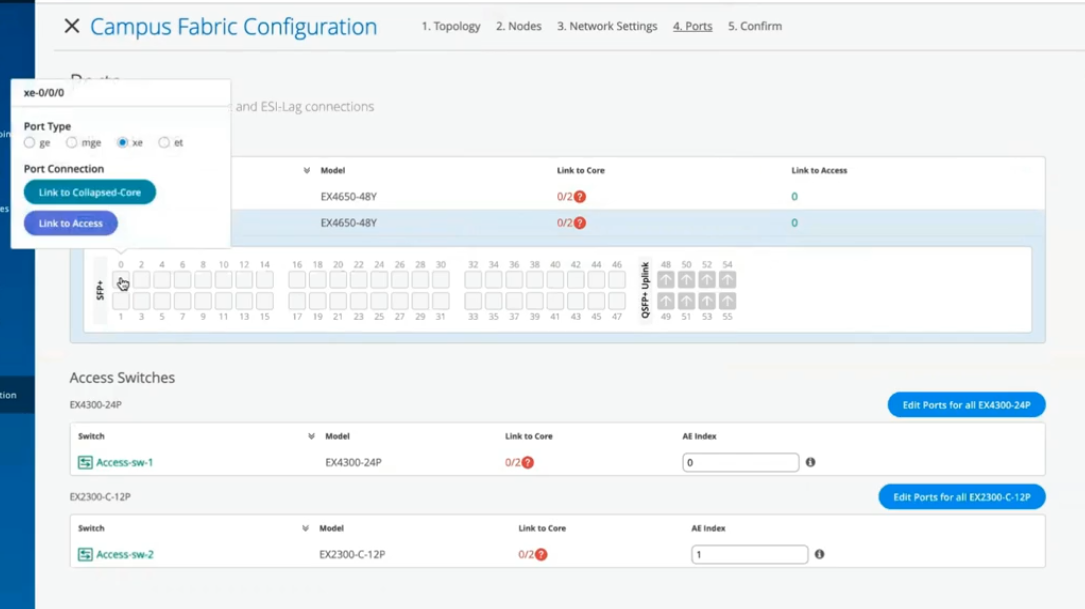 Para configurar as portas do switch na camada de acesso:
Para configurar as portas do switch na camada de acesso:- Selecione um switch na seção de acesso para abrir o painel de porta do switch.
- No painel de portas do switch, selecione uma porta que você deseja configurar.
- Especifique um tipo de porta (por exemplo,
geouxe).Caso a camada de acesso use um Virtual Chassis (VC), você pode configurar portas nas guias primárias e de backup.
Para os switches de acesso, selecione apenas as interfaces que devem ser usadas para interconectar com o switch de distribuição. O sistema agrupa todas as interfaces em um único pacote Ethernet através da opção de índice AE. Você pode especificar um valor de índice de AE para os dispositivos de acesso.
Se você quiser visualizar as informações de configuração e status de uma porta específica, passe o mouse sobre a caixa numerada que representa essa porta na UI do painel de portas.
- Clique em Continuar a acessar a guia Confirmação.
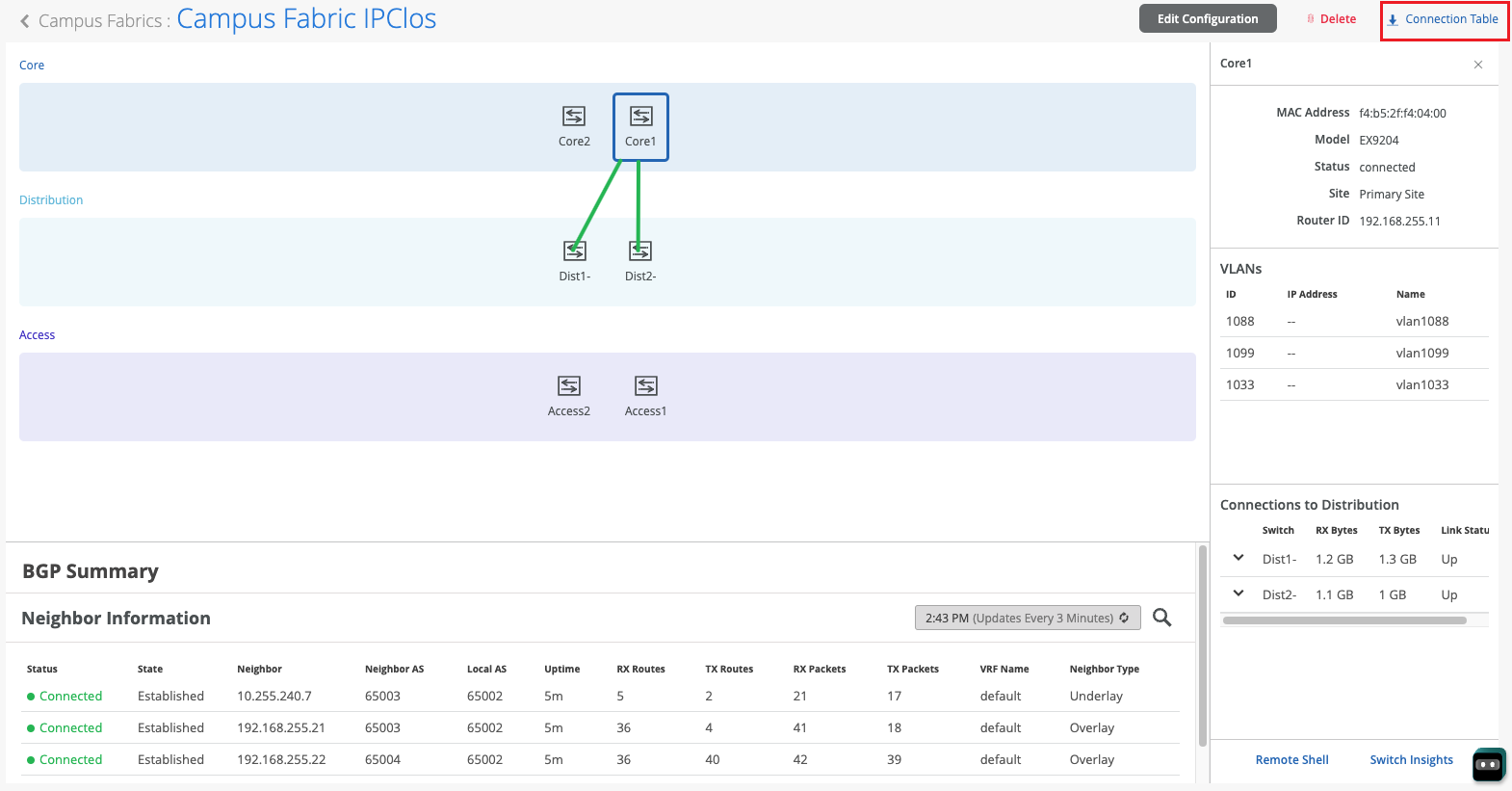
- Clique em cada ícone do switch para visualizar e verificar a configuração.
- Após verificar a configuração, clique em Aplicar alterações > Confirmar.
Essa etapa salva a configuração da malha do campus para a nuvem da Mist e a aplica aos switches. Se os switches estiverem offline, a configuração será aplicada a eles quando estiverem on-line da próxima vez. Um switch pode levar até 10 minutos para concluir a configuração.
- Clique em Fechar a configuração da malha do campus.
Depois que a Mist construir a malha do campus ou enquanto estiver construindo a malha, você pode baixar a tabela de conexão. A tabela de conexão representa o layout físico da malha do campus. Você pode usar esta tabela para validar todas as interconexões de switches para os dispositivos que participam da construção física da malha de campus. Clique na Tabela de conexão para baixá-la (formato .csv).
- Verifique a configuração da malha do campus. Para verificar, siga as etapas listadas na seção de verificação no fluxo de trabalho multihoming EVPN de malha de campus.
Hello and welcome to this edition of Wired Assurance. My name is Rohan Chada and today I'll be talking about building an EVPN week stand campus fabric in just four steps. Today we're going to talk about the deployment of EVPN multi homing topology. I'll walk you through the different steps that are required and I can promise you none of those require any CLI configuration.
Everything will be done through the UI and it'll be as simple as you can expect it to be. So let's just jump right into it and talk about EV Pin Multi Hamming. Before we jump into building the EV Pin Multi Hamming topology, let's understand the building blocks of it from a device perspective. Today as you can see, we're going to be using 2 core devices and two access devices.
The EVPN Multi Hamming topology can support up to 4 core devices, a minimum of two and a maximum of four and as many access devices as you'd like. But for this purposes of this video, we'll be using 2 core devices and two access devices. So to begin with, we click on organization and we under the wire tab we see Campus fabric. So as we click on Campus fabric, we can see that we are inside the site EVPN campus primary one and there is no campus fabric configured at this time.
And that's exactly where we'll begin. Click on configure campus fabric and we see that there are three topologies that are presented to us. EVPN multi homing which is collapse code with ESI lag, campus fabric Code distribution which is EVPN code distribution with ESI lag and canvas fabric IP cloth. What you see on the left side of each of these three names is a small diagram that basically depicts the topology that this this entails.
So you basically have above the line that you see the horizontal line in the diagram on each of these topologies. Above the line is where your your evpn vxlan construct exists. And what I mean by that is that's where those devices are, the devices that run Evpn vxlan configuration. Anything below the horizontal line are just pure access devices layer to they can be, they have to be non evpn VXLAN capable devices.
So once you've selected the EVPN multi homing we see that it's a collapsed core and what that means is that two or three layers of EVPN configuration is collapsed into just one layer. So we'll jump right in there by giving it a topology name. We're going to go ahead and call it evpn image. There are two settings that you have to provide on the initial page and that's for the overlay and the underlay settings.
For overlay we use ibgp today and for underlay we use ebgp. The default values will be presented to you, there is no reason to change it if there isn't a purpose behind it. And 65,000 is the local AS and 65,001 is the AS base to begin with for the underlay ebgp. And then we'll increment sequentially on a device spaces starting with 65001.
The loopback prefix as you can see is the the prefix that's used to assign to all the interfaces, all the loopback interfaces on all the devices. These interfaces are used to peer with every other VTAP in the campus fabric. And then last is the subnet, which is again a default value provided that can be changed by the user. This subnet is used to connect the underlying physical interfaces between the campus fabric.
Let's jump right into the next step and click on Continue. At this step we'll be selecting the Campus fabric nodes. In this Campus fabric configuration we'll be selecting 2 Campus course and I'll select Code one and Code 3 for this demo. And as you can see in this nice drop down, you have all the information provided to you and that includes the model as well as the Mac address so you don't have to go back and forth between different pages of the UI.
Every information is provided right here. For the access devices, I'll be picking switch one and switch two. My core devices are EX 465048 wise that are EVPN capable. My access devices are EX 2300 and 4300 that do not understand EVPN.
Hence I am putting these in an access layer. The platform support on a topology basis is on the on the website and we've listed every platform that's supported on a per layer basis. So once you've selected this topology, we know that there are two core devices, 2 access devices. I can click on these core devices and I can see that the basic information about core one I see there is a router ID assigned.
This router ID is assigned as needed for the loop back interface. As I mentioned earlier, that's used for peering between the two core devices. In case of a collapsed core, the two core devices will act as the as the two vtips that basically they will be forming A VXLAN tunnel between each other. The access, which is on the other hand do not necessarily need a router ID, but we've provided them for consistency's sake.
They do not need it, but let's go ahead with that. Step three is basically configuring networks. So networks are basically of Vlans. So we'll go ahead and start creating some new networks here.
I'm going to be assigning some generic names here and I'll call it image vlan 10 and S and vlan ID 10 and I'll give it the subnet 190 to one 6810.0 slash 24 and I'll give it a virtual gateway for 190 to 168 dot 10.1. Now providing this subnet is. This is the only I would say.
This is the second step wherein you'll be providing us a subnet. The IP addressing for the IRB slash SVI interfaces or any IP addressing in the underlying physical interfaces in our fabric is taken care by missed Wire Assurance Campus Fabric. As a user and administrator, you don't have to worry about it. So once you've provided us a subnet, we'll take care of it.
So this virtual gateway will essentially be used for as a common address between the two core devices. So any underlying device, for example an access switch or any any device connected to the access switch will have its gateway as 190 to 168 or 10.1 which will be advertised via avpn and that's why we come in here and manually define it. So as you can see, I created a VLAN, VLAN 10 and voila, we see two IP addresses that have already been chosen to be assigned for the corresponding IRB slash SVI interfaces that will be assigned to code one and code 3 for VLAN 10.
Let's go ahead and create another one and we'll call it image VLAN 20. But in this case I'm not going to assign a subnet or virtual git net because I want to route for this particular VLAN. I want to route on the the the firewall of the campus fabric. So my the two core devices that I have will be connected dual home to a firewall and I want the routing to happen for this particular VLAN on the firewall.
So I'm going to skip this and this is basically a bridged overlay design wherein we'll assign the VNI to the corresponding VLAN 20, but we will not be configuring A subnet or a gateway on the 2 core devices. This is one way of creating a VLAN. The other way of adding a VLAN to the campus fabric is if you have existing network on the sites already. So we'll click on existing network and what we see is that there is a common VLAN that we already created earlier before we started this demo on an entire site.
So using the site configuration here, I created a VLAN called site wide VLAN with a VLAN ID of 100 and that's it. And what that did was all the devices in that site inherited the site wide VLAN. So I'm going to take site wide VLAN and I'm going to add that. So now I'm told that there is a virtual gateway that is required.
OK, there is a virtual gateway required. So we'll go ahead and add the virtual gateway. The subnet basically was inherited from the the site configuration where I had created VLAN printer. So I'm being told that the provided gateway is already used.
OK, so here we have 3 Vlans and as we already see that for two of them the static IP addresses have already been defined. For VLAN 10 there are two IP addresses, code one and code 3. Similarly for site VLAN 100, we have two IP addresses, one each for core one and core 3. And as we already know VLAN 20 is a doesn't have a virtual gateway on the collapse core, so we do not have a gateway for that.
Now let's jump into VRF and understand this is virtual routing and forwarding wherein you can create separate routing instances. You can basically increase the security in your network by segregating the Vlans in different routing instances. A different routing instance basically means that there is a different routing table on a per VLAN basis or however many Vlans you would like in that particular VRF. So we'll go and assign this name vrf one and then we'll we'll add image vlan 10 to vrf one if if there is a need.
I can always add extra routes within the VRF as well and that is an option. You go ahead and another VRF called VRF 2 and I'll use site by vlan for this particular VRF 2. The last step on this page is to basically configure the core access port configuration. This is the port configuration towards the access switches from the collapse code as it if you read the description it says this is the ESL configuration.
So let's just assign it a name and let's call it Yesi LAG, any name of the book, but Yesi Haffen LAG is what I've assigned. We presume that all the Vlans and networks that you've defined here are going to be a part of the ESI LAG configuration, and so we automatically add them to the trunk networks. You can come in here and manually change any settings that you would like. If you would like a smaller MTU or if you would like to manipulate the MTU size here to your environment needs, you can do that.
You can enable storm control. You can also enable Poe if that's a requirement, change the speed, duplex, add native VLAN. All of that is an option that we've provided. This is the last and final step and what we see here is there are different port panels.
These port panels are on a platform basis. For the purposes of this video, we are using EX4650 and two other platforms. So we'll show you the appropriate port panels as needed whenever any platform other than these are used. So let's jump right into it and let's let I'll go ahead and I'll configure these interfaces quickly.
So what I've done at this point is I've connected all the two collapsed core devices with the other two access devices. Basically the requirement is that there should be two interfaces connected to each other between the two core devices. Evpn multi Homing has that requirement for redundancy and then core one needs to connect to both access switch one and Access switch 2. Similarly code 3 needs to connect to both access switch one and access Switch 2.
So once those interfaces have been have been connected here you've told the missed UI that these are the interfaces. We can proceed and we can click on continue. This is the last step wherein you confirm that the topology changes that you want are there and if you click on code 1, we can see that on the right. We see a lot of information about everything that we've done so far.
We see the model, we see the router ID, we see the Vlans that we wanted in the campus fabric. Along with the Vlans we also see the IP addresses. I see that there are two IP addresses and three Vlans. One of them is and doesn't have an IP address and that is basically a bridge overlay design as I mentioned earlier.
We also see the connections by the way. I can see and I can verify here the connections connections to collapsed core or three and access switch one and access switch two at any point in this entire step. If you'd like to access the remote shell, we've provided you that option as well. So before you hit apply changes, if you'd like to log into your device you can do that here.
You can click on remote shell and pop up window will open for you and at this point you can you can look at your configuration. You can look at how your devices are connected. I see here that my devices are connected or one connects to two core 3 interfaces and core one has a connection to switch to and switch one as well. So a a little handy tool here where you can verify by logging into the device.
Let's click apply changes and confirm. At this time, what has happened is that the configuration that we decided to push to the devices is being pushed and is being committed to the junuper devices and right after that's committed, BGP Underlay as well as Overlay will be provisioned. Once BGP Underlay is provisioned, overlay and the VX LAN tunnels will come up, the VX LAN tunnel will be two way between collapsed Core one and collapsed Core 2. Let's just jump right into the switches while this configuration is happening.
We look at what's the scenario and the switches and the configuration that we pushed under the hood. Remember, everything that we did so far was based on UI. We did not touch the CLI. We did not make any CLI changes manually.
You did not have to define the EVPN configuration or the BGP configuration or the underlying physical connectivity. This is the value of Missed Wire Assurance Campus Fabric. Let's click on Utilities and click on Download JS Config. We see that configuration file has been downloaded.
This is a. This is a handy tool. What this does is it enables us to verify the configuration. All of us have been used to configuring things while the CLI and so it is very important that we verify that if you're doing this for the first time that everything that you want in the configuration should be there.
You could be a Greenfield environment or or a brownfield environment. You should be able to verify your configuration. So let's dive right into it. Let's look at this.
So as we can see, the first thing I see is I see some BGP configuration here. That's very important. We see the underlay BGP configuration here between the two core devices. There are two peers here on 2 interfaces.
We see the overlay configuration here since there's only one peer for core one and that is core three. There is only one neighbor. We see some EVPN configuration here, right? We also see the ESI LAG configuration here that was pushed by Campus Fabric.
None of that required us to push anything through CLI. We see 22 LAG interfaces AE0 and AE1AE0. It's towards switch one and AE three is towards switch two. We see the IRB configuration as we discussed earlier.
IRB 10 is the the first VLAN that we defined with a gateway and IRB 100 is the third one that was inherited from the site wide template. We also see the VRF configuration here. So as we can see, there's VRF one configuration that has one VLAN IRB .10. We also have type 5 routes as a part of it.
We also see VRF 2 configuration in this VRF 2 configuration, what we see is IRP 100. The second, I'm sorry, the third VLAN that we chose is also there. And then if you look at the configuration here, we see all three Vlans, even the VLAN, even the VLAN that we made bridged overlay is a part of the configuration has a VNI. So we can go ahead and we can assign the gateway for this particular VLAN on either the router of the campus fabric or the firewall based on your environment.
So now that we've looked at the configuration, let's look at how our EVPN campus fabric is doing and what do the EVPN insights tell us. So the EVPN insights, it's basically a pretty layer on top of the campus fabric that tells you about a few green and red links. And those green and red links are not not just the the interface status. They tell you some good information about your peering in the network.
So we looked at there are a few green links. We see that the status is up, but we see these triangles. And these triangles are not, they do not look great. So when I hover over this topology, I am being told that the selected port is not connected to the correct switchboard in the campus traffic topology.
What that basically means is that the the the back end of the campus fabric knows that the core one to core 3 port that I've selected is not the right port and instead it is something else. It is smart enough to understand that there was another port that should have been connected, but I have connected the wrong the wrong port and that is absolutely right. So I'm going to jump right into the campus fabric and change that quickly for you guys. So I'll click on edit configuration and go right to the last step and I'll change this zero to 1 and we'll hit continue and we'll apply changes and save them while the provisioning takes a while.
I'll be right back in a minute. So, so we're back. So as we can see our pretty green lines are back. What and what that means is that we've you corrected the interface that was not correct in the right way.
Campus Fabric was smart enough to let us know that the interfaces that were connected between code one and code three were not right. As you can see, I had 000 earlier and I switched that over to 001 and after doing that my BGP neighborship came back. And then here we can see if I click on any device the statistics between the two devices. We can also see, as I mentioned earlier, the Vlans and the IP addresses.
Thank you. This concludes our campus fabric demo today. I'll summarize all the things that we did today in this last 2025 minute session. So we built a campus fabric using the Mist UI.
None of those steps included anything to do on the CLI. We built a campus fabric in four steps wherein we as a step one, we selected the kind of topology that the user would want. As a second step, we chose the campus fabric nodes that will participate in the campus fabric. The third step was to provide us the networks that will be participating in the in the campus fabric.
And the last and final step was the connectivity of the devices itself. It's as simple as that.
